Search results for "Research"
-

 5.2KHow To
5.2KHow ToHow to Hack Tiktok Account Through SMS Demonstration By Researchers
TikTok, the third busiest app in 2019, is undergoing a rigorous study on user privacy, censorship of politically conflicting content and national...
-

 4.1KNews
4.1KNewsApple Bug Bounty Program Opens Its Invite-Only to All Researchers
As Apple promised in August this year, the company finally launched a bug bounty program for all security researchers, offering cash prizes...
-

 4.1KData Security
4.1KData SecurityHackerOne platform got hacked by a researcher who reported a vulnerability but never got paid
HackerOne is one of the most important vulnerability reporting platforms, so it has access to large amounts of information, although sometimes that...
-

 2.9KNews
2.9KNewsResearchers found privilege escalation and code execution vulnerabilities in Kaspersky software
A security issue discovered by security research company SafeBreach in Kaspersky Secure Connection, which itself is bundled into a range of other...
-
 2.9KCyber Events
2.9KCyber EventsResearchers develop AI tool to evade Internet censorship
The research particularly names India, China, and Kazakhstan for using Internet censorship as a tool to curb freedom of expression and how...
-
 3.2KNews
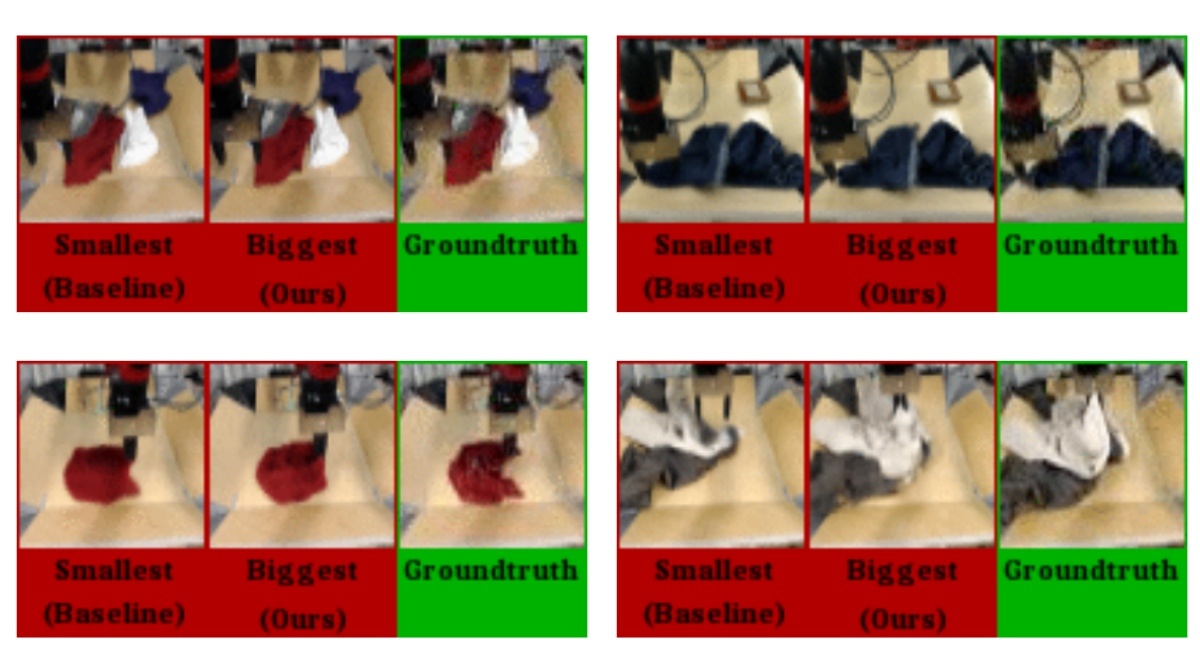
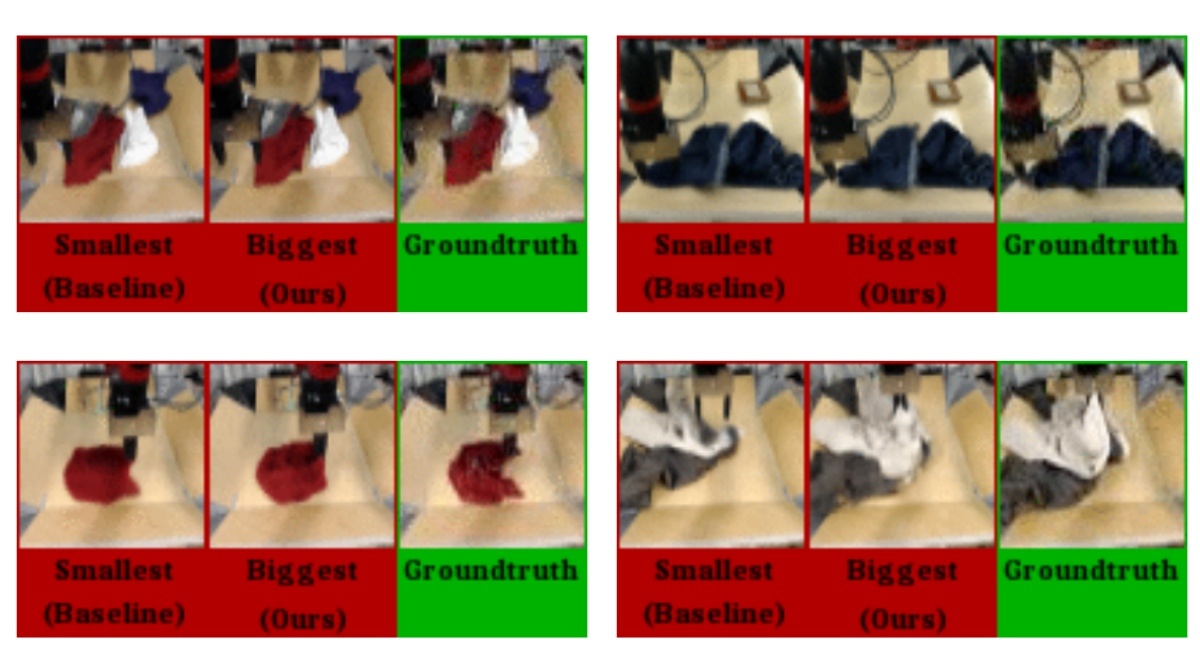
3.2KNewsThis AI Predicts “Future” Video Frames, Says New Research
We have already seen AI algorithms creating animations of people that don’t exist, predicting crop growth, analyzing user actions for serving ads,...
-
 2.0KNews
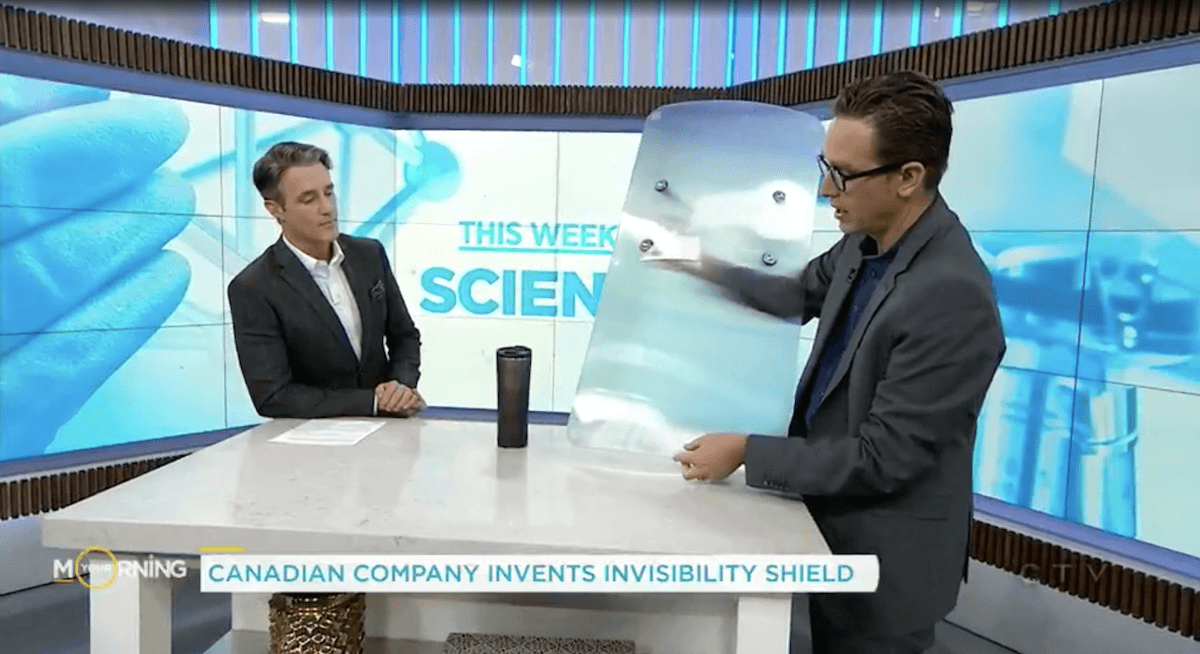
2.0KNewsResearchers Invent Cheap ‘Invisibility Shield’ To Hide People, Buildings
There have been multiple attempts at inventing something similar to Harry Potter’s invisibility cloak but Canada-based researchers’ ‘Quantum Stealth’ could be the...
-

 1.8KNews
1.8KNewsGoogle Researchers Are Training AI To Recognize Smell
Humans can detect one trillion different smells, no wonder it is often considered one of the most powerful senses of the body....
-

 3.5KNews
3.5KNewsResearchers Develop Software To Extend WiFi Range By 200 Feet
Over the years, there has been an exponential increase in the WiFi speeds all over the globe. However, the high speeds come...
-

 372News
372NewsResearchers Are Developing A Nearly “Zero Energy” Bitcoin Alternative
We are way past the cryptocurrency boom that made Bitcoin one of the world’s fastest-growing currencies. One of the downsides of Bitcoin...
-

 577Social Engineering
577Social EngineeringGeoSpy – OSINT analysis and research tool for social engineering attacks
Geolocation Spy (GeoSpy) is an OSINT analysis and research tool, which allows people to track and execute intelligent social engineering attacks in...
-

 476Malware
476MalwarePKPLUG -New Research Found Same Chinese Hacking Group Involved with Multiple Cyber Attacks Across Asia
Researchers linked multiple Cyber-espionage campaigns across Asia to the threat actor group PKPLUG. The group uses its PlugX malware and the number...
-

 3.1KCyber Attack
3.1KCyber AttackCylance Security Researchers Warn Technology Firms in Southeast Asia for Chinese Open –Source Backdoor
Attackings of technology businesses in Southeast Asia by a suspected Chinese threat actor employ a version of the open-source PcShare backdoor, safety...
-

 280Vulnerabilities
280VulnerabilitiesWarning: Researcher Drops phpMyAdmin Zero-Day Affecting All Versions
A cybersecurity researcher recently published details and proof-of-concept for an unpatched zero-day vulnerability in phpMyAdmin—one of the most popular applications for managing...
-

 328Hacked
328Hacked99% Email Attacks Require Human Interaction: Security Researchers
Email-based cyber attacks have become common these days. I am not the only one receiving emails saying that the file in the...
-

 205News
205NewsResearchers Have Found A Way To Predict Your Death (Almost)
Out of all aspects of human life, death is one thing that’s inevitable and all of us move one step closer to...
-

 310News
310NewsMIT Researchers Make Video Streaming Faster On Busy WiFi Connections
Video buffering can be annoying. And it becomes unbearable when a Netflix episode stops every few seconds or gets ridiculously pixilated. But...
-

 306Hacked
306HackedHackers Can Reduce Tor Network Performance For Just $17,000/mo: Research
Amongst privacy enthusiasts, the Tor network is a popular means to browse the internet anonymously. However, time and again, vulnerabilities have been...
-

 252News
252NewsHow Researchers Hacked FaceID Using Modified Glasses On Unconscious Users
Yeah, I know it doesn’t sound right, but this is what researchers have come up with. At the ongoing Black Hat conference...
-

 279News
279NewsSamsung Phones Have Faster Download Speeds Than iPhones: Research
According to a study by OpenSignal, Samsung phones have high LTE speeds when stacked against iPhones and Huawei phones. OpenSignal, an independent...
-

 223News
223NewsMicrosoft Launches Azure Security Lab, Bounty Reward for Researchers up to $40,000
Microsoft launched Azure Security Lab, a set of dedicated cloud hosts for researchers to confidently and aggressively test Azure vulnerabilities. Azure is...






