Search results for "Research"
-

 3.5KVulnerabilities
3.5KVulnerabilitiesResearchers Detail Bug That Could Paralyze Snort Intrusion Detection System
Details have emerged about a now-patched security vulnerability in the Snort intrusion detection and prevention system that could trigger a denial-of-service (DoS)...
-

 2.7KMalware
2.7KMalwareResearchers Share In-Depth Analysis of PYSA Ransomware Group
An 18-month-long analysis of the PYSA ransomware operation has revealed that the cybercrime cartel followed a five-stage software development cycle from August...
-

 349Malware
349MalwareResearchers warn of FFDroider and Lightning info-stealers targeting users in the wild
Cybersecurity researchers are warning of two different information-stealing malware, named FFDroider and Lightning Stealer, that are capable of siphoning data and launching...
-

 4.6KMalware
4.6KMalwareResearchers Connect BlackCat Ransomware with Past BlackMatter Malware Activity
Cybersecurity researchers have uncovered further links between BlackCat (aka AlphaV) and BlackMatter ransomware families, the former of which emerged as a replacement...
-
 2.5KMalware
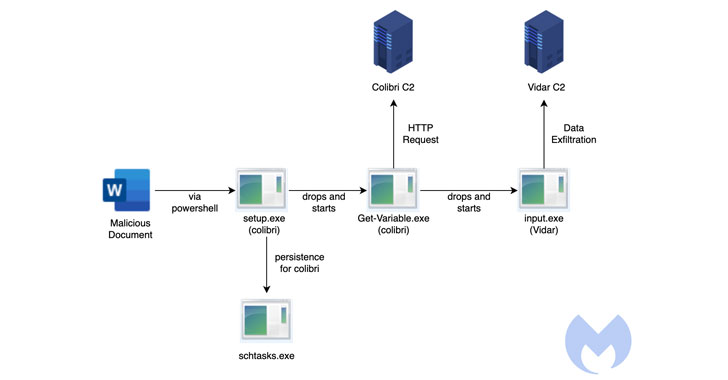
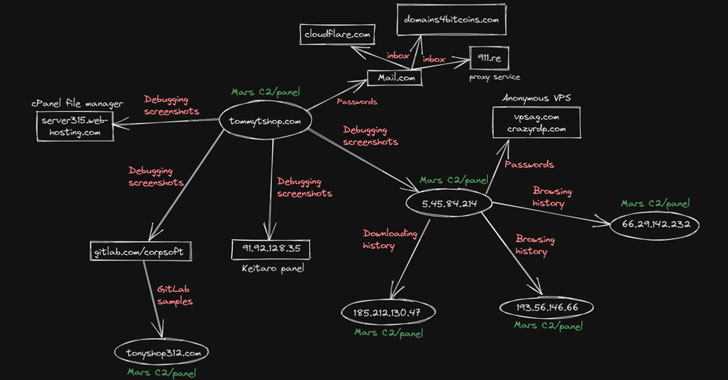
2.5KMalwareResearchers Uncover How Colibri Malware Stays Persistent on Hacked Systems
Cybersecurity researchers have detailed a “simple but efficient” persistence mechanism adopted by a relatively nascent malware loader called Colibri, which has been...
-
 1.3KMalware
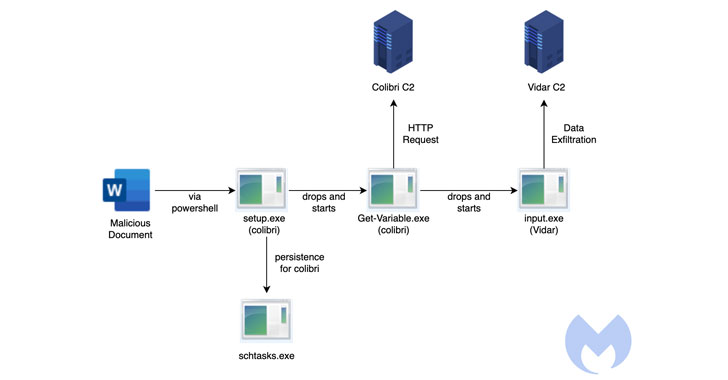
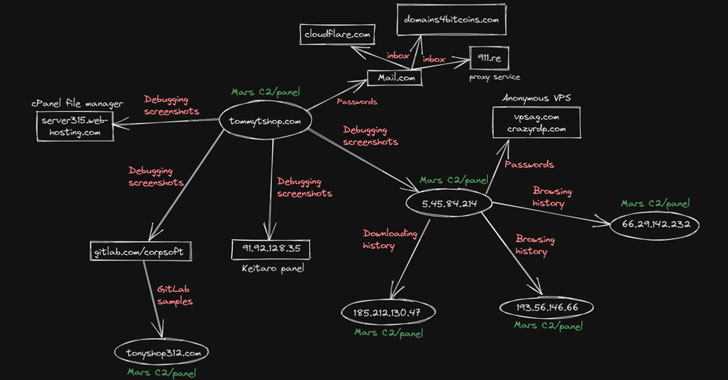
1.3KMalwareResearchers Expose Mars Stealer Malware Campaign Using Google Ads to Spread
A nascent information stealer called Mars has been observed in campaigns that take advantage of cracked versions of the malware to steal...
-

 1.2KData Breach
1.2KData BreachResearchers Trace LAPSUS$ Cyber Attacks to 16-Year-Old Hacker from England
Authentication services provider Okta on Wednesday named Sitel as the third-party linked to a security incident experienced by the company in late...
-

 2.0KMalware
2.0KMalwareResearchers Find New Evidence Linking Kwampirs Malware to Shamoon APT Hackers
New findings released last week showcase the overlapping source code and techniques between the operators of Shamoon and Kwampirs, indicating that they...
-
 2.6KVulnerabilities
2.6KVulnerabilitiesResearchers Warn of Linux Kernel ‘Dirty Pipe’ Arbitrary File Overwrite Vulnerability
Linux distributions are in the process of issuing patches to address a newly disclosed security vulnerability in the kernel that could allow...
-

 4.7KMalware
4.7KMalwareDownload the Conti Ransomware source code. Ukrainian researcher hacked Russian cybercriminal group
Over the past few days a Ukrainian researcher has waged a campaign against the operators of the Conti ransomware, inadvertently spying on...
-

 2.6KIncidents
2.6KIncidentsHow to hack Coinbase to steal cryptocurrency? Researcher details an easy way to do it
A cybersecurity specialist received a bug bounty of $250,000 USD thanks to his report of a critical vulnerability in the cryptocurrency exchange...
-
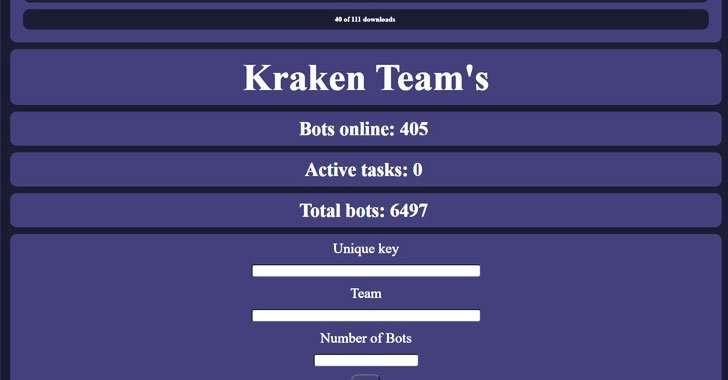
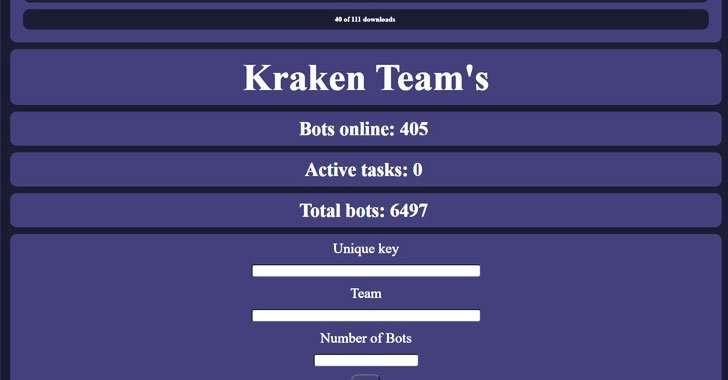 1.5KMalware
1.5KMalwareResearchers Warn of a New Golang-based Botnet Under Continuous Development
Cybersecurity researchers have unpacked a nascent Golang-based botnet called Kraken that’s under active development and features an array of backdoor capabilities to...
-

 4.7KVulnerabilities
4.7KVulnerabilitiesChinese researchers find multiple vulnerabilities in VMware ESXi, Workstation and Fusion; update ASAP
Earlier this week, VMware announced the correction of multiple critical vulnerabilities in products such as VMware ESXi, Workstation and Fusion, most of...
-

 4.9KMalware
4.9KMalwareResearchers Link ShadowPad Malware Attacks to Chinese Ministry and PLA
Cybersecurity researchers have detailed the inner workings of ShadowPad, a sophisticated and modular backdoor that has been adopted by a growing number...
-

 4.5KIncidents
4.5KIncidentsThis cyber security researcher took matter in his own hands and shut down North Korea’s Internet for taking a revenge
In recent weeks, several cyber security researchers have reported massive flaws in the Internet infrastructure in North Korea, affecting the few users...
-

 3.2KVulnerabilities
3.2KVulnerabilitiesGoogle Project Zero researcher finds two critical vulnerabilities in ZOOM
Natalie Silvanovich, a researcher at Google Project Zero, reported the detection of two vulnerabilities in the Zoom video conferencing platform whose exploitation...
-
 2.1KMalware
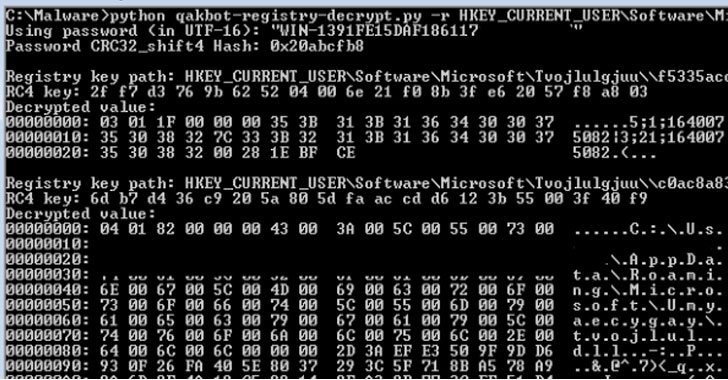
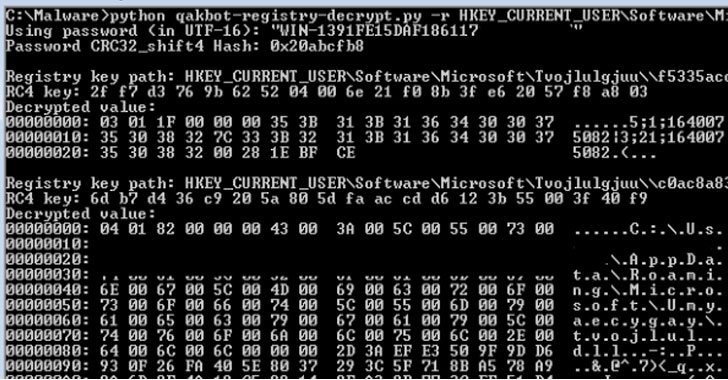
2.1KMalwareResearchers Decrypted Qakbot Banking Trojan’s Encrypted Registry Keys
Cybersecurity researchers have decoded the mechanism by which the versatile Qakbot banking trojan handles the insertion of encrypted configuration data into the...
-

 4.6KMalware
4.6KMalwareHackers Distribute Malicious Version of dnSpy Malware To Attack Security Researchers
In a recent sophisticated malware campaign, the hackers have targeted the cybersecurity researchers and developers in which they were found to be...
-
 2.7KMalware
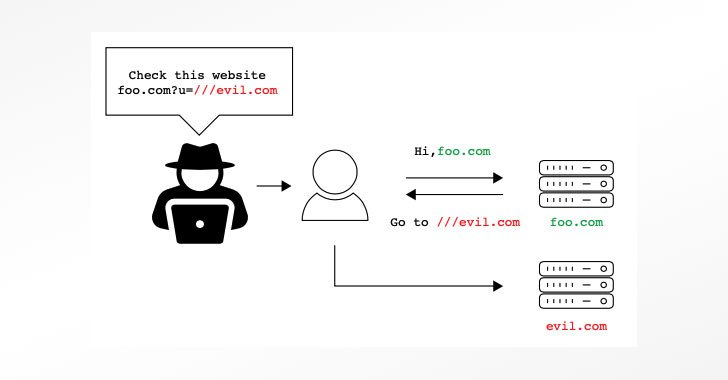
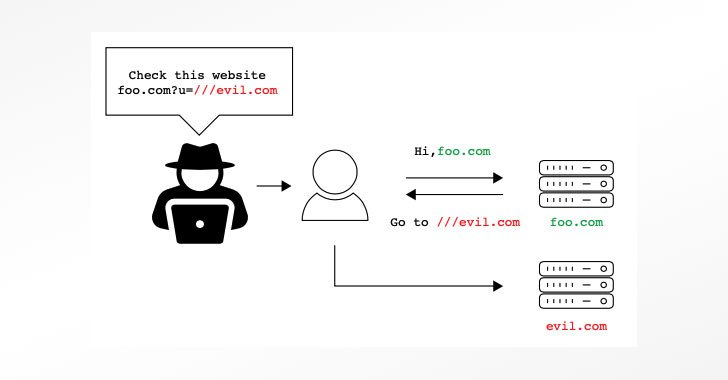
2.7KMalwareResearchers Find Bugs in Over A Dozen Widely Used URL Parser Libraries
A study of 16 different Uniform Resource Locator (URL) parsing libraries has unearthed inconsistencies and confusions that could be exploited to bypass...
-

 1.1KIncidents
1.1KIncidentsHow Chinese cyber army forced a GlaxoSmithKline employee to steal Cancer drug research data from the company
The U.S. Department of Justice (DOJ) announced that Lucy Xi, a resident of the state of Philadelphia, has pleaded guilty to conspiracy...
-

 4.4KData Security
4.4KData SecurityResearch claims Samsung Galaxy Store apps are spreading malware
According to Max Weinbach of Android Police, “Samsung is hosting literal malware on the Galaxy Store.” It is becoming harder and harder...






