Search results for "Research"
-

 3.8KVulnerabilities
3.8KVulnerabilitiesResearchers Leak PoC Exploit for a Critical Windows RCE Vulnerability
A proof-of-concept (PoC) exploit related to a remote code execution vulnerability affecting Windows Print Spooler and patched by Microsoft earlier this month...
-

 4.4KNews
4.4KNewsResearcher Discovers Susceptibility Affecting Numerous Linux Marketplaces
The cross-site scripting (XSS) susceptibility plus various supply chain operations greatly impact on the Linux marketplaces, which are located on the Pling...
-

 888Cyber Attack
888Cyber AttackNorth Korea Exploited VPN Flaw to Hack South’s Nuclear Research Institute
South Korea’s state-run Korea Atomic Energy Research Institute (KAERI) on Friday disclosed that its internal network was infiltrated by suspected attackers operating...
-

 1.6KMalware
1.6KMalwareResearchers Uncover ‘Process Ghosting’ — A New Malware Evasion Technique
Cybersecurity researchers have disclosed a new executable image tampering attack dubbed “Process Ghosting” that could be potentially abused by an attacker to...
-

 1.7KMalware
1.7KMalwareGitHub Updated Policies For Actively Used Exploits, Malware & Vulnerability Research
A set of all-new updates were being released by GitHub on Friday, all the updates pronounce that how the company will deal...
-
 2.6KMalware
2.6KMalwareResearchers Discover First Known Malware Targeting Windows Containers
Security researchers have discovered the first known malware, dubbed “Siloscope,” targeting Windows Server containers to infect Kubernetes clusters in cloud environments. “Siloscape...
-
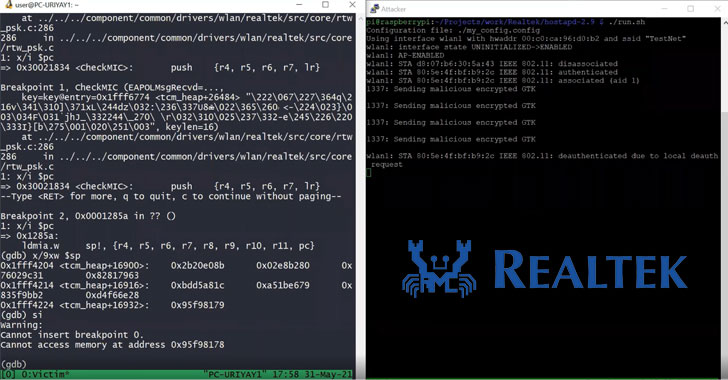
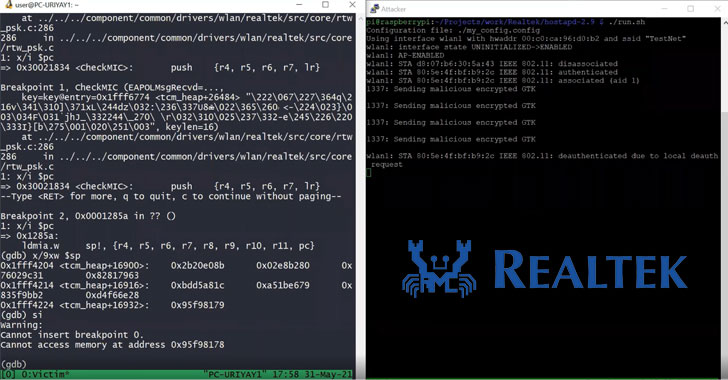 4.5KVulnerabilities
4.5KVulnerabilitiesResearchers Warn of Critical Bugs Affecting Realtek Wi-Fi Module
A new set of critical vulnerabilities has been disclosed in the Realtek RTL8170C Wi-Fi module that an adversary could abuse to gain...
-
 1.8KCyber Attack
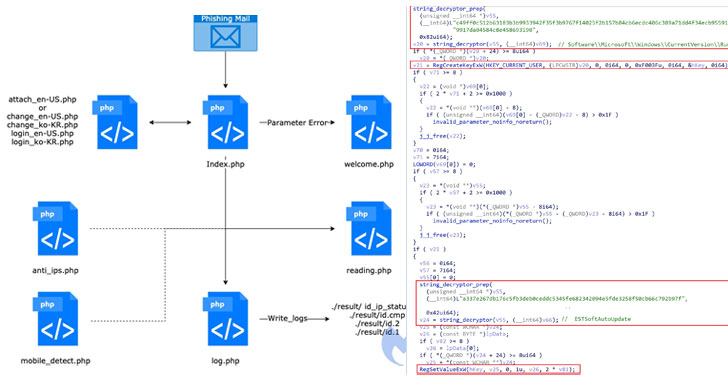
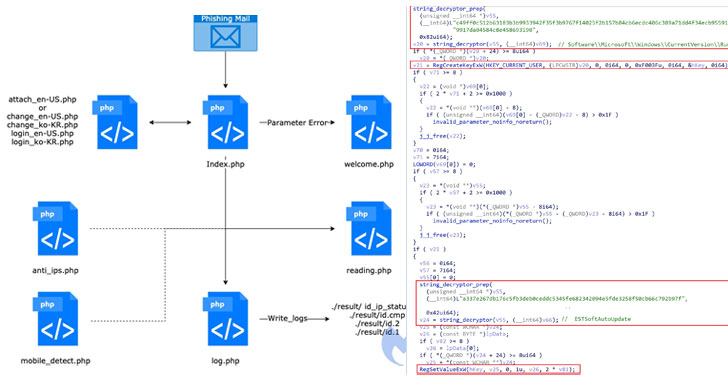
1.8KCyber AttackResearchers Uncover Hacking Operations Targeting Government Entities in South Korea
A North Korean threat actor active since 2012 has been behind a new espionage campaign targeting high-profile government officials associated with its...
-

 3.9KMalware
3.9KMalwareResearchers Warn of Facefish Backdoor Spreading Linux Rootkits
Cybersecurity researchers have disclosed a new backdoor program capable of stealing user login credentials, device information and executing arbitrary commands on Linux...
-
 5.3KCyber Attack
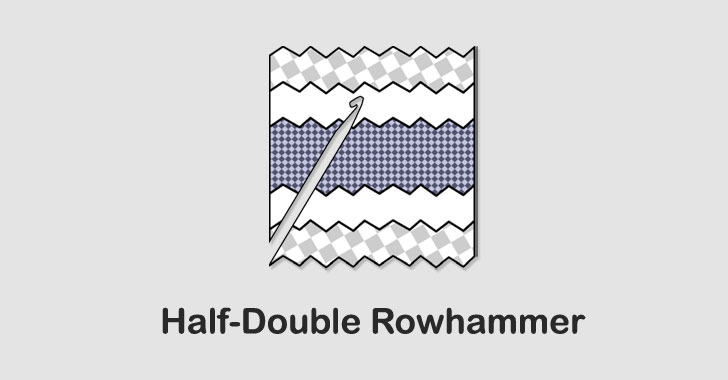
5.3KCyber AttackGoogle Researchers Discover A New Variant of Rowhammer Attack
A team of security researchers from Google has demonstrated yet another variant of the Rowhammer attack that bypasses all current defenses to...
-

 2.2KData Security
2.2KData SecurityLogistics giant exposes customer data, Lolz at researchers when alerted
Bergen Logistics, a New Jersey-based company exposed its database back in December 2020 but Lolz when alerted about the incident. Recently, the...
-

 3.4KMalware
3.4KMalwareResearchers Link CryptoCore Attacks On Cryptocurrency Exchanges to North Korea
State-sponsored hackers affiliated with North Korea have been behind a slew of attacks on cryptocurrency exchanges over the past three years, new...
-

 4.1KMalware
4.1KMalwareResearchers Link CryptoCore Attacks On Cryptocurrency Exchanges to North Korea
State-sponsored hackers affiliated with North Korea have been behind a slew of attacks on cryptocurrency exchanges over the past three years, new...
-

 3.8KVulnerabilities
3.8KVulnerabilitiesResearcher publishes PoC for CVE-2021-31166 vulnerability in Microsoft IIS
Axel Souchet, a security researcher who used to work for Microsoft, revealed the Proof of Concept (PoC) exploit code to abuse a...
-

 4.1KMalware
4.1KMalwareDarkSide ransomware affiliates are using Sophos firewall and VPN vulnerability to hack. Researchers track down 5 affiliates of them
FireEye cybersecurity specialists published details of a recent research related to the DarkSide ransomware operation. This week experts released reports on five...
-

 4.8KMalware
4.8KMalwareESET Research goes to RSA Conference 2021 with two presentations
We will explore two threats – Android stalkerware and XP exploits
-

 1.2KMalware
1.2KMalwareResearchers Uncover Iranian State-Sponsored Ransomware Operation
Iran has been linked to yet another state-sponsored ransomware operation through a contracting company based in the country, according to new analysis....
-
 3.4KMalware
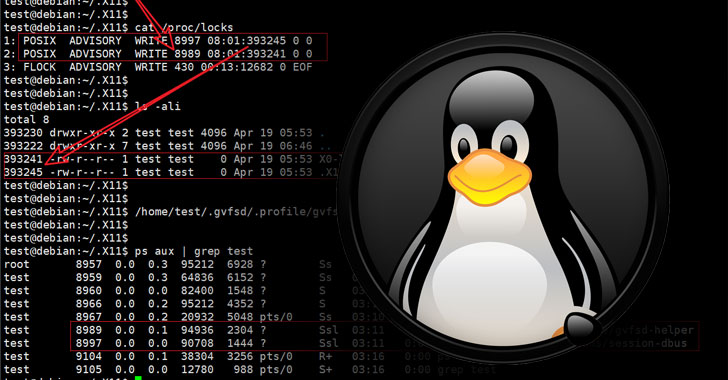
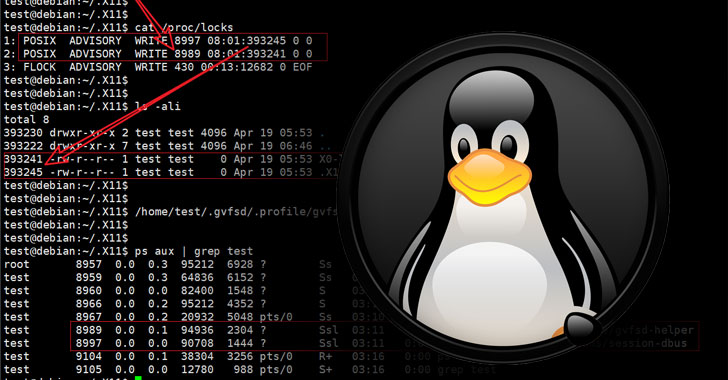
3.4KMalwareResearchers Uncover Stealthy Linux Malware That Went Undetected for 3 Years
A previously undocumented Linux malware with backdoor capabilities has managed to stay under the radar for about three years, allowing the threat...
-

 708Cyber Attack
708Cyber AttackResearchers Find Additional Infrastructure Used By SolarWinds Hackers
The sprawling SolarWinds cyberattack which came to light last December was known for its sophistication in the breadth of tactics used to...
-
 1.4KCyber Attack
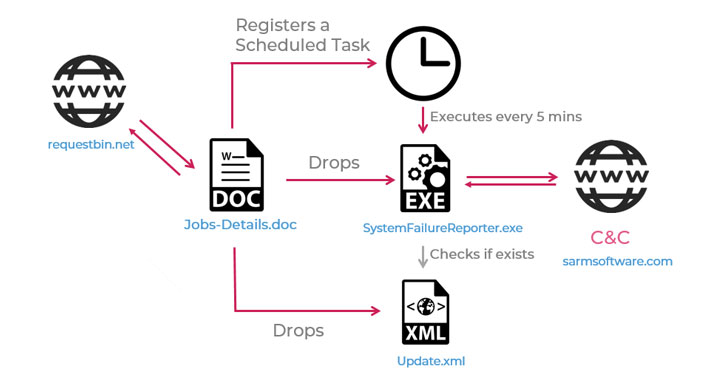
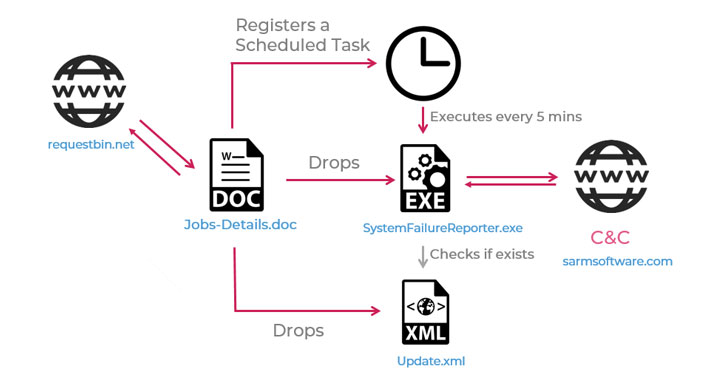
1.4KCyber AttackResearchers uncover a new Iranian malware used in recent cyberattacks
An Iranian threat actor has unleashed a new cyberespionage campaign against a possible Lebanese target with a backdoor capable of exfiltrating sensitive...
-

 1.7KVulnerabilities
1.7KVulnerabilitiesHackers use sophisticated techniques to prevent researchers from detecting phishing websites
Cybersecurity specialists report that multiple phishing websites are using JavaScript to prevent detection, checking whether users are browsing from a virtual machine...






