Search results for "Research"
-
 1.4KMalware
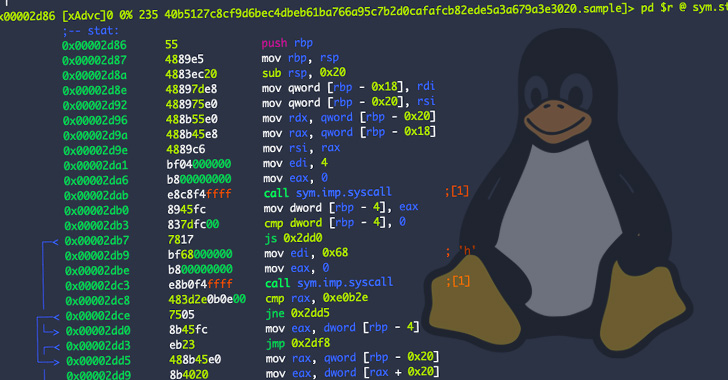
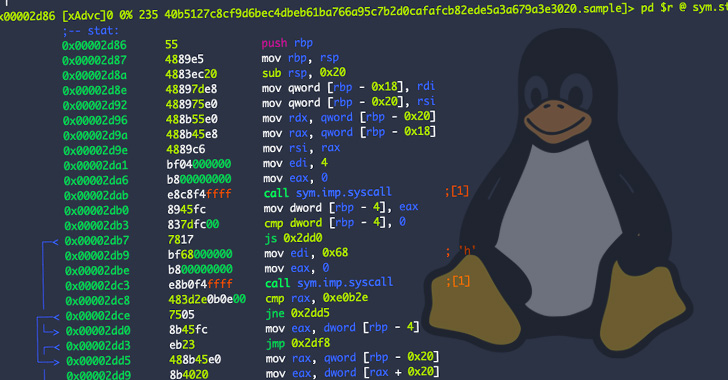
1.4KMalwareResearchers Warn of New OrBit Linux Malware That Hijacks Execution Flow
Cybersecurity researchers have taken the wraps off a new and entirely undetected Linux threat dubbed OrBit, signally a growing trend of malware...
-

 4.5KMalware
4.5KMalwareResearchers Warn of ‘Matanbuchus’ Malware Campaign Dropping Cobalt Strike Beacons
A malware-as-a-service (Maas) dubbed Matanbuchus has been observed spreading through phishing campaigns, ultimately dropping the Cobalt Strike post-exploitation framework on compromised machines....
-
 5.0KMalware
5.0KMalwareResearchers Uncover ‘Hermit’ Android Spyware Used in Kazakhstan, Syria, and Italy
An enterprise-grade surveillanceware dubbed Hermit has been put to use by entities operating from within Kazakhstan, Syria, and Italy over the years...
-
 4.2KMalware
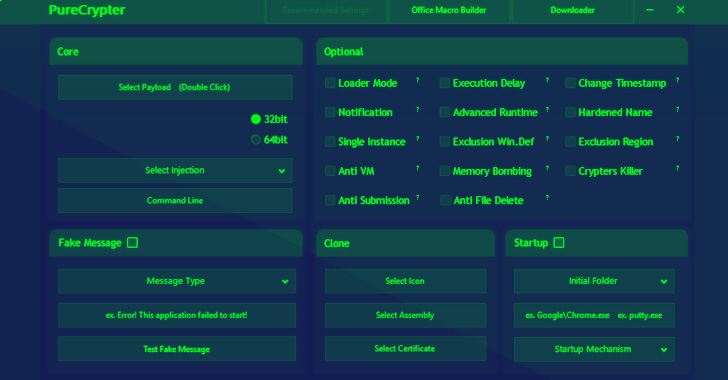
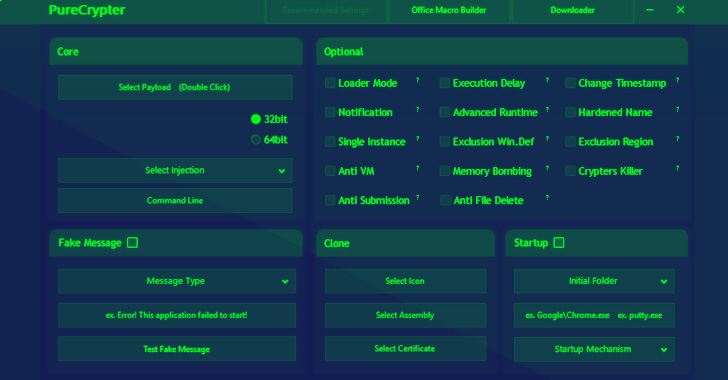
4.2KMalwareResearchers Detail PureCrypter Loader Cyber Criminals Using to Distribute Malware
Cybersecurity researchers have detailed the workings of a fully-featured malware loader dubbed PureCrypter that’s being purchased by cyber criminals to deliver remote...
-

 2.3KMalware
2.3KMalwareMIT Researchers Discover New Flaw in Apple M1 CPUs That Can’t Be Patched
A novel hardware attack dubbed PACMAN has been demonstrated against Apple’s M1 processor chipsets, potentially arming a malicious actor with the capability...
-
 830Vulnerabilities
830VulnerabilitiesResearchers Warn of Unpatched “DogWalk” Microsoft Windows Vulnerability
An unofficial security patch has been made available for a new Windows zero-day vulnerability in the Microsoft Support Diagnostic Tool (MSDT), even...
-
 4.9KMalware
4.9KMalwareResearchers Warn of Spam Campaign Targeting Victims with SVCReady Malware
A new wave of phishing campaigns has been observed spreading a previously documented malware called SVCReady. “The malware is notable for the...
-

 4.7KMalware
4.7KMalwareResearchers Uncover Malware Controlling Thousands of Sites in Parrot TDS Network
The Parrot traffic direction system (TDS) that came to light earlier this year has had a larger impact than previously thought, according...
-
 2.2KMalware
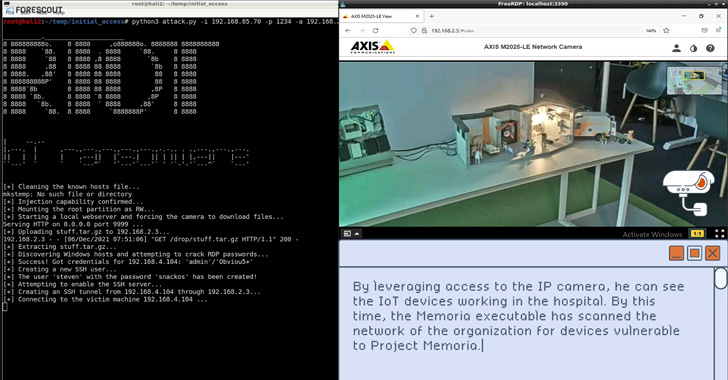
2.2KMalwareResearchers Demonstrate Ransomware for IoT Devices That Targets IT and OT Networks
As ransomware infections have evolved from purely encrypting data to schemes such as double and triple extortion, a new attack vector is...
-
 2.4KVulnerabilities
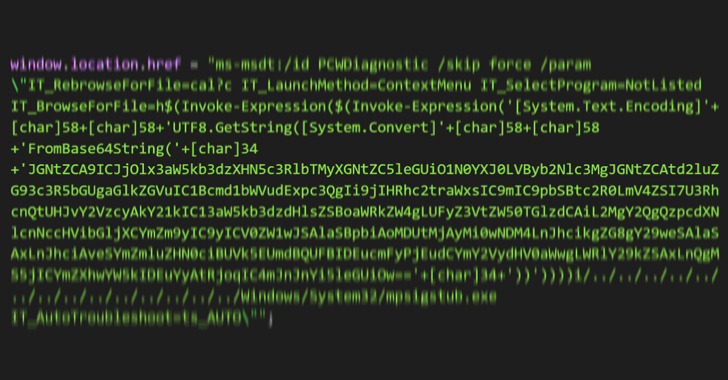
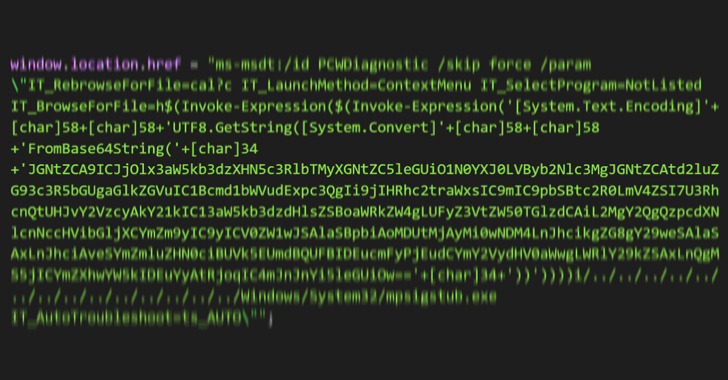
2.4KVulnerabilitiesWatch Out! Researchers Spot New Microsoft Office Zero-Day Exploit in the Wild
Cybersecurity researchers are calling attention to a zero-day flaw in Microsoft Office that could be abused to achieve arbitrary code execution on...
-
 1.1KMalware
1.1KMalwareResearchers Find New Malware Attacks Targeting Russian Government Entities
An unknown advanced persistent threat (APT) group has been linked to a series of spear-phishing attacks targeting Russian government entities since the...
-
 5.0KMalware
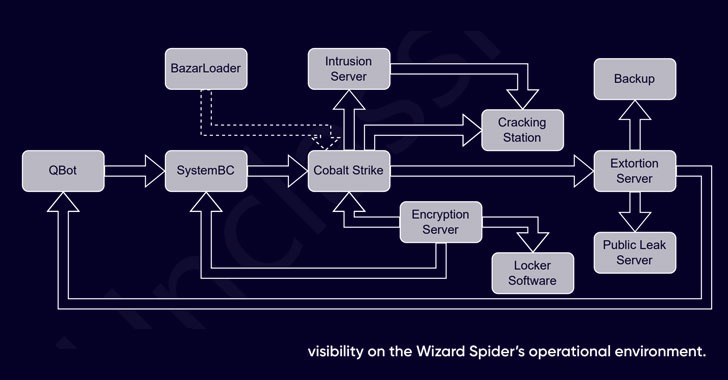
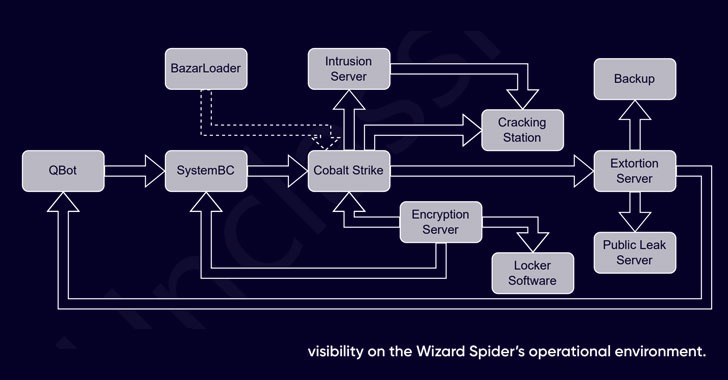
5.0KMalwareResearchers Expose Inner Workings of Billion-Dollar Wizard Spider Cybercrime Gang
The inner workings of a cybercriminal group known as the Wizard Spider have been exposed, shedding light on its organizational structure and...
-

 2.7KVulnerabilities
2.7KVulnerabilitiesSecurity researcher finds new way to exploit CVE-2022-22005, recently patched deserialization bug in Microsoft SharPoint
In early 2022, Microsoft addressed CVE-2022-22005, a remote code execution (RCE) vulnerability that used website creation features in SharePoint, releasing a security...
-

 701Malware
701MalwareResearchers Find Potential Way to Run Malware on iPhone Even When it’s OFF
A first-of-its-kind security analysis of iOS Find My function has identified a novel attack surface that makes it possible to tamper with...
-
 1.5KMalware
1.5KMalwareResearchers Warn of “Eternity Project” Malware Service Being Sold via Telegram
An unidentified threat actor has been linked to an actively in-development malware toolkit called the “Eternity Project” that lets professional and amateur...
-

 3.2KMalware
3.2KMalwareResearchers Warn of Nerbian RAT Targeting Entities in Italy, Spain, and the U.K.
A previously undocumented remote access trojan (RAT) written in the Go programming language has been spotted disproportionately targeting entities in Italy, Spain,...
-
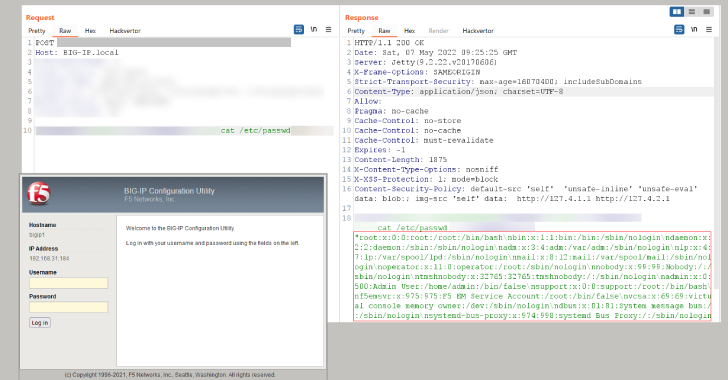
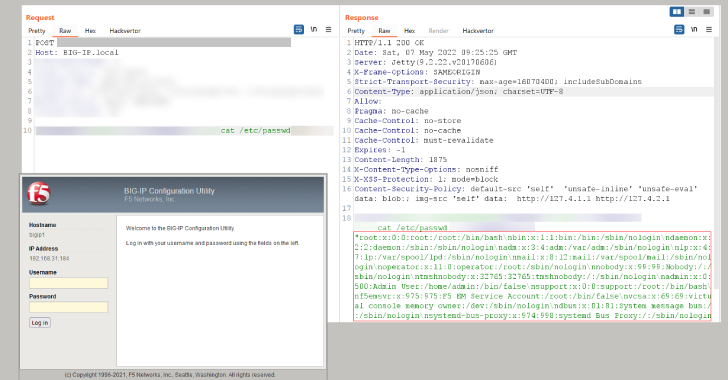 4.7KVulnerabilities
4.7KVulnerabilitiesResearchers Develop RCE Exploit for the Latest F5 BIG-IP Vulnerability
Days after F5 released patches for a critical remote code execution vulnerability affecting its BIG-IP family of products, security researchers are warning...
-
 4.6KMalware
4.6KMalwareResearchers Warn of ‘Raspberry Robin’ Malware Spreading via External Drives
Cybersecurity researchers have discovered a new Windows malware with worm-like capabilities and is propagated by means of removable USB devices. Attributing the...
-

 2.0KMalware
2.0KMalwareResearcher finds DLL hijacking vulnerability in Conti, REvil, LockBit, Black Basta, BitLocker, and AvosLocker ransomware variants that could prevent file encryption
A researcher has detected a critical vulnerability in some of the most common malware and ransomware variants today and whose exploitation would...
-

 4.7KMalware
4.7KMalwareResearchers Takeover Unpatched 3rd-Party Antivirus Sandboxes via VirusTotal
Security researchers have disclosed a security issue that could have allowed attackers to weaponize the VirusTotal platform as a conduit to achieve...
-
 5.3KVulnerabilities
5.3KVulnerabilitiesResearcher Releases PoC for Recent Java Cryptographic Vulnerability
A proof-of-concept (PoC) code demonstrating a newly disclosed digital signature bypass vulnerability in Java has been shared online. The high-severity flaw in...






