Search results for "Research"
-

 302News
302NewsVulnerability Helps Researchers Expose Malware C&C Servers
We usually get to hear of vulnerabilities that cybercriminals exploit to expose or steal data. This time it’s the other way around;...
-

 194Articles
194ArticlesHacking Virtual Reality – Researchers Exploit Popular Bigscreen VR App
A team of cybersecurity researchers from the University of New Haven yesterday released a video demonstrating how vulnerabilities that most programmers often...
-

 275Data Security
275Data SecurityAccording to researchers, blockchain is not safe anymore
Academics describe scenarios that put the use of blockchain technology at risk Network security specialists from the International Institute of Cyber Security...
-
 163Articles
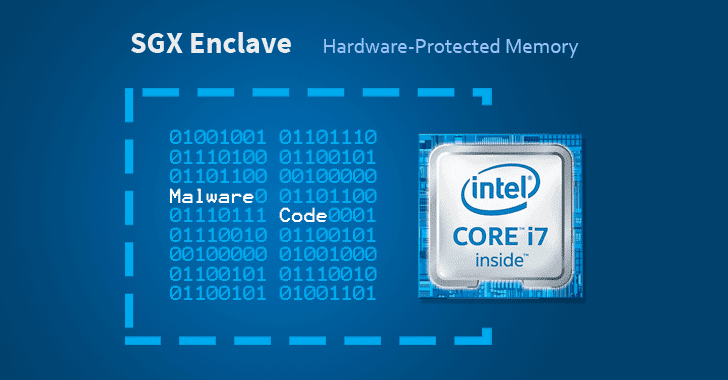
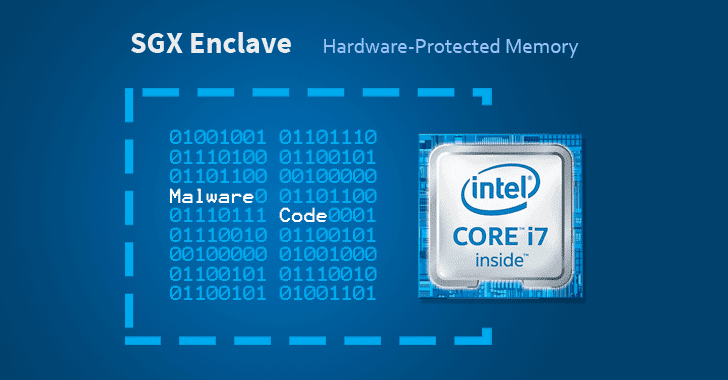
163ArticlesResearchers Implant “Protected” Malware On Intel SGX Enclaves
Cybersecurity researchers have discovered a way to hide malicious code in Intel SGX enclaves, a hardware-based memory encryption feature in modern processors...
-

 337News
337NewsResearcher Refuses To Disclose Critical macOS Keychain Security Flaw
Linus Henze, a security researcher, has uncovered a security flaw in macOS Mojave Keychain that can allow bad actors to steal the...
-

 202News
202News48,000 Indians Earned Thousands Of Dollars From Facebook’s “Research” App
Facebook was recently caught extracting data from its “research” app in exchange of $20 gift cards. Apple punished the social media company...
-

 296News
296NewsFacebook Defends ‘Research’ App; Says Kids Consented To Data Collection
On Tuesday, Techcrunch reported that Facebook is paying teenagers to install a “Research” VPN app in iOS devices in exchange for $20...
-

 181Articles
181ArticlesFacebook Paid Teens $20 to Install ‘Research’ App That Collects Private Data
If you are thinking that Facebook is sitting quietly after being forced to remove its Onavo VPN app from Apple’s App Store,...
-

 318News
318NewsFacebook’s “Research” Tool Pays Users To Get Complete Access To Their Data
Update: After the report surfaced, Facebook said it would shut down the iOS version of its Research app, however, Apple says it has...
-
 167Articles
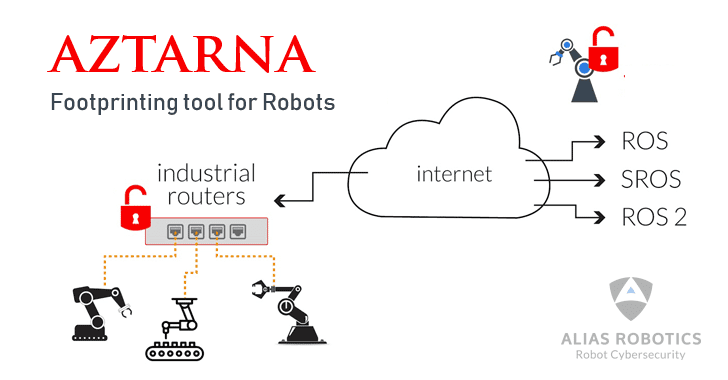
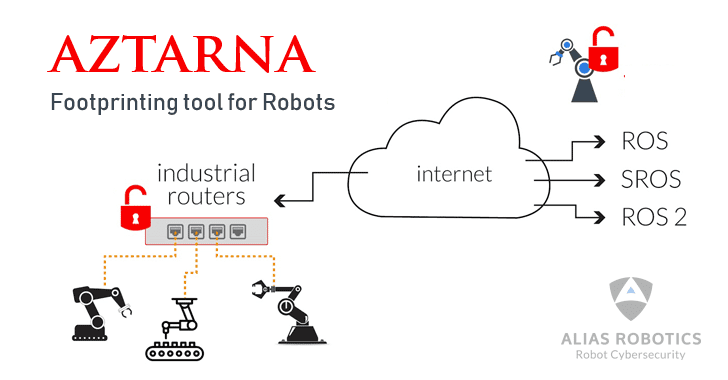
167ArticlesResearchers Release Tool That Finds Vulnerable Robots on the Internet
A team at a robot cybersecurity startup has released a free, open-source tool for information security professionals to help them easily ‘footprint’...
-
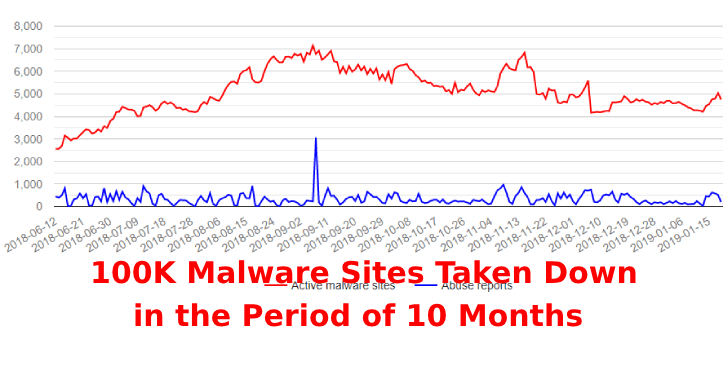
 175Malware
175MalwareSecurity Researchers Globally take down Nearly 100K Malware Sites in the Period of 10 Months
The coordinated efforts were part of the URLhaus initiative that Abuse.ch launched in March 2018, and whose primary objective is to collect...
-
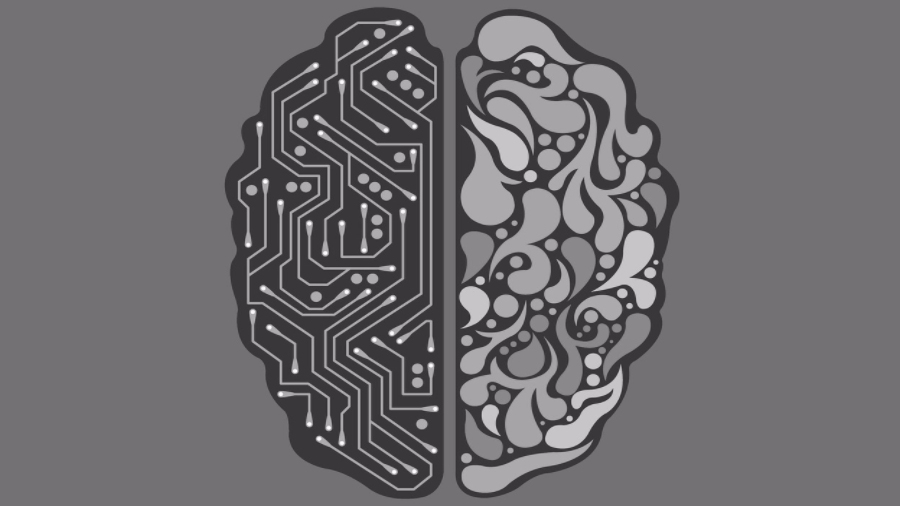
 182News
182NewsResearchers Are Making A Quantum Neural Network Similar To Our Brain
Until now quantum computers have competed with classic computers in solving problems. But, researchers are planning to leverage the power of quantum...
-

 2.1KMalware
2.1KMalwareResearchers Found Goldluck Malware Infecting iPhone Apps
The Goldluck malware has been around for more than a year. The malware basically gave hackers privileges which allowed them to send...
-

 220News
220NewsMark Zuckerberg-Funded Researchers Are Testing Brain Implants
Mark Zuckerberg and his wife Priscilla Chan have raised nearly $5 billion by selling almost 29 million Facebook shares to fund an...
-

 392Data Security
392Data SecurityResearchers exploit Vein-based authentication system using a wax hand
Biometric authentication is currently a widely used option for maintaining the security of devices and systems. With the emergence of vein-based authentication,...
-

 245News
245NewsResearcher Shows How Facebook Worm Attack Can Spam Your Wall
A security researcher has published the proof-of-concept code which demonstrates how to create a fully functional Facebook worm. It’s a clickjack bomb...
-

 663Privacy
663PrivacySecurity researchers bypass encryption on self‑encrypting drives
Industry standard specification does not guarantee the safety of the self-encrypting drives despite verification
-

 429Malware
429MalwareResearchers reveal the malware used by North Korean hackers to attack ATMs
The Lazarus hackers have been using the FastCash Trojan on obsolete AIX servers to steal tens of millions of dollars The researchers...
-

 238Articles
238ArticlesRussian Research Lab Aided the Development of TRITON Industrial Malware
Cybersecurity firm FireEye claims to have discovered evidence that proves the involvement of a Russian-owned research institute in the development of the...
-

 283Data Security
283Data SecurityResearchers demonstrate how to unlock Tesla wireless key fobs in 2 seconds
Vulnerabilities and security flaws in vehicle security systems aren’t as surprising for us as it is that even the most renowned car...
-

 248Uncategorized
248UncategorizedMicrosoft Research Detours Package
Detours is a software package for monitoring and instrumenting API calls on Windows. Detours has been used by many ISVs and is...






