Search results for "Research"
-

 264News
264NewsMicrosoft Asks Researchers To “Do Their Worst,” Doubles Azure Bounty To $40,000
At the ongoing Black Hat USA 2019 conference, Microsoft announced the Azure Security Lab ‚ a sandbox-like environment for security researchers to...
-
 338Vulnerabilities
338VulnerabilitiesResearchers Discover New Ways to Hack WPA3 Protected WiFi Passwords
The same team of cybersecurity researchers who discovered several severe vulnerabilities, collectively dubbed as Dragonblood, in the newly launched WPA3 WiFi security...
-
 355News
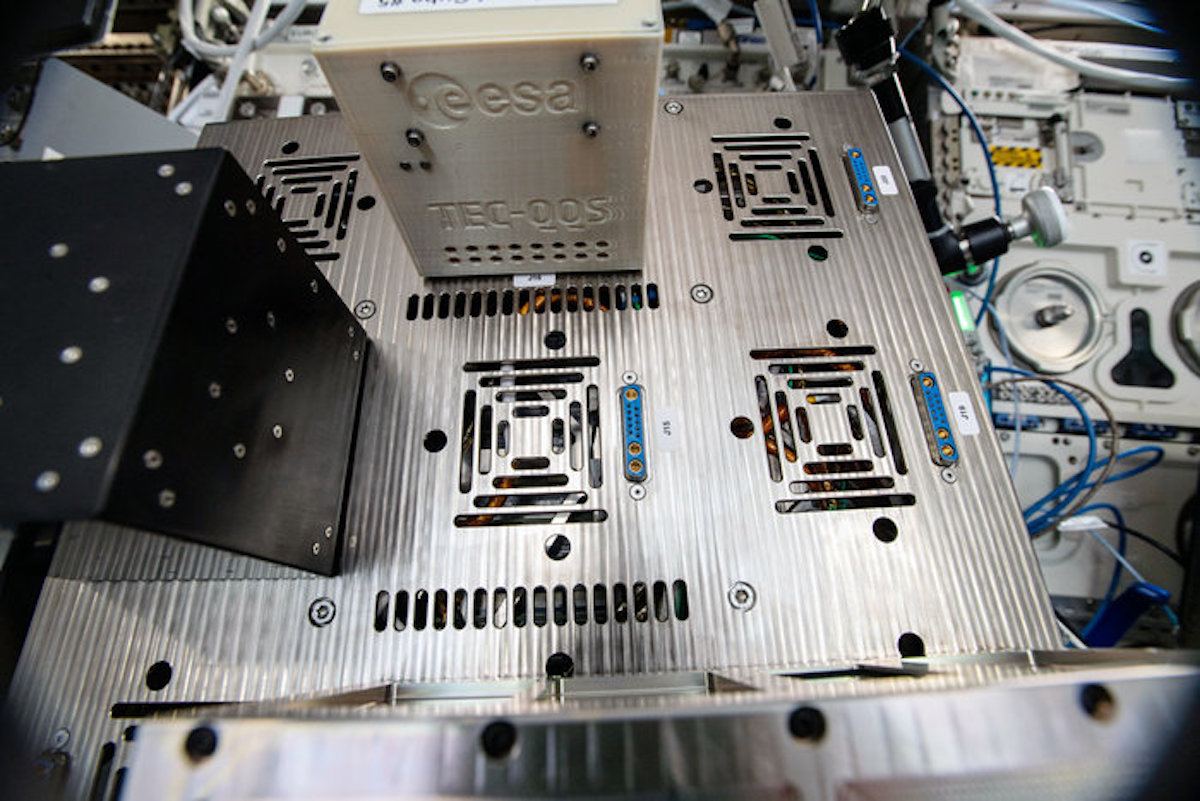
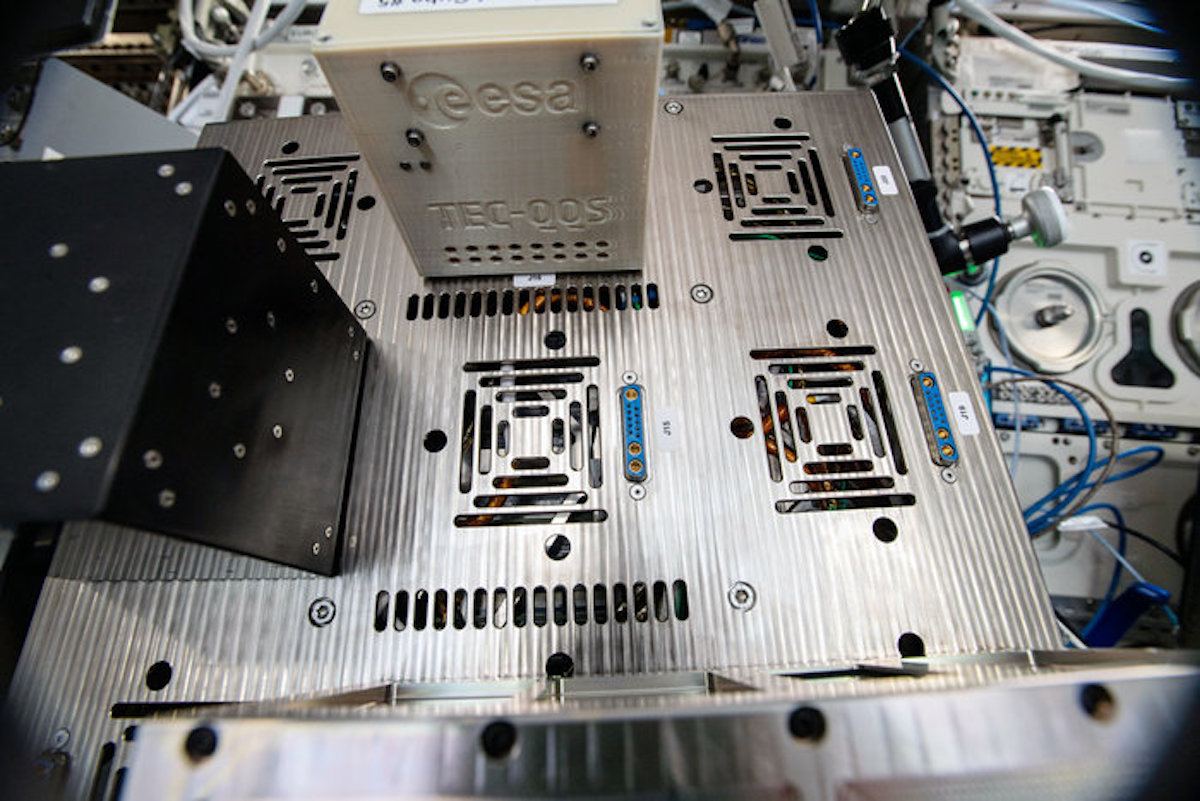
355NewsResearchers Are Using $10 Raspberry Pi Zero For ‘Cheap Encryption’ In Space
There are several techniques of encryption that are deployed to secure communication protocols and devices but these techniques aren’t effective if you...
-

 259News
259NewsResearchers Re-identify 99.98% People In ‘Anonymized’ Dataset
Various companies collect data from our devices almost all the time. While there is always a privacy concern in the picture, they...
-
 233News
233NewsResearchers Build Transistor-Like ‘Quantum Gates’ Using Qudits
Quantum computing is a promising field but not much progress has been made until now. The reason behind this is the unstable...
-
 582Infosec
582InfosecMost Important Security Tools and Resources For Security Researcher and Malware Analyst
Security Professionals always need to learn many tools, techniques, and concepts to analyze sophisticated Threats and current cyber attacks. Hex Editors HxD...
-

 292News
292NewsDeepfake AI: Researchers Have Finally Found A ‘Good’ Way To Use It
Deepfakes have gained a lot of negative attention recently. Be it the hugely criticized DeepNude AI app which removes clothing from pictures...
-

 213News
213NewsGoogle Researcher Finds Nasty iMessage Bug That ‘Bricks’ iPhone
Time and again, we have seen that sending a string of particular characters in iMessage can lead to strange things on an...
-
 299Data Security
299Data SecurityResearchers exploit LTE flaws to send 50,000 fake presidential alerts
Researchers managed to cover a 50,000 seat football stadium using only four malicious portable stations. A group of security researchers from the...
-
 278News
278NewsNetflix Researchers Just Fixed 4 Severe Linux And FreeBSD Vulnerabilities
Movies and TV shows pop up in our minds when we say the word Netflix. But it turns out the company wants...
-

 266News
266NewsFacebook’s ‘Research’ App Is Back: This Time It Pays Adults For Sharing Data
In January, Facebook landed itself in trouble and got its developer license revoked after it was revealed by TechCrunch that the social...
-
 267News
267NewsAI Techs Of Facebook, Microsoft, And Google Prefer “Rich People”: Research
Object recognition is a computer vision (CV) technique using which computers can recognize objects, such as items in our common households. Now...
-
 161News
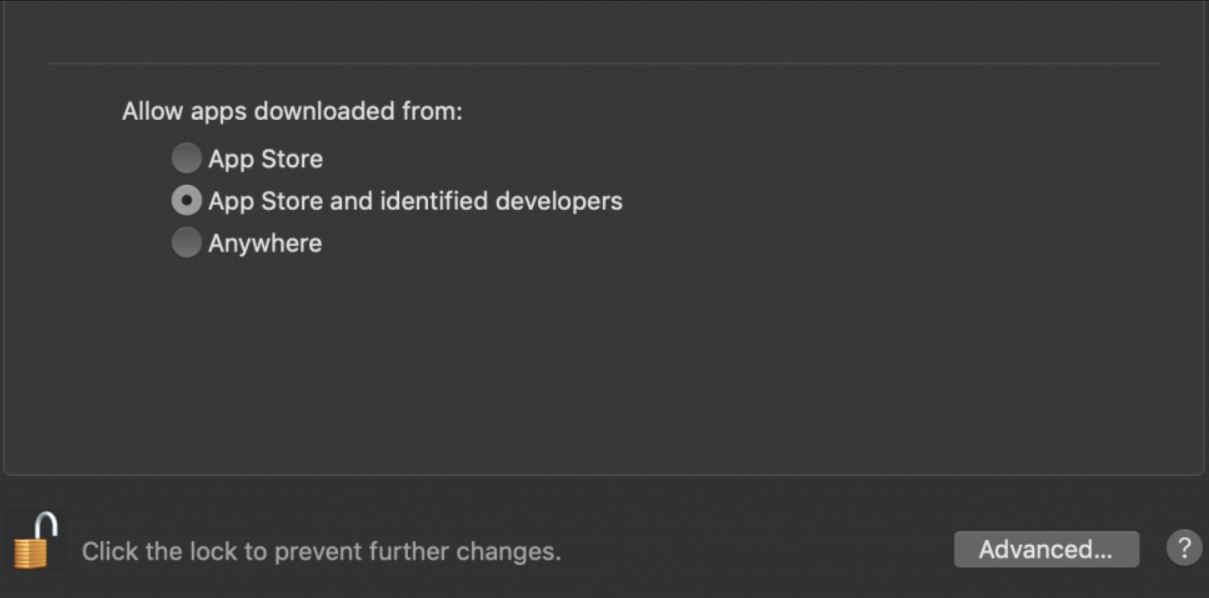
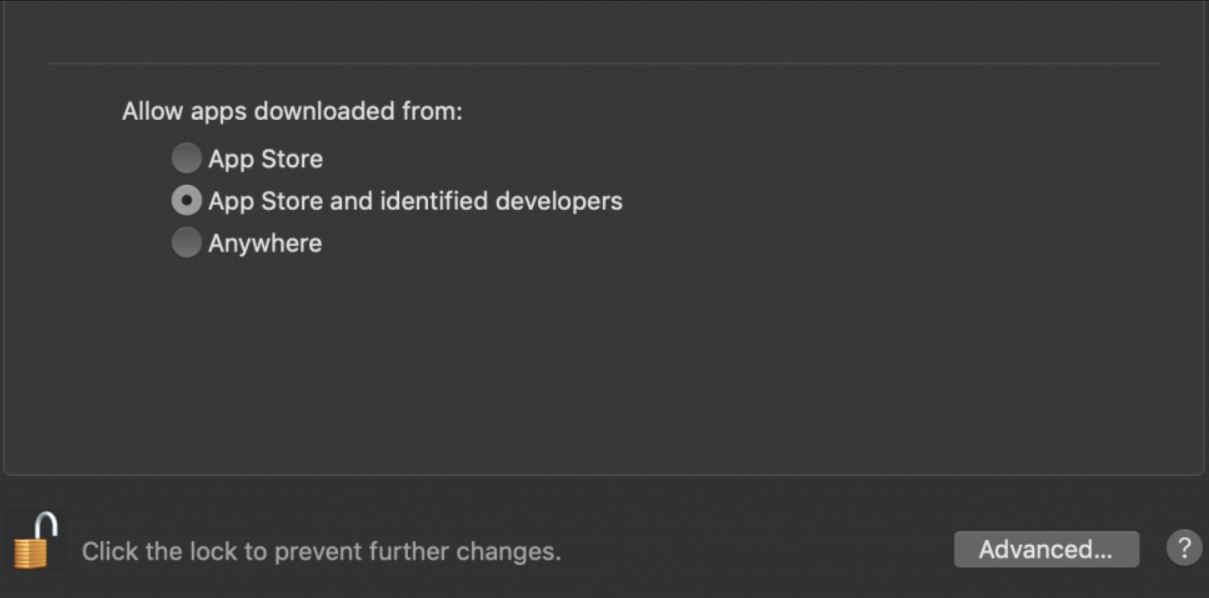
161NewsResearcher publishes macOS Gatekeeper bypass vulnerability
Security researcher Filippo Cavallarin recently discovered a security vulnerability on macOS 10.14.5 that can ignore the first barrier of the system security...
-

 256News
256NewsResearchers Have Invented The World’s First Unhackable Processor
Meet MORPHEUS — a new computer architecture developed by researchers from the University of Michigan that is claimed to be ‘unhackable’ because...
-

 165News
165NewsResearchers have developed a new technology to identify malware
Researchers at North Carolina State University and the University of Texas at Austin have developed a new technology to detect malware. The...
-

 152News
152NewsBiodegradable Plastic Is As Bad As Conventional Plastic: Research
Biodegradable plastic bags can survive up to 3 years in soil and water, according to a study. Biodegradable bags used in the...
-

 257Vulnerabilities
257VulnerabilitiesResearchers Find 36 security vulnerabilities in LTE standard
Each new research conducted by experts from the best ethical hacking Institute and specialists from the International Institute of Cyber Security (IICS)...
-

 278News
278NewsElements Of A Well Researched Phishing Attempt
Phishers for decades have honed their skills of persuasion, that is why the art of fooling people through an Internet-messaging method is...
-

 274News
274NewsElements Of A Well Researched Phishing Email Attempt
Phishers for decades have honed their skills of persuasion, that is why the art of fooling people through an Internet-messaging method is...
-
 263Malware
263MalwareOperation Sharpshooter – Researchers Linked the Global Campaign to Lazarus Hacker Group
Security researchers from McAfee linked the global campaign dubbed Operation Sharpshooter to the infamous Lazarus Hacker Group. Sharpshooter campaign targets primarily on...
-
 275Articles
275ArticlesResearchers Link ‘Sharpshooter’ Cyber Attacks to North Korean Hackers
Security researchers have finally, with “high confidence,” linked a previously discovered global cyber espionage campaign targeting critical infrastructure around the world to...






