Search results for "Secure"
-

 520Privacy
520Privacy10 steps to staying secure on public Wi‑Fi
The convenience of public Wi-Fi for many people is invaluable, yet there are risks. With all this in mind, here are 10...
-

 271Surveillance
271SurveillanceHORNET – Faster and Secure Anonymity Network Than Tor
Most of you must have heard about Tor, which is one of the renowned network based on onion router, delivers a good...
-
 196Hacked
196HackedCyberGhost Privacy Accelerator Program Offers €100,000 if You Can Make Web a Secure Place
“How Government secretly read your e-mails with this insane law?“ “Snowden’s Revelations: XKEYSCORE is NSA’s search engine.” “Real-Time Cyber Attacks across the globe. ““NSA’s...
-

 111Password
111PasswordUK Consumers willing to share DNA with banks to secure identity
Consumers in the UK would be happy to share their DNA if it would help secure their financial and personal information, according...
-
 214Hacked
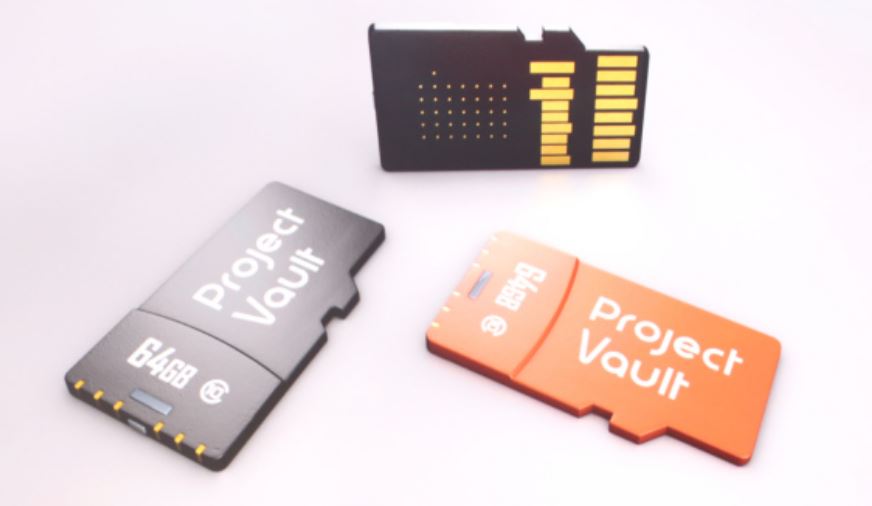
214HackedGoogle’s Project Vault: A Secure Computer On A Micro SD Card
From the stage of Google I/O 2015, Google’s Regina Duggan introduced something that wants you to forget the passwords and become one...
-
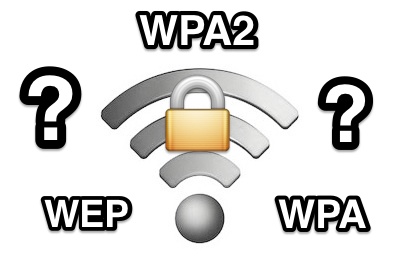
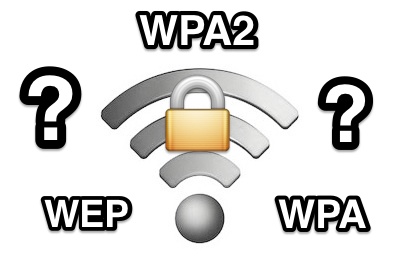 156Hacking Tutorials
156Hacking Tutorials6 Ways to Secure a Wireless Wi-Fi Network
Wireless Networking (Wi-Fi) has made it so easy for anyone to use Internet on your computer, mobile phones, tablets and other wireless...
-

 315Hacked
315HackedAnonymous Hijacks Thousands of Insecure Routers to Power Its DDoS Tools
Lack of some elementary security measures can risk your router’s security and this has stemmed to grow into a large-scale denial-of-service (DDoS)...
-

 129Hacked
129HackedNew Firefox Features Will Only Support Secure Websites
In a recent blog post, Mozilla has showed its intent to phase out the non-secure websites i.e. the HTTP. Earlier this week,...
-

 110Privacy
110PrivacyHackers spy on Kansas family through unsecured baby monitor
A Kansas family are the latest victims of a hacked nanny cam, after noticing the device purchased to monitor their three-month-old baby...
-

 103Mobile Security
103Mobile SecurityHow secure is your smartwatch?
Last week’s Apple Watch launch has put the spotlight back on the ‘smart’ inter-connected watches that are expected to change how we...
-

 194Cyber Events
194Cyber EventsUS Air Force Introduces ‘Task Force Cyber Secure’ to tackle cyber attacks
”Task Force Cyber Secure” was signed and established by Chief of Staff (CSAF) General Mark Walsh III on March 20, 2015 as...
-

 252Hacked
252Hacked‘Unsend’ Your Text Messages With World’s Most Secured Messaging App
Congratulations people! The app that we had been waiting for the since a long time, has finally arrived. Regretting a wrong message...
-
 205How To
205How To9 Linux Commands To Be Known To Secure Your Linux From Danger
Linux shell or terminal commands are very powerful and just a simple command could lead one to delete a folder, files or root folder,...
-
 432Privacy
432PrivacyHobbit‑inspired sword can help you find unsecured WiFi hotspots
Like many others, I was enchanted by The Hobbit (and later Lord of the Rings) at a young age - long before...
-

 97How To
97How ToHow do open source tools stay secure?
Security of open source code is a hot topic, what with Heartbleed, Shellshock, and Poodle making the news. Open source code is...
-

 410Privacy
410PrivacyUltra‑secure hard drive ‘shatters on demand’
A new gadget from British drive maker Secure Drives forges off into Mission Impossible territory with a genuine, physical 'self-destruct' command which...
-

 84Password
84PasswordSecure password: CyberVor hoard of 1.2 billion details ‘used in attack’
Hosting provider Namecheap said that it has come under attack from hackers apparently using the “Cybervor” hoard of 1.2 billion usernames and...
-

 172Privacy
172Privacy‘Secure’ Blackphone hacked in 5 minutes
An ultra-secure phone claimed to be the first privacy-focused smartphone on sale swiftly fell victim to a security researcher - who hacked...
-

 484Privacy
484PrivacyBlackphone ultra‑secure Android handset goes on sale
The Blackphone, a new super-secure Android handset is now on sale. The Blackphone offers encryption technology that makes snooping on calls or...
-

 398Password
398PasswordSamsung raises Apple an eyeball with ultra‑secure iris‑scan smartphones
High-end Samsung phones could soon ship with a biometric scanner which puts fingerprint-swipe buttons (as seen in both Samsung and Apple’s flagship...
-

 96How To
96How ToMaster of Mavericks: How to secure your Mac using Apple’s latest update
Apple’s Mavericks update was the first free update to Mac OS X – itself a big step forward for security, as all...






