Search results for "Secure"
-

 195How To
195How ToHow to secure your website?
Nowadays, websites are necessary for most of the businesses and especially in e-commerce. Every attacker knows that your site holds customers data....
-
 172Incidents
172IncidentsHow to remote hijack computers using Intel’s insecure chips: Just use an empty login string
Exploit to pwn systems using vPro and AMT. Code dive You can remotely commandeer and control computers that use vulnerable Intel chipsets...
-
 156Vulnerabilities
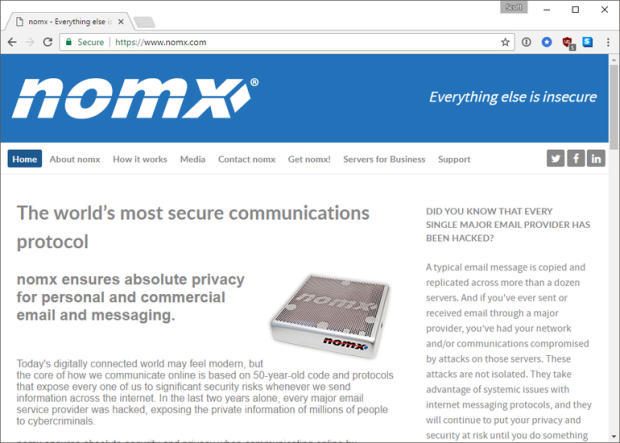
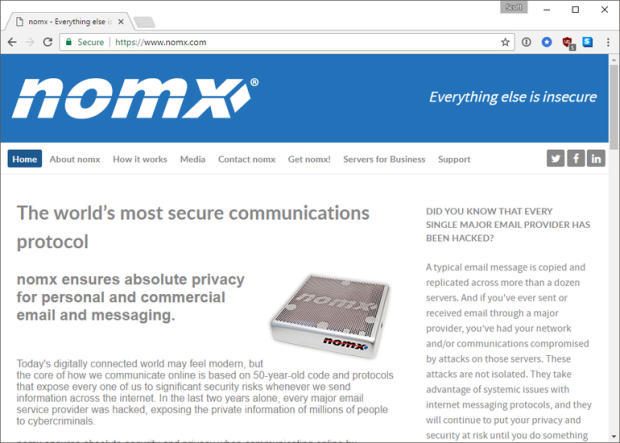
156VulnerabilitiesNomx, the “most secure” email service, can be easily hacked, say researchers
I was recently invited to take part in some research by BBC Click, alongside Professor Alan Woodward, to analyse a device that...
-
 279Hacked
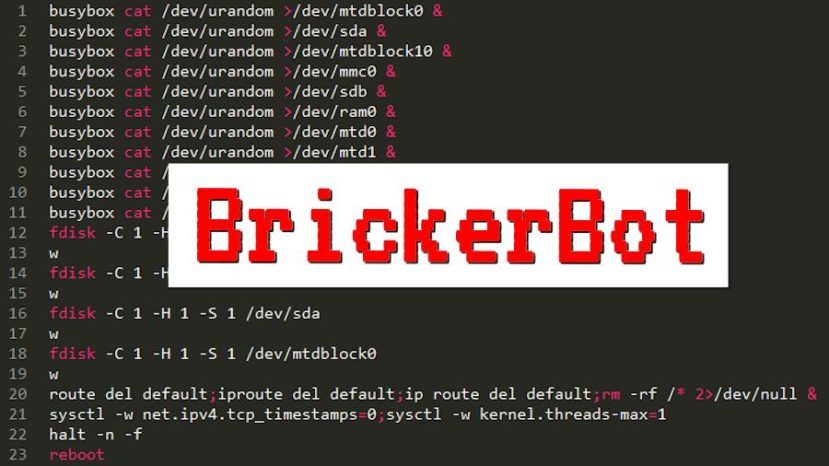
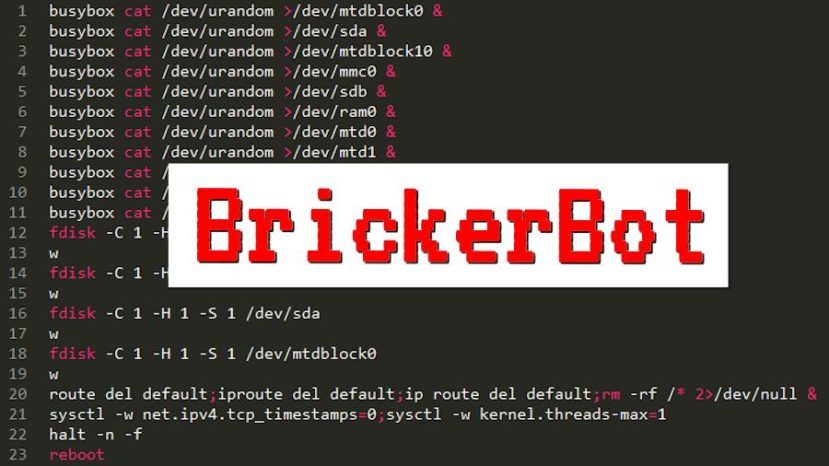
279HackedBrickerBot: “The Doctor’s” PDoS Attack Has Killed Over 2 Million Insecure Devices
Short Bytes: A hacker, who goes by the name Janit0r, claims to have bricked more than 2 million insecure IoT devices. This hardware-damaging...
-
 83Malware
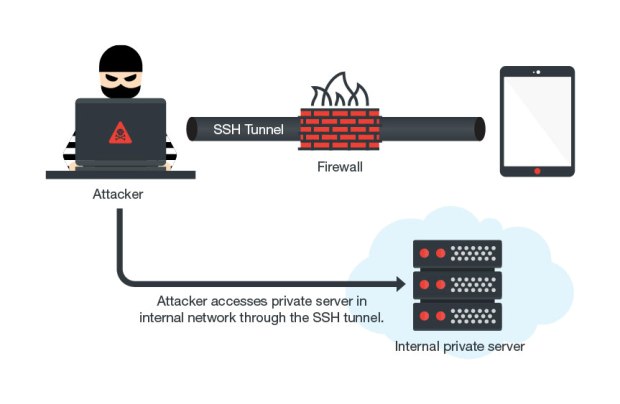
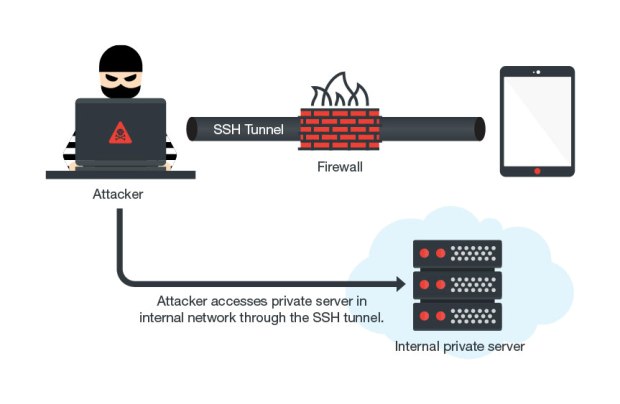
83MalwareMilkyDoor Android Malware Uses SSH Tunnels to Access Secure Corporate Networks
A new form of Android malware, named Milkydoor, uses remote port forwarding via Secure Shell (SSH) tunnels to hide malicious traffic and...
-
 164Data Security
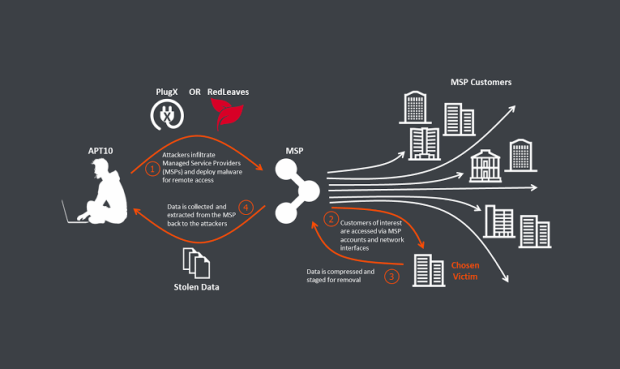
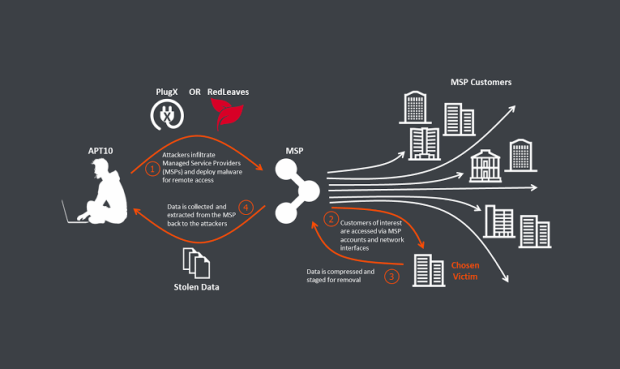
164Data SecurityChinese Group Is Hacking Cloud Providers to Reach Into Secure Enterprise Networks
A cyber-espionage group that first surfaced in 2009 is using a novel tactic into hacking its targets by first breaching one of...
-
 113Geek
113GeekTelegram Update Allows Users to Make Secure, AI-Powered Voice Calls
Telegram, the secure instant messaging service has issued an update v.3.18 allowing users to make and receive end-to-end encrypted calls over WiFi, 3G, and...
-

 142Malware
142Malware16 years of Mac OS X: Secure but not invincible to malware
Mac OS X is still secure 16 years after its creation, but increasingly being targeted by cybercriminals. No operating system is 100%...
-

 169Vulnerabilities
169VulnerabilitiesDenuvo forgets to secure server, leaks years of messages from game makers
Massive log file includes user complaints, apparently legitimate developer requests. The developers at Denuvo have been in the news thanks to cracks against...
-
 207Operating Systems
207Operating SystemsLinux Kodachi3 – Secure Open Source Linux Distribution
Linux Kodachi operating system is based on Debian 8.6 it will provide you with a secure, anti forensic, and anonymous operating system...
-

 203How To
203How ToHere is The Best Way To Securely Wipe Sensitive Data From Your Computer
Hi there guys. Today in this post, we are going to discuss the best way to securely wipe all the sensitive data...
-

 253Incidents
253IncidentsA Benevolent Hacker Is Warning Owners of Unsecured Cassandra Databases
An unknown hacker is accessing public and unsecured Apache Cassandra databases and adding an extra table through which it warns server owners...
-

 196Cyber Attack
196Cyber AttackD-Link Fail to Secure Its Routers and IP Cameras From Hackers
The united states’ trade watchdog has sued Taiwan-primarily based D-link, alleging that the lax protection left its merchandise at risk of hackers....
-

 167Android Hacking
167Android HackingInsecureBankv2 – Vulnerable Android Application
Information security awareness training may include several demo that describe how attacker may exploit vulnerabilities on system to gain full control on...
-
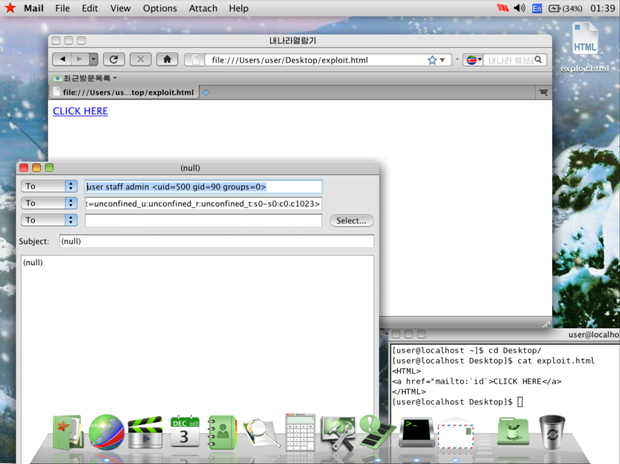
 199Data Security
199Data SecurityNorth Korea’s “Super-Secure” Red Star OS Can Be Hacked with Just a Link
Security researchers find easy to exploit vulnerability. North Korea is one of those countries whose governments pushed for the migration to a...
-

 348Data Security
348Data SecurityTor Phone Is The “Super-secure Version Of Android”, Developed By Tor Project
Short Bytes: The Tor Project has released Tor Phone–a privacy-focused and secure version of Android mobile OS. It’s based on Copperhead OS,...
-
 245Data Security
245Data SecurityCERT to Microsoft: Don’t Kill EMET, Windows 10 Is Not as Secure as You Think
Will Dormann, a Vulnerability Analyst for the US-CERT Coordination Center (CERT/CC), is advising Microsoft to continue developing EMET because Windows 10 does...
-
 328How To
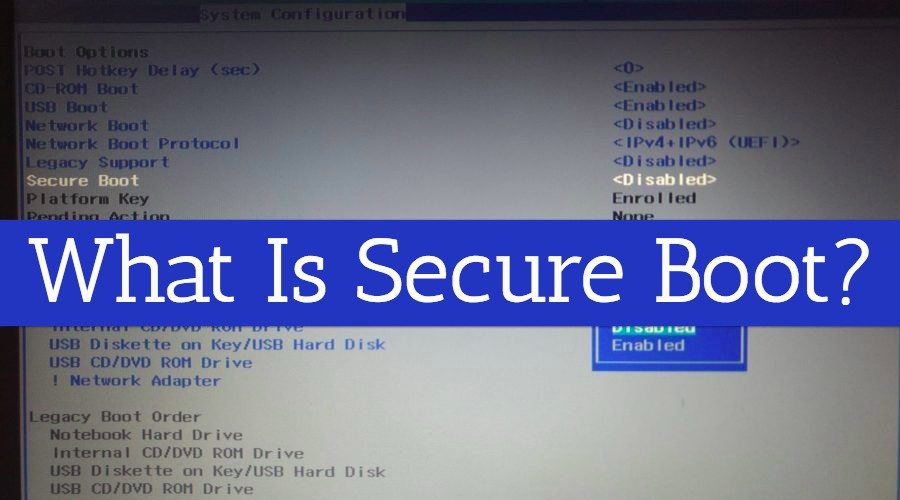
328How ToHow To Enable/Disable Secure Boot In Windows 8, 8.1, And 10?
Short Bytes: Windows 8 and later versions of Windows come with UEFI Firmware settings which allow a user to disable any external...
-
 311News
311NewsUnsecured MongoDB Database: 58M Business Firm Accounts Leaked
Unsecure Database Leads to Exploitation of Personal Details of 58M Users of in-house data management firm Modern Business Solutions. The famous database...
-

 195How To
195How ToHow To Secure Your Facebook/Gmail Accounts From Hackers
How To Secure Your All Social Media Accounts From Hackers? Social Media is a tool in every single person’s hand to share...
-
 252Geek
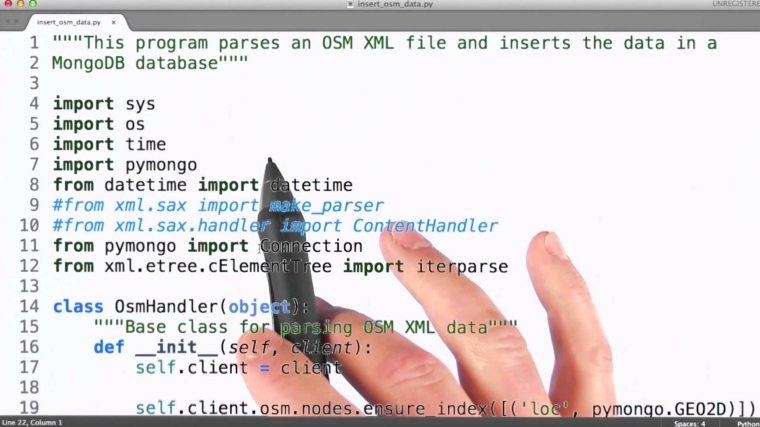
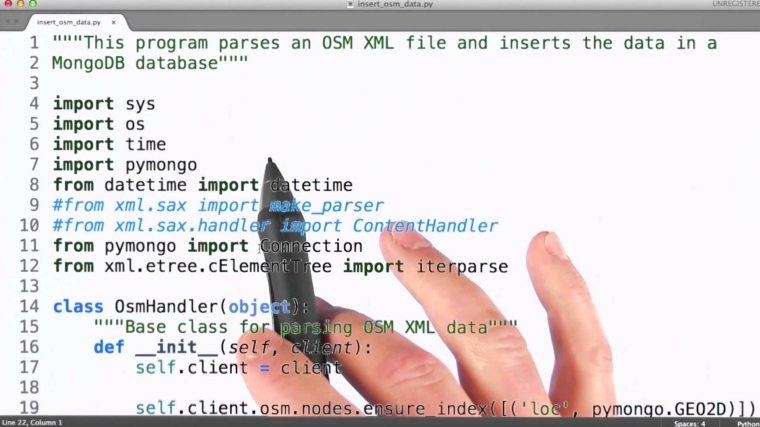
252GeekResearchers Send Secure Passwords Using the Human Body
Sending passwords through an Internet connection or Bluetooth is not safe anymore so these researchers have developed a technology that sends passwords...






