Search results for "Secure"
-

 185Geek
185GeekORWL — First Open Source And Physically Secure PC, Runs Linux And Windows
Short Bytes: ORWL is the first open source, physically secure computer. Using a secure microcontroller (MCU) and an ‘active clamshell mesh’, the device makes sure...
-
 170Hacked
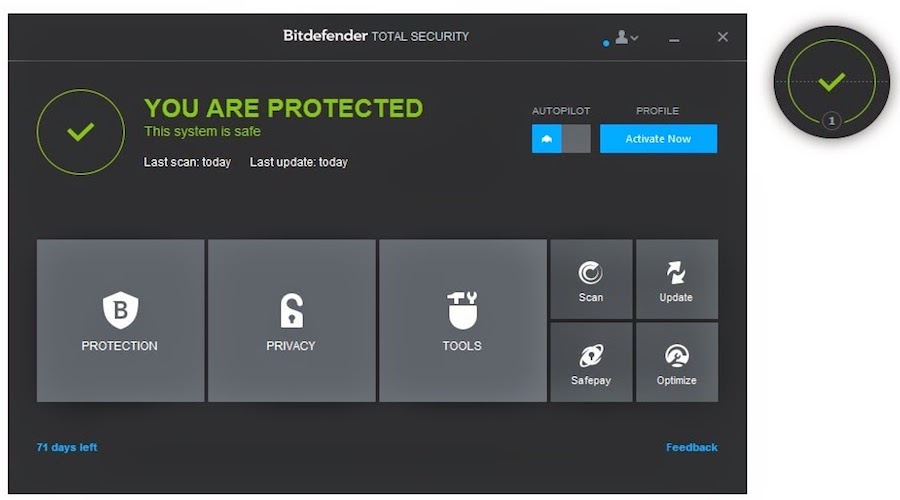
170HackedBitdefender 2017 Is Here To Kill Ransomware And Secure Your Wi-Fi Connection
Short Bytes: Bitdefender is here with its new lineup of revamped antivirus solutions. This range includes Bitdefender Internet Security 2017, Bitdefender Total Security...
-
 286Hacked
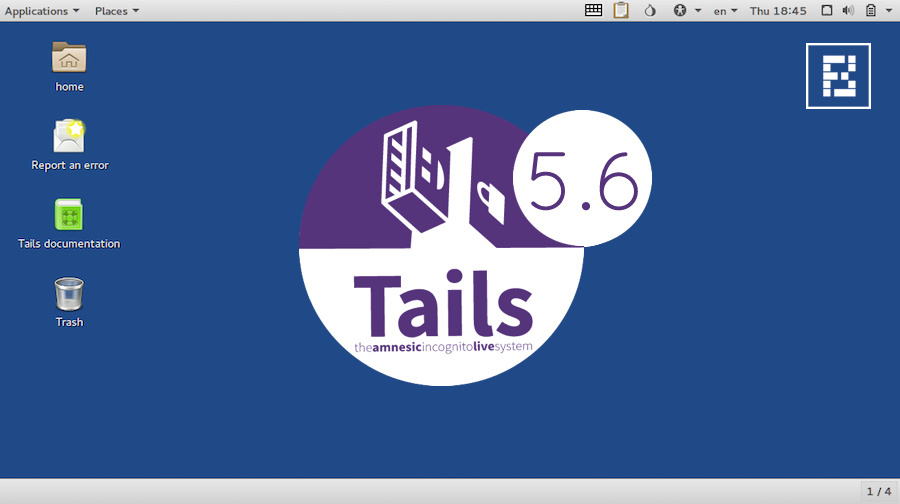
286HackedTails 2.6 — Ultra-secure Linux OS Used By Snowden Gets Updated Tor And Kernel
Short Bytes: The development team of Tails, the anonymity-focused Debian GNU/Linux-based Live CD operating system, is here with its latest release. Tails...
-
 339Geek
339Geek11 easy tips to secure your Mac against hackers
Today, it is still true that Mac has less malware problem than its counterparts Windows and Android. But, it does not mean...
-

 117Vulnerabilities
117VulnerabilitiesSWEET32 Attack: 3DES and Blowfish Ciphers Considered Insecure
HTTPS and VPN traffic broken with new semi-practical attack. Two scientists from the French Institute for Research in Computer Science and Automation (INRIA)...
-

 300Cyber Attack
300Cyber AttackOMG!! Accidentally Microsoft leaked backdoor Keys to BYPASS UEFI secure boot
Keys to BYPASS UEFI secure boot Microsoft accidentally leaked the Secret keys to BYPASS UEFI secure boot that allow hackers to unlock devices...
-

 205Hacked
205HackedMicrosoft Creates Backdoor In Windows, Accidentally Leaks UEFI Secure Boot Keys
Short Bytes: Two researchers reported that Microsoft accidently compromised the golden keys to its UEFI Secure boot feature. The golden keys allow...
-

 169Vulnerabilities
169VulnerabilitiesWhat really happened in mass Telegram secure messenger hack
Were 15 million Iranian accounts truly placed at risk?Telegram has fought back against researcher claims that Iranian cyberattackers have managed to compromise...
-

 336Data Security
336Data SecurityHow to secure your cyber infrastructure from threats like ransomware?
The Internet is a great place to do business and cybercriminals are aware of that fact so how can you protect your networks,...
-

 230Hacked
230HackedRiffle: MIT Creates New Anonymity Network Which Is More Secure Than TOR
Short Bytes: Researchers at MIT and EPFL have come up with a new anonymity network that is said to be more secure...
-

 257Social Media
257Social MediaHow to secure your social media accounts
Social media platforms are increasingly being targeted, as Facebook CEO Mark Zuckerberg found out earlier this month. Here, we look at how...
-

 198Cyber Crime
198Cyber CrimeCash machines turn 49 today: Are ATMs really that secure?
Forty-nine years after the first ATM was installed in London, we ask how secure our cash machines are today?
-

 204How To
204How ToHow to delete your smartphone data securely before selling your device
Understanding how to delete your smartphone data before selling your device is important if you want to protect your privacy and keep...
-
 391Data Security
391Data SecurityHow to do secure data destruction of information from storage devices?
There are statistical evidences supported by data destruction companies which present that in countries like Mexico, Brazil, United States, Colombia, Costa Rica,...
-
 283Hacked
283HackedHow To Create A Super Secure Password To Defeat Hackers
Short Bytes: Deciding a security-focused password is tougher that one might think. Even the most security-conscious users commit the mistake of forming...
-

 153Data Security
153Data SecurityQatar National Bank Declares Systems ‘Fully Secure’ Sequel To Cyber-attack
Following the recent security breach suffered by the Qatar National Bank has assured that its systems are “fully secure”. Sequel to a...
-

 177Data Security
177Data SecurityHacker exposes thousands of insecure desktops that anyone can remotely view
VNC Roulette allows you to randomly view insecure desktops accessible over the internet. Recently, a new website has come up on the Internet,...
-
 203Hacked
203HackedSubgraph OS: Secure, Free, Open Source Linux Operating System For Non-technical Users
Short Bytes: To answer your security related concerns, Subgraph OS is here as a free, secure, open source Linux operating system for...
-
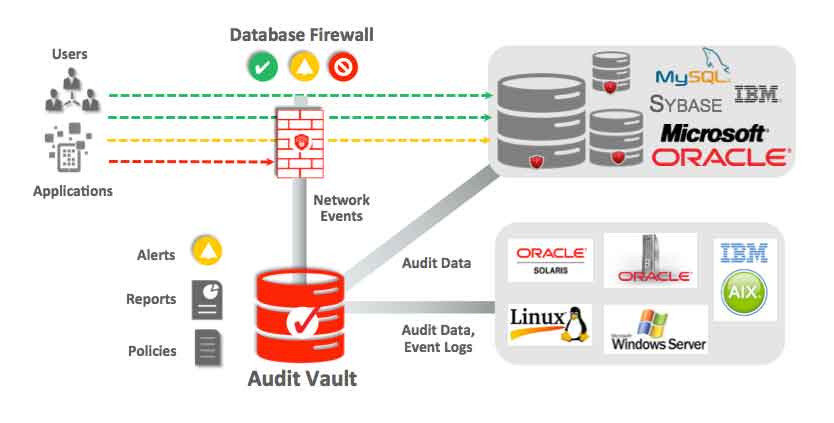
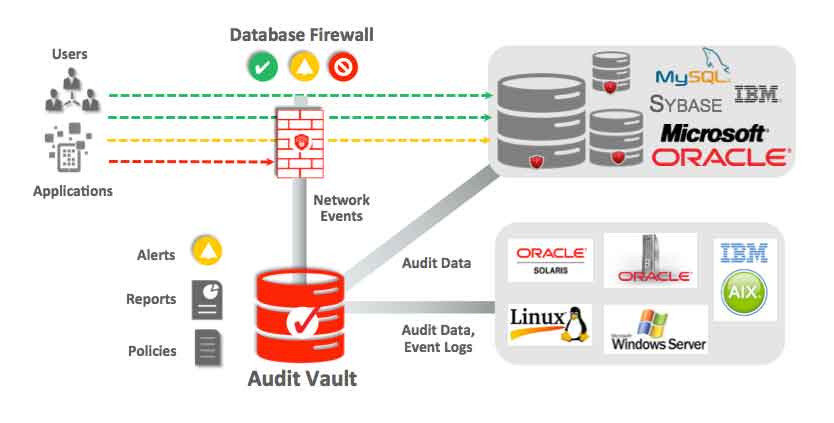 110Data Security
110Data SecurityHow to secure databases?
Databases can be a treasure trove of confidential data. Normally most databases contain confidential information, private data of companies, people, intellectual property,...
-

 195Data Security
195Data SecurityGmail to warn you if your friends aren’t using secure e-mail
Messages coming to or from non-encrypted sources will be flagged by Google. Google has confirmed a number of changes to Gmail with...
-

 222Hacked
222HackedThese Vigilante Hackers Aim To Hack 200,000 Routers To Make Them More Secure
Short Bytes: Remember the white hat hackers — The White Team — responsible for creating the Linux.Wifatch malware last October? The same hackers...






