Search results for "Secure"
-

 148Articles
148ArticlesHow to Secure Your Mid-Size Organization From the Next Cyber Attack
If you are responsible for the cybersecurity of a medium-sized company, you may assume your organization is too small to be targeted....
-

 194How To
194How ToHow To Ensure Spam Protection And Secure Your Website
Spam Protection It is no secret spammers can be very harmful for any website, by flooding the comment section, consuming website resources,...
-
 308Geek
308GeekThe Advantages of a More Secure and Safer Blockchain
Blockchain technology has many uses and advantages over other types of ledger-based technology. One aspect of blockchain technology that is especially valuable...
-
 307Cryptocurrency
307Cryptocurrency3 Hacker-Proof Tips You Need to Know to Secure Your Cryptocurrencies
Investing in cryptocurrencies has become a worldwide phenomenon over the last couple of years. You talk to any investor and the first...
-
 364Malware
364MalwareCyber Attack Prevention Checklist to Keep Your Business Safe & Secure From Hackers
Cyber Security manages business risk during the full cycle(monitor, assess, advise, re-mediate). It fights against the cybercrime: detection of attacks and fraud...
-
 165Articles
165ArticlesSignal Secure Messaging App Now Encrypts Sender’s Identity As Well
Signal, the popular end-to-end encrypted messaging app, is planning to roll out a new feature that aims to hide the sender’s identity...
-
 211Articles
211ArticlesWindows Built-in Antivirus Gets Secure Sandbox Mode – Turn It ON
Microsoft Windows built-in anti-malware tool, Windows Defender, has become the very first antivirus software to have the ability to run inside a...
-

 185Data Security
185Data SecurityEthical hackers, the US government’s alternative to secure medical devices
This government institution is opting to work with ethical hackers and their researches to protect vulnerable medical devices The work of malicious...
-

 354Data Security
354Data SecurityHow to Choose the Most Secure Software for your Business
When it comes to protecting your business, how do you choose the best available and secure software on the market? Security software...
-

 175Infosec
175InfosecBest Way to Accelerate and Secure Your Website From Top Common Web Threats
Web Applications Security becomes essential as more and more data gets stored in web applications. Web Security assessment is a wide-ranging process...
-

 359Data Security
359Data SecurityThe best practices to secure your web applications
Make sure your organization is aware of the best ways to keep out of harm your critical applications An organization faces both...
-

 332Infosec
332InfosecMost Important Cybersecurity Consideration to Secure Your Company’s Integrity
When it comes to cybersecurity then no any business would be able to ignore it! In fact, if we consider the reports...
-

 281Data Security
281Data SecurityNew Instagram security measures are not that secure
The social network will try with third-party authentication to reinforce its security Cyber security organization specialists from the International Institute of Cyber...
-

 174News
174News4 Creative Ways to Secure Surveillance Cameras from known Vulnerability
Corporate systems are categorized into two: Internally developed Developed by a vendor Internally developed systems are the exact tailor fit solutions that...
-

 330Cyber Crime
330Cyber CrimeIranian Hackers are Developing Ransomware to Secure Bitcoin
Cybersecurity experts have come up with the warning that Iranian Hackers, in the face of the economic issues that the country is...
-

 186How To
186How ToDoes Your Antivirus Software Work? – How To Test it Securely
In a world bombarded with malware threats, you never know what’s lurking around the corner. Viruses are always looking for an opportunity...
-

 306News
306NewsHere’s How You Can Secure Your Google Chrome From Cyberattack
Google Chrome is definitely one of the most popular web browsers being used today—but could it also be one of the riskiest?...
-
 256Hacked
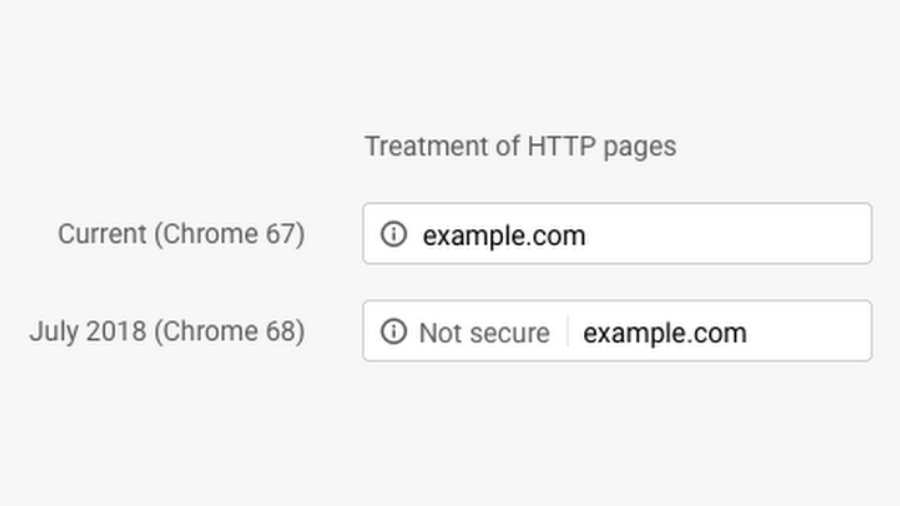
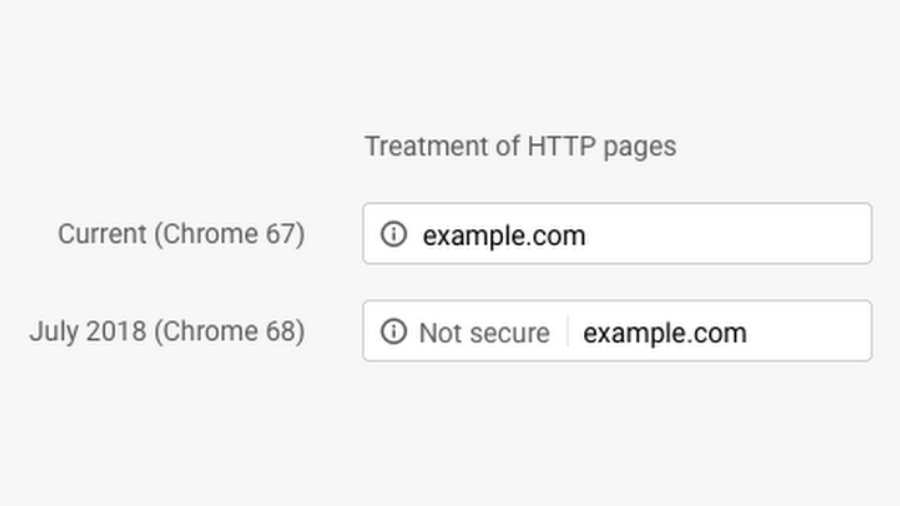
256HackedHere’s Why Chrome Is Now Showing Millions of Websites As “Not Secure”
Google is taking the privacy quite seriously, and the new Chrome security update will undoubtedly put a significant toll on all your...
-

 273Cyber Crime
273Cyber CrimeHow Can Vietnam’s New Cybersecurity Law Secure Safety For All?
The new Cyber Security Law that Vietnam has adopted, and which will come into effect on January 1, 2019, seeks to ensure...
-
 168Data Security
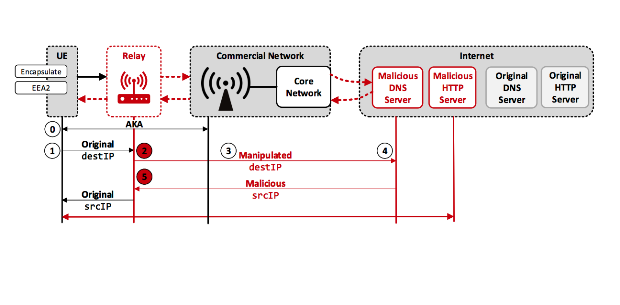
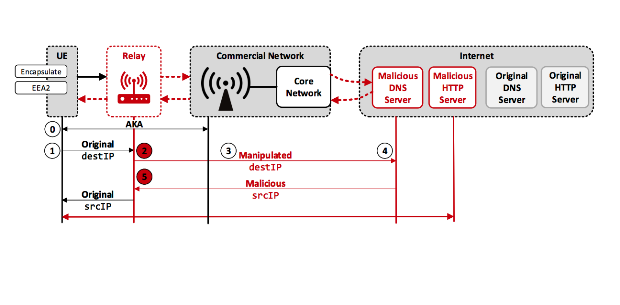
168Data SecurityLTE wireless connections used by billions aren’t as secure as we thought
LTE was supposed to fix security and privacy shortcomings—now it’s broken, too. The Long Term Evolution mobile device standard used by billions...
-

 313News
313NewsWhy Password-Based Authentication is Not Secure
FIDO (Fast Identity Online) Alliance and W3C (World Wide Web Consortium) proposed a web authentication standard that aims to replace the traditional...






