Search results for "Threat"
-

 3.4KMalware
3.4KMalwareLockBit 3.0 Ransomware: Inside the Cyberthreat That’s Costing Millions
U.S. government agencies have released a joint cybersecurity advisory detailing the indicators of compromise (IoCs) and tactics, techniques, and procedures (TTPs) associated...
-
 2.2KMalware
2.2KMalwareA New Security Category Addresses Web-borne Threats
In the modern corporate IT environment, which relies on cloud connectivity, global connections and large volumes of data, the browser is now...
-
 5.3KMalware
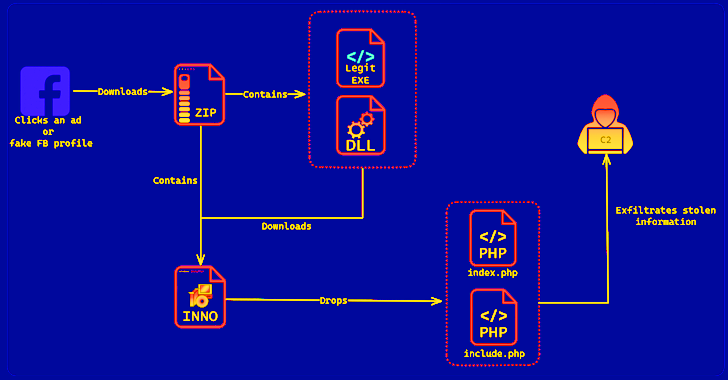
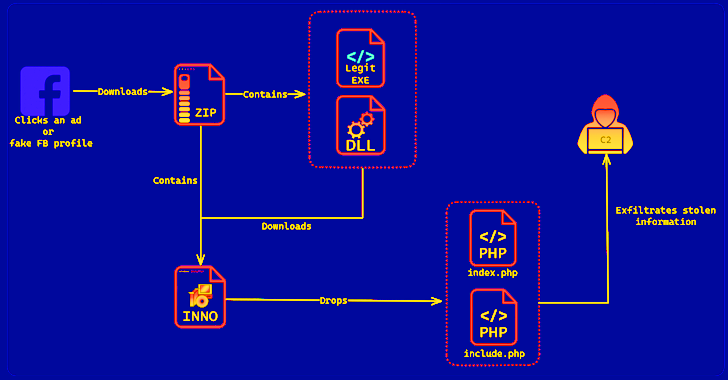
5.3KMalwareSYS01stealer: New Threat Using Facebook Ads to Target Critical Infrastructure Firms
Cybersecurity researchers have discovered a new information stealer dubbed SYS01stealer targeting critical government infrastructure employees, manufacturing companies, and other sectors since November...
-

 1.5KCyber Attack
1.5KCyber AttackHydrochasma: New Threat Actor Targets Shipping Companies and Medical Labs in Asia
Shipping companies and medical laboratories in Asia have been the subject of a suspected espionage campaign carried out by a never-before-seen threat...
-
 4.9KMalware
4.9KMalwareHow to Detect New Threats via Suspicious Activities
Unknown malware presents a significant cybersecurity threat and can cause serious damage to organizations and individuals alike. When left undetected, malicious code...
-

 5.0KCyber Attack
5.0KCyber AttackNew Threat Actor WIP26 Targeting Telecom Service Providers in the Middle East
Telecommunication service providers in the Middle East are being targeted by a previously undocumented threat actor as part of a suspected intelligence...
-

 3.6KMalware
3.6KMalwareFinancially Motivated Threat Actor Strikes with New Ransomware and Clipper Malware
A new financially motivated campaign that commenced in December 2022 has seen the unidentified threat actor behind it deploying a novel ransomware...
-

 2.2KMalware
2.2KMalwareNew Threat: Stealthy HeadCrab Malware Compromised Over 1,200 Redis Servers
At least 1,200 Redis database servers worldwide have been corralled into a botnet using an “elusive and severe threat” dubbed HeadCrab since...
-

 4.6KMalware
4.6KMalwareNew Analysis Reveals Raspberry Robin Can be Repurposed by Other Threat Actors
A new analysis of Raspberry Robin’s attack infrastructure has revealed that it’s possible for other threat actors to repurpose the infections for...
-
 3.0KMalware
3.0KMalware2022 Top Five Immediate Threats in Geopolitical Context
As we are nearing the end of 2022, looking at the most concerning threats of this turbulent year in terms of testing...
-

 4.9KCyber Attack
4.9KCyber AttackZerobot Botnet Emerges as a Growing Threat with New Exploits and Capabilities
The Zerobot DDoS botnet has received substantial updates that expand on its ability to target more internet-connected devices and scale its network....
-

 3.1KIncidents
3.1KIncidentsAustralian telecom company TPG hacked as threat actor got access to a server that hosts the email accounts of 15,000 clients
This week, an announcement was made by TPG Telecom in Australia stating that an unidentified threat actor had acquired unauthorized access to...
-

 4.7KMalware
4.7KMalwareRoyal Ransomware Threat Takes Aim at U.S. Healthcare System
The U.S. Department of Health and Human Services (HHS) has cautioned of ongoing Royal ransomware attacks targeting healthcare entities in the country....
-
 816Malware
816MalwareDarknet’s Largest Mobile Malware Marketplace Threatens Users Worldwide
Cybersecurity researchers have shed light on a darknet marketplace called InTheBox that’s designed to specifically cater to mobile malware operators. The actor...
-

 247Vulnerabilities
247Vulnerabilities3 vulnerabilities in Zoom Client and Zoom Rooms allows threat actor to become admin of the machine
According to the most recent research, three recently found security flaws in Zoom can grant an attacker access to root or SYSTEM...
-
 1.5KData Security
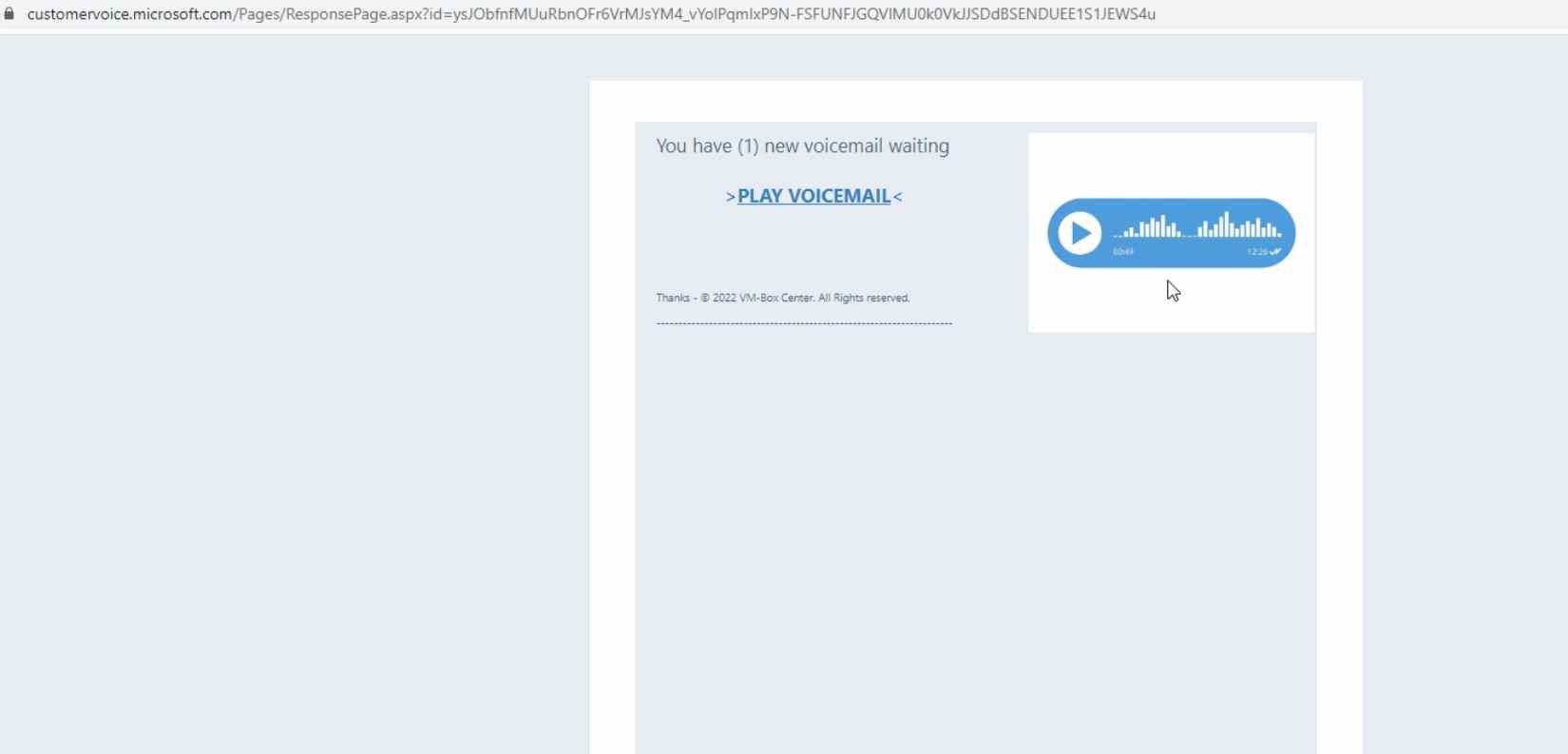
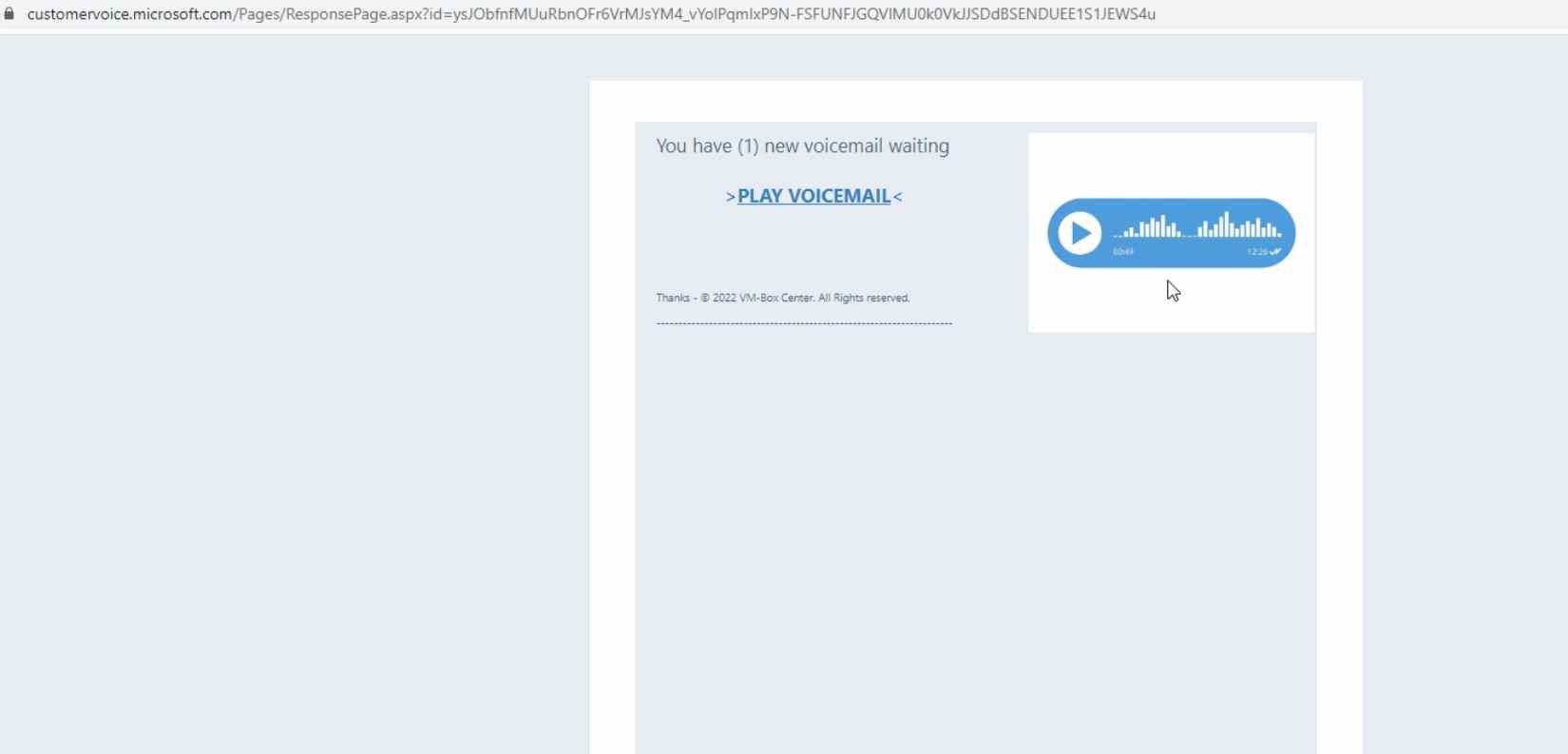
1.5KData SecurityDon’t open emails from Microsoft Dynamics 365. Threat actors are exploiting its flaws to send phishing emails with legitimate Microsoft links
Microsoft’s Dynamics 365 Customer Voice is a software that is primarily used to collect customer feedback.It may be utilized to gather data...
-
 1.4KVulnerabilities
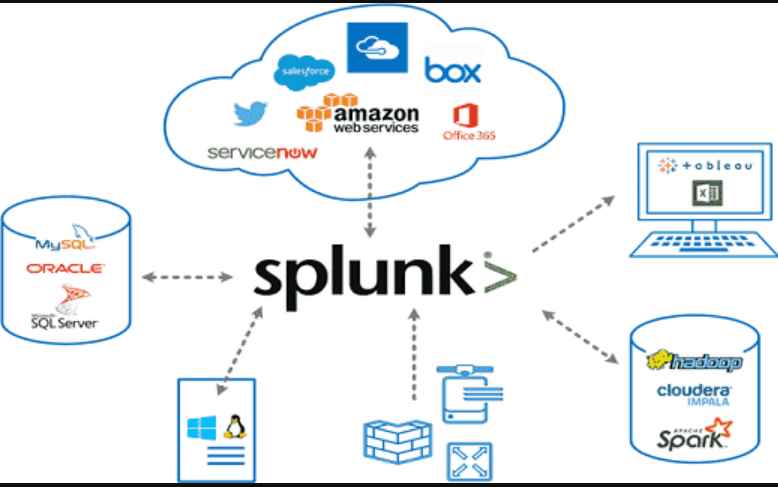
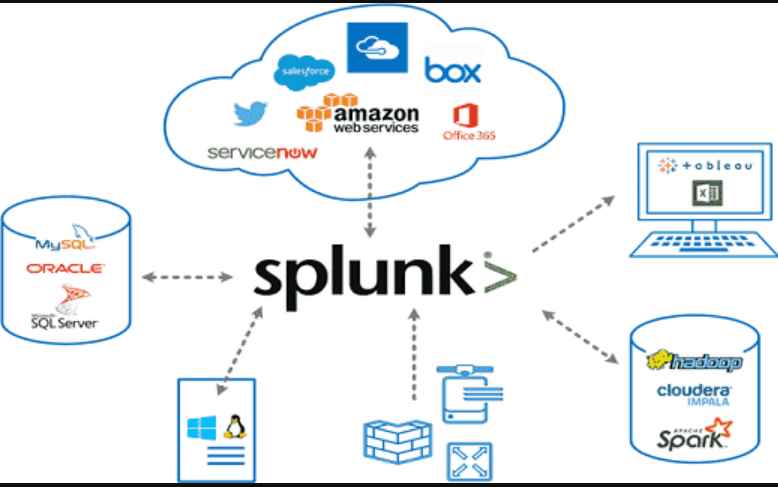
1.4KVulnerabilitiesEight high-severity vulnerabilities in Splunk Enterprise Software allow threat actors to take control of a network
With the use of the Splunk software, real-time data can be collected, indexed, and corroborated in a searchable repository from which graphs,...
-
 336Vulnerabilities
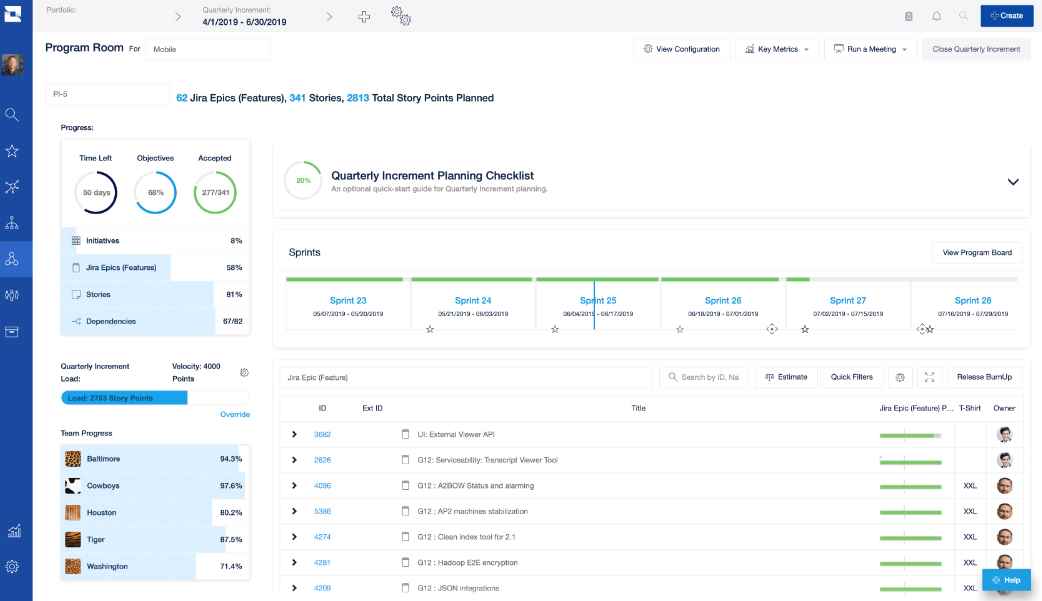
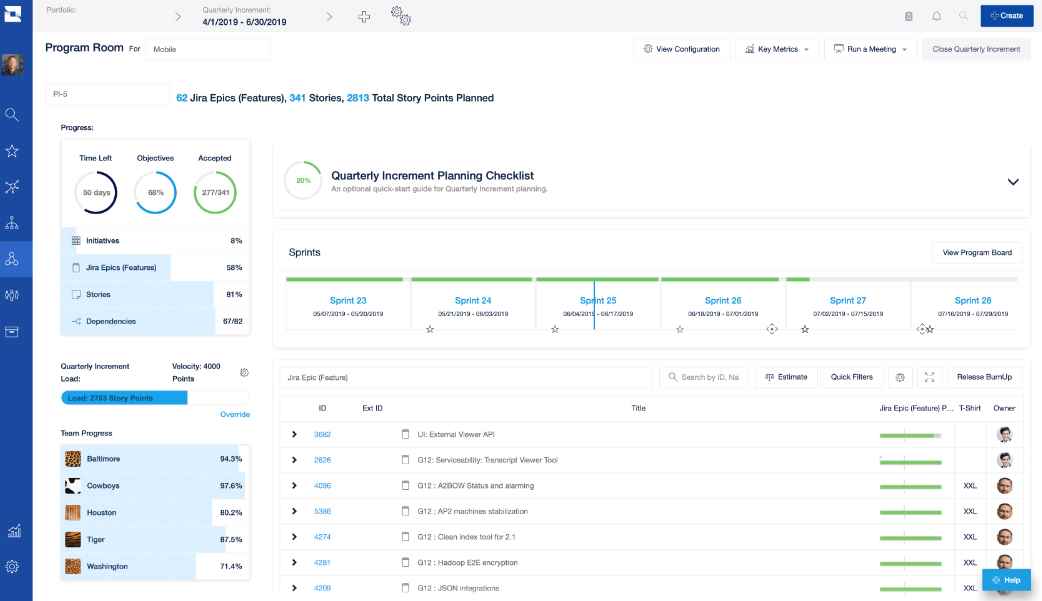
336VulnerabilitiesVulnerability in Atlassian Jira Align allows threat actor to access whatever the SaaS client has in their Jira deployment or simply take the entire thing down
Jira Align is a software-as-a-service (SaaS) platform that enables businesses to grow their cloud installations of the wildly popular bug tracking and...
-

 3.8KLeaks
3.8KLeaksAfter hackers threatened to target celebrities, Medibank confirmed the impact of a larger cyberattack
On Tuesday, Australian private insurer Medibank stated that a recent disclosed cyberattack affects more customers’ data than first believed. Days after hackers...
-

 4.5KData Security
4.5KData SecurityHow Chinese threat actors are using recently discovered zero day flaws in office and Sophos firewall
By deploying a new Trojan named LOWZERO, integrated into an espionage campaign aimed against Tibetan organizations, the Chinese APT known as TA413...
-

 4.0KVulnerabilities
4.0KVulnerabilities5 Network Security Threats And How To Protect Yourself
Cybersecurity today matters so much because of everyone’s dependence on technology, from collaboration, communication and collecting data to e-commerce and entertainment. Every...






