Search results for "Threat"
-

 439News
439NewsMicro Fixes Vulnerability in an Anti-Threat Toolkit
Trend Micro recently patched its Anti-Threat Toolkit (ATTK) for a high-grade remote software execution vulnerability. The Trend Micro ATTK tool lets users...
-

 446Exploitation Tools
446Exploitation ToolsRITA – Real Intelligence Threat Analytics
RITA is an open source framework for network traffic analysis. The framework ingests Bro/Zeek Logs in TSV format, and currently supports...
-
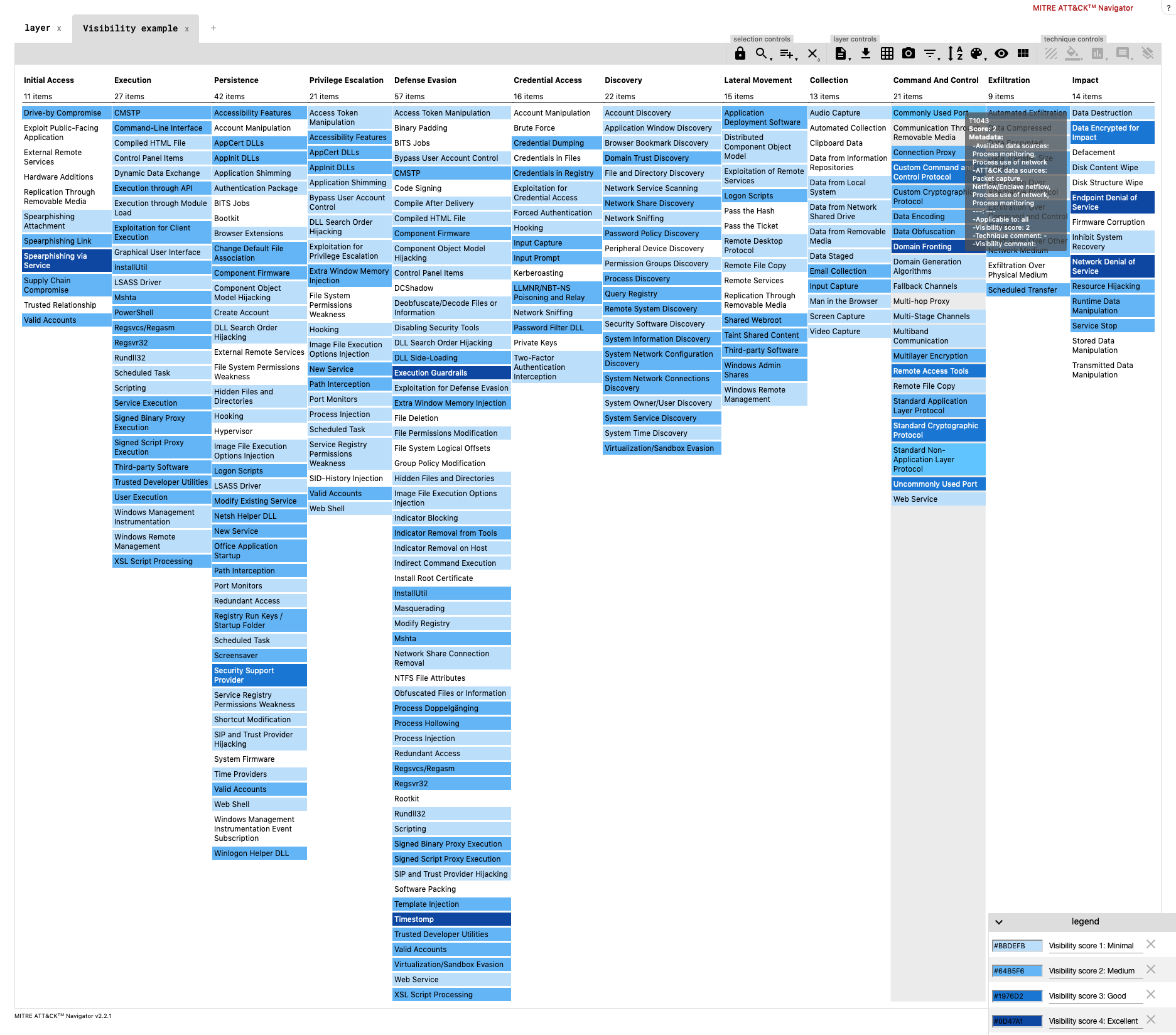
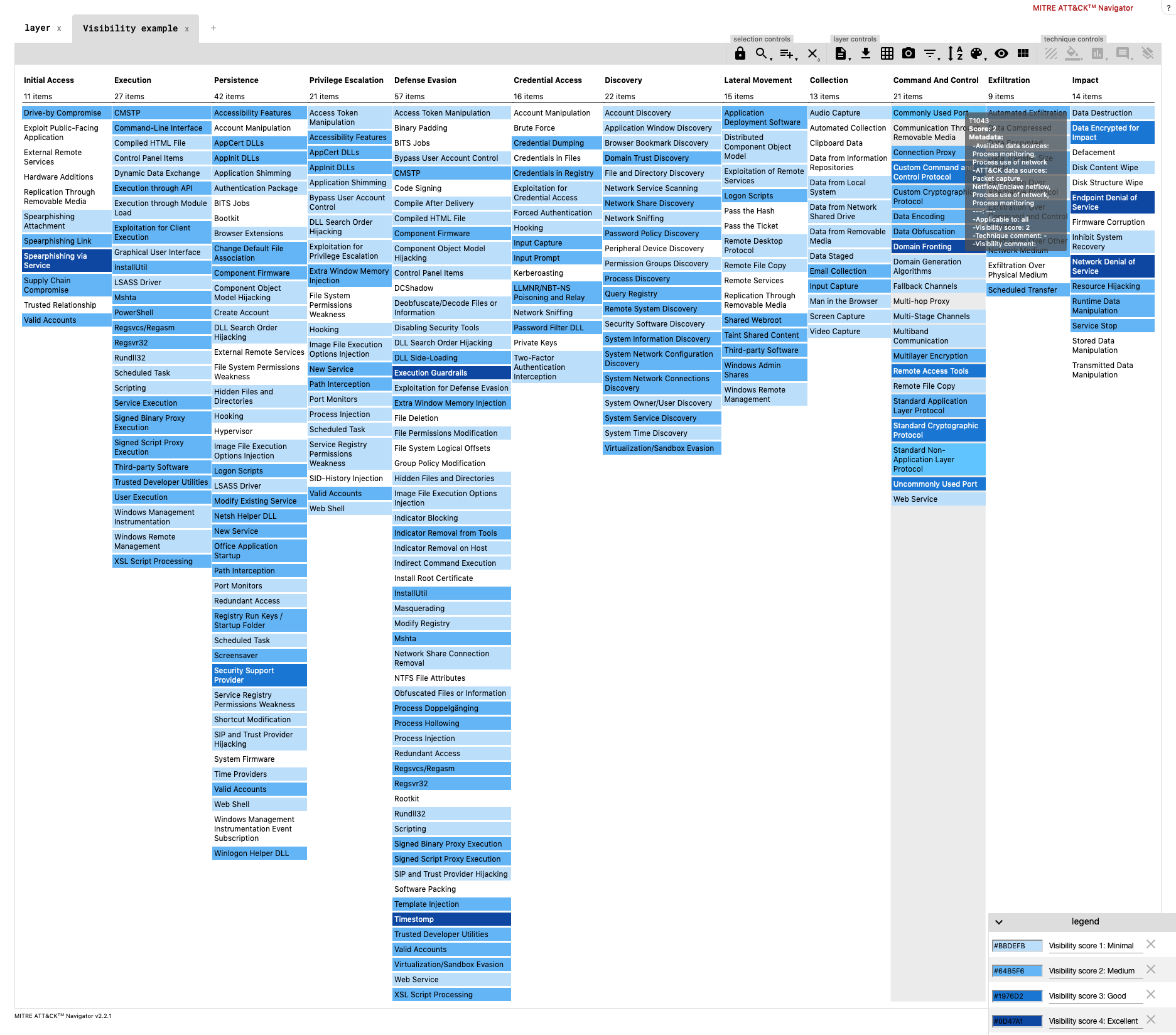 630Incident Response
630Incident ResponseDeTTecT – Detect Tactics, Techniques & Combat Threats
DeTT&CT aims to assist blue teams using ATT&CK to score and compare data log source quality, visibility coverage, detection coverage and threat...
-
Security Tools
Tylium – Data for Intrusion Detection, Security Analytics and Threat Hunting
These files contain configuration for producing EDR (endpoint detection and response) data in addition to standard system logs. These configurations enable...
-
 497Data Security
497Data SecurityHow your work phone could be a huge security threat
You know about cyber security and mobile network vulnerabilities. You’ve heard of DDoS attacks. You might have even moved on from your...
-
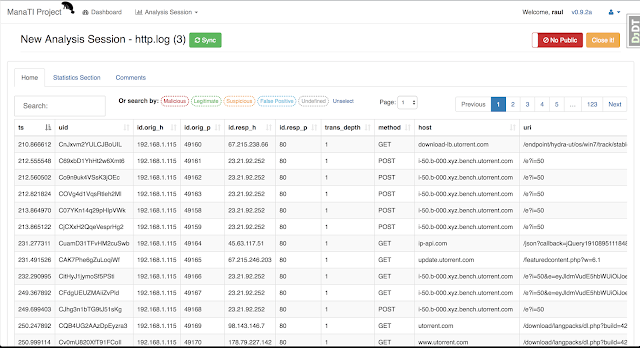
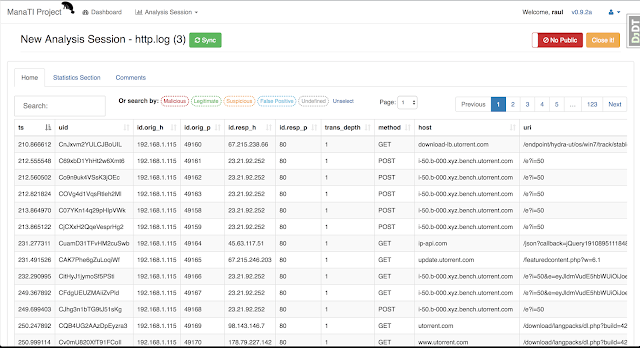 422Vulnerability Analysis
422Vulnerability AnalysisManaTI – A Web-Based Tool To Assist The Intuitive Threat Analysts
Machine Learning for Threat Intuitive Analysis The goal of the ManaTI project is to develop machine learning techniques to assist an...
-

 530How To
530How ToHow to Protect Your Online Store from Cyber Threats
Owning an online store can be a fabulous and lucrative venture in today’s marketplace. With so many sales and transactions taking place...
-

 379News
379NewsWhat Is Advanced Threat Protection?
Advanced Threat Protection, or ATP, is a type of security solution specifically designed to defend a network or system from sophisticated hacking...
-

 5.2KCyber Attack
5.2KCyber AttackAdvanced Persistent Threat: What You Need to Know
Today, criminal organizations no longer attack corporations and businesses physically with weapons. Instead, they use computers and malware, aiming to steal vital...
-

 242How To
242How To3 Ways Attack Simulations Can Protect Enterprises Against Advanced Persistent Threats
Enterprises face the tough challenge of ensuring the security of their IT infrastructure. Data breach attempts have now become commonplace as customer...
-

 320Threat Intelligence
320Threat IntelligenceThreatHunting – A Splunk App Mapped To MITRE ATT&CK To Guide Your Threat Hunts
This is a Splunk application containing several dashboards and over 120 reports that will facilitate initial hunting indicators to investigate. You obviously...
-

 293News
293NewsChina Threatens To Fight Back If India Blocks Huawei
Huawei is stuck in a political tug of war between different countries. After facing a brief ban in the US, the world’s...
-
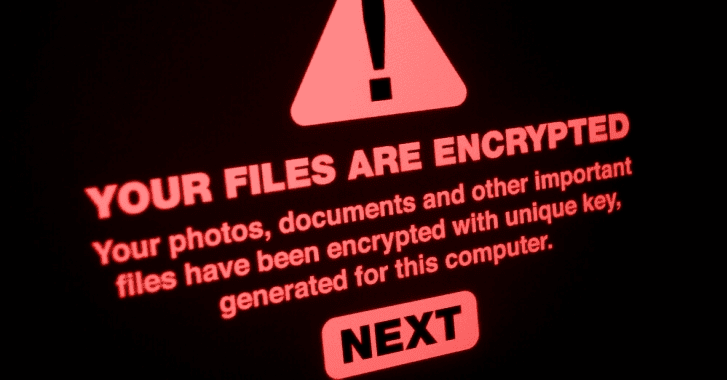
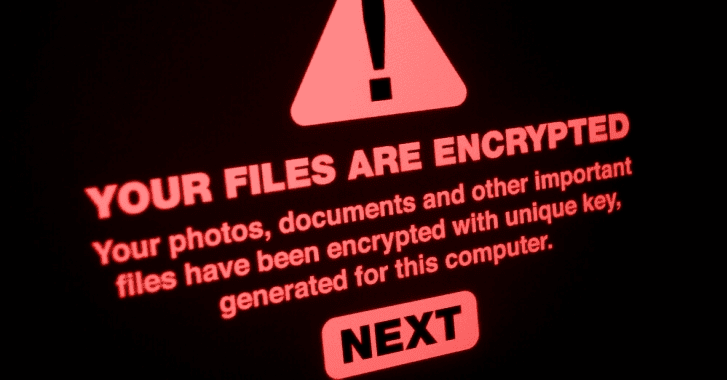 330Ransomware
330RansomwareProtecting Your Network & PC From The Impending Threat of Ransomware
Digital extortion continues to pose a threat everywhere. According to the Cyber Advisor newsletter, incidents of ransomware attacks are only going to...
-

 333News
333NewsAndroid “Sex Simulator” Ransomware Threatens Users, Spreads Via SMS
A new family of Android ransomware has been discovered, which spreads via SMS. This comes after a two-year decline in the spread...
-
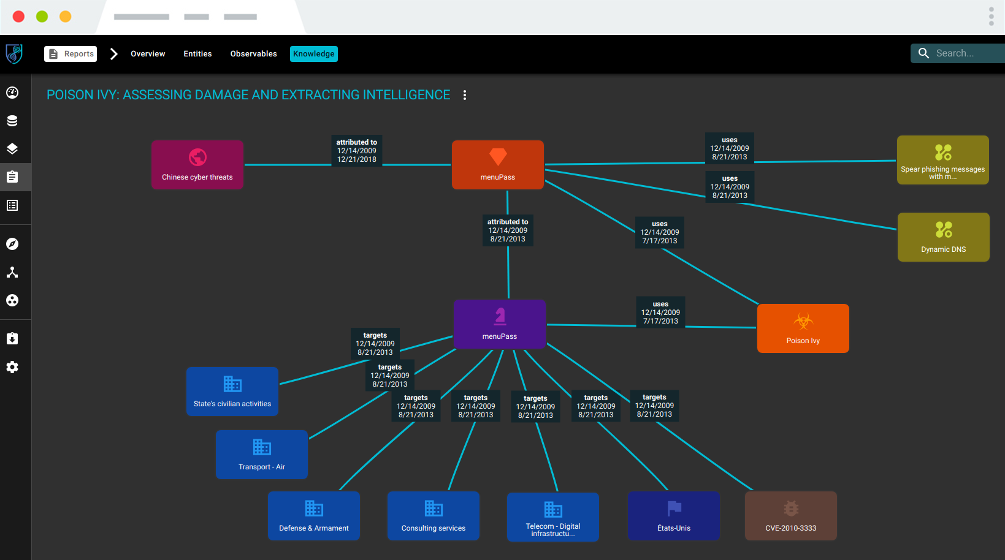
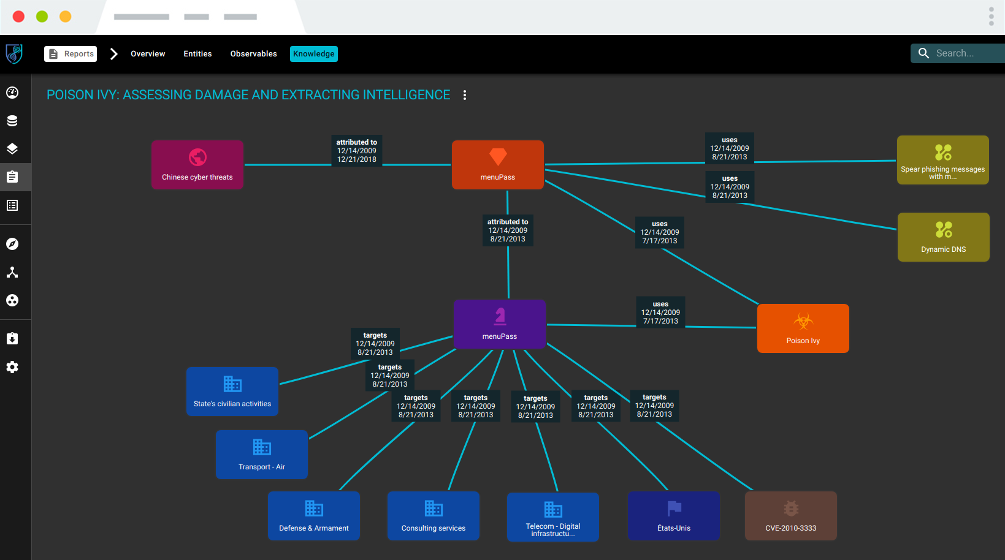 384Threat Intelligence
384Threat IntelligenceOpenCTI – Open Cyber Threat Intelligence Platform
OpenCTI is an open source platform allowing organizations to manage their cyber threat intelligence knowledge and observables. It has been created in...
-
 239Malware
239MalwareRubyGems strong_password Library Hijacked by Threat Actors
Ruby users who updated with strong_password gem version 0.0.7 are urged to roll back to the previous versions after a developer discovered...
-

 377Cyber Crime
377Cyber CrimeThe Logic of a Classic Advanced Persistent Threat Attack
Story of an Advanced Persistent Threat attack against a large corporation that started with a series of blank emails. Advanced persistent threats...
-

 729Malware
729MalwareWannaHydra – The Latest Malware Threat For Android Devices
The Antivirus Company Avast issued an alert on Monday about the spread of a virus that attempts to infect Brazilians smartphones and...
-

 323Malware
323MalwareSOC Second Defense Phase – Understanding the Threat Profiles
In the first phase of architecturing the SOC, we have seen the basic level understanding of the attacks and necessary steps to...
-
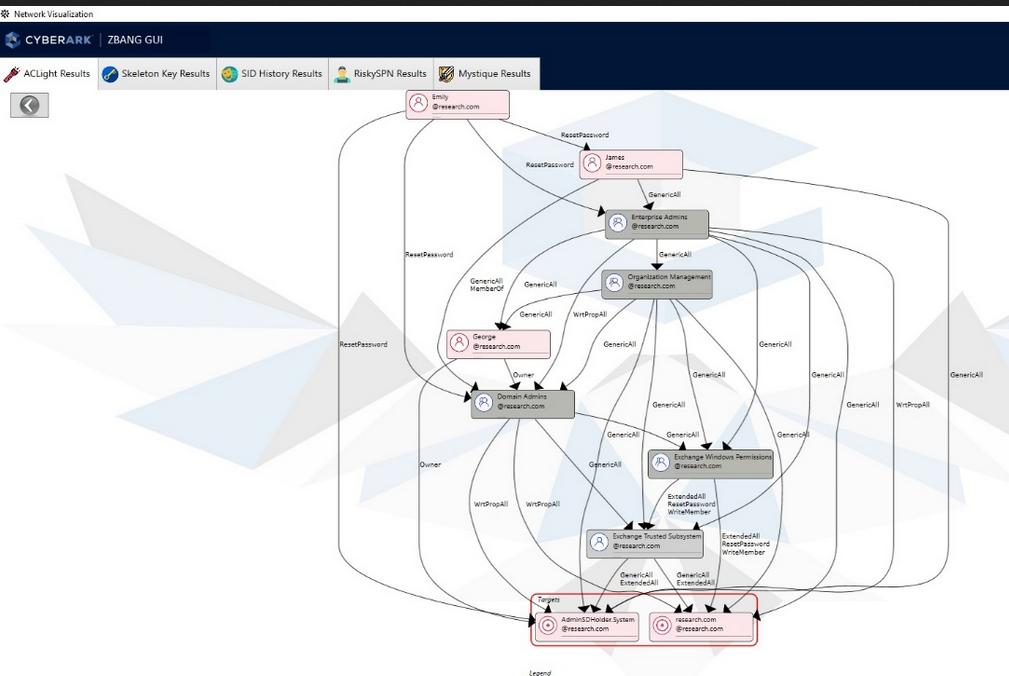
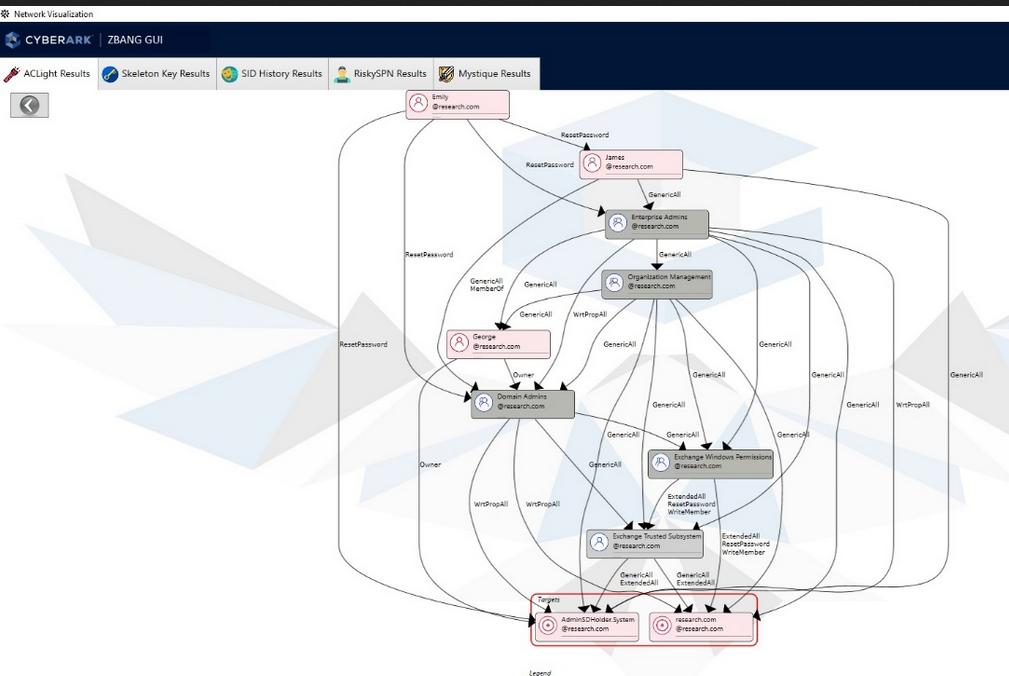 173Hack Tools
173Hack ToolszBang – Risk Assessment Tool that Detects Potential Privileged Account Threats
Organizations and red teamers can utilize zBang to identify potential attack vectors and improve the security posture of the network. The results...
-
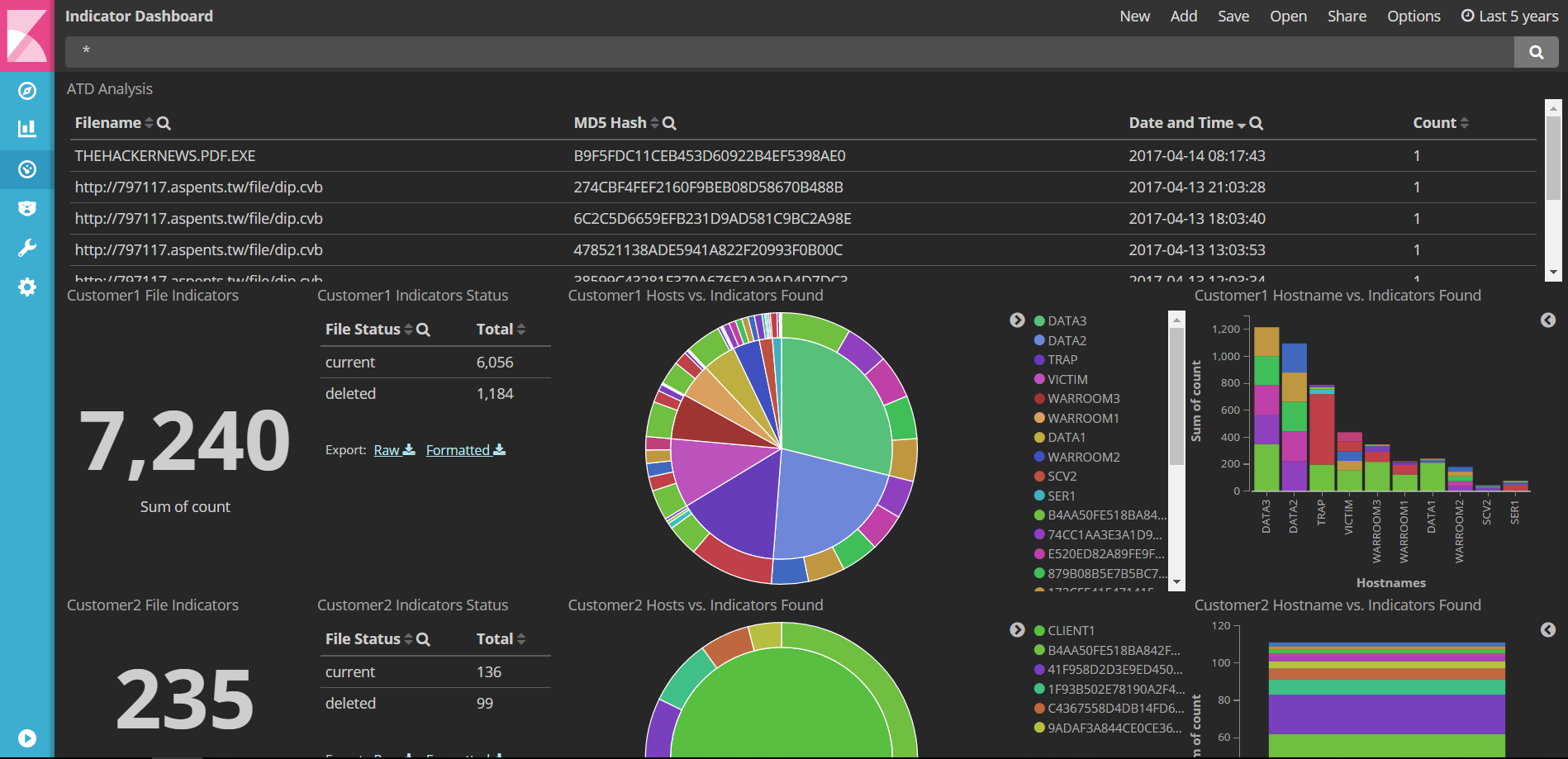
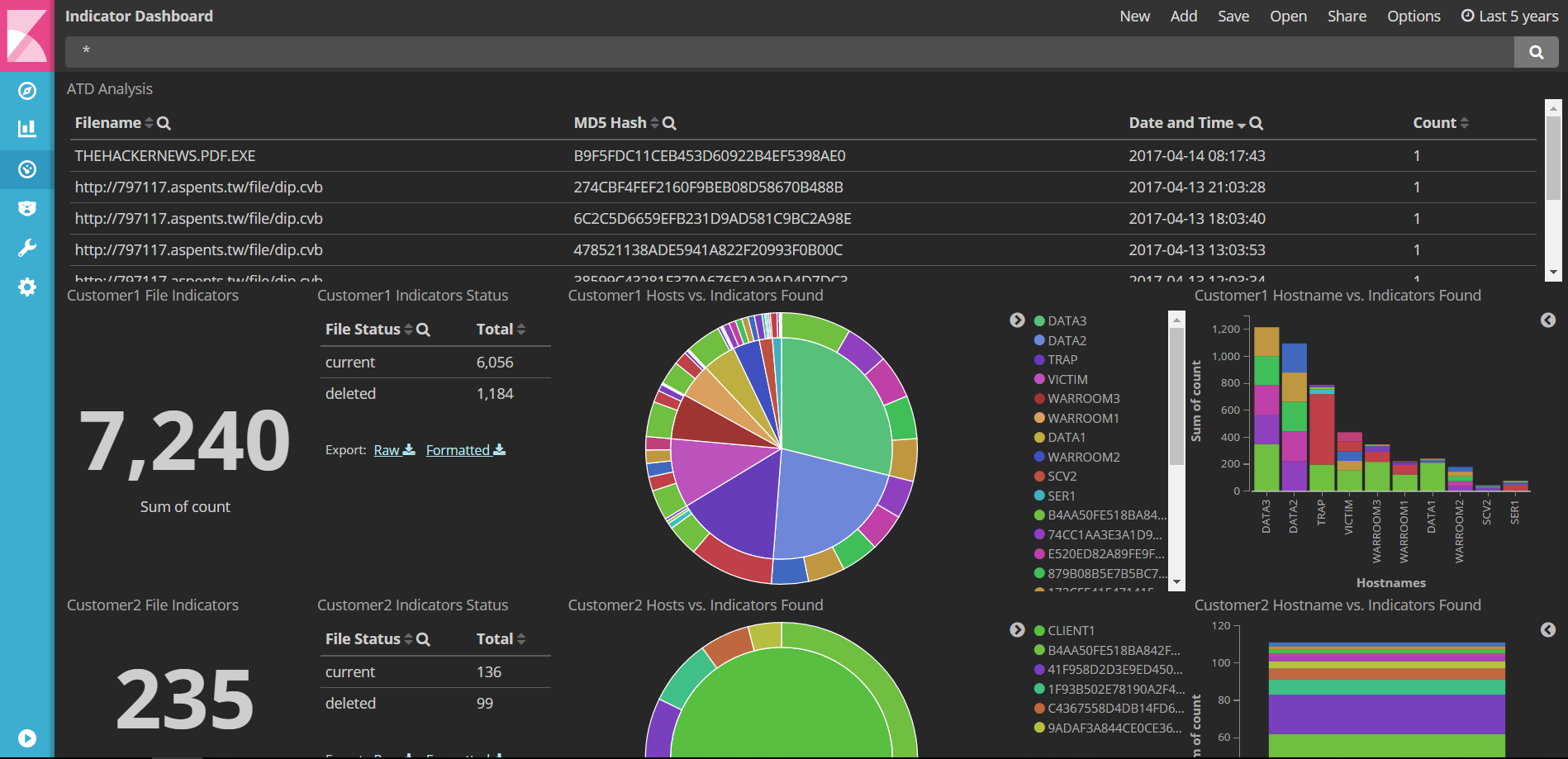 513Threat Intelligence
513Threat IntelligenceATIS – Automated Threat Intelligent System integrated with McAfee Advanced Threat Defense and Malware Information Sharing Platform.
An improvised automated threat intelligent system with advanced vulnerability scanners and Opensource Intelligence Information gathering python scripts when integrated with McAfee Advanced...






