Search results for "Threat"
-

 347Mobile Security
347Mobile SecurityMost Important Steps to Keep Your Mobile Safe From Sophisticated Cyber Threats
Mobile phones have become a part of everyday life, and their functionality continues to develop at a rapid pace. You can switch...
-
 284Infosec
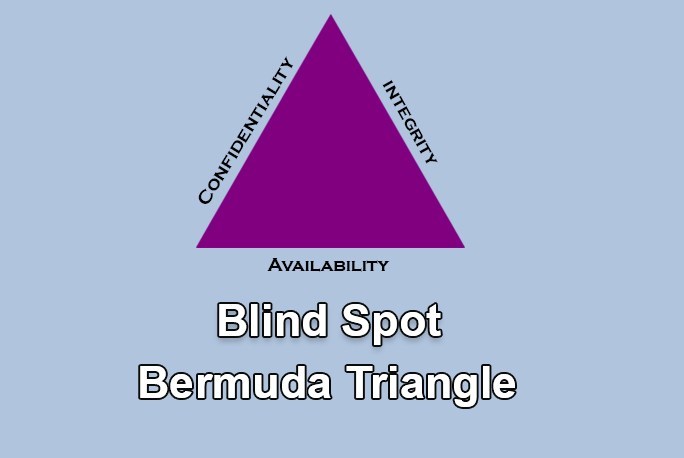
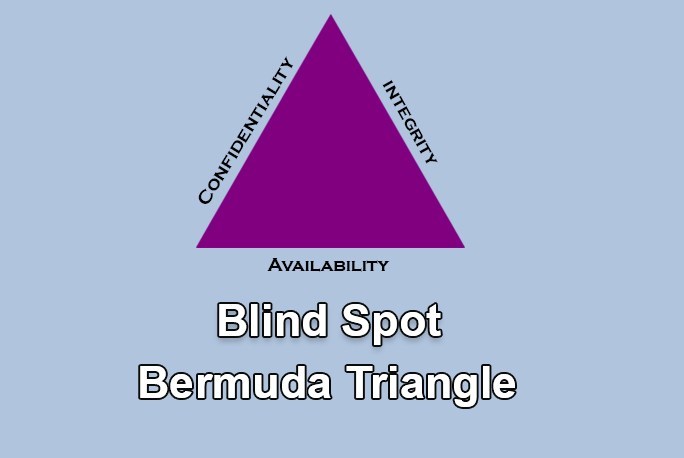
284InfosecCIA Triangle – Most Important Security Challenge with Organisation Insider Threats
Inspection in detail is available for Packet’s behaviour, but unfortunately, there is no possibility or means to inspect a person’s Intention. (...
-

 273Cyber Crime
273Cyber CrimeActress Bella Thorne posts her nudes to tackle threats from hackers
Bella Throne will not be bullied by cybercriminals. Stealing private photographs of celebrities and threatening to post them online unless they give...
-

 170How To
170How To4 Rising Cyber Threats In 2019
2018 was full of cybersecurity catastrophes, from enormous data breaches to the exposure of security imperfections in huge amounts of microchips and...
-

 266Data Breach
266Data BreachWhen Time is of the Essence – Testing Controls Against the Latest Threats Faster
A new threat has hit head the headlines (Robinhood anyone?), and you need to know if you’re protected right now. What do...
-
 316Hack Tools
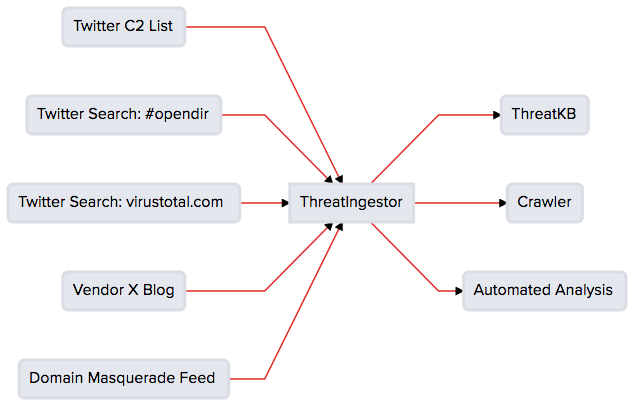
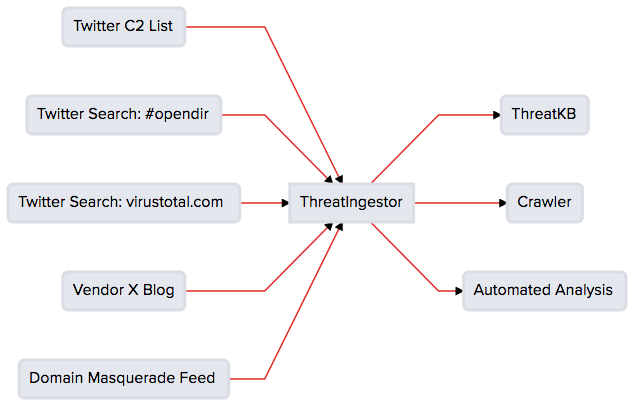
316Hack ToolsThreatIngestor – Extract and Aggregate Threat Intelligence
An extendable tool to extract and aggregate IOCs from threat feeds. Integrates out-of-the-box with ThreatKB and MISP, and can fit seamlessly into...
-

 319Infosec
319InfosecIs this website Safe : How to Check Website Safety to Avoid Cyber Threats Online
is this website safe ? In this digital world, Check website safety is most important concern since there are countless malicious websites...
-
Threat Intelligence
Cyber Threat Intelligence Tools List For Hackers and Security Professionals
Threat Intelligence Tools are more often used by security industries to test the vulnerabilities in network and applications. It helps for the...
-
 394Operating Systems
394Operating SystemsRedhunt OS – Virtual Machine for Adversary Emulation and Threat Hunting
RedHunt aims to be a one stop shop for all your threat emulation and threat hunting needs by integrating attacker’s arsenal as...
-

 381News
381NewsGlobal Threat Statistics for the week of April 5, 2019
Cryptojacking Boosts Botnet Expansion Botnets have been essential tools in distributed denial of service attacks for many years. With the continued success...
-

 274Malware
274MalwareFree Email Security Penetration Testing Tool to Check Organization’s Security against Advanced Threats
BitDam launches a free Email Security Penetration Testing tool to determine the organization’s security posture against advanced threats. The Email accounts are...
-

 302Infosec
302InfosecFLASHMINGO – Free Threat Intelligence Tool for Malware Analysts’ to Analyse Flash Exploits
FireEye released a Free automated analysis tool FLASHMINGO, which enables malware analysts to detect suspicious flash samples and to investigate them. The...
-

 294News
294NewsGlobal Threat Statistics for the week of March 22, 2019
PayPal Phishing Casts a Wide Net One of the most successful phishing methods is to co-opt a well-respected brand. PayPal topped the...
-

 202Data Security
202Data SecurityCynet is Launching a Free Threat Assessment for Businesses
In the age of regular cyber attacks and constant digital threats, it’s no wonder that businesses find themselves spending more and more...
-

 214News
214News68% of Firms, Moderate to Extremely Vulnerable To Internal Threats
With malware infestation, data breaches allegedly caused by state-funded actors and phishing attacks becoming headlines in both mainstream media and tech news...
-
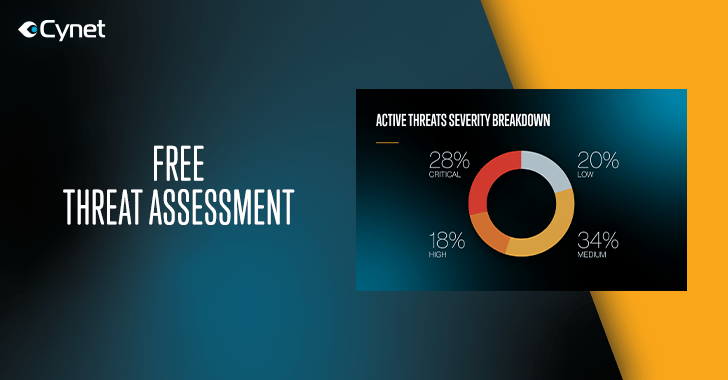
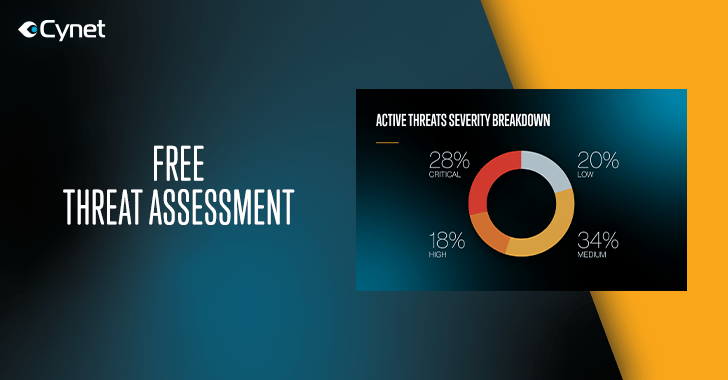 292Infosec
292InfosecCynet Offers a Free Threat Assessment for Mid-Sized and Large Organizations – Take a Free Ride Now
Visibility into an environment attack surface is the fundamental cornerstone to sound security decision making. However, the standard process of 3rd party...
-
 503Malware
503MalwareTop-10 Cybersecurity Threats in 2019 and How to Protect Yourself
Cybersecurity deals with emerging dangers and includes protecting and preventing means against hacker attacks. New technologies are booming, and our gadgets become...
-

 369News
369NewsThreat Intelligence With Two Most Used Operating Systems
With 4.312 billion users in the world, comprising 55.6% of the global population, the Internet has become an everyday center hub for...
-

 337Data Security
337Data SecurityMedtronic defibrillators vulnerable to life threatening cyber attacks
Defibrillators are electronic devices manufactured to save the lives of people with life-threatening heart conditions such as Hypertrophic Cardiomyopathy (HCM). But now,...
-

 206News
206NewsSub-Saharan Africa’s SMEs, A Growing Favorite Target Of Threat Actors
When it comes to malware development and infection campaigns, it does not matter where the vulnerable computer systems are located. Malware in...
-

 284News
284NewsWi-Fi ‘Hiding’ Inside USB Cable: A New Security Threat On The Rise?
Today, the world has become heavily reliant on computers owing to the various advantages they offer. It has thus become imperative that...






