Search results for "Threat"
-

 3.4KCyber Attack
3.4KCyber AttackFBI Analyst Charged With Stealing Counterterrorism and Cyber Threat Info
The U.S. Department of Justice (DoJ) indicted an employee of the Federal Bureau of Investigation (FBI) for illegally removing numerous national security...
-

 3.5KMobile Security
3.5KMobile SecurityAndroid stalkerware threatens victims further and exposes snoopers themselves
ESET research reveals that common Android stalkerware apps are riddled with vulnerabilities that further jeopardize victims and expose the privacy and security...
-
 4.4KMalware
4.4KMalwareHackers Threaten to Leak D.C. Police Informants’ Info If Ransom Is Not Paid
The Metropolitan Police Department (MPD) of the District of Columbia has become the latest high-profile government agency to fall victim to a...
-

 4.1KMalware
4.1KMalwareKobalos – A complex Linux threat to high performance computing infrastructure
ESET researchers publish a white paper about unique multiplatform malware they’ve named Kobalos
-

 4.3KMalware
4.3KMalwareFreakOut, the new botnet that threatens thousands of vulnerable Linux systems
According to a recent report by cybersecurity experts, the operators of a botnet have been targeting non-patched applications running on Linux systems....
-

 1.5KCyber Crime
1.5KCyber CrimeFBI warns of threat actors spoofing Bureau domains, email accounts
The U.S. law enforcement agency shares a sampling of more than 90 spoofed FBI-related domains registered recently
-
 1.2KData Breach
1.2KData BreachHow to Become a Certified Cyber Threat Intelligent Analyst?
Nowadays, Cyber crimes are increasing. The demand for cyber thteat intelligence experts is high. The field of cyber Intelligence is growing and...
-

 1.9KCyber Crime
1.9KCyber CrimeCrooks threaten to leak customer data stolen from e‑commerce sites
A hack-and-extort campaign takes aim at poorly secured databases replete with customer information that can be exploited for further attacks
-
 3.8KPhishing
3.8KPhishingBeware of Zoom Phishing Campaign that Threatens Employees Contracts will be Suspended or Terminated
A new zoom phishing campaign observed asking recipients to join a zoom meeting that threatens employees that their contracts will be either...
-

 3.5KCyber Attack
3.5KCyber AttackHow Can Social Engineering Alter the Insider Threat Game?
Social engineering attacks are not becoming common against corporate organizations and SMBs but are also getting increasingly advanced. With hackers adopting smarter...
-

 3.6KHack Tools
3.6KHack ToolsRTTM – Real Time Threat Monitoring Tool
Monitoring possible threats of your company on Internet is an impossible task to be achieved manually. Hence many threats of the company...
-
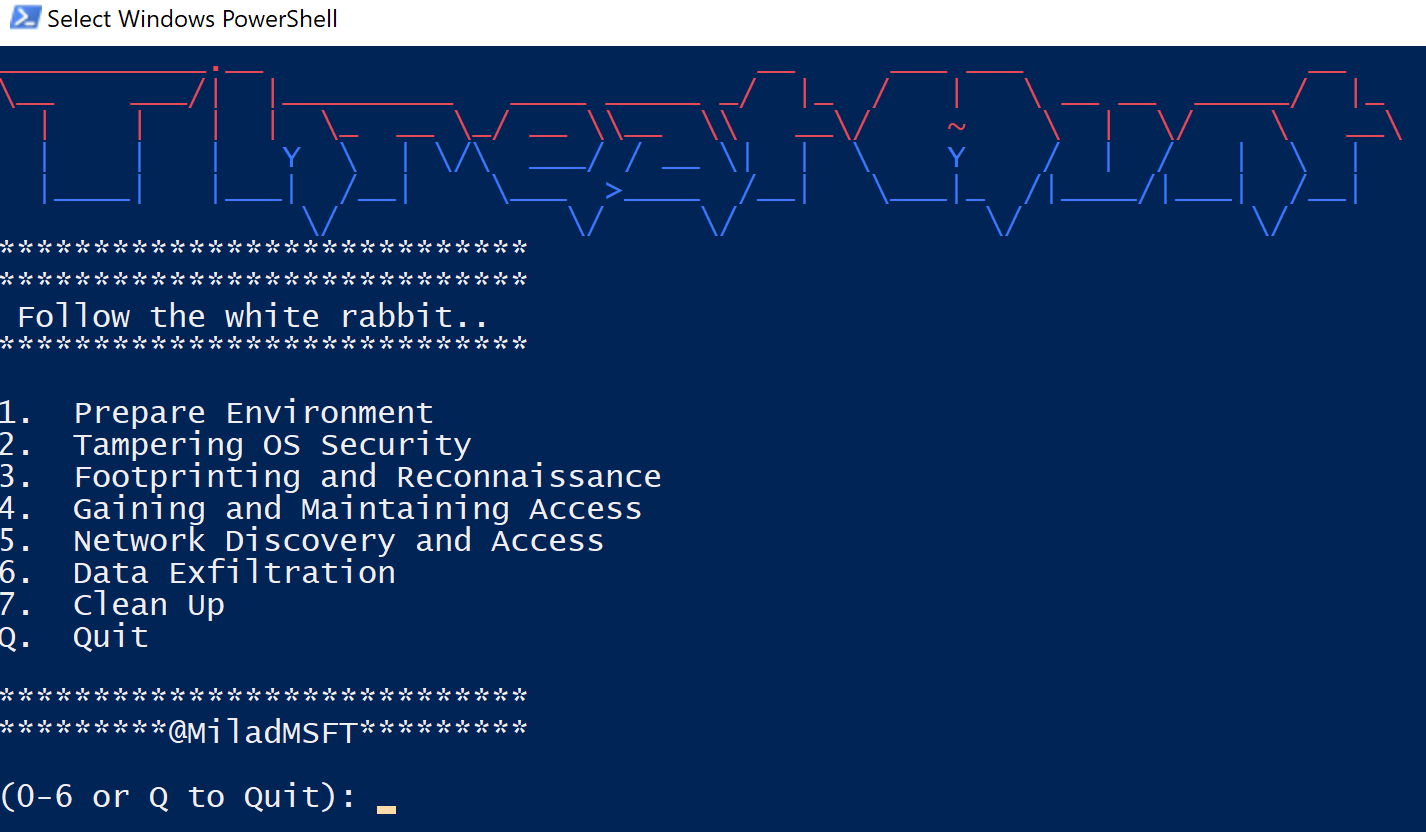
 5.1KHack Tools
5.1KHack ToolsThreatHunt: PowerShell repository to train your threat hunting skills
ThreatHunt is a simple PowerShell repository that allows you to train your threat hunting skills. ThreatHunt allows you to simulate a variety...
-
 1.2KHack Tools
1.2KHack Tools[BlackHat Europe tool] Real Time Threat Monitoring Tool
Real Time Threat Monitoring Tool V2.0 Monitoring possible threats of your company on the Internet is an impossible task to be achieved...
-

 2.2KInfosec
2.2KInfosecTop 3 Categories That Mostly Impact by Cyber Threats & Protection Against Cyber Attack
Cybersecurity can be termed as the process of recovering programs, networks, and devices from different types of cyber threats. Over the past...
-

 2.4KNews
2.4KNewsNew SMS Alternative ‘RCS Standard’ Is Exposing Users To Security Threats
Replacing the regular SMS with the RCS or Rich Communication Services is making users vulnerable to text-based attacks, call interception, location tracking,...
-

 1.5KHow To
1.5KHow To5 Insider Threat Solutions You Should Follow in 2019
There are five main pillars of organization security that every successful business needs to adhere to: Protect your important assets Create a...
-

 3.9KData Security
3.9KData SecurityGinp Android trojan targets banking apps & threatens 2FA/SMS
Dubbed Ginp; the trojan keeps coming back with new capabilities. Researchers at ThreatFabric, the cybersecurity firm based in Amsterdam, have been following...
-

 1.7KHow To
1.7KHow ToCyber Security Threats to Consider in 2019 and Beyond
“2018: Banking Trojans came out to be the most prominent threat vector for mobile devices, witnessing a growth of 150 percent!” For...
-
 3.0KHack Tools
3.0KHack Toolsthreat_note – DPS’ Lightweight Investigation Notebook
threat_note is a web application built by Defense Point Security to allow security researchers the ability to add and retrieve indicators related...
-
 3.7KInformation Gathering
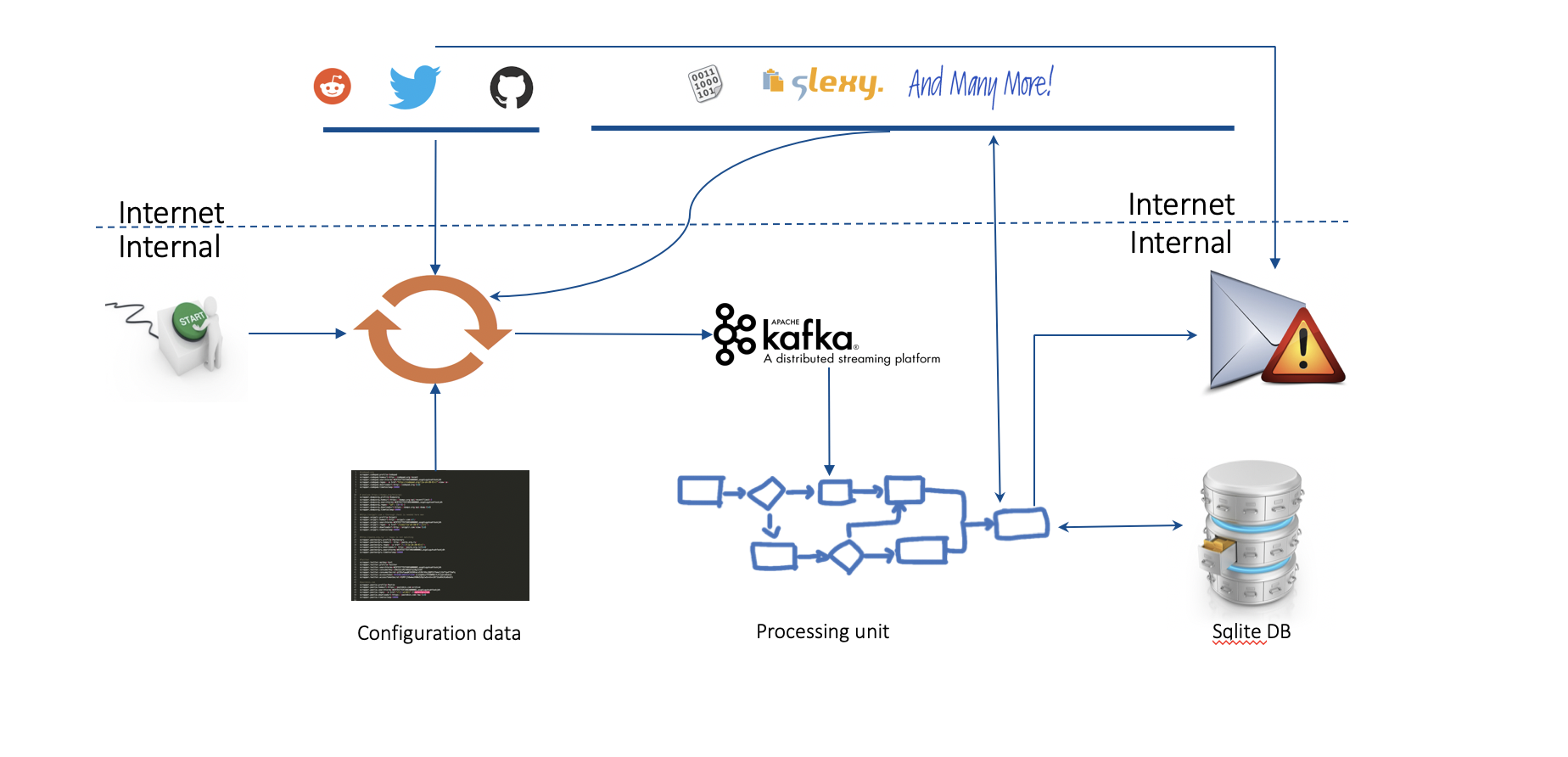
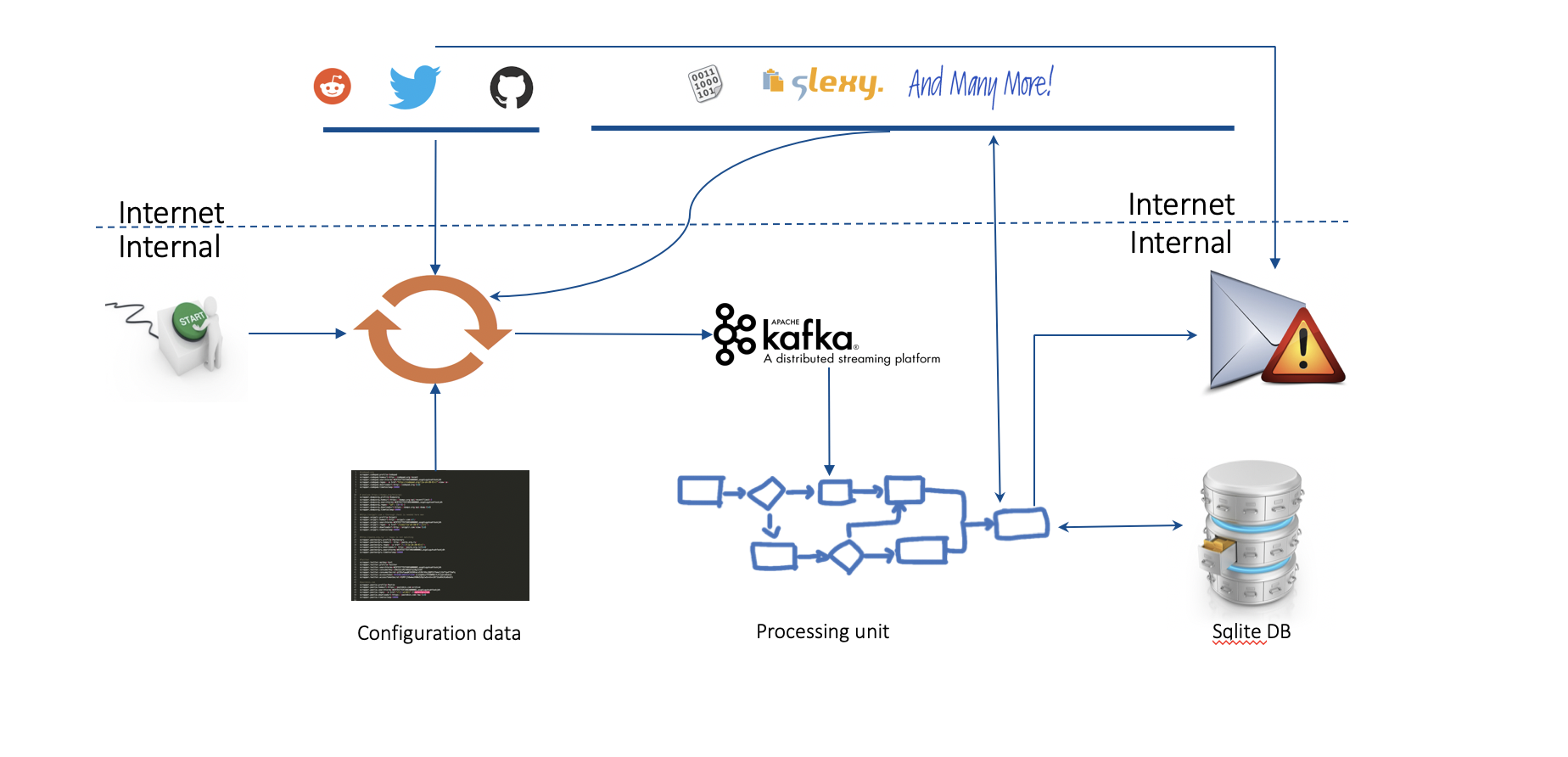
3.7KInformation GatheringACT Platform – Collection And Exchange Of Threat Intelligence Information
Semi-Automated Cyber Threat Intelligence (ACT) is a research project led by mnemonic as with contributions from the University of Oslo, NTNU,...
-

 5.5KHow To
5.5KHow ToWays To Manage Cybersecurity Threats Relating to Cryptocurrency
Cryptocurrency may be on the verge of taking over the world economy. It has drawn much attention from people around the world...






