Search results for "Threat"
-

 216Mobile Security
216Mobile SecurityHow to Keep Your Mobile Safe from Cyber Threats
Before smartphones were popular, people didn’t take mobile security much seriously. After all, we used to have a few contacts, some classic...
-

 200Articles
200ArticlesXiaomi Electric Scooters Vulnerable to Life-Threatening Remote Hacks
Smart devices definitely make our lives easier, faster, and more efficient, but unfortunately, an insecure smart device can also ruin your day,...
-

 266Infosec
266Infosec5 Steps How To Protect Your Company Infrastructure From Insider Threats
While most people worry about threats from hackers trying to breach their security from the outside, it’s just as, if not more,...
-
 249News
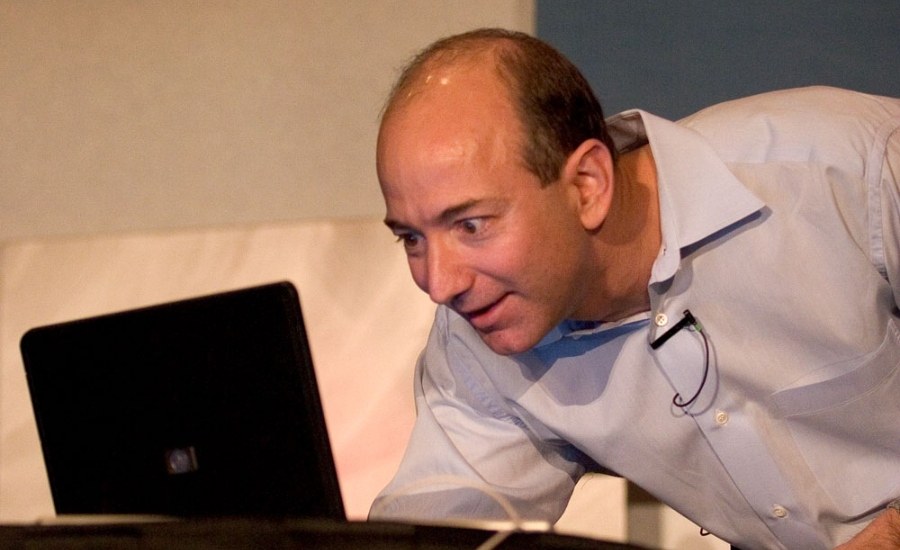
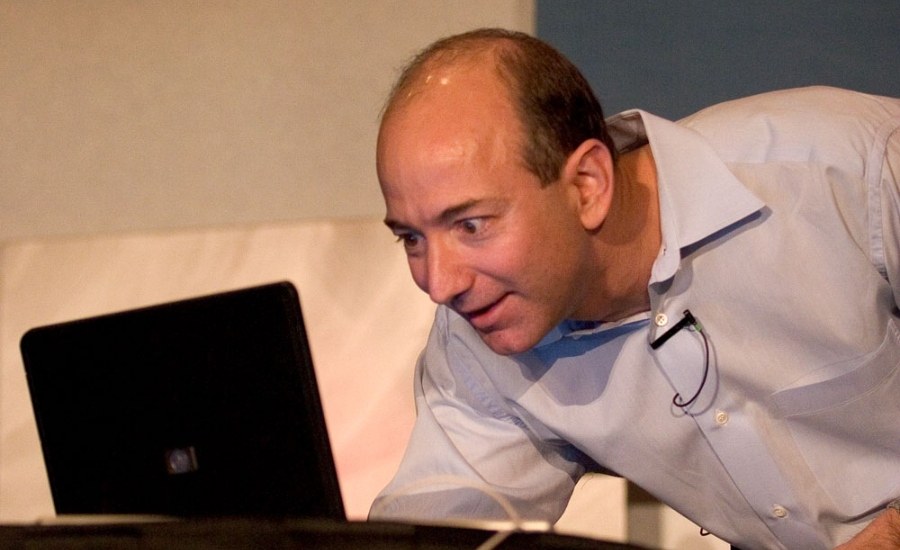
249NewsJeff Bezos Claims National Enquirer Is Threatening To Release His Nudes
Amazon CEO Jeff Bezos, via a long post on Medium, has accused the National Enquirer’s parent company, American Media Inc. (aka AMI),...
-
 283Malware
283MalwareOceanLotus(APT32) Threat Actor Group Deliver KerrDown Malware Via Word Document and RAR Archive
OceanLotus group known for Multiple attack campaigns around the globe, the threat actor group targets private sectors across multiple industries, foreign governments,...
-

 210Mobile Security
210Mobile SecurityRising Threats in CyberSpace – Organizations Must be Prepared to Experience
Recently we have seen more increase in various threats and the ways of intruding the network and there were increase by APT...
-

 190Articles
190ArticlesNew Exploit Threatens Over 9,000 Hackable Cisco RV320/RV325 Routers Worldwide
If the connectivity and security of your organization rely on Cisco RV320 or RV325 Dual Gigabit WAN VPN routers, then you need...
-

 245Infosec
245InfosecInsider Threat Detection Software: Protecting Against the Insider Threat – What You Should Know
Insider Threat is one of the dangerous threat actors for many organization and keeping your business protected from outside threats is hard...
-

 292Data Security
292Data SecurityU.S. Senate introduces bill against Chinese cyberthreats
Legislators from both political parties presented a bill designed to protect American technological infrastructure Senators Marco Rubio (Republican Party) and Mark Warner...
-

 277News
277NewsHackers Threaten To Release Stolen Data Related to 9/11 Attacks
In an announcement posted on Pastebin, the hacker group TheDarkOverlord told that it has been successful in breaching law firms that handle cases...
-
 229Data Security
229Data SecurityThese are worst cyberthreats of 2018
Cybersecurity specialists from the International Institute of Cyber Security already predicted that this would be a difficult year for users and organizations,...
-

 308Leaks
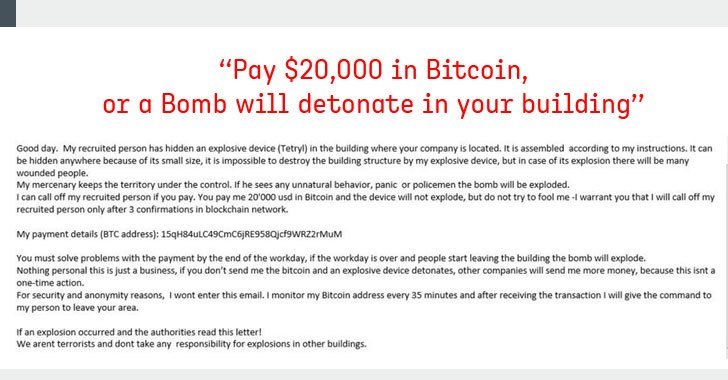
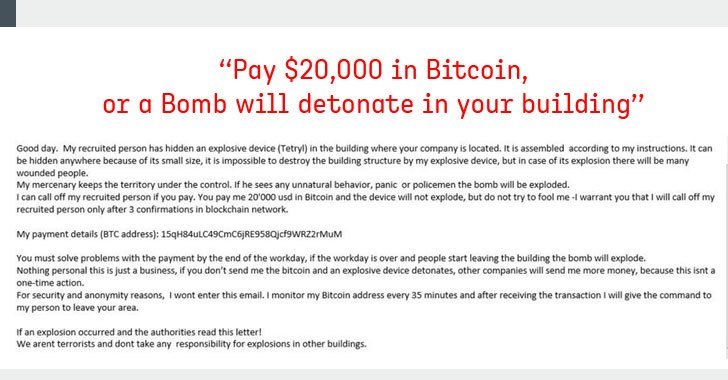
308LeaksExtortion Emails with Bomb Threats Cause Panic in US Cities
Extortion emails which carried bomb threats caused panic in various cities across the U.S. and police had to tell people to stay...
-

 323Incidents
323IncidentsSPAM POSTS THREATEN WITH DETONATING BOMBS IF BITCOINS ARE NOT PAID
This extortion scheme has received massive attention from the media, although it has not achieved so many funds Police departments across the...
-
 191Articles
191ArticlesFake Bomb Threat Emails Demanding Bitcoins Sparked Chaos Across US, Canada
“Pay $20,000 worth of bitcoin, or a bomb will detonate in your building” A massive number of businesses, schools, government offices and...
-

 303Scams
303ScamsHow to protect yourself as the threat of scam apps grows
As the threat of bogus apps continues, what can we do to protect ourselves against these fraudulent practices?
-
 207Malware
207MalwareTA505 Cyber Threat Actors Installing Remote Monitoring Tool via Weaponized MS Word Document
Cyber Criminals from TA505 group started a new campaign that targeting retail, grocery, and restaurant chains by distributing weaponized MS word documents....
-

 320Incidents
320IncidentsCitrix forced its users to change passwords due to cyberattack threat
The company fears a credential stuffing attack in ShareFile Information security and digital forensics specialists from the International Institute of Cyber Security...
-

 425News
425NewsFlawedAmmy, the Only RAT in CheckPoint’s Global Threat Index 2018 List
2017 was a year of ransomware, primarily the WannaCry malware that made $4 billion in profits from the ransom payments of its...
-
 309Infosec
309Infosec2019 Israeli Security Expo Promises to Deliver Solutions to New-Age Threats
The 2019 International HLS & Cyber Expo is all set to be the largest cybersecurity conference and exhibition in Israel. Attracting global...
-

 266News
266NewsHuawei a Threat to Australia’s Infrastructure, Says Spy Chief
Australia’s spy chief says that China’s Huawei could pose a great security threat to the country’s infrastructure, especially the water supply and...
-

 264News
264NewsRemoval Storage, USB Drives Serious Security Threats: Report
Removal storage and USB thumb drives are serious security threats and could cause massive damage to industrial systems, as per a new...






