Search results for "Toolkit"
-
 329Data Security
329Data SecurityRIG Exploit Toolkit Distributing CeidPageLock Malware to Hijack Browsers
A previously discovered browser hijacker malware dubbed as CeidPageLock has resurfaced again, in a bigger and better avatar, reveal researchers at Check...
-
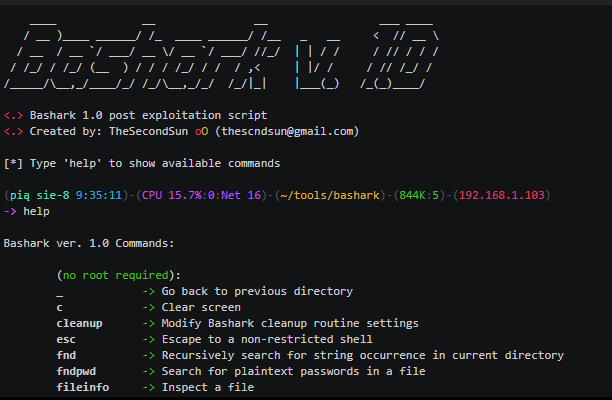
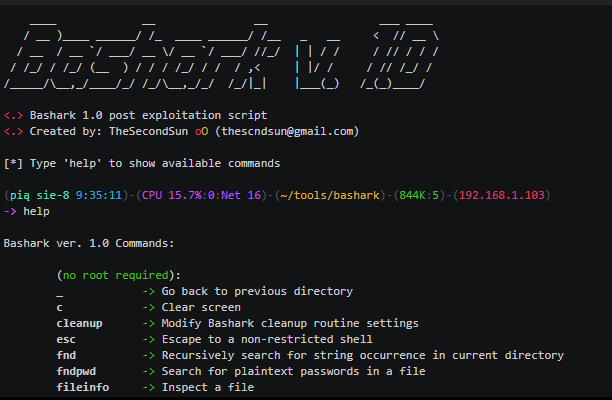 216Hack Tools
216Hack ToolsBashark- Post Exploitation Toolkit Written in Pure Bash
Bashark aids Pentesters and Security Researchers during the post-exploitation phase of security audits. Usage To launch Bashark on compromised host, simply source...
-

 281MITM
281MITMZigBee Security Research Toolkit: KillerBee
KillerBee framework is a tool for attacking ZigBee and IEEE 802.15.4 networks. KillerBee is designed to simplify the process of sniffing packets...
-
 319Network Tools
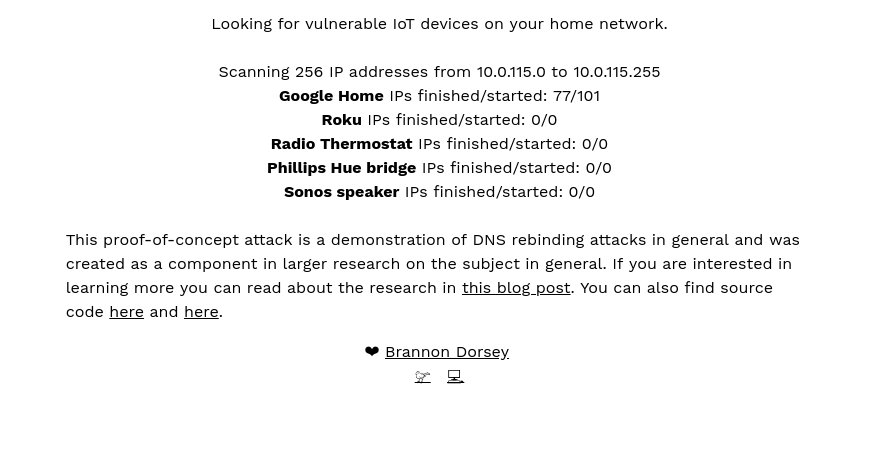
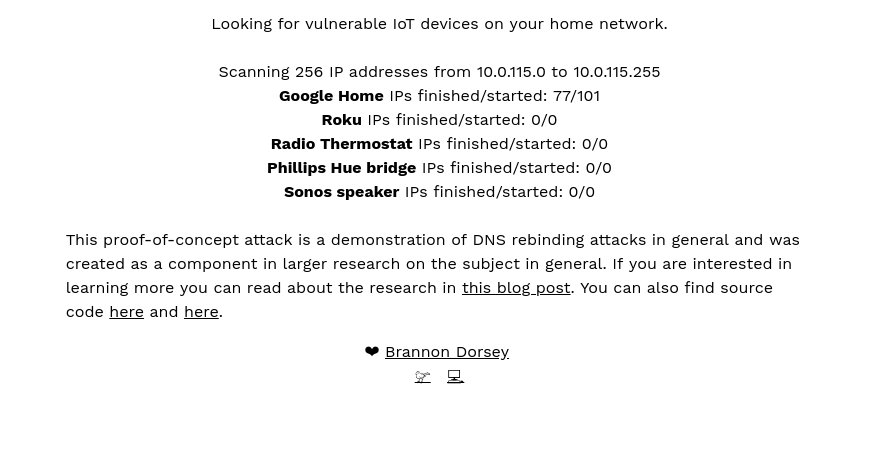
319Network ToolsDNS Rebind Toolkit – A Front-End JavaScript Toolkit For Creating DNS Rebinding Attacks
DNS Rebind Toolkit is a frontend JavaScript framework for developing DNS Rebinding exploits against vulnerable hosts and services on a...
-
 262Wireless Attacks
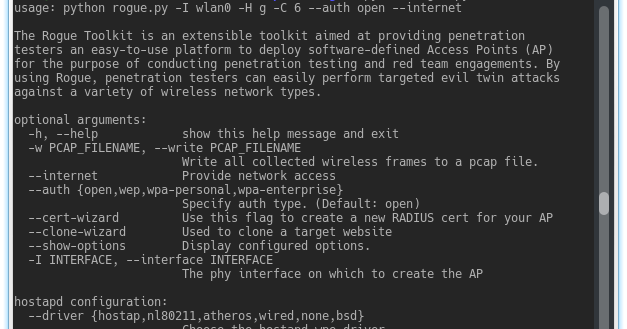
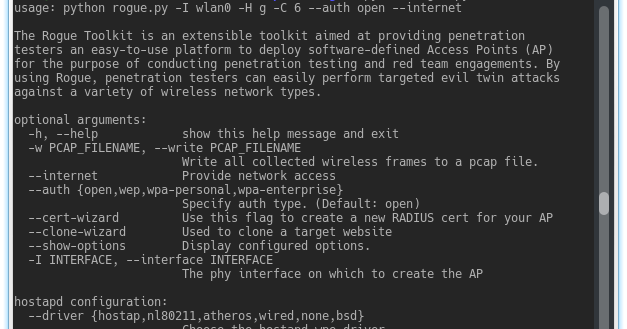
262Wireless AttacksThe Rogue Toolkit – An Extensible Toolkit Aimed At Providing Penetration Testers An Easy-To-Use Platform To Deploy Access Points
The Rogue Toolkit is an extensible toolkit aimed at providing penetration testers an easy-to-use platform to deploy software-defined Access Points (AP)...
-
 271Cryptography and Encryption
271Cryptography and EncryptionStego-Toolkit – Collection Of Steganography Tools (Helps With CTF Challenges)
This project is a Docker image useful for solving Steganography challenges as those you can find at CTF platforms like hackthebox.eu. The...
-
 224Wireless Attacks
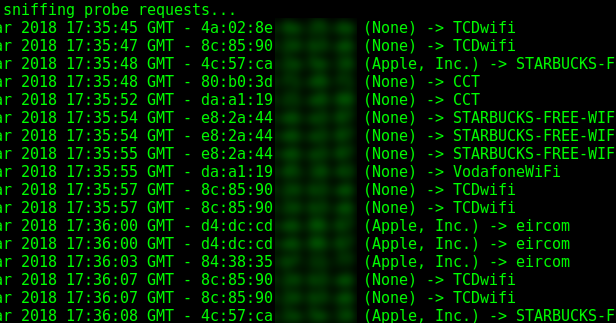
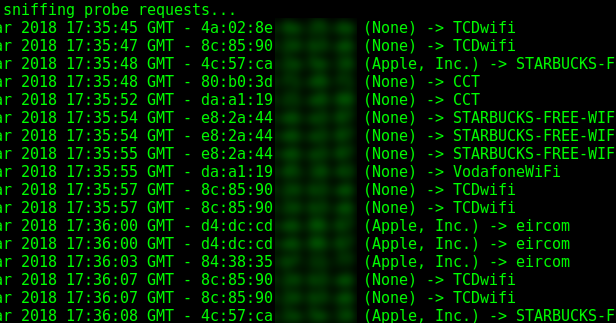
224Wireless AttacksProbequest – Toolkit For Playing With Wi-Fi Probe Requests
Toolkit allowing to sniff and display the Wi-Fi probe requests passing near your wireless interface. Probe requests are sent by a station...
-

 208Hackers Repository
208Hackers RepositoryBackdoorMan – Toolkit that helps you find malicious PHP scripts and shells
BackdoorMan BackdoorMan is a toolkit that helps you find malicious, hidden and suspicious PHP scripts and shells in a chosen destination. Description...
-

 256Exploitation Tools
256Exploitation Toolsp0wnedShell- PowerShell Runspace Post Exploitation Toolkit
p0wnedShell is an offensive PowerShell host application written in C# that does not rely on powershell.exe but runs powershell commands and functions...
-

 187Exploitation
187ExploitationREXT – Router Exploitation Toolkit
REXT is a toolkit for easy creation and usage of various python scripts that work with embedded devices. Requirements: requests paramiko beautifulsoup4...
-
 429Video Tutorials
429Video TutorialsHow to Perform Mass Mailer Attack using Setoolkit – Kali Linux 2018.1
Mass mailer is commonly used to send a phishing page link to the e-mail ID of the target. The attacker needs to...
-

 240Wifi Hacking
240Wifi HackingThe Rogue Toolkit – Targeted Evil Twin Wireless Access Point Attack
The Rogue Toolkit is an extensible toolkit aimed at providing penetration testers an easy-to-use platform to deploy software-defined Access Points (AP) for...
-

 279Wireless Attacks
279Wireless AttacksThe Rogue Toolkit – Targeted Evil Twin Wireless Access Point Attack Toolkit
The Rogue Toolkit is an extensible toolkit aimed at providing penetration testers an easy-to-use platform to deploy software-defined Access Points (AP) for...
-

 245System Administration
245System AdministrationPowerUpSQL – A PowerShell Toolkit for Attacking SQL Server
The PowerUpSQL module includes functions that support SQL Server discovery, auditing for common weak configurations, and privilege escalation on scale. It is...
-
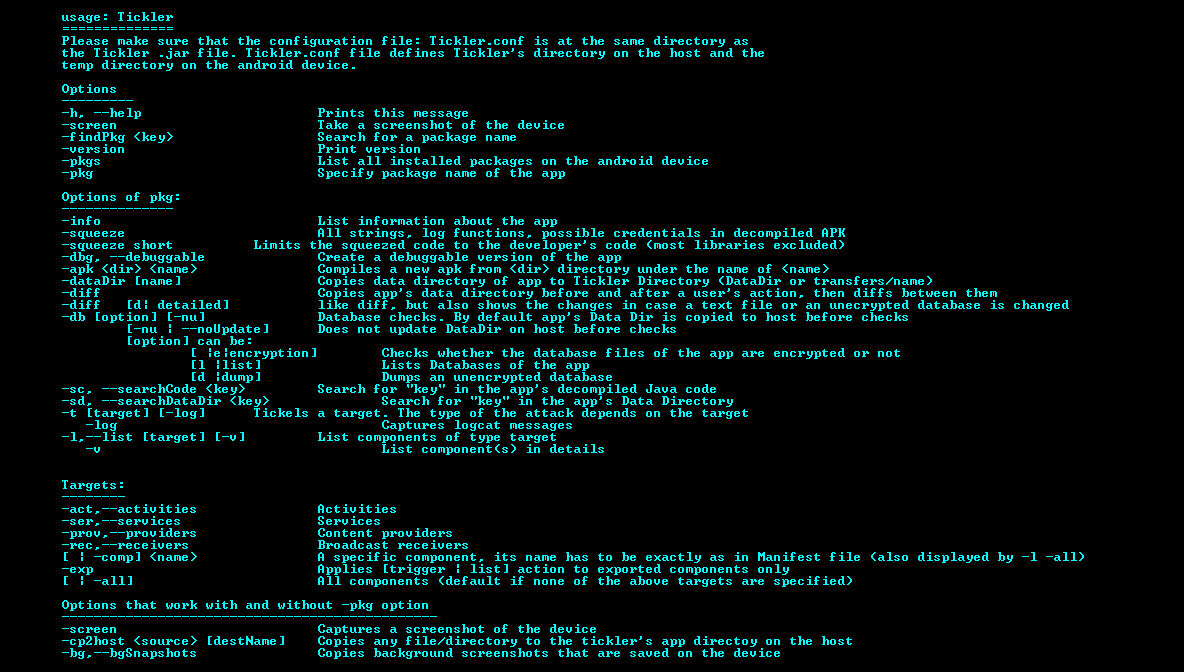
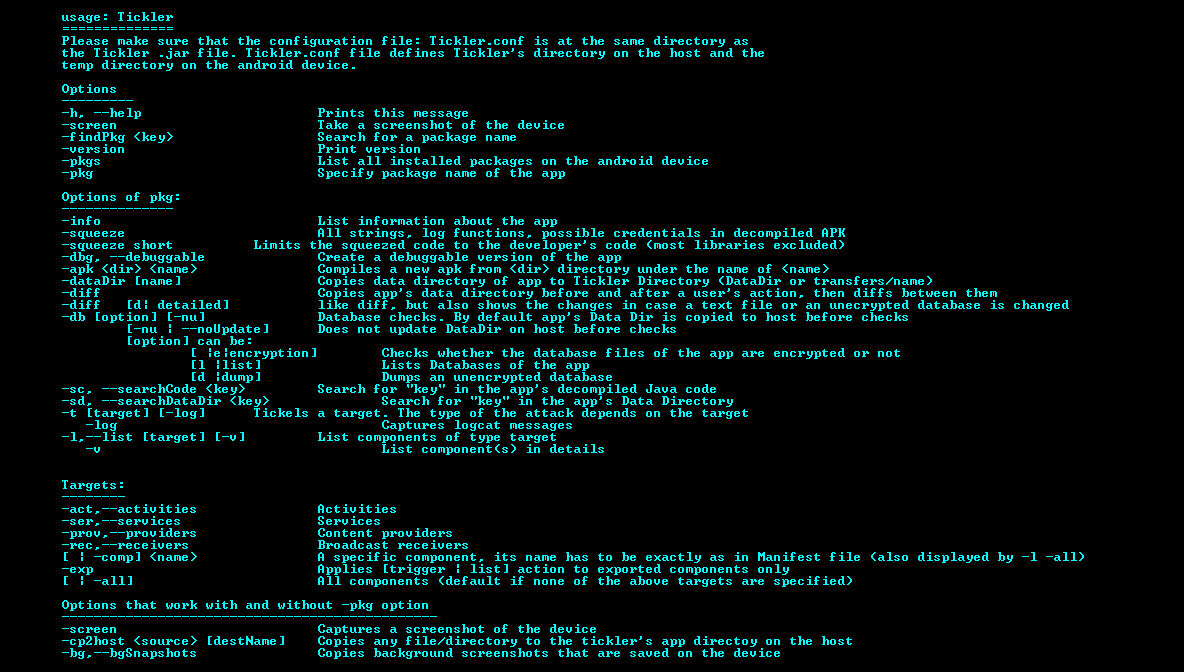 242Mobile Security
242Mobile SecurityAndroTickler – Penetration Testing and Auditing Toolkit for Android Apps
A java tool that helps to pentest Android apps faster, more easily and more efficiently. AndroTickler offers many features of information gathering,...
-

 404Tricks & How To's
404Tricks & How To'sMicrosoft Toolkit – All in one Windows and Office Activator [Download]
Microsoft toolkit is a combination of all activators. Auto KMS and EZ activator modules are built in to provide a perfect activation...
-

 321Wifi Hacking
321Wifi HackingEAPHammer – Toolkit for Performing Targeted Evil Twin Attacks
It is designed to be used in full scope wireless assessments and red team engagements. As such, focus is placed on providing...
-

 272Hackers Repository
272Hackers RepositoryHabu – Python Network Hacking Toolkit
Habu: Network Hacking Toolkit I’m developing Habu to teach (and learn) some concepts about Python and Network Hacking. These are basic functions...
-
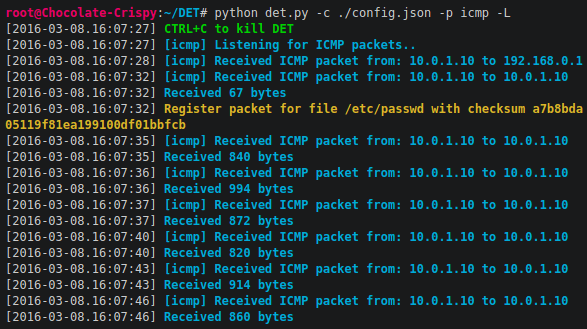
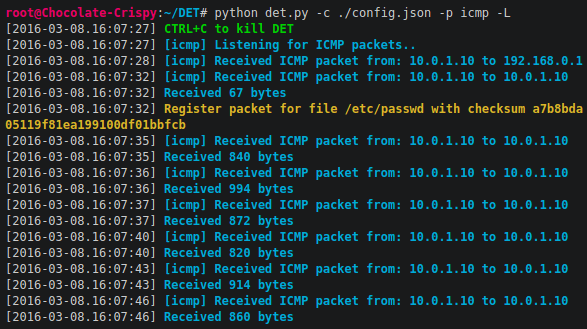 213Information Gathering
213Information GatheringDET – (extensible) Data Exfiltration Toolkit
DET (is provided AS IS), is a proof of concept to perform Data Exfiltration using either single or multiple channel(s) at the...
-

 237Network Tools
237Network Toolshabu – Network Hacking Toolkit
Habu is to teach (and learn) some concepts about Python and Network Hacking. These are basic functions that help with some tasks...
-
 187Hackers Repository
187Hackers RepositoryGophish – Open-Source Phishing Toolkit
Gophish: Open-Source Phishing Toolkit Gophish is an open-source phishing toolkit designed for businesses and penetration testers. It provides the ability to quickly...






