Search results for "Toolkit"
-
 175Hackers Repository
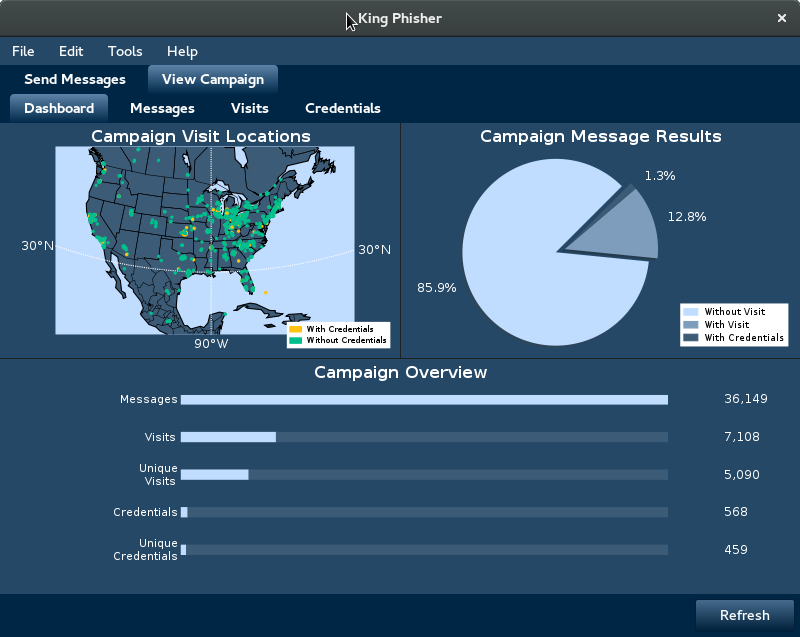
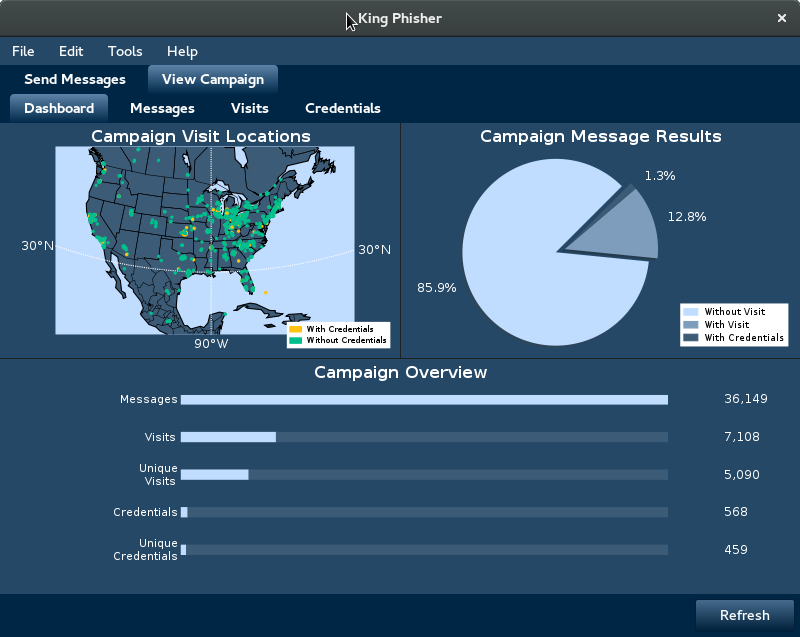
175Hackers RepositoryKing Phisher – Phishing Campaign Toolkit
Phishing Campaign Toolkit Installation For instructions on how to install, please see the INSTALL.md file. After installing, for instructions on how to...
-

 265Hack Tools
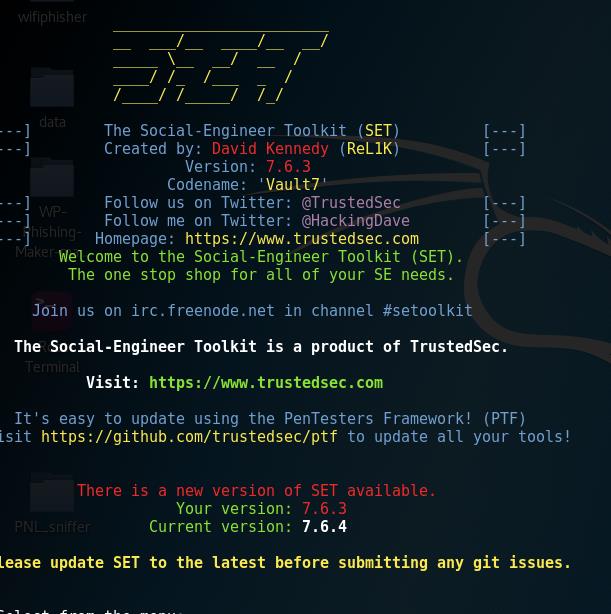
265Hack ToolsSET v7.7 – The Social-Engineer Toolkit “Blackout”
The Social-Engineer Toolkit (SET) was created and written by the founder of TrustedSec. It is an open-source Python-driven tool aimed at penetration...
-
 282Hacking Tutorials
282Hacking TutorialsHow to Use Metasploit, SEToolkit, AndroRAT Without Opening Ports in Kali Linux
It can be quite annoying when you have limited access to ports on a network and causes problems when pentesting, as you...
-

 149Hack Tools
149Hack ToolsLeviathan Framework – Wide Range Mass Audit Toolkit
Leviathan is a mass audit toolkit which has wide range service discovery, brute force, SQL injection detection and running custom exploit capabilities....
-

 267Hackers Repository
267Hackers RepositorySEToolkit – Hacking Windows Machines Using USB/CD Infectious Media Generator
SEToolkit – Hacking Windows Machines Infectious Media Generator Requirements Linux based Operating System (In this tutorial we are using Kali Linux) SEToolkit...
-

 319Hackers Repository
319Hackers RepositoryHow to Use Metasploit, SEToolkit Without Opening Ports Kali Linux
How to Use Metasploit, SEToolkit Without Opening Ports Kali Linux It can be quite annoying when you have limited access to ports...
-
 271Exploitation
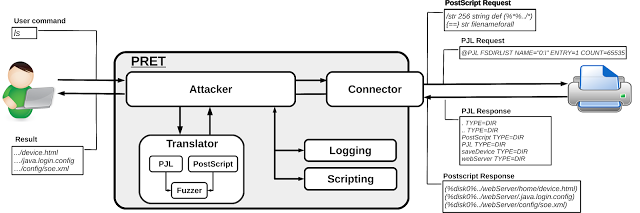
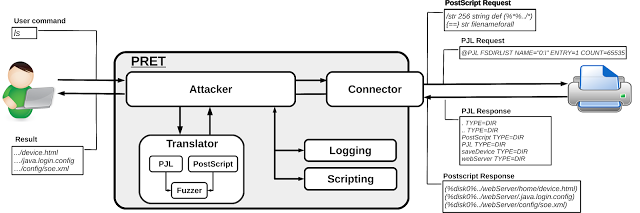
271ExploitationPrinter Exploitation Toolkit – Hacking Printers
PRET is a new tool for printer security testing developed in the scope of a Master’s Thesis at Ruhr University Bochum. It...
-
 171Hackers Repository
171Hackers RepositoryThe Social-Engineer Toolkit (SET) v7.6.4 released
The Social-Engineer Toolkit (SET) v7.6.4 released The Social-Engineer Toolkit (SET) is an open-source penetration testing framework designed to perform advanced and quick...
-
 96Data Security
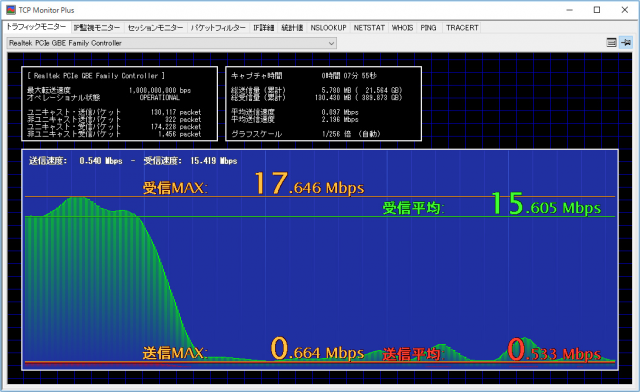
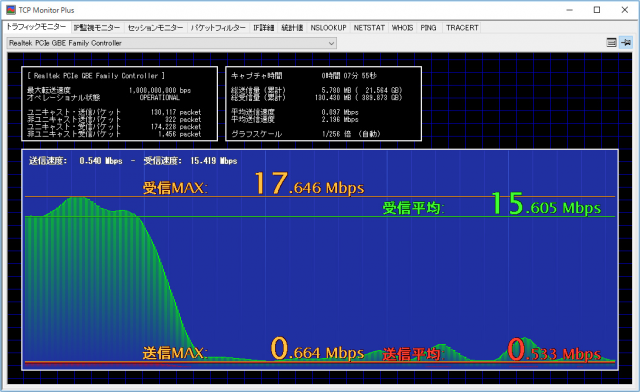
96Data SecurityTCP Monitor Plus is a portable network toolkit
Portable network toolkit TCP Monitor Plus has had its first update since 2015, adding a snapshot feature and some handy display tweaks....
-

 199Data Security
199Data SecurityQuickly Add an .onion URL to Your Site with the Enterprise Onion Toolkit (EOTK)
Security researcher and software engineer Alec Muffett has created a new project called the Enterprise Onion Toolkit (EOTK), which can help website...
-

 197Vulnerabilities
197VulnerabilitiesPopular hacking toolkit Metasploit adds hardware testing capabilities
The Metasploit hacking toolkit now includes a new hardware bridge that makes it easier for users to analyze hardware devices. The popular...
-

 233Hack Tools
233Hack ToolsBurp Suite Professional 1.7.14 – The Leading Toolkit for Web Application Security Testing
Burp Suite is an integrated platform for performing security testing of web applications. Its various tools work seamlessly together to support the...
-
 224Backdoors
224BackdoorsBackdoorMan – Toolkit That Helps You Find Malicious, Hidden And Suspicious PHP Scripts And Shells
A Python open source toolkit that helps you find malicious, hidden and suspicious PHP scripts and shells in a chosen destination, it...
-
 228Automated Pentest
228Automated PentestAPT2 – Automated Penetration Testing Toolkit
This tool will perform an NMap scan, or import the results of a scan from Nexpose, Nessus, or NMap. The processesd results...
-

 193How To
193How ToBrutal – A Toolkit To Create Various HID Attacks
Brutal is a simple toolkit to quickly create various payload,powershell attack , virus attack and launch listener for a Human Interface Device....
-
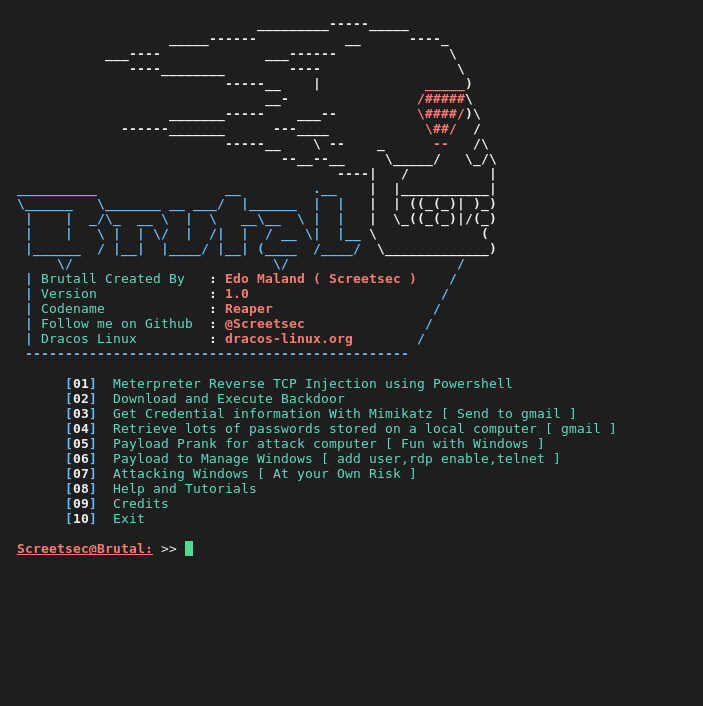
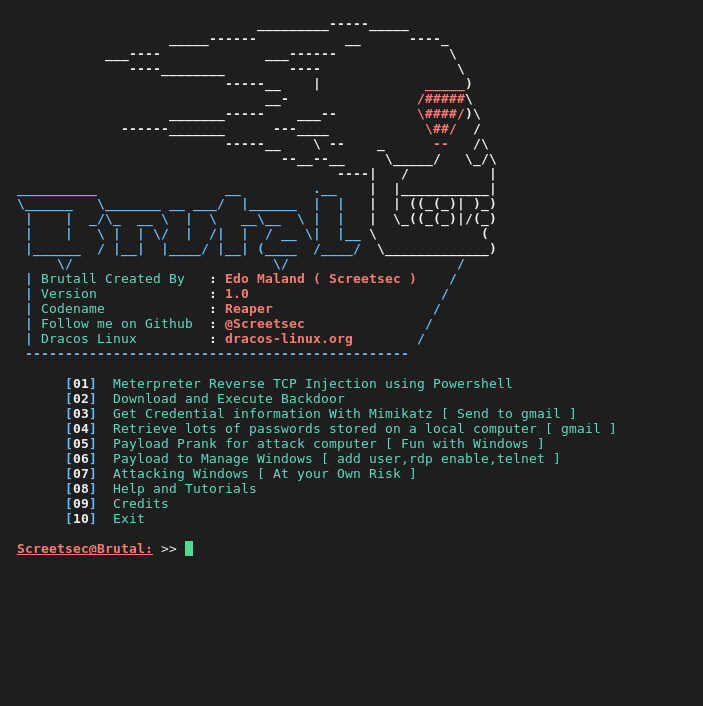 194Hack Tools
194Hack ToolsBrutal – Toolkit to quickly create various payloads,powershell and virus attacks
Brutal is extremely useful for executing scripts on a target machine without the need for human-to-keyboard interaction ( HID -ATTACK )...
-
 306Geek
306GeekMicrosoft Releases Open Source Toolkit That Understands Words Just Like Humans, Adds C++ & Python Support
Short Bytes: Microsoft used the CNTK toolkit to create a system which can understand words in a conversation just like humans. In...
-
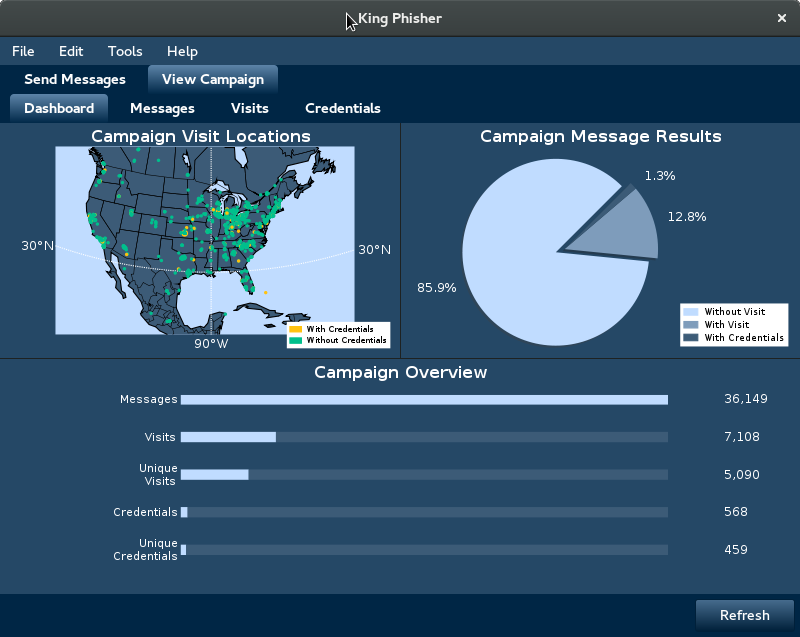
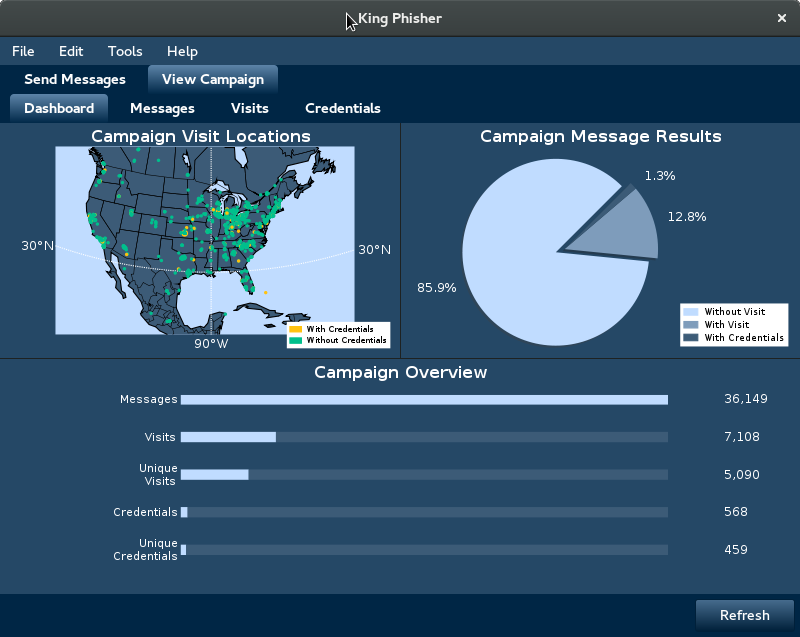 218Phishing
218PhishingKing Phisher 1.5.2 – Phishing Campaign Toolkit
King Phisher is a tool for testing and promoting user awareness by simulating real world phishing attacks. It features an easy to...
-

 70Malware
70MalwareEspionage toolkit targeting Central and Eastern Europe uncovered
Over the course of the last year, ESET has detected and analyzed several instances of malware used for targeted espionage – dubbed...
-

 121Exploitation
121ExploitationFirefox Security Toolkit – A Tool that Transforms Firefox Browsers into a Penetration Testing Suite
A tool that transforms Firefox Browsers into a penetration testing suite How ? It downloads the most important extensions, and install it...
-
 333Hacking Tutorials
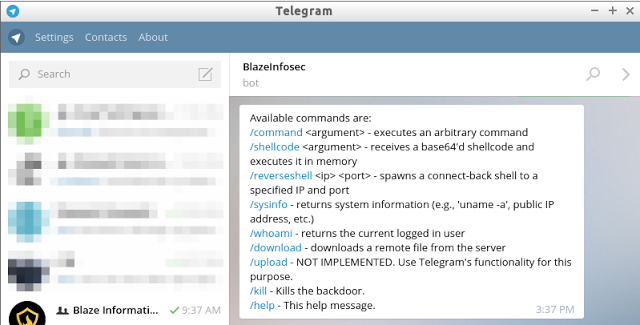
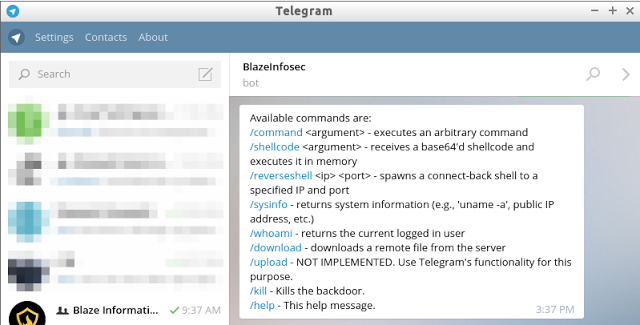
333Hacking TutorialsBt2 – Blaze Telegram Backdoor Toolkit
bt2 is a Python-based backdoor in form of a IM bot that uses the infrastructure and the feature-rich bot API provided by...






