Search results for "Toolkit"
-
 294Hack Tools
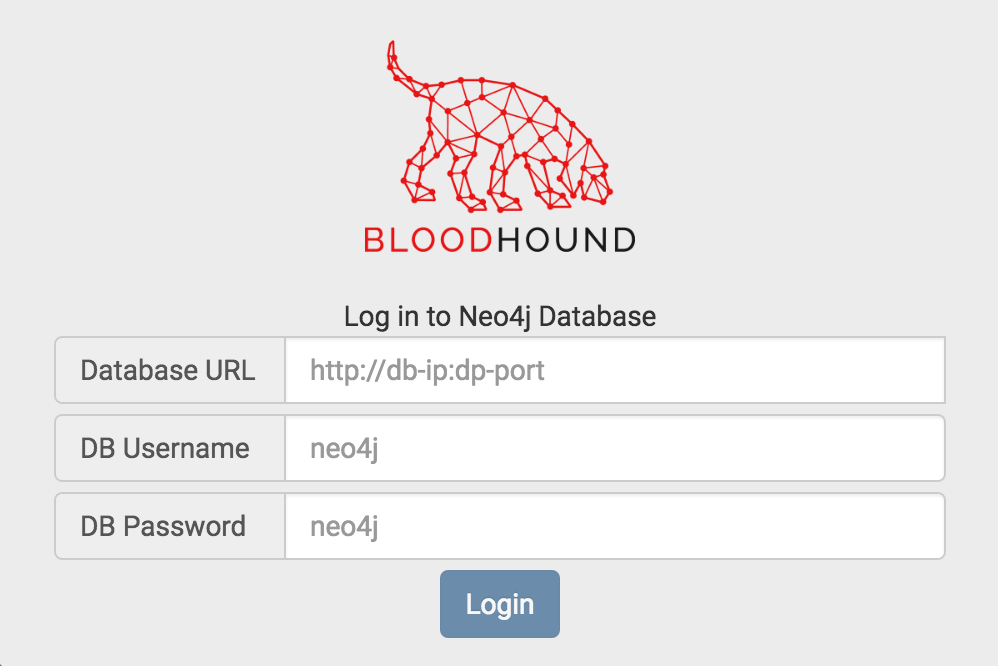
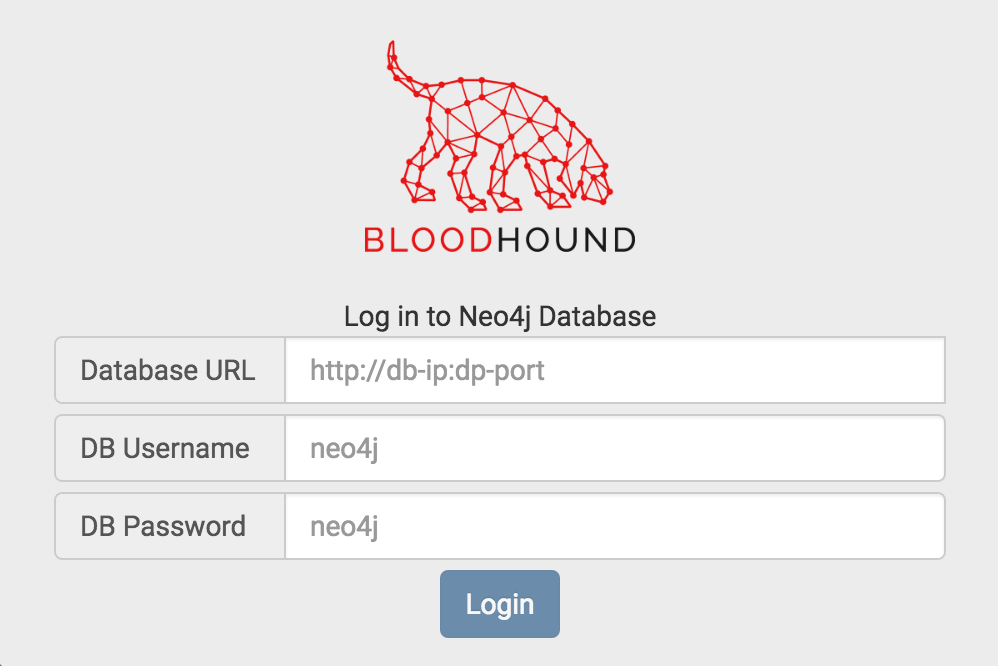
294Hack ToolsBloodhound v2.2 – Active Directory Toolkit
BloodHound is a single page Javascript web application, built on top of Linkurious, compiled with Electron, with a Neo4jdatabase fed by a PowerShell ingestor. BloodHound...
-

 239Hack Tools
239Hack Tools0xsp Mongoose – Linux Privilege Escalation Enumeration Toolkit
Using 0xsp mongoose you will be able to scan targeted operating system for any possible way for privilege escalation attacks,starting from collecting...
-

 216Hack Tools
216Hack ToolsPivotSuite – A Network Pivoting Toolkit
PivotSuite is a portable, platform independent and powerful network pivoting toolkit, Which helps Red Teamers / Penetration Testers to use a compromised...
-

 336Hack Tools
336Hack ToolsBeemka – Electron Exploitation Toolkit
Beemka shows how vulnerabilities in the Electron Framework could allow an attacker to inject malicious code inside a legitimate application without raising...
-
 322Hack Tools
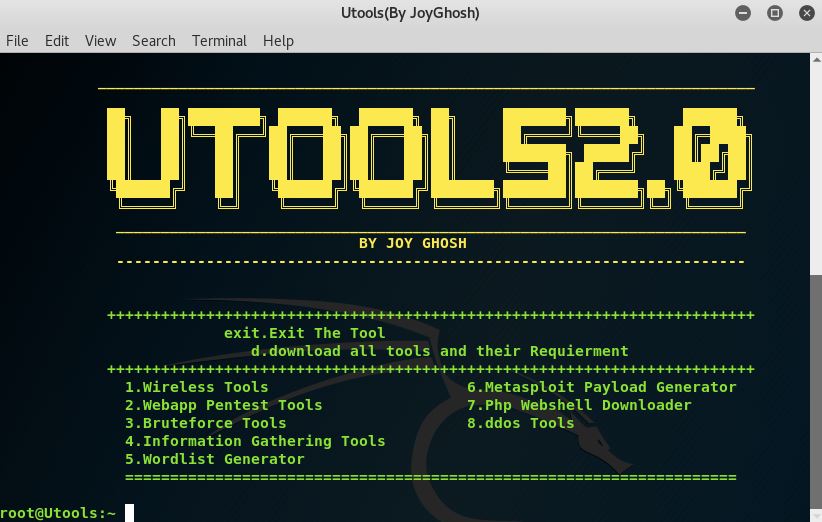
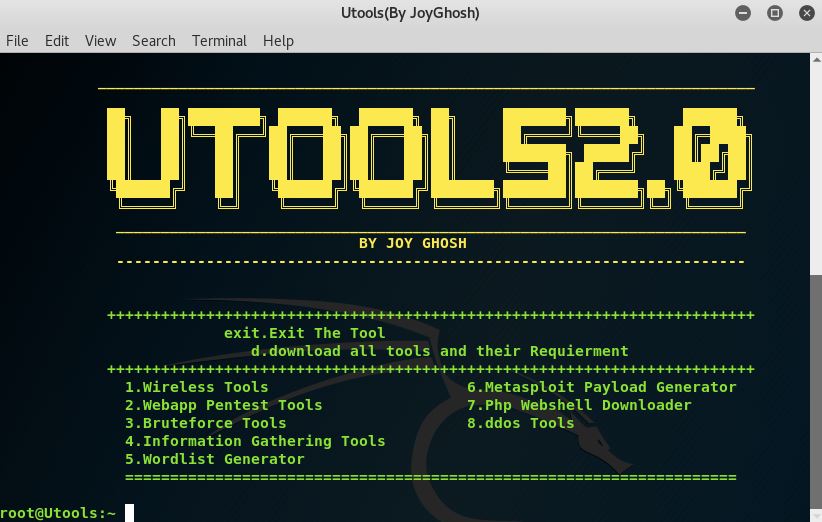
322Hack ToolsUtools2 – Hacking Toolkit
A simple one click to install and download, Utools2 toolkit contains some of the best hacking tools used and compiled into one...
-
 307Computer Forensics
307Computer ForensicsDeft X – Digital Evidence & Forensics Toolkit
Born from an idea of Stefano Fratepietro, DEFT (acronym for Digital Evidence & Forensics Toolkit) is a distribution made for Digital Forensics...
-

 292Hack Tools
292Hack ToolsCQTools – Ultimate Hacking Toolkit
This toolkit allows you to deliver complete attacks within the infrastructure, starting with sniffing and spoofing activities, going through information extraction, password...
-

 422Automated Pentest
422Automated PentestCQTools: The New Ultimate Hacking Toolkit
On March 27 and 28, 2019, Paula presented Briefings and Arsenal sessions at Black Hat Asia 2019 in Singapore. CQURE Team has...
-
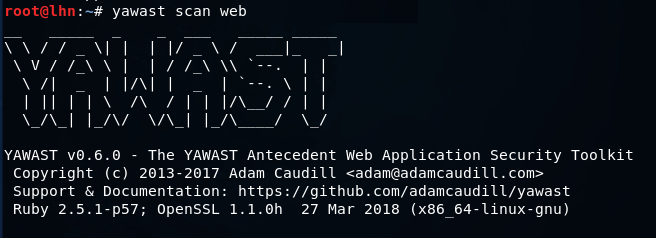
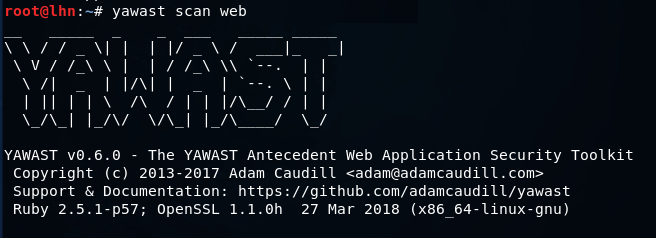 314Hacking Tools
314Hacking ToolsYAWAST – Open Source Web Application Information Gathering Toolkit
YAWAST is a web application penetration testing toolkit that can perform information gathering and basic vulnerabilities (misconfiguration) assessment tasks related to TLS/SSL,...
-
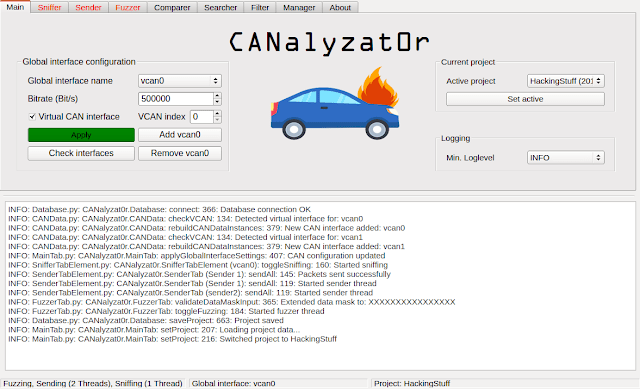
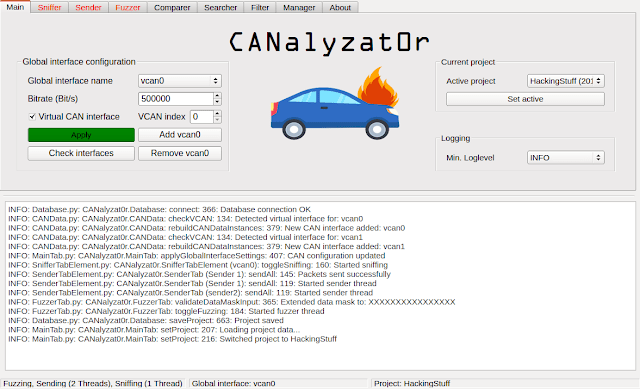 407Security Tools
407Security ToolsCANalyzat0r – Security Analysis Toolkit For Proprietary Car Protocols
This software project is a result of a Bachelor’s thesis created at SCHUTZWERK in collaboration with Aalen University by Philipp Schmied.Please refer...
-
 232Exploitation Tools
232Exploitation ToolsXSRFProbe – The Prime Cross Site Request Forgery Audit And Exploitation Toolkit
XSRFProbe is an advanced Cross Site Request Forgery (CSRF/XSRF) Audit and Exploitation Toolkit. Equipped with a Powerful Crawling Engine and Numerous Systematic...
-
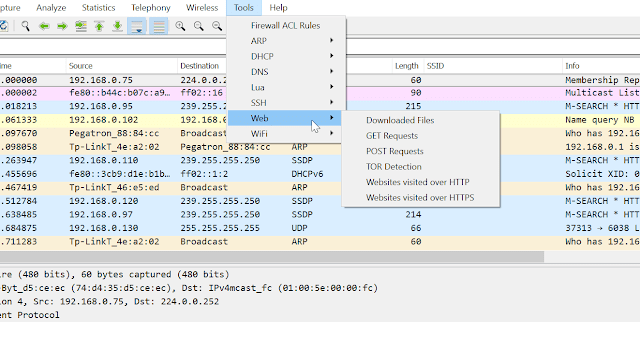
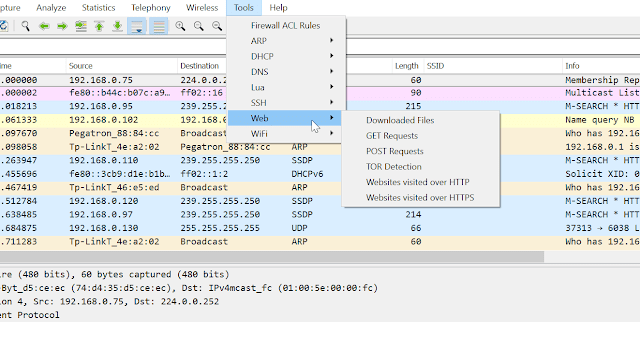 256Network Tools
256Network ToolsPA Toolkit – A Collection Of Traffic Analysis Plugins Focused On Security
PA Toolkit is a collection of traffic analysis plugins to extend the functionality of Wireshark from a micro-analysis tool and protocol dissector...
-

 229Hacking Tools
229Hacking ToolsXerosploit – Open Source Toolkit For Man In The Middle Attacks
Xerosploit is a python-based toolkit for creating efficient Man In The Middle attacks which combines the power of bettercap and nmap. The...
-
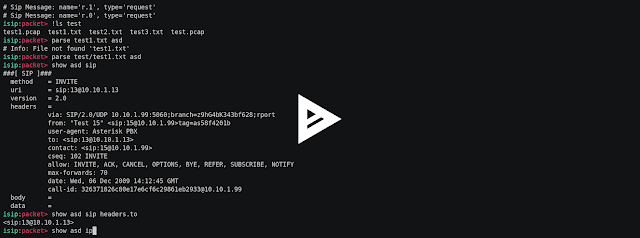
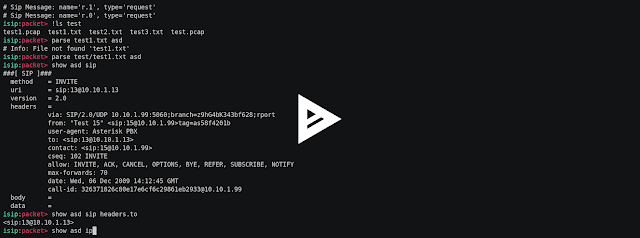 353Man-In-The-Middle
353Man-In-The-MiddleIsip – Interactive Sip Toolkit For Packet Manipulations, Sniffing, Man In The Middle Attacks, Fuzzing, Simulating Of Dos Attacks
Interactive sip toolkit for packet manipulations, sniffing, man in the middle attacks, fuzzing, simulating of dos attacks. Video Setup git clone https://github.com/halitalptekin/isip.git...
-
 261Exploitation Tools
261Exploitation ToolsBashark – Bash Post Exploitation Toolkit
Bashark aids pentesters and security researchers during the post-exploitation phase of security audits. Usage To launch Bashark on compromised host, simply source...
-
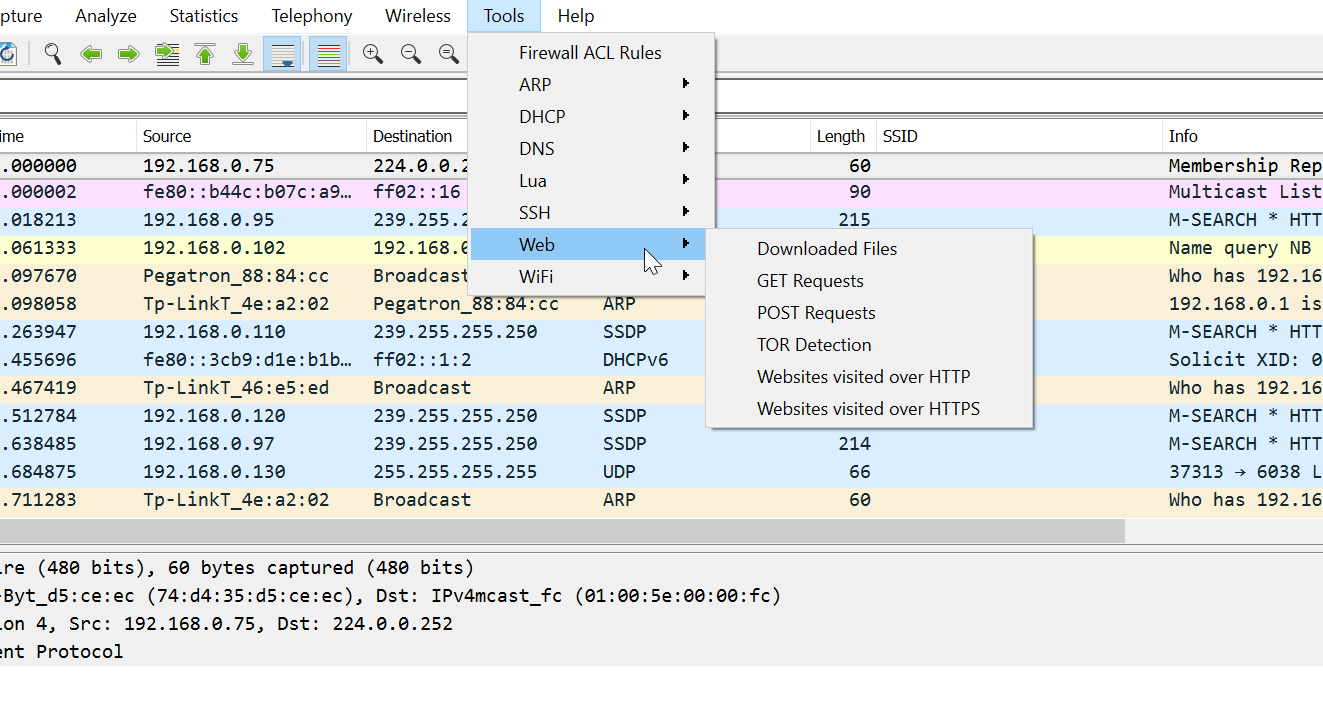
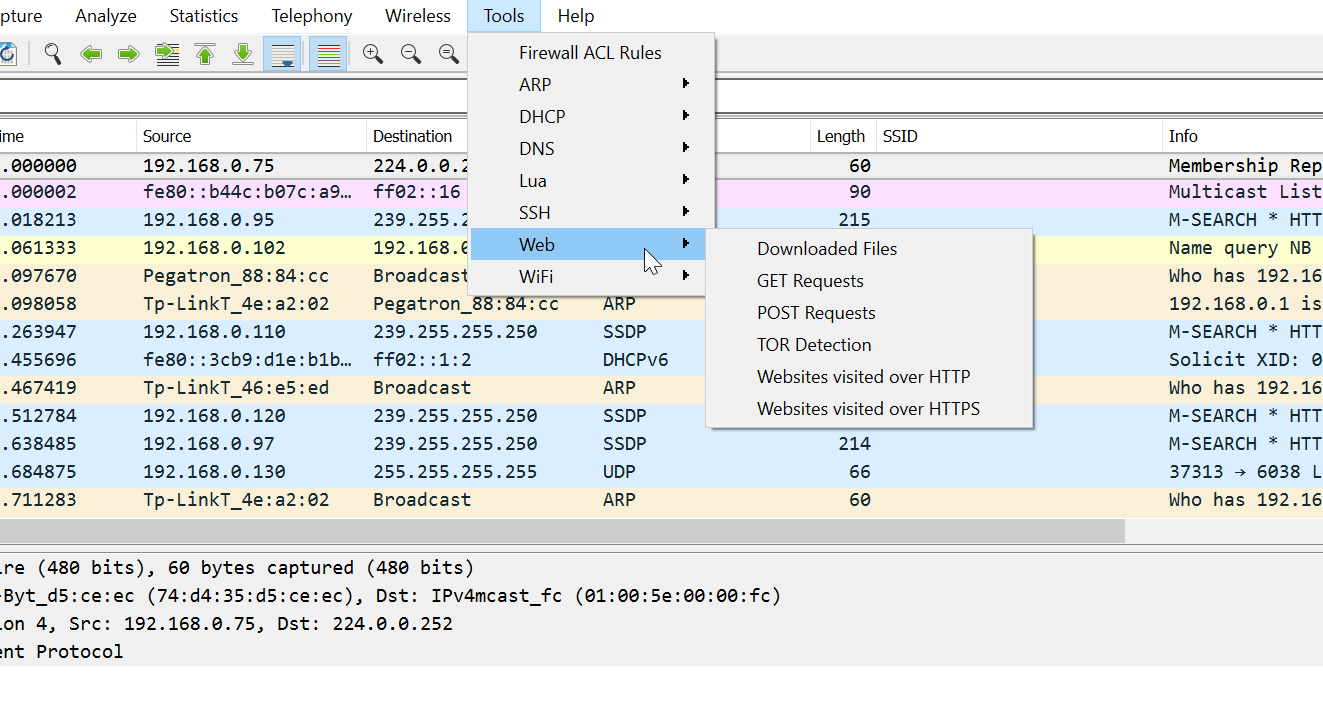 218Packet Manipulation
218Packet ManipulationPA Toolkit – Wireshark Extensions for Penetration Testers
PA Toolkit is a collection of traffic analysis plugins to extend the functionality of Wireshark from a micro-analysis tool and protocol dissector...
-

 497How To
497How ToUltimate Windows 10 Bloatware Removal Tool | MSMG Toolkit: Delete Bloatware, Cortana, Windows Defender
A Windows 10 OS installation that’s free of all the telemetry data collection, a nagging Cortana, and practically all bloatware — sounds...
-
 235Hacking Tools
235Hacking ToolsHabu – Open Source Network Penetration Testing Toolkit
Habu is an open source penetration testing toolkit that can perform various penetration testing tasks related to networks. These include ARP poisoning,...
-
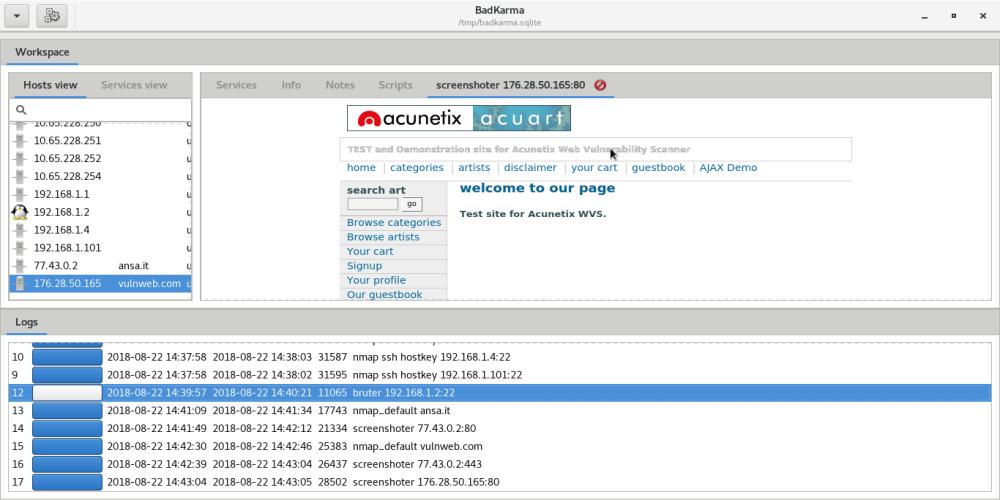
 247Enumeration
247EnumerationbadKarma – Advanced Network Reconnaissance Toolkit
badKarma is a python3 GTK+ toolkit that aim to assist penetration testers during all the network infrastructure penetration testing activity phases. It...
-
 243Hacking Tools
243Hacking ToolsLeviathan – Mass Audit Toolkit for Networks and Applications
Leviathan is an open source toolkit that can be used for auditing networks and web applications. The types of audits that can...
-

 305Mobile Hacking
305Mobile HackingScrounger – Mobile Application Testing Toolkit
Even though several other mobile application analysis tools have been developed, there is no one tool that can be used for both...






