Search results for "Vulnerable"
-
 906Malware
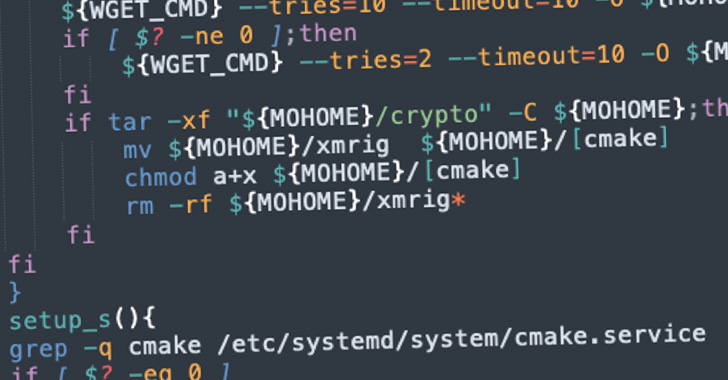
906MalwareNew Cryptojacking Campaign Targeting Vulnerable Docker and Kubernetes Instances
A new cryptojacking campaign has been uncovered targeting vulnerable Docker and Kubernetes infrastructures as part of opportunistic attacks designed to illicitly mine...
-

 1.0KMalware
1.0KMalwareBlackByte Ransomware Abuses Vulnerable Windows Driver to Disable Security Solutions
In yet another case of bring your own vulnerable driver (BYOVD) attack, the operators of the BlackByte ransomware are leveraging a flaw...
-
 938Malware
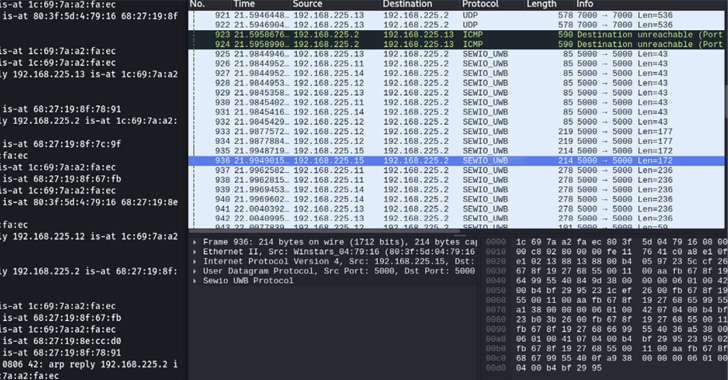
938MalwareRTLS Systems Found Vulnerable to MiTM Attacks and Location Tampering
Researchers have disclosed multiple vulnerabilities impacting Ultra-wideband (UWB) Real-time Locating Systems (RTLS), enabling threat actors to launch adversary-in-the-middle (AitM) attacks and tamper...
-
 4.4KMalware
4.4KMalwareGitHub Dependabot Now Alerts Developers On Vulnerable GitHub Actions
Cloud-based code hosting platform GitHub has announced that it will now start sending Dependabot alerts for vulnerable GitHub Actions to help developers...
-

 4.9KRansomware
4.9KRansomwareHive Ransomware Affiliate Attacking Microsoft Exchange Servers vulnerable to ProxyShell Flaw
The cybersecurity experts at Varonis security firm have recently discovered a Hive ransomware affiliate that has been deploying a variety of backdoors,...
-

 2.7KMalware
2.7KMalwareSquirrelwaffle malware takes control of vulnerable Microsoft Exchange servers to spread banking scam
Researchers at security firm Sophos recently reported a hacking campaign related to the ProxyLogon and ProxyShell exploits for the exploitation of an...
-

 1.8KMalware
1.8KMalwareOver 300,000 MikroTik Devices Found Vulnerable to Remote Hacking Bugs
At least 300,000 IP addresses associated with MikroTik devices have been found vulnerable to multiple remotely exploitable security vulnerabilities that have since...
-

 3.1KData Security
3.1KData SecurityHigh severity Intel chip flaw left cars, medical and IoT devices vulnerable
The vulnerability can be exploited by attackers with physical access to the CPU to breach the security protocols and obtain sensitive information....
-

 432Data Security
432Data SecurityDangerous hacking group attacks vulnerable Docker servers in cryptocurrency mining campaign
According to a report by Trend Micro, the hacking group identified as TeamTNT has been attacking Docker servers with exposed REST APIs...
-
 5.0KVulnerabilities
5.0KVulnerabilitiesMillions of Printers Worldwide Vulnerable To The 16-Year-Old Bug
Cybersecurity analysts have recently discovered a vulnerability in a common printer driver used by major manufacturers like HP, Xerox, and Samsung. This...
-

 2.4KVulnerabilities
2.4KVulnerabilitiesNVIDIA Jetson Chipsets Found Vulnerable to High-severity Flaws
U.S. graphics chip specialist NVIDIA has released software updates to address a total of 26 vulnerabilities impacting its Jetson system-on-module (SOM) series...
-

 1.8KMalware
1.8KMalwareInfamous Necro Python bot Added new Tools to Improve Its Chances of Infecting Vulnerable Systems
Nowadays, cyberattacks are increasing rapidly, and as per the report, most cybercriminals are using the automatic bot method to perform all kinds...
-

 2.5KVulnerabilities
2.5KVulnerabilitiesPDF certification process is vulnerable to new attack variants; flaws affect Adobe, Foxit and other PDF tools
A recent research states that certified PDF files are not protected enough, so they are vulnerable to various types of cyberattack. These...
-

 1.8KMalware
1.8KMalwareMagecart Group 12 launches a PHP skimmer targeting Magento’s vulnerable e-commerce platforms
Cybersecurity researchers have discovered that a new credit card theft malware has been implemented to bypass client-side detection on e-commerce sites running...
-

 1.8KVulnerabilities
1.8KVulnerabilitiesHundreds of Millions of Dell Systems Vulnerable to Hack Due to Driver Bug
The cybersecurity researchers have detected a set of five high-severity flaws in hundred of millions of Dell’s firmware update. The set of...
-

 2.1KVulnerabilities
2.1KVulnerabilitiesF5 BIG-IP Found Vulnerable to Kerberos KDC Spoofing Vulnerability
Cybersecurity researchers on Wednesday disclosed a new bypass vulnerability (CVE-2021-23008) in the Kerberos Key Distribution Center (KDC) security feature impacting F5 Big-IP...
-

 2.7KVulnerabilities
2.7KVulnerabilitiesPopular Netop Remote Learning Software Found Vulnerable to Hacking
Cybersecurity researchers on Sunday disclosed multiple critical vulnerabilities in remote student monitoring software Netop Vision Pro that a malicious attacker could abuse...
-

 3.9KHow To
3.9KHow ToFifty shades of vulnerable: How to play it safe with your smart sex toy
While you’re living out your fantasies, your internet-enabled sex toy may be setting you up for a privacy nightmare
-

 4.3KMalware
4.3KMalwareFreakOut, the new botnet that threatens thousands of vulnerable Linux systems
According to a recent report by cybersecurity experts, the operators of a botnet have been targeting non-patched applications running on Linux systems....
-
 2.6KRansomware
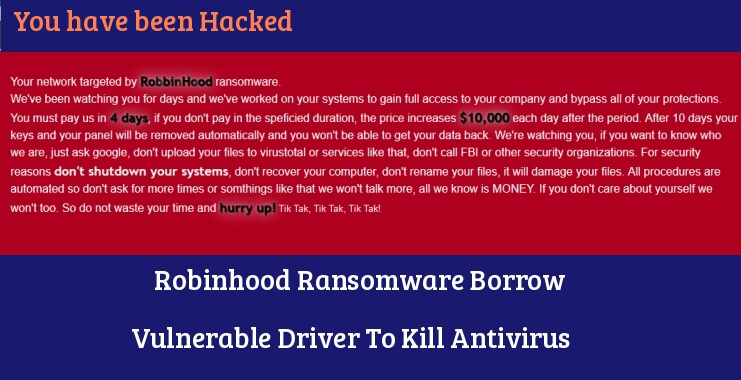
2.6KRansomwareRobinhood Ransomware Borrow Vulnerable Driver To Kill Antivirus and Encrypt Windows System Files
Researchers observed a new ransomware family called “Robinhood” that using a digitally signed vulnerable driver to bypass the protection by killing files...
-

 2.4KScams
2.4KScams5 major US wireless carriers vulnerable to SIM swapping attacks
When it comes to protection against this insidious type of scam, the telcos’ authentication procedures leave a lot be desired, a study...






