Search results for "Vulnerable"
-
 2.5KHack Tools
2.5KHack ToolsSplunk Attack Range – A Tool That Allows You To Create Vulnerable Instrumented Local Or Cloud Environments To Simulate Attacks Against And Collect The Data Into Splunk
The Attack Range solves two main challenges in development of detections. First, it allows the user to quickly build a small lab...
-
 1.7KNews
1.7KNewsNew Android SMS service, RCS vulnerable to hacking
With the rise of instant messaging applications such as WhatsApp, Signal, and Telegram. A large number of similar applications have begun to...
-

 504Malware
504MalwareNFC Beaming Vulnerability in Android Let Hackers to Infect Vulnerable Devices With Malware
NFC expanded as Near Field Communication, contains a set of protocols that allows Android devices to establish communication at a very shortest...
-

 4.4KVulnerabilities
4.4KVulnerabilitiesAvira Antivirus 2019 software is vulnerable; update as soon as possible
A recent investigation by vulnerability testing specialists at security firm SafeBreach Labs has revealed the presence of a critical vulnerability in the...
-
 453Vulnerabilities
453VulnerabilitiesSIM Cards in 29 Countries Vulnerable to Remote Simjacker Attacks
Until now, I’m sure you all might have heard of the SimJacker vulnerability disclosed exactly a month ago that affects a wide...
-

 423Vulnerabilities
423VulnerabilitiesPalo Alto, Fortinet and Pulse Secure VPNs are vulnerable to attacks: NSA
Ironically, companies that offer information security services are also exposed to malicious hackers; they’re even a great target. Experts from the National...
-

 450Geek
450GeekCopying Codes From Stack Overflow Leads To Vulnerable GitHub Projects
It is a common practice among programmers to copy-paste code snippets from the popular Q&A forum Stack Overflow to solve their coding...
-
 324Data Security
324Data SecurityNearly 400 million X-ray analyses exposed by vulnerable medical devices worldwide
After a group of IT system audit specialists performed an analysis on medical imaging systems connected to the public Internet, it has...
-

 440Vulnerabilities
440VulnerabilitiesAlmost every Cisco device is vulnerable to DoS attacks; fix now using this patch
It seems that companies will never stop being inconvenienced by some security flaws. Vulnerability testing experts report that Cisco has extended the...
-
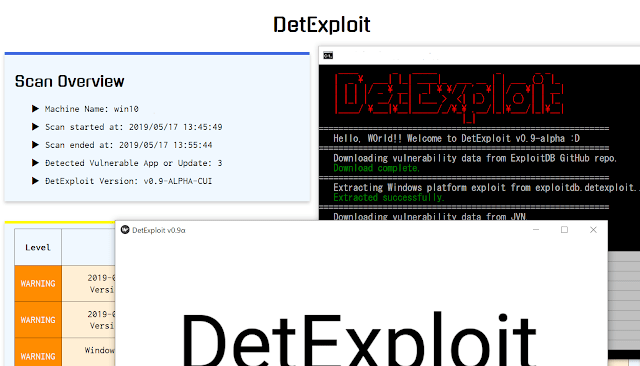
 371Vulnerability Analysis
371Vulnerability AnalysisDetExploit – Software That Detect Vulnerable Applications
DetExploit is software that detect vulnerable applications and not-installed important OS updates on the system, and notify them to user. As...
-
 463Surveillance
463Surveillance600,000 GPS child trackers found vulnerable to location tracking
Today the use of trackers has become widespread, particularly due to the fine balance found between their ease of use and the...
-

 388Hacked
388HackediPhone Is Vulnerable! How Websites Have Been Hacking iPhones For Years?
Today, security researchers at Google shattered the common belief that iPhones are non-susceptible to hacking. The researchers have revealed that a number...
-

 308Vulnerabilities
308Vulnerabilities40 OEM drivers like ASUS, Realtek, Gigabyte, Intel, AMD and Toshiba are vulnerable to hackers
A team of ethical hacking specialists from Eclypsium security firm has revealed a report describing a critical vulnerability present in the design...
-

 270News
270NewsSystems Using Intel Processors Vulnerable To SWAPGS Attack
A speculative execution vulnerability has been discovered by BitDefender researchers in systems running Intel modems built since 2012. SWAPGS vulnerability allows a...
-

 248Mobile Hacking
248Mobile HackingAndrill – Vulnerable Mobile Application with Various Levels
Andrill is an android mobile application interacting with a back-end API that is vulnerable with various levels of difficulty. It provides a...
-
 293Data Security
293Data SecurityWarning as small planes found vulnerable to hacking
The IT security researchers at Rapid7 have reported a critical vulnerability in the modern flight systems of small planes allowing hackers with...
-

 356Incidents
356IncidentsWill Cisco pay all its customers for selling vulnerable products as it paid US government?
Currently it is no longer uncommon to hear about cases where technology companies intentionally omit the security issues present in their products...
-

 216Vulnerabilities
216VulnerabilitiesDHS Warns Small Airplanes Vulnerable to Flight Data Manipulation Attacks
What could be more horrifying than knowing that a hacker can trick the plane’s electronic systems into displaying false flight data to...
-

 231News
231News1 Million+ ProFTPD Servers Vulnerable To Remote Code Execution Attacks
ProFTPD is an open-source and one of the most popular FTP server software used by more than one million servers all over...
-

 353News
353NewsWhatsApp, Telegram Vulnerable To ‘Media File Jacking’: Change Your Settings Now!
Instant messaging apps like WhatsApp and Telegram keep your messages encrypted in transit, but once a media file reaches your phone, the...
-

 215Vulnerabilities
215VulnerabilitiesZoom Video Conferencing for macOS Also Vulnerable to Critical RCE Flaw
The chaos and panic that the disclosure of privacy vulnerability in the highly popular and widely-used Zoom video conferencing software created earlier...






