Search results for "Vulnerable"
-
 239Vulnerability Scanners
239Vulnerability ScannersTROMMEL – Search Files For Potential Vulnerable Indicators
TROMMEL sifts through embedded device files to identify potential vulnerable indicators. The tool can be used to search files and configurations in...
-

 229News
229NewsExcel Power Query vulnerability puts 120 million users Vulnerable to Remote DDE Attacks
Recently, security researchers at the Mimecast Threat Center discovered a new vulnerability in the Microsoft Excel spreadsheet application, which has caused 120...
-
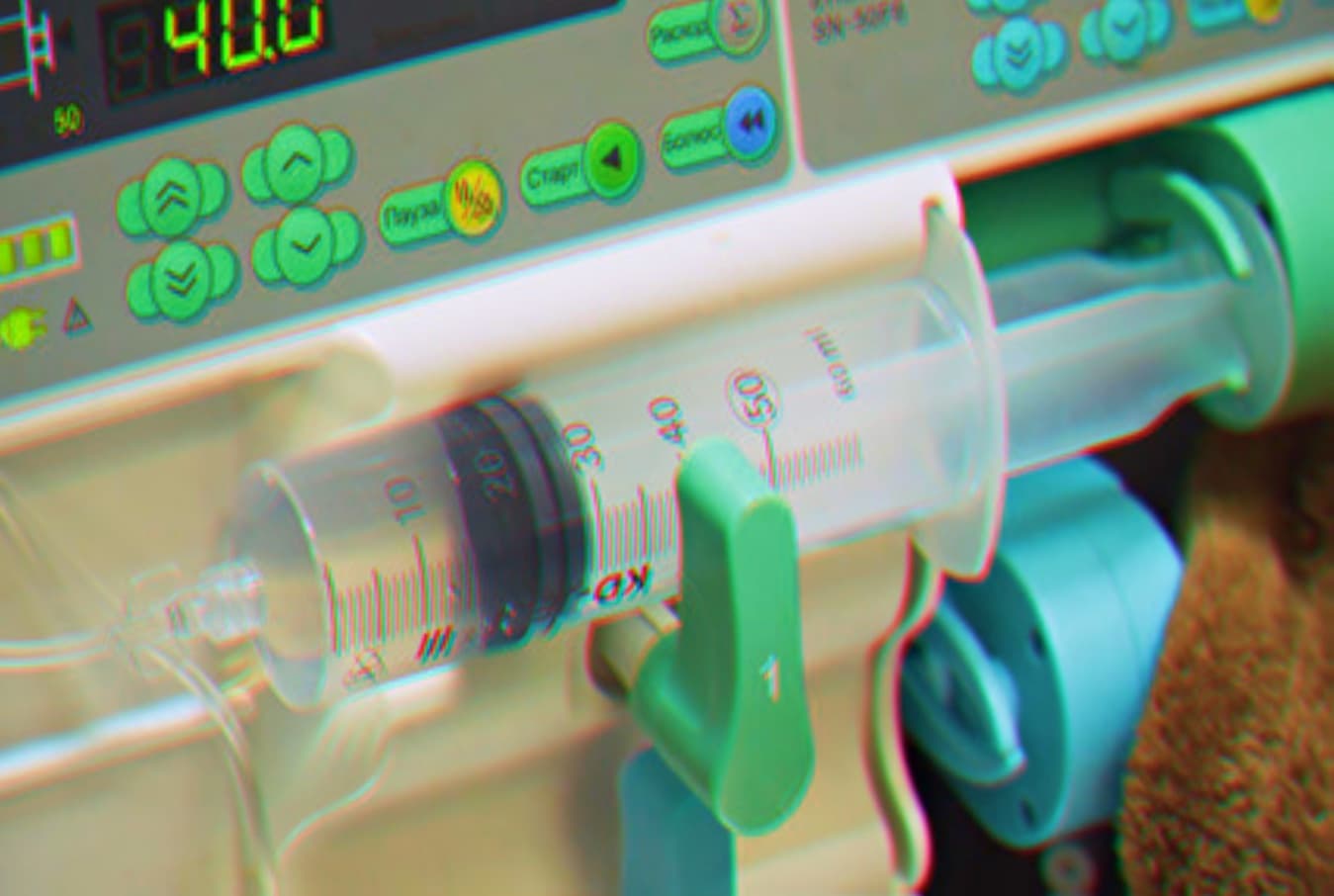
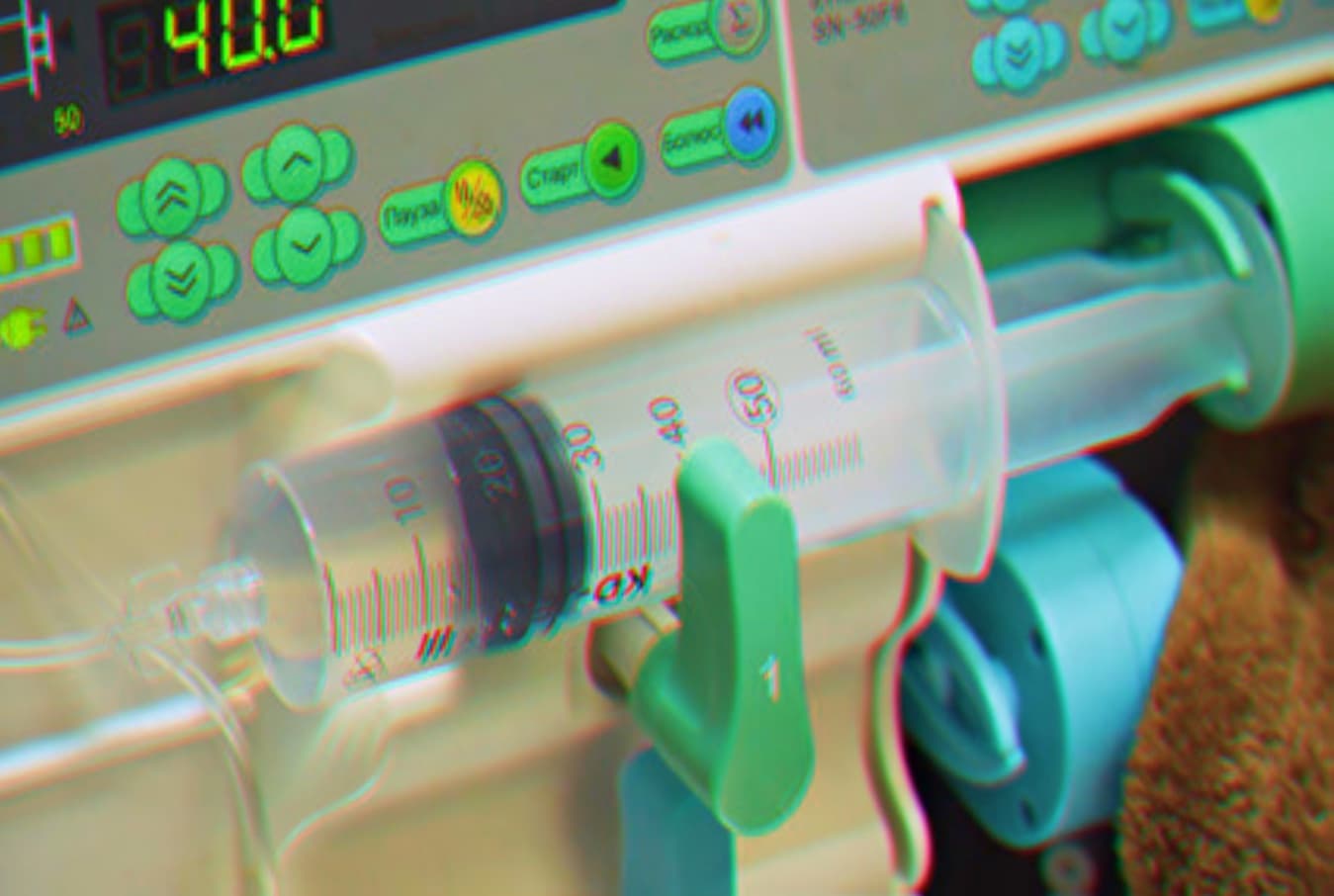 302Data Security
302Data SecurityVulnerable infusion pumps can be remotely accessed to change dosages
Critical Bug in Medical Infusion Pumps lets Attacker Remotely install Unauthorized Firmware to Change Medication Dosages. Researchers at CyberMDX, a healthcare security...
-

 260News
260NewsVictoria’s Public Health System “Highly Vulnerable”: Report
Victoria’s public health system is “highly vulnerable” to a Singapore-like data breach, according to a recent report. As per an auditor general...
-
 229Malware
229MalwareRCE Bug in Microsoft RDP Protocol Let Hackers Perform WannaCry Level Attack on 3 Million Vulnerable Endpoints
A critical remote execution vulnerability in Microsoft remote desktop services enables let attackers compromise the vulnerable system with WannaCry level malware. Microsoft...
-
 317Vulnerabilities
317Vulnerabilities5.0.8 and previous Linux kernel versions vulnerable to remote code execution
Linux operating system computers running versions prior to 5.0.8 kernel distributions are impacted by a vulnerability exposing systems committed to a wide...
-

 312News
312NewsD-Link IP Camera’s Unencrypted Cloud Infra, Vulnerable to MiTM Attacks
Cloud cameras (AKA IP Cameras) provide convenient and easy to use visual monitoring device for offices, houses, and shops of all sizes....
-

 297News
297News17-Yr-Old Finds Dell Laptops And PCs Are Vulnerable To Remote Attack
Dell laptop and computer owners beware! Your machine is vulnerable to an attack that can be executed remotely to hijack your system —...
-

 221News
221NewsDell Laptops and Computers Found Vulnerable to Attacks
According to research, February 2019, at the University of Cambridge, it was found that many modern laptops desktop computers are vulnerable to...
-

 211News
211News68% of Firms, Moderate to Extremely Vulnerable To Internal Threats
With malware infestation, data breaches allegedly caused by state-funded actors and phishing attacks becoming headlines in both mainstream media and tech news...
-

 315News
315News150 Million Xiaomi Devices Vulnerable To A Major Security Flaw
The purpose of security apps is to protect devices and user data. However, Xiaomi’s pre-installed security app did just the opposite and...
-

 298Vulnerabilities
298VulnerabilitiesFirefox 66.0.1 Released – Critical Security Vulnerabilities in Firefox Allows Hackers to Take Over the Vulnerable System
Firefox 66.0.1 Released with Fix for Critical Security Vulnerabilities that discovered via Trend Micro’s Zero Day Initiative. The vulnerability affects all the...
-

 335Data Security
335Data SecurityMedtronic defibrillators vulnerable to life threatening cyber attacks
Defibrillators are electronic devices manufactured to save the lives of people with life-threatening heart conditions such as Hypertrophic Cardiomyopathy (HCM). But now,...
-

 342News
342NewsWordPress Plugin WooCommerce is Vulnerable to XSS Attacks
As WordPress gained popularity over its CMS competitors like Joomla and Drupal, it grew to a level where plugin developers jumped into...
-

 231Data Security
231Data SecurityVulnerable smart alarms allowed hackers to track & turn off car engine
By gaining access to the vehicles, hackers can not only locate them but also open their doors and even turn off the...
-
 415Data Security
415Data SecurityOne of the most common and vulnerable passwords is ‘Ji32k7au4a83’
Experts explain why this combination of characters has been linked to multiple incidents of data breach According to network security and ethical...
-

 291Malware
291MalwareElasticsearch versions 1.4.2 and earlier vulnerable to malware infections
Two old vulnerabilities were exploited, allegedly by Chinese hackers The Cisco network security and ethical hacking teams recently detected intrusions from malicious...
-

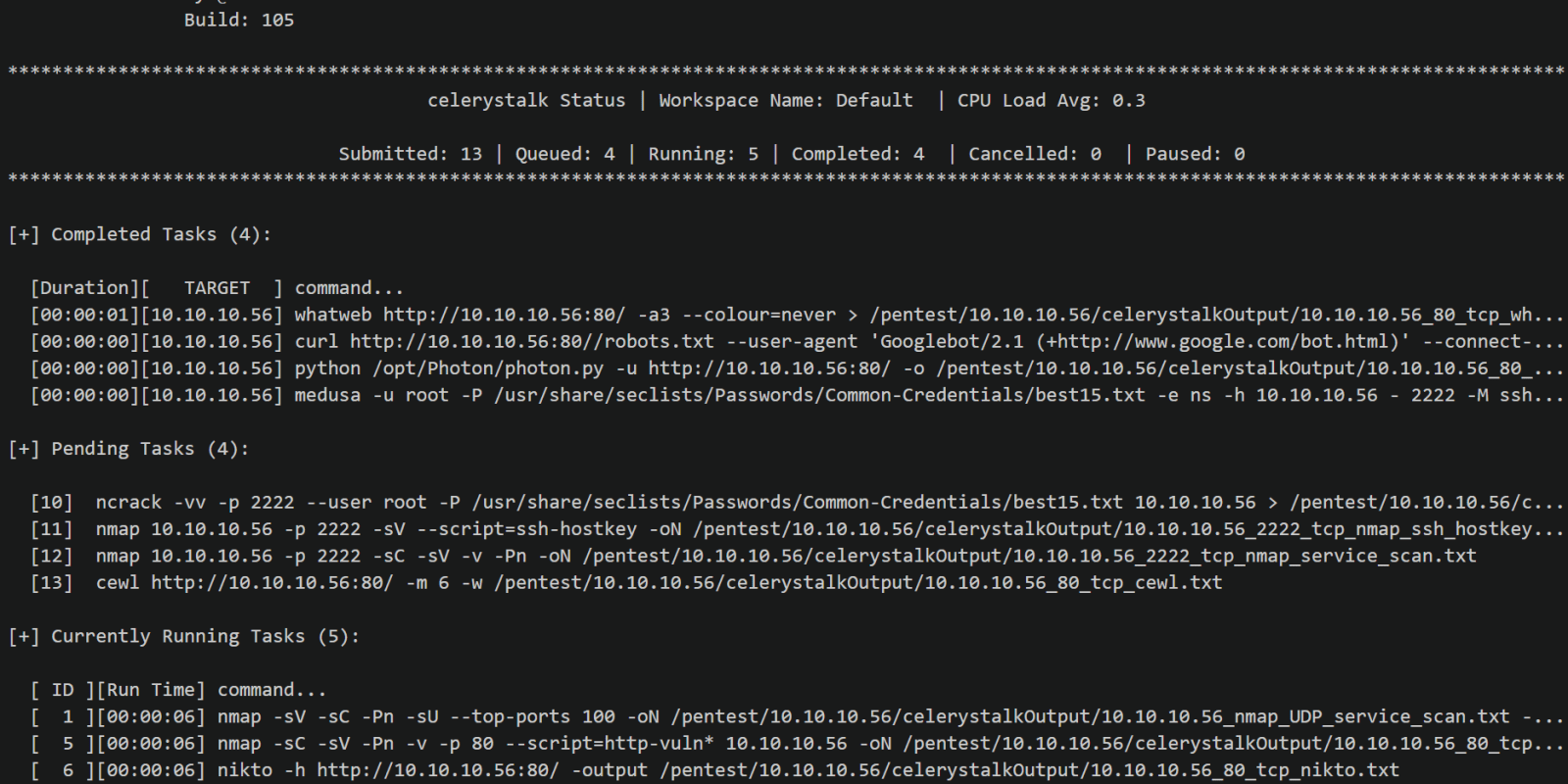
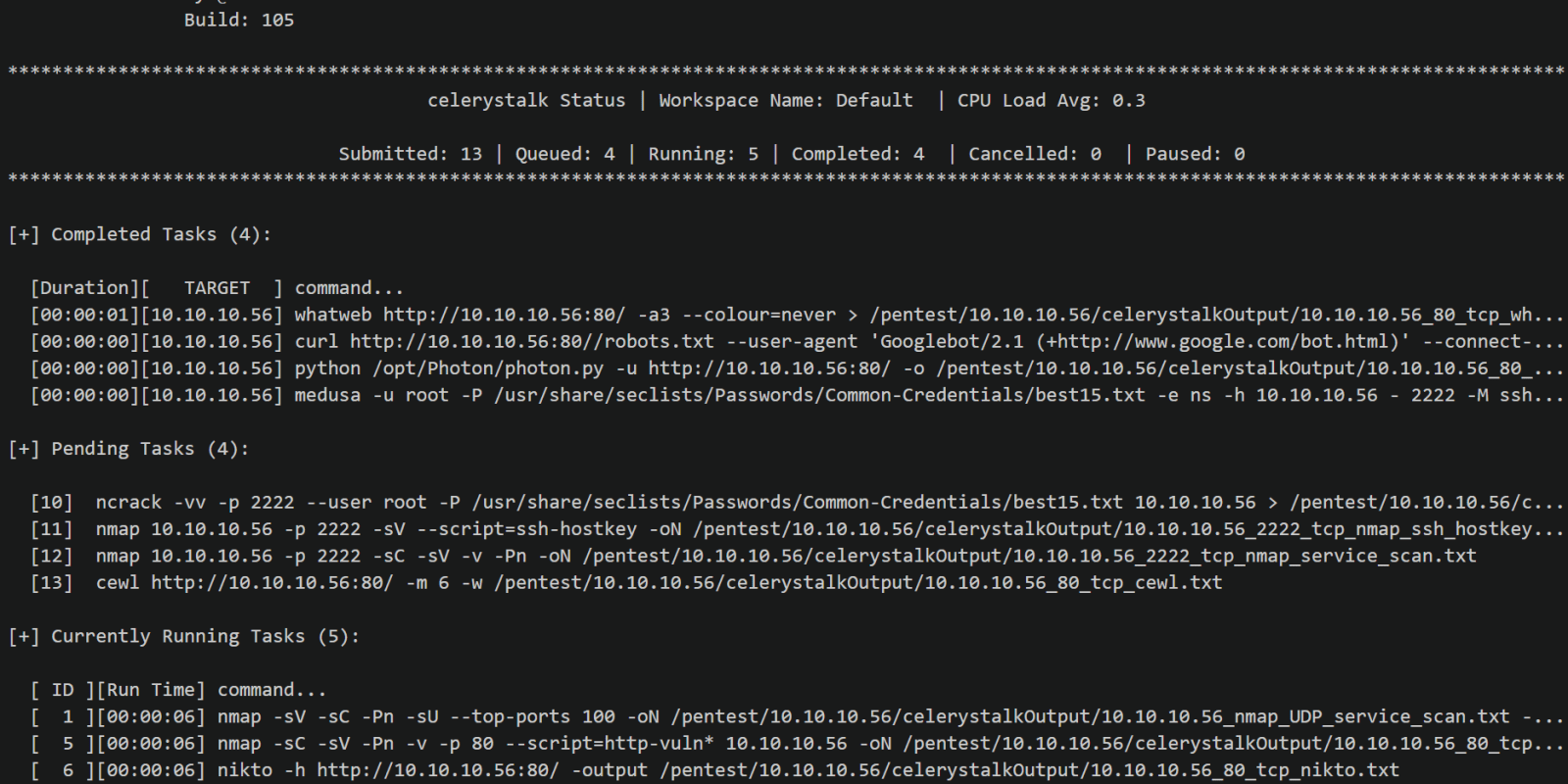
 324Information Gathering
324Information GatheringDCOMrade – Powershell Script For Enumerating Vulnerable DCOM Applications
DCOMrade is a Powershell script that is able to enumerate the possible vulnerable DCOM applications that might allow for lateral movement,...
-

 197Articles
197ArticlesXiaomi Electric Scooters Vulnerable to Life-Threatening Remote Hacks
Smart devices definitely make our lives easier, faster, and more efficient, but unfortunately, an insecure smart device can also ruin your day,...
-

 310News
310NewsVulnerable Legacy Systems Used By Banks, Need A Careful Review
The legacy-dependence of the financial sector is very evident, many banks are still using legacy hardware and software to perform their day-to-day...
-
 166Articles
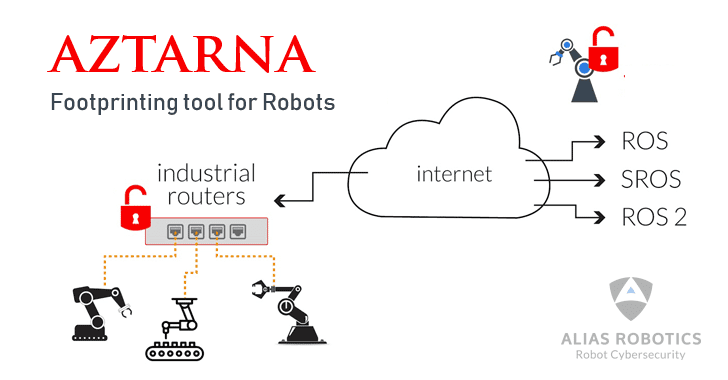
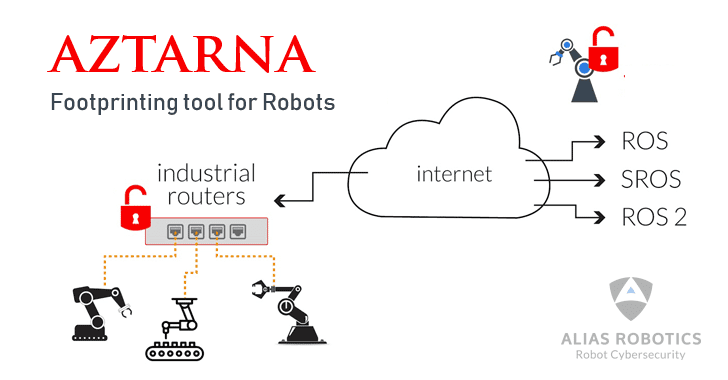
166ArticlesResearchers Release Tool That Finds Vulnerable Robots on the Internet
A team at a robot cybersecurity startup has released a free, open-source tool for information security professionals to help them easily ‘footprint’...






