Search results for "Vulnerable"
-

 235Vulnerabilities
235VulnerabilitiesNew Tool Automatically Finds and Hacks Vulnerable Internet-Connected Devices
Hacking just got fully automated for script kiddies. Hacking isn’t always hard. Some lower-tier hackers use programs to automatically churn through breached login details...
-

 469Geek
469Geek3 of 5 Fortune 500 companies vulnerable due to ManageEngine flaws
Hackers can exploit security flaws in ManageEngine software to gain administrator type control of the system. Digital Defense Inc., a San Antonio based IT security...
-

 289Cyber Crime
289Cyber CrimeCan you believe Distributed Grid is Vulnerable to Cyber-attack?
One of the major concerns for the US economy is to deal with Cyber security. The critical infrastructure like the energy system,...
-
 182Hack Tools
182Hack ToolsYasuo – Tool For Detecting Vulnerable & Exploitable 3rd-party Web Applications
Yasuo is a ruby script that scans for vulnerable 3rd-party web applications. There are over 10,000 remotely exploitable vulnerabilities that exist in...
-
 302Articles
302ArticlesIntel Chips Vulnerable To Hack
One of the biggest names in IT industry, Intel, has verified a report stating that some microprocessors have been built containing flaws...
-
 244Articles
244ArticlesThousands Of IoT Devices Are Vulnerable To Remote Code Execution
Security researchers from security firm Elttam have discovered a critical vulnerability (tracked as CVE-2017-17562) in GoAhead tiny web server that affects many...
-

 262Articles
262ArticlesvBulletin Vulnerable To Code Execution & File Deletion Flaws
Last week, security researchers have published the details of two possibly critical flaws affecting version 5 of the vBulletin forum software. vBulletin...
-

 203Articles
203ArticlesAT&T DirecTV WVB Devices Are Vulnerable To Code Execution
The security vulnerability was discovered in the Linksys WVBR0-25 wireless video bridge, which was designed to enable the main Genie DVR to...
-

 156Cyber Attack
156Cyber AttackMajor Banking Apps Are Vulnerable To Man In The Middle Attack Over SSL
Man In The Middle Attack Over SSL A group of security researchers found a critical man in the middle attack implementation gap...
-

 361Vulnerabilities
361VulnerabilitiesMan-in-the-middle flaw left smartphone banking apps vulnerable
A flaw in certificate pinning exposed customers of a number of high-profile banks to man-in-the-middle attacks on both iOS and Android devices....
-

 283Vulnerabilities
283VulnerabilitiesAmazon Echo and Google Home were vulnerable to Bluetooth exploit
Don’t worry, these vulnerabilities have already been patched out. Back in September, Bluetooth-connected device owners got a little scare when security firm...
-

 396Geek
396GeekAmazon Echo and Google Home Devices Vulnerable to BlueBorne Attack
In September 2017, the IT security researchers at Armis found eight zero-day vulnerabilities in Bluetooth protocol. Dubbed BlueBorne by researchers, these vulnerabilities affected...
-

 326Vulnerabilities
326VulnerabilitiesDHS – Tests demonstrate Boeing 757 airplanes vulnerable to hacking
Researchers and private industry experts, along with DHS officials, remotely hacked a Boeing 757 airplane that was parked at the airport in...
-
 269Malware
269MalwareAll Android Version Except 8.0/Oreo are Vulnerable to Toast Overlay Malware Attack
A First Android malware called TOASTAMIGO has been discovered that capable of installing other malware into infected devices using Toast Overlay attack. Overlay...
-

 466Google Dorks
466Google DorksGoogle Dorks To Find Vulnerable WordPress Sites
WordPress is one of the most popular blogging applications in the world and its easy to install. This can make WordPress a...
-
 262Vulnerabilities
262VulnerabilitiesIndustrial Products of many vendors still vulnerable to KRACK attack
Many industrial networking devices from various vendors are still vulnerable to the recently disclosed KRACK attack (Key Reinstallation Attack). Many industrial networking devices...
-

 340News
340NewsShips Are Vulnerable to Cyber Attacks Due To Maritime Platform Flaw
Previously it was reported that hackers can take over ships by exploiting critical vulnerabilities in VSAT communication system. Now, security consulting firm...
-
Articles
Security Flaw in LG IoT Software Left Home Appliances Vulnerable
LG has updated its software after security researchers spotted a flaw that allowed them to gain control of devices like refrigerators, ovens,...
-

 341How To
341How ToHow To Find Vulnerable Webcams Around The World
Today I am going to tell you how to Find Vulnerable Webcams Using Shodan THIS IS FOR EDUCATIONAL PURPOSE ONLY, I AM NOT...
-

 205Vulnerability Analysis
205Vulnerability AnalysisDorkNet – Selenium Powered Python Script To Automate Searching For Vulnerable Web Apps
Selenium powered Python script to automate searching the web for vulnerable applications. DorkNet can take a single dork or a list of...
-
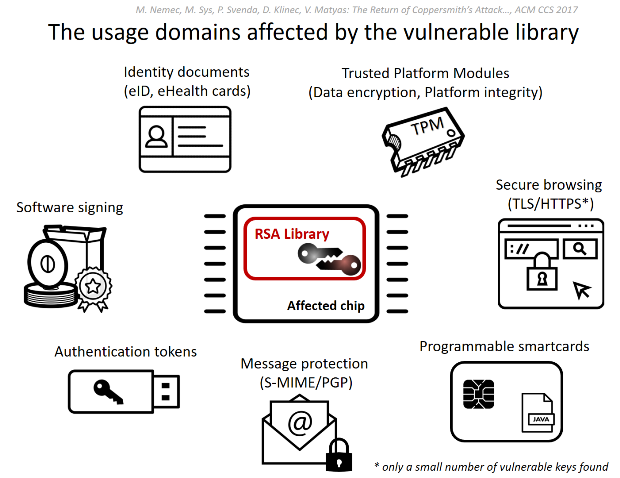
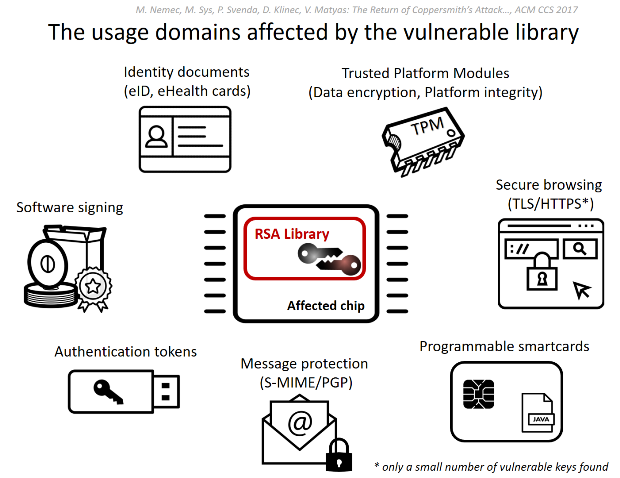 451Vulnerabilities
451VulnerabilitiesROCA: Vulnerable RSA generation (CVE-2017-15361)
A newly discovered vulnerability in generation of RSA keys used by a software library adopted in cryptographic smartcards, security tokens and other...






