All posts tagged "Hacking"
-
 4.4KMalware
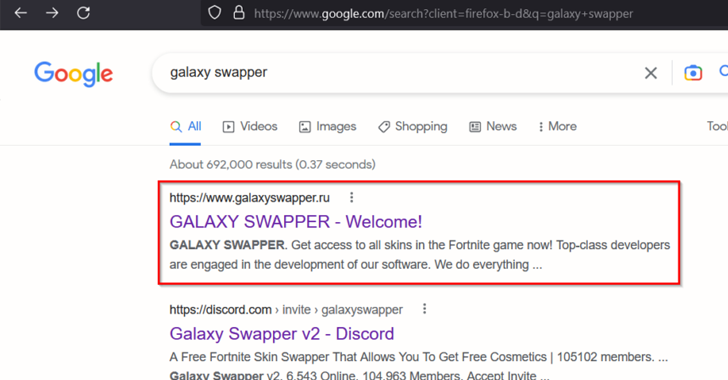
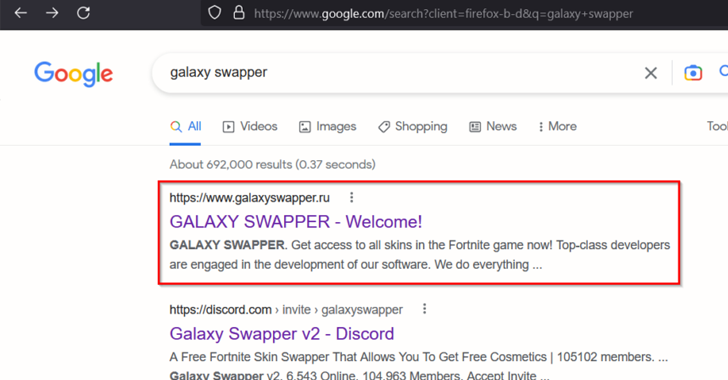
4.4KMalwareNew DotRunpeX Malware Delivers Multiple Malware Families via Malicious Ads
A new piece of malware dubbed dotRunpeX is being used to distribute numerous known malware families such as Agent Tesla, Ave Maria,...
-

 3.0KMalware
3.0KMalwareFakeCalls Vishing Malware Targets South Korean Users via Popular Financial Apps
An Android voice phishing (aka vishing) malware campaign known as FakeCalls has reared its head once again to target South Korean users...
-
 2.2KMalware
2.2KMalwareA New Security Category Addresses Web-borne Threats
In the modern corporate IT environment, which relies on cloud connectivity, global connections and large volumes of data, the browser is now...
-

 1.6KData Breach
1.6KData BreachMultiple Hacker Groups Exploit 3-Year-Old Vulnerability to Breach U.S. Federal Agency
Multiple threat actors, including a nation-state group, exploited a critical three-year-old security flaw in Progress Telerik to break into an unnamed federal...
-

 4.4KVulnerabilities
4.4KVulnerabilitiesMicrosoft Rolls Out Patches for 80 New Security Flaws — Two Under Active Attack
Microsoft’s Patch Tuesday update for March 2023 is rolling out with remediations for a set of 80 security flaws, two of which...
-

 4.4KMalware
4.4KMalwareLarge-scale Cyber Attack Hijacks East Asian Websites for Adult Content Redirects
A widespread malicious cyber operation has hijacked thousands of websites aimed at East Asian audiences to redirect visitors to adult-themed content since...
-
 1.7KMalware
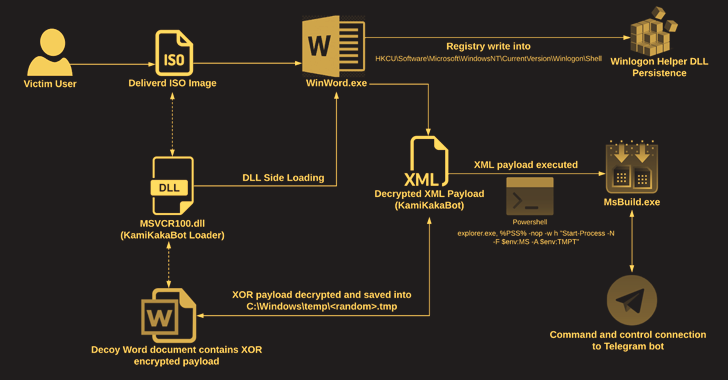
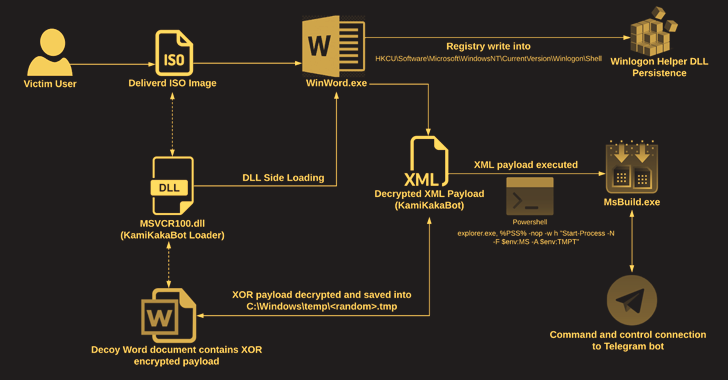
1.7KMalwareKamiKakaBot Malware Used in Latest Dark Pink APT Attacks on Southeast Asian Targets
The Dark Pink advanced persistent threat (APT) actor has been linked to a fresh set of attacks targeting government and military entities...
-

 4.7KMalware
4.7KMalwareExperts Warn of ‘Beep’ – A New Evasive Malware That Can Fly Under the Radar
Cybersecurity researchers have unearthed a new piece of evasive malware dubbed Beep that’s designed to fly under the radar and drop additional...
-
 1.4KMalware
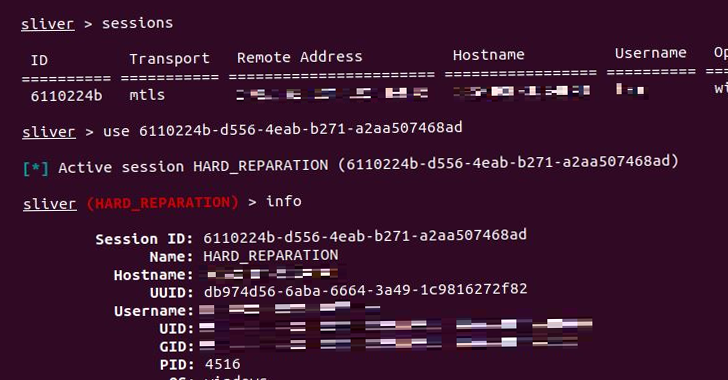
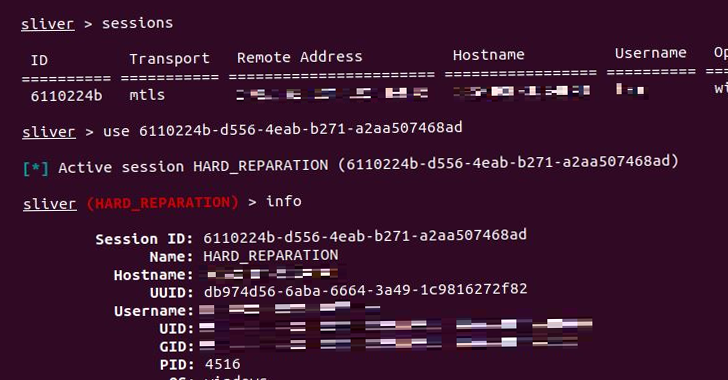
1.4KMalwareHackers Exploit Vulnerabilities in Sunlogin to Deploy Sliver C2 Framework
Threat actors are leveraging known flaws in Sunlogin software to deploy the Sliver command-and-control (C2) framework for carrying out post-exploitation activities. The...
-
 5.2KMalware
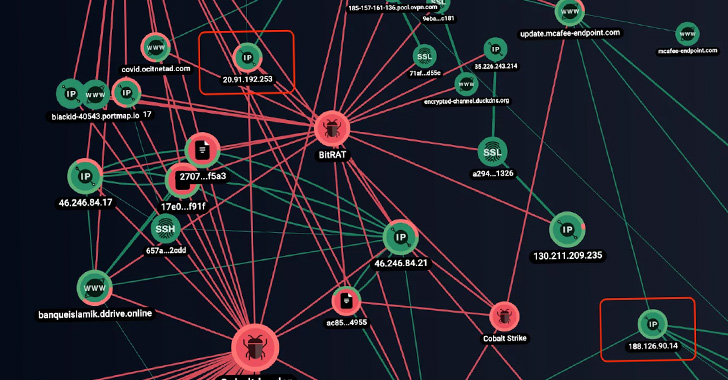
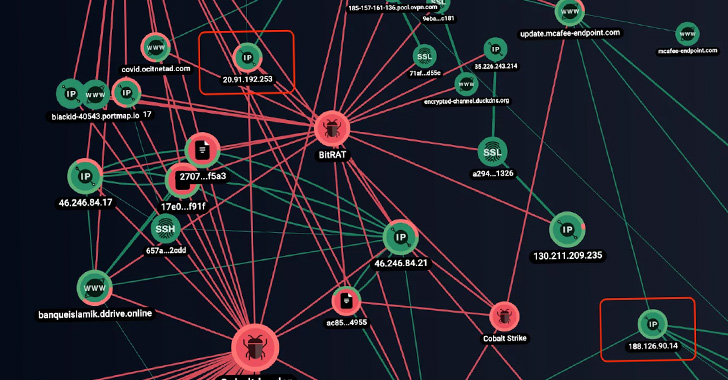
5.2KMalwareOPERA1ER APT Hackers Targeted Dozens of Financial Organizations in Africa
A French-speaking threat actor dubbed OPERA1ER has been linked to a series of more than 30 successful cyber attacks aimed at banks,...
-
 3.7KMalware
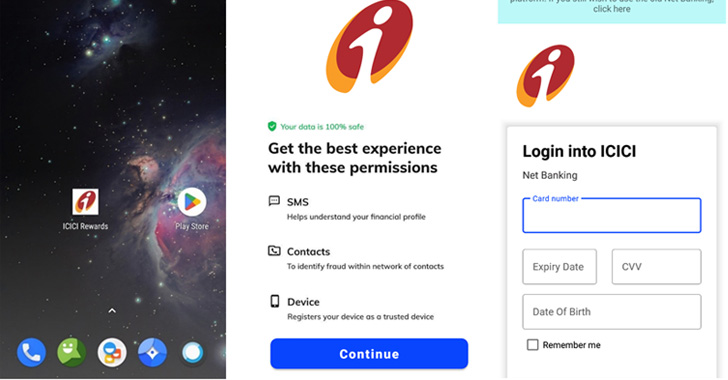
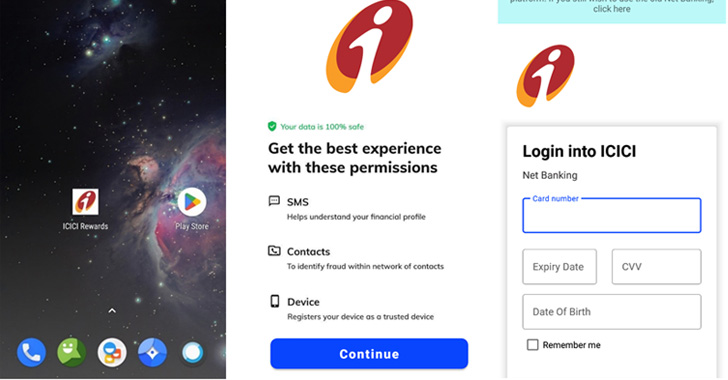
3.7KMalwareFake Indian Banking Rewards Apps Targeting Android Users with Info-stealing Malware
An SMS-based phishing campaign is targeting customers of Indian banks with information-stealing malware that masquerades as a rewards application. The Microsoft 365...
-

 1.8KMalware
1.8KMalwareU.S. Charges 3 Iranian Hackers and Sanctions Several Others Over Ransomware Attacks
The U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) on Wednesday announced sweeping sanctions against ten individuals and two entities backed...
-
 1.5KMalware
1.5KMalwareResearchers Warn of “Eternity Project” Malware Service Being Sold via Telegram
An unidentified threat actor has been linked to an actively in-development malware toolkit called the “Eternity Project” that lets professional and amateur...
-
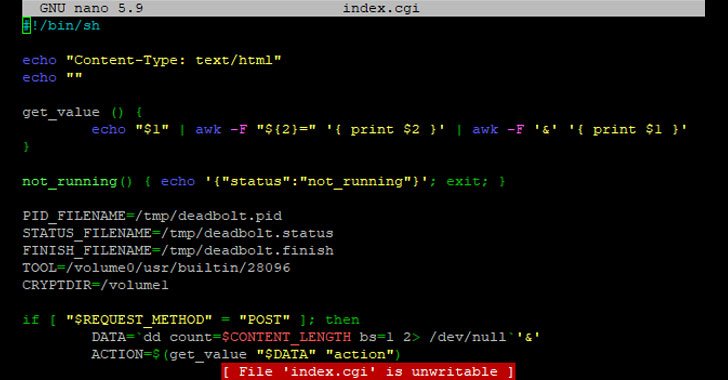
 4.5KMalware
4.5KMalwareWarning — Deadbolt Ransomware Targeting ASUSTOR NAS Devices
ASUSTOR network-attached storage (NAS) devices have become the latest victim of Deadbolt ransomware, less than a month after similar attacks singled out...
-

 1.2KNews
1.2KNewsT-Mobile’s latest data breach exposed users to SIM swapping attacks
T-Mobile is the only telecom giant to suffer at least three known data breaches in 2021. Another day, another data breach at...
-
 2.9KNews
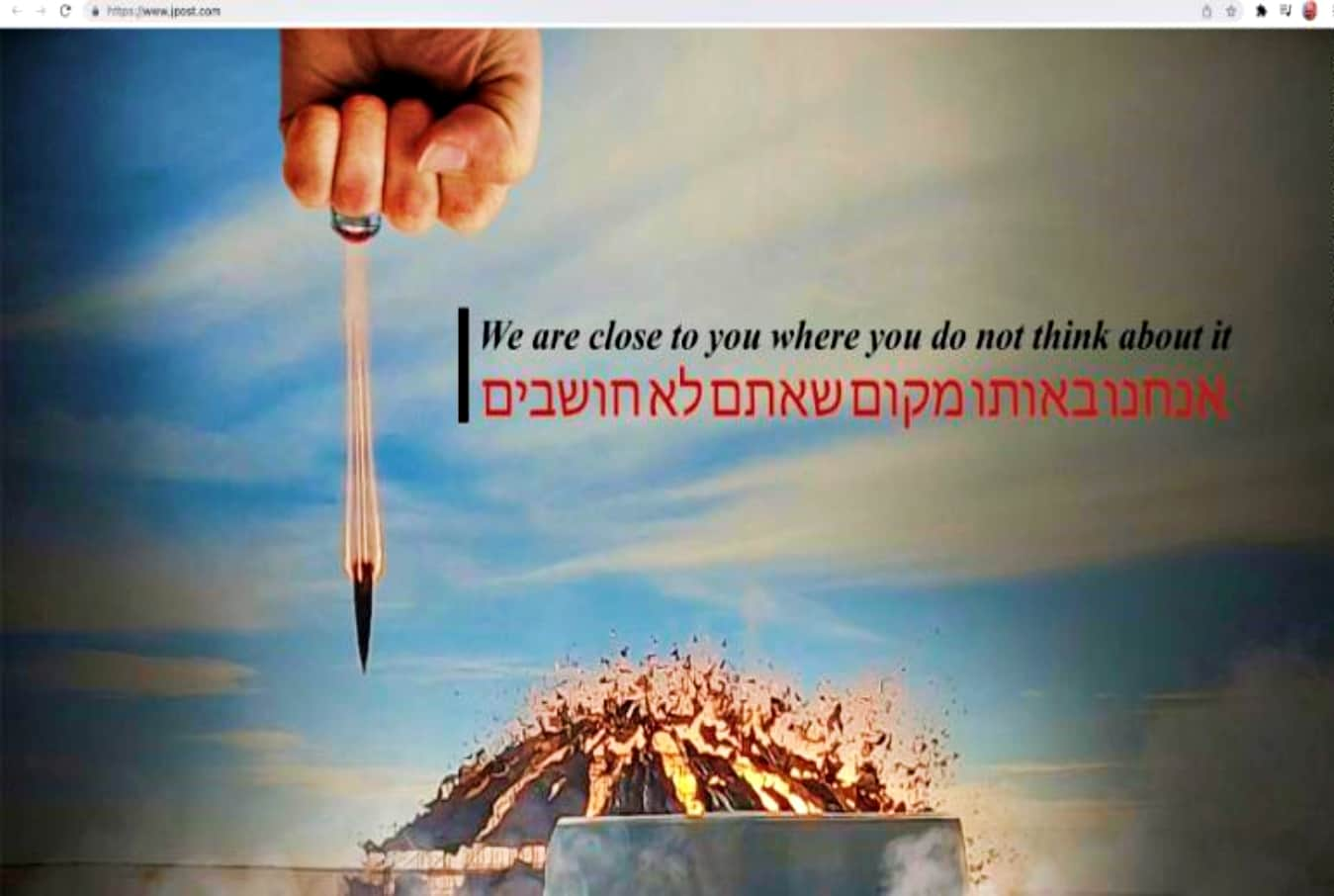
2.9KNewsJerusalem Post and Maariv hacked on Gen. Soleimani’s death anniversary
On the morning of Monday 3rd, Jan 2022, hackers managed to deface the official website of Jerusalem Post and compromise Maariv’s Twitter...
-
 4.0KData Security
4.0KData SecuritySoftware flaws in walk-through metal detectors made them hackable
Walk-through metal detectors manufactured by well-known U.S.-based firm Garett are vulnerable to remote attacks, according to Cisco Talos. Researchers at Cisco Talos discovered as...
-

 613Data Security
613Data SecurityGrim Finance hacked – $30 million worth of tokens stolen
According to Grim Finance, it was an “advanced attack” in which hackers exploited a flaw in the vault contract. Grim Finance, a...
-
 4.2KData Security
4.2KData SecurityAvast found backdoor in US Federal Agency Network
Avast Threat Intelligence Team stated that it tried to notify the agency about the intrusion but didn’t receive any favorable response, which...
-
 4.6KData Security
4.6KData SecurityTwo backdoors detected in Auerswald VoIP ystem
The backdoors were detected during penetration testing by RedTeam Pentesting GmbH. On December 20th, it was reported that a backdoor was found...
-

 3.9KCyber Events
3.9KCyber EventsTop workforce management firm Kronos hit by ransomware attack
Kronos has taken down its private cloud services and advises customers to use “alternative business continuity protocols” while the company is working...






