All posts tagged "Hacking"
-

 5.1KCyber Crime
5.1KCyber CrimeUS offers $10m reward for decisive info on DarkSide ransomware gang
The U.S. Department of State is paying an additional $5 million to anyone who can provide information leading to the arrest or...
-
 3.5KCyber Crime
3.5KCyber CrimeTwitter hacker charged in sim swapping, cryptocurrency scheme
The 22-year-old British national Joseph James O’Connor, aka PlugwalkJoe, was one of the hackers behind 2020’s massive Twitter hack – PlugwalkJoe also stole...
-

 5.4KCyber Crime
5.4KCyber CrimeConti ransomware gang apologized to Arab Royals over data leak
The data leak took place last month when the infamous Conti ransomware gang hacked Graff, a UK-based jewelry store Graff popular amongst...
-

 3.4KNews
3.4KNewsRansom fail: Iranian hackers leak trove of Israeli LGBTQ dating app data
Iranian Hackers Leaked Private Messages and sensitive data of 690,000 Israeli LGBTQ Dating App Atraf Users After $1 Million Ransom is Denied....
-

 5.1KData Security
5.1KData SecurityResearcher found 70% Wi-Fi networks in Tel Aviv are hackable
While examining Wi-Fi networks in Tel Aviv, Israel, 70% or around three-quarters of home and small-scale office Wi-Fi network passwords were vulnerable...
-

 4.7KData Security
4.7KData SecurityTrojan Source attack lets hackers exploit source code
Trojan Source attack impacts all popular programming language compilers, such as C, C++, C#, Java, JavaScript, Python, Rust, and Go. A research...
-
 4.3KCyber Events
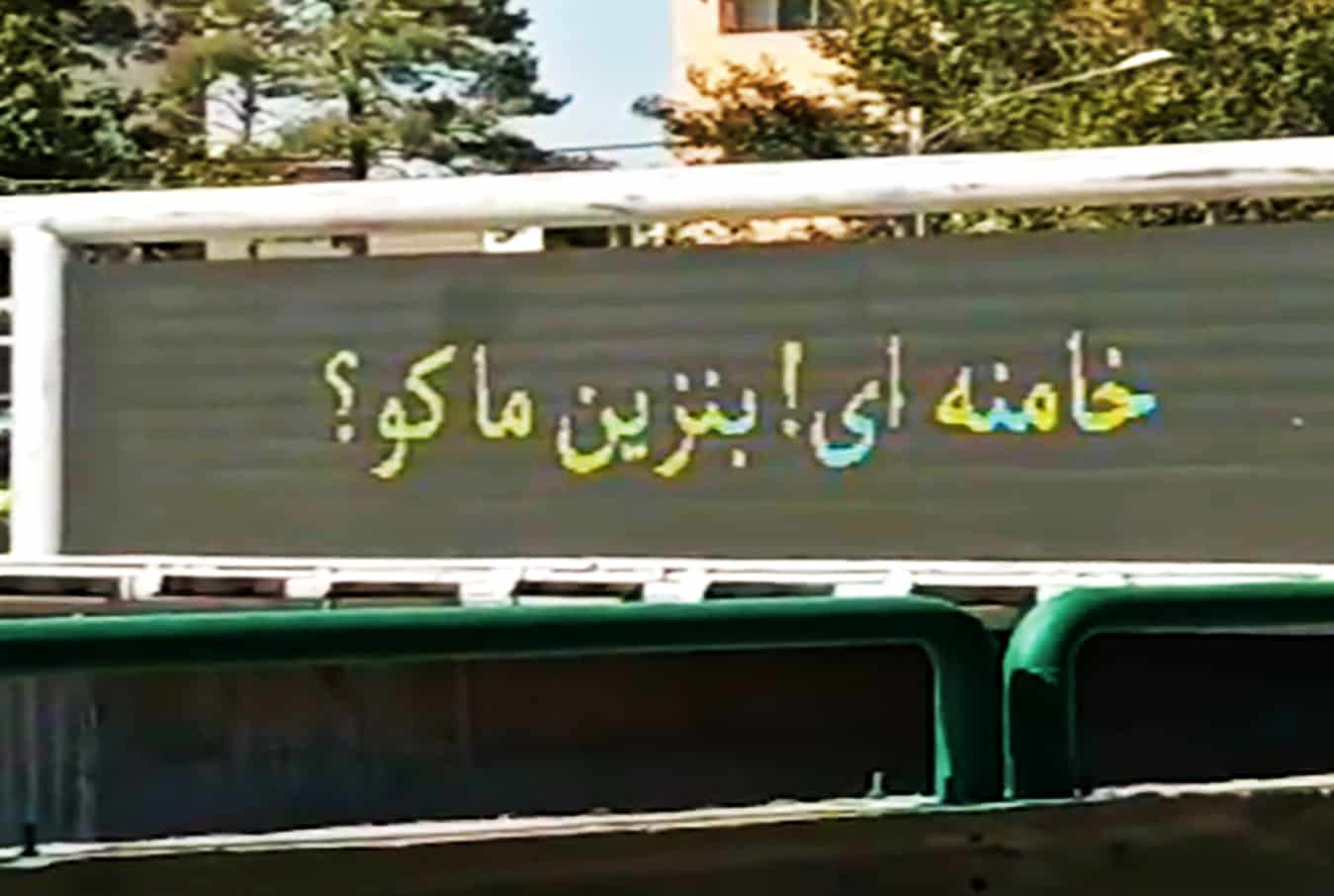
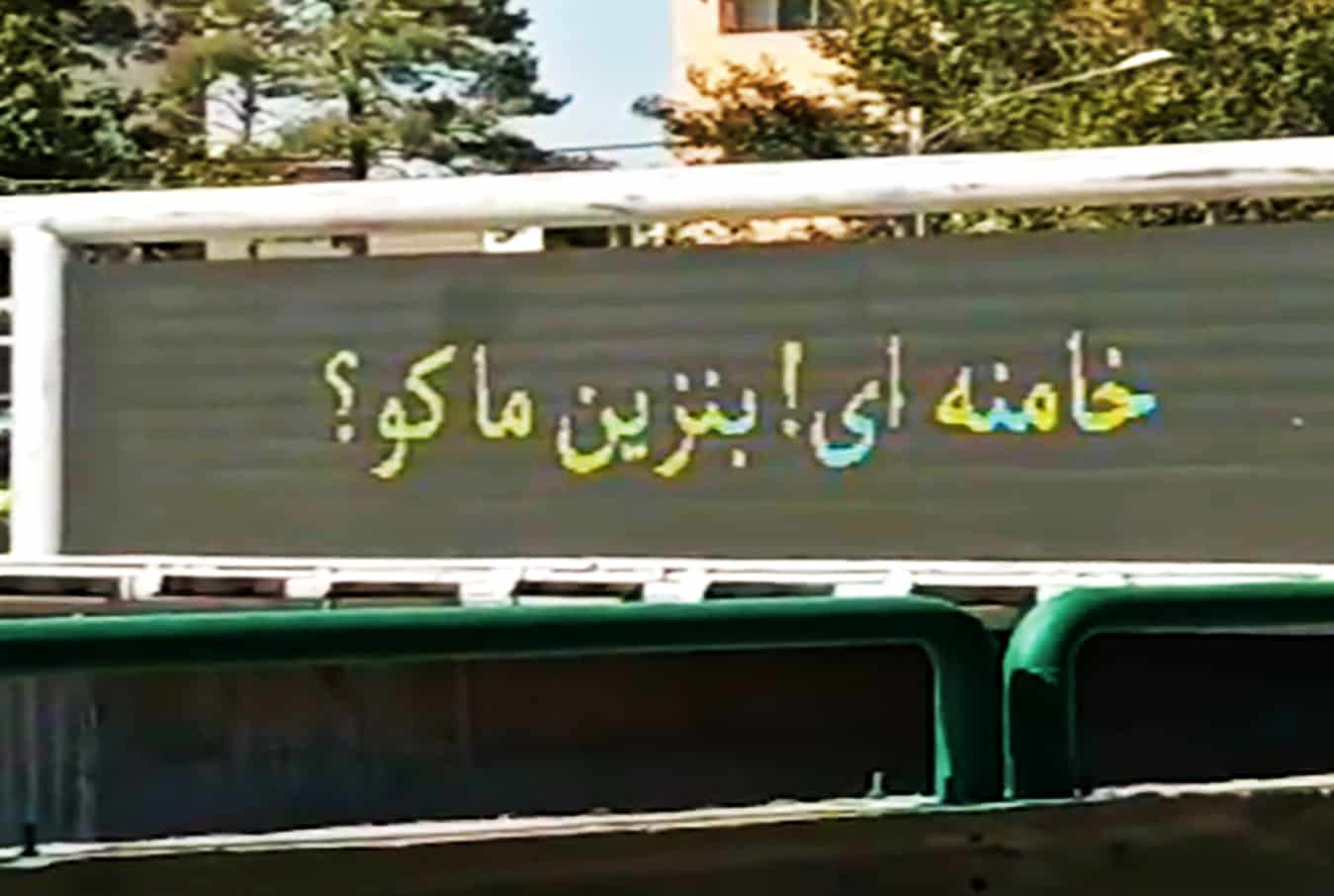
4.3KCyber EventsIranian Gas Stations Crippled After Suffering Cyberattack
Soon after the cyberattack, videos and posts started surfacing on social media displaying messages that read: “Khamenei! Where is our gas?” Another...
-
 4.2KCyber Attack
4.2KCyber AttackResearchers Uncover ‘Pink’ Botnet Malware That Infected Over 1.6 Million Devices
Cybersecurity researchers disclosed details of what they say is the “largest botnet” observed in the wild in the last six years, infecting...
-

 3.0KNews
3.0KNewsHacker steals govt database with info of entire Argentine population
Reportedly, the database also contains personal information of Argentinian President Alberto Fernández, football superstars Sergio Aguero and Lionel Messi. After the infamous...
-
 1.2KData Security
1.2KData SecurityCloud security is an ongoing struggle to keep sensitive data safe. Is it getting any easier?
The latest cloud security breaches show that we have miles to go as we keep fighting to keep our sensitive data safe. ...
-
 1.5KData Security
1.5KData SecurityWinRAR vulnerability allowed attackers to remotely hijack systems
The vulnerability in WinRAR trialware could be abused by a remote attacker for executing arbitrary code on any system thus, getting an...
-

 2.9KData Security
2.9KData SecuritySolarWinds hackers, Nobelium, hit cloud providers and resellers
So far, Microsoft has informed 140 companies about the new attack campaign being carried out by Nobelium 14 of which were compromised...
-
 993Cyber Attack
993Cyber AttackHackers Exploited Popular BillQuick Billing Software to Deploy Ransomware
Cybersecurity researchers on Friday disclosed a now-patched critical vulnerability in multiple versions of a time and billing system called BillQuick that’s being...
-

 4.8KCyber Crime
4.8KCyber CrimeHow using the purple team approach helps in addressing cybercrime
Automated purple teaming is one of the best ways to address cybercrime as it does not only test for the deficiencies in...
-

 4.1KCyber Crime
4.1KCyber CrimeREvil ransomware gang goes dark after its Tor sites are hacked
In July 2021 the REvil ransomware group vanished due to mounting US pressure after the Kaseya attack. However, the group was back...
-

 2.6KMalware
2.6KMalwareA New Variant of FlawedGrace Spreading Through Mass Email Campaigns
Cybersecurity researchers on Tuesday took the wraps off a mass volume email attack staged by a prolific cybercriminal gang affecting a wide...
-

 4.2KSurveillance
4.2KSurveillanceWhat is a data breach & how to prevent one?
What is a data breach? A data breach is a security lapse where a non-authorized person can assess sensitive information without authorization....
-
 4.6KNews
4.6KNewsiPhone 13 Pro, Windows, Chrome, Linux and others pwned at Tianfu Cup
Tianfu Cup is the Chinese version of the Pwn2own in which hackers from Kunlun Lab managed to secure first place by hacking...
-

 696Malware
696MalwareOver 30 Countries Pledge to Fight Ransomware Attacks in US-led Global Meeting
Representatives from the U.S., the European Union, and 30 other countries pledged to mitigate the risk of ransomware and harden the financial...
-
 5.0KData Security
5.0KData SecurityIran-linked hackers hit Israeli, US and EU defense tech firm
Microsoft has warned that hackers linked to Iran are mainly targeting Office 365 clients in defense technology firms. Researchers at Microsoft Threat...
-
 4.0KData Security
4.0KData SecurityBest performing cybersecurity companies and their recent developments
Cybersecurity companies are the backbone to fight cybercrime – Let’s dig deeper into which cybersecurity company is doing what and how. Cybersecurity...






