All posts tagged "malware"
-

 168Geek
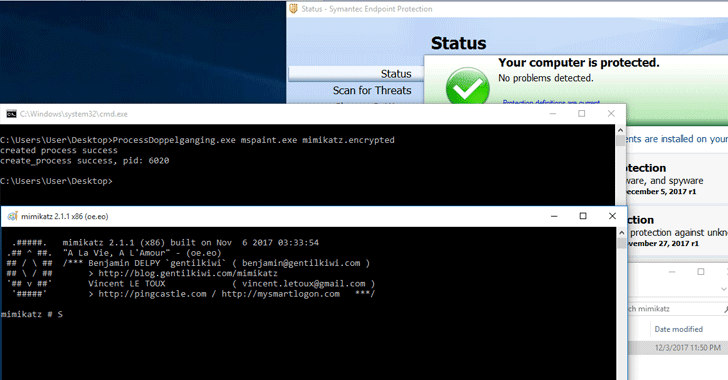
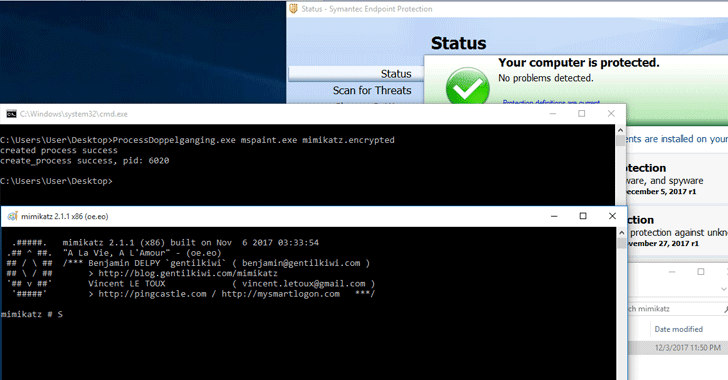
168GeekProcess Doppelgänging attack affects all Windows version & evades AV products
Researchers at endpoint security firm enSilo have identified a new attack that affects all Windows versions and allows attackers to use Microsoft Windows features...
-
 178Malware
178MalwareNew Malware Evasion Technique Works On All Windows Versions
A team of security researchers has discovered a new malware evasion technique that could help malware authors defeat most of the modern...
-

 369Cyber Crime
369Cyber CrimeAuthorities dismantle Andromeda Botnet that infected millions of devices
In an international cyber operation, the law enforcement authorities have dismantled a massive botnet called Andromeda (also known as Wauchos and Gamarue) associated with...
-

 296Cyber Crime
296Cyber CrimeMalware display fake BSOD to sell phony Windows anti-virus for $25
Microsoft has a never-ending malware problem, in fact, millions of Windows devices worldwide have been plagued with some sort of malicious software. Recently,...
-

 348Hacked
348HackedWorld’s Biggest Botnet “Necurs” Sends 12.5 Million Scarab Ransomware Emails
If you keep a close eye on the cybersecurity world, you must be knowing about Necurs botnet, which is one of the...
-
 378Data Security
378Data SecurityMS Office’ Default Function Can Be Used to Create Self-Replicating Malware
Italian security researcher Lino Antonio Buono discovered a security flaw that affects almost all versions of Microsoft office. As per the findings...
-

 157Malware
157MalwaremacOS Malware Notorious for Its Data Stealing Capabilities Is Back
Mac malware, Proton, is spreading through a legitimate security company. Security researchers spotted criminals using search poisoning to get more targets and...
-

 282Reverse Engineering
282Reverse EngineeringPortEx – Java library to analyse Portable Executable files with a special focus on malware analysis and PE malformation robustness
PortEx is a Java library for static malware analysis of Portable Executable files. Its focus is on PE malformation robustness, and anomaly...
-

 312News
312NewsSacramento Regional Transit System in California Held for $7,000 Ransom
On Saturday night an unknown hacker targeted the Sacramento Regional Transit System (RT or SacRT) in California and hacked into its website...
-

 303Malware
303MalwareEMOTET Malware Hijacking the Windows API & Evade the Sandbox Analysis
A wide Spread EMOTET malware emerging again with new stealthy capabilities to hijack the Windows API and evade the sandbox detection which also gives...
-

 355Data Security
355Data SecurityMcAfee’s ClickProtect Apparently Infected Devices with Banking Malware
According to a French researcher, the renowned antivirus vendor McAfee sent s file loaded with Emotet banking malware to customers using its...
-
 241Vulnerability Analysis
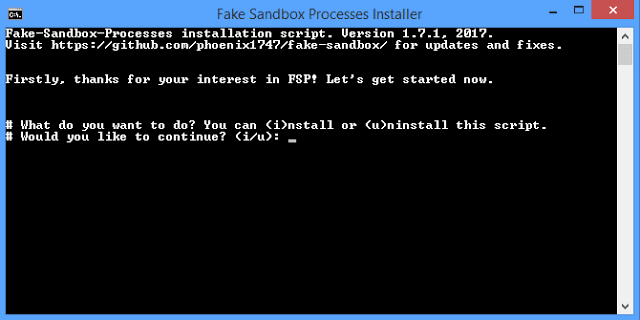
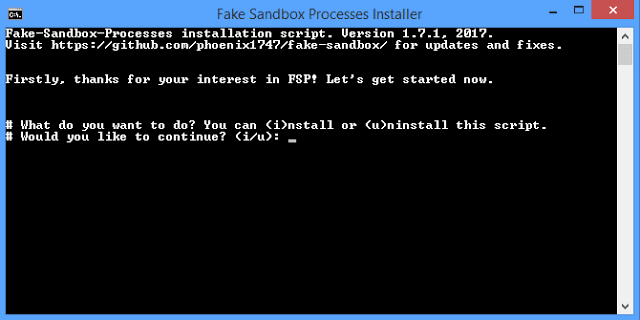
241Vulnerability AnalysisFake Sandbox Processes (FSP) – Tool to simulate fake processes of analysis sandbox/VM software
This small script will simulate fake processes of analysis, sandbox and/or VM software that some malware will try to avoid. You can...
-

 225Malware
225MalwareNew Android Trojan “Android/Trojan.AsiaHitGroup” Discovered in Google Play Store
Nowadays Trojanized Android apps evolving rapidly in play store and continuously targetting innocent users who all are unaware of the malicious application...
-
 327Vulnerabilities
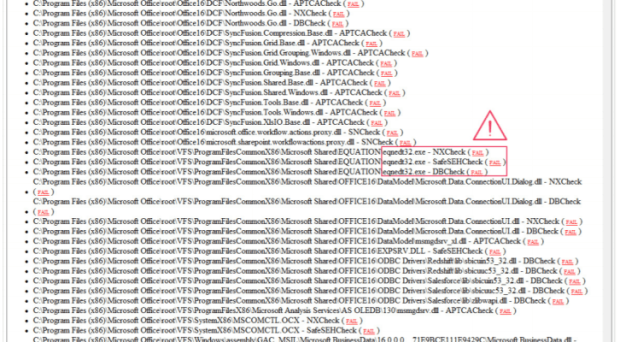
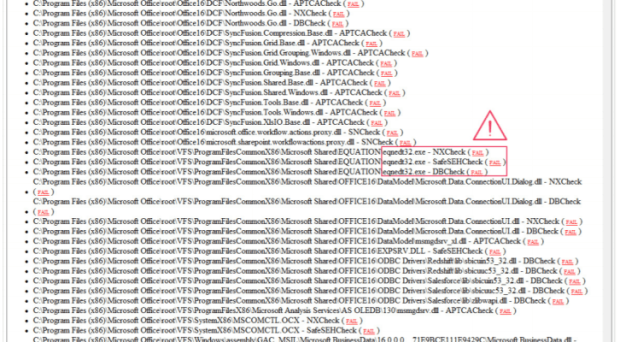
327Vulnerabilities17-Year-Old MS Office flaw CVE-2017-11882 could be exploited to remotely install malware without victim interaction
Ops, a 17-Year-Old flaw in MS Office, tracked as CVE-2017-11882, could be exploited by remote attackers to install a malware without user...
-

 127Malware
127MalwareMulti-stage malware sneaks into Google Play
Another set of malicious apps has made it into the official Android app store. Detected by ESET security systems as Android/TrojanDropper.Agent.BKY, these...
-

 295Geek
295GeekThere is a Pre-Installed Backdoor in OnePlus 5, 3 and 3T Devices
If you are using OnePlus 5, 3 or its 3T model, an IT security researcher Elliot Alderson (whose real name is Robert Baptiste) has bad...
-
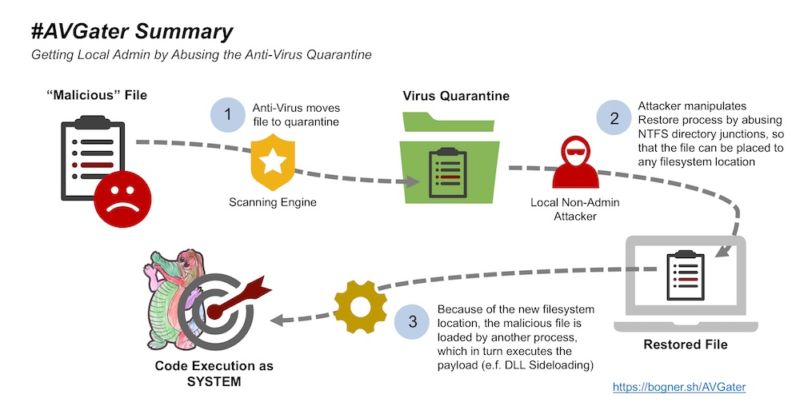
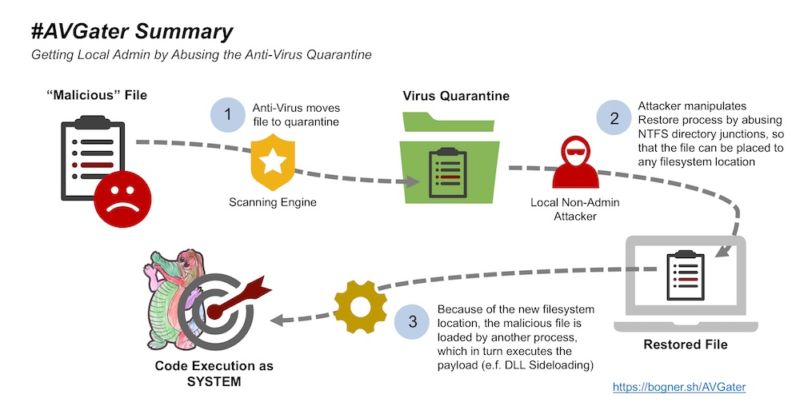 140Vulnerabilities
140VulnerabilitiesHow AV can open you to attacks that otherwise wouldn’t be possible
New AVGater flaw provided key ingredient for hacker to hijack computer. Antivirus programs, in many cases, make us safer on the Internet....
-

 76Malware
76MalwareA c espionage group has been using a new strain of malware dubbed Reaver
Experts at Palo Alto Networks have discovered a new malware family named Reaver with ties to hackers who use the SunOrcal malware....
-
 452Data Security
452Data SecurityNew Vulnerability Exploits Antivirus Programs to Install Malware
It is common notion that antivirus software keeps our computers safe from all types of bugs and malware. However, it seems that...
-
 159Malware
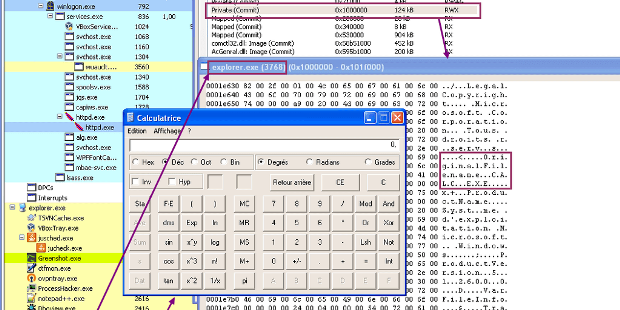
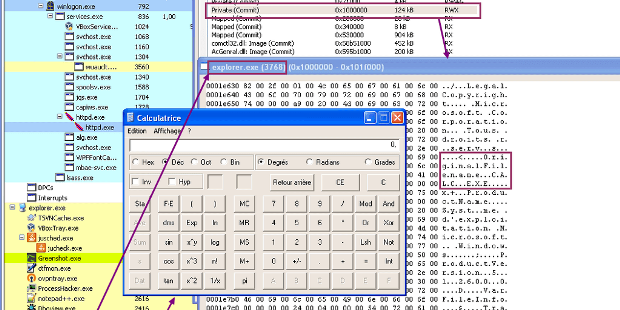
159MalwareRunPE: How to hide code behind a legit process
Hiding a process has always being challenging for malware writers, and they found many ways to do so. The tip I’ll talk about...
-
 265Malware
265MalwareAll Android Version Except 8.0/Oreo are Vulnerable to Toast Overlay Malware Attack
A First Android malware called TOASTAMIGO has been discovered that capable of installing other malware into infected devices using Toast Overlay attack. Overlay...






