All posts tagged "malware"
-

 282Geek
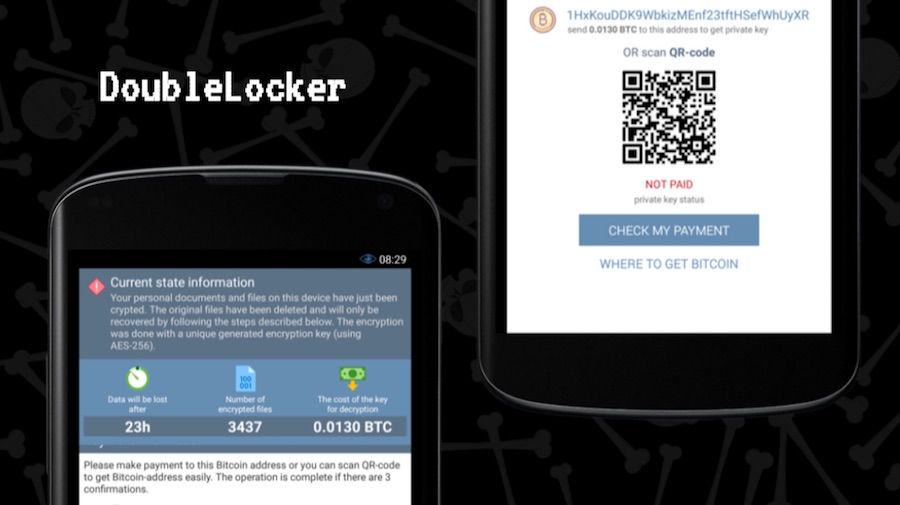
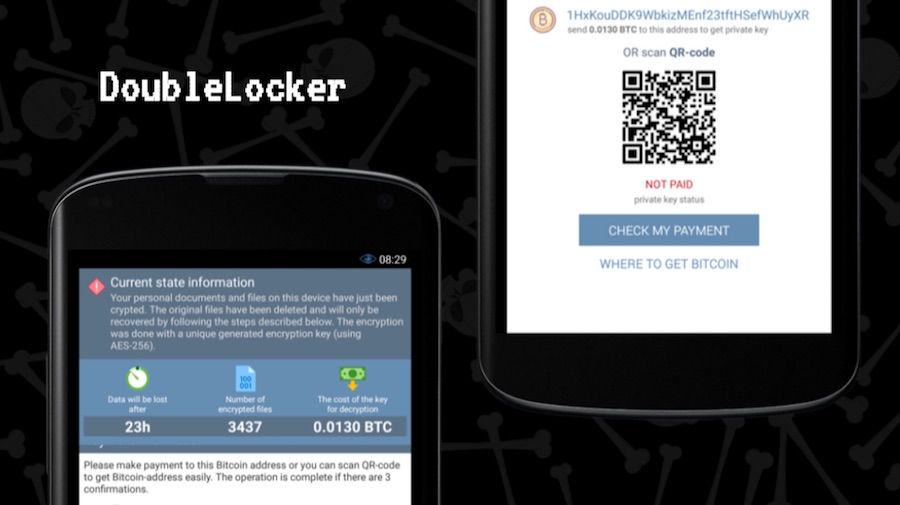
282GeekNew Android Ransomware Permanently Changes PIN, Demands Ransom
DoubleLocker Android Ransomware Encrypts Data and Changes PIN to Permanently Lock Your Phone. ESET’s security researchers have identified a new kind of...
-
 261Hacked
261HackedDoubleLocker: This Android Ransomware Activates Every Time You Press Home Button
Android’s accessibility services are features that help the users to take advantage of an alternative navigation method on behalf of apps installed on...
-

 159Articles
159ArticlesMicrosoft Office feature enables a malware to execute without Macros enabled
What if I told you that there is a method will let you execute commands on Microsoft Word without any Macros, or...
-

 221Malware
221MalwareATM Malware Called “ATMii” allows Hackers to Dispense all the Cash from the ATM
ATM Malware Called “ATMii” could allow Cyber Criminals to Hack and Dispense the Cash from ATM by Infecting the ATM Machine which...
-
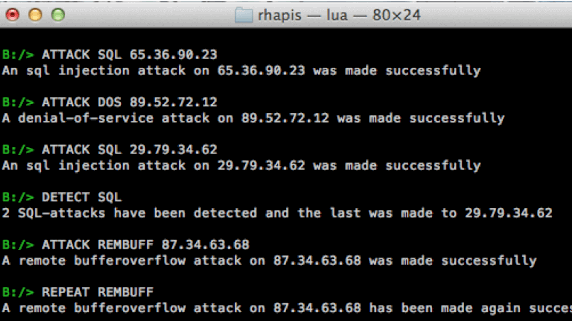
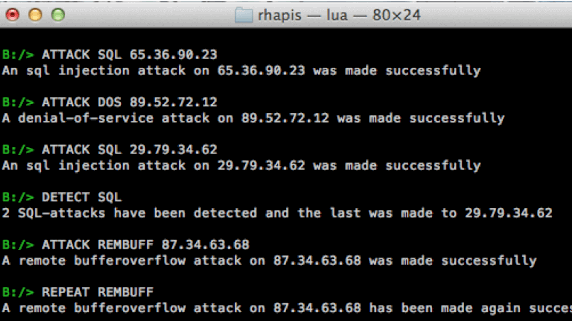 228Network Tools
228Network ToolsRHAPIS – Network Intrusion Detection Systems Simulator
Network intrusion detection systems simulator. RHAPIS provides a simulation environment through which user is able to execute any IDS operation. Basic Usage...
-

 132Malware
132MalwareRansomware is now big business on the dark web and malware developers are cashing in
Appeal of ransomware sees sales rise from $250,000 in 2016 to over $6m in 2017 – and some ransomware sellers are now...
-
 342Vulnerabilities
342VulnerabilitiesMicrosoft addresses CVE-2017-11826 Office Zero-Day used to deliver malware
Microsoft October Patch Tuesday addresses the CVE-2017-11826 Office Zero-Day vulnerability that has been exploited in the wild in targeted attacks. Yesterday we...
-
 295Vulnerabilities
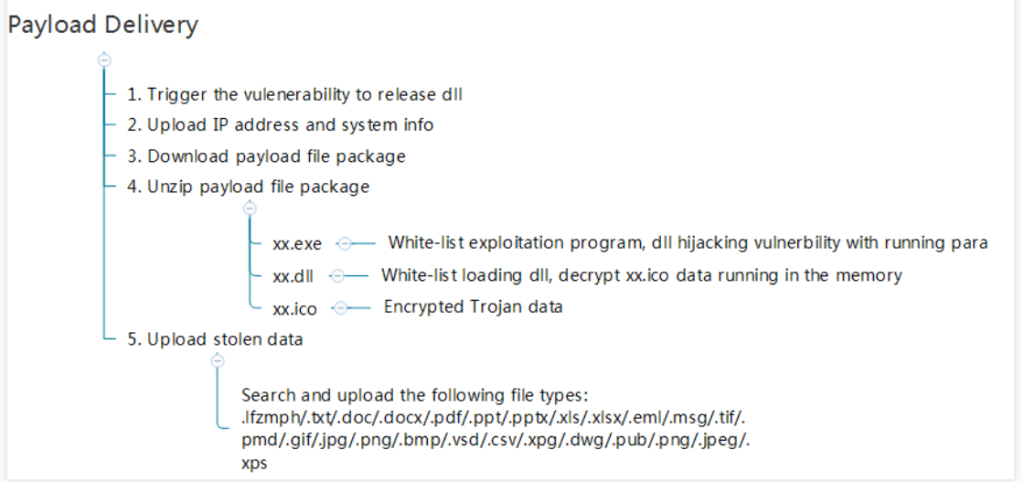
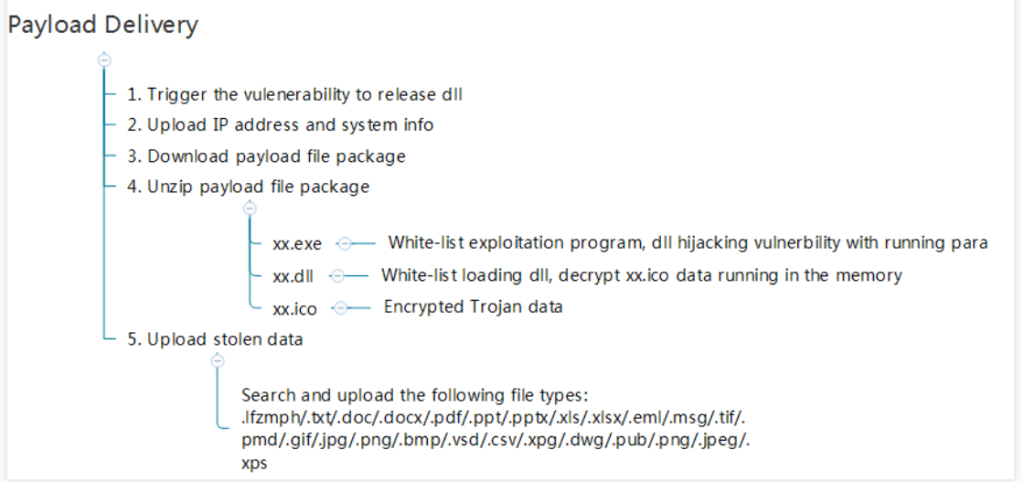
295VulnerabilitiesKovter Group malvertising campaign exposes millions to potential ad fraud malware infections
This attack chain exposed millions of potential victims in the US, Canada, the UK, and Australia, leveraging slight variations on a fake...
-
 183Cyber Crime
183Cyber CrimeFreeMilk Phishing Scam Hijacks Active Email Conversations to Deploy Malware
The IT security researchers at Palo Alto Networks Unit 42 have come to know about a new, targeted spear-phishing scheme, which is...
-
 247Malware
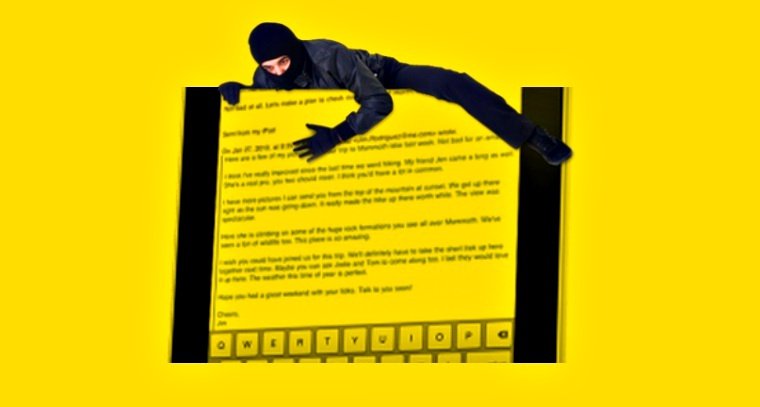
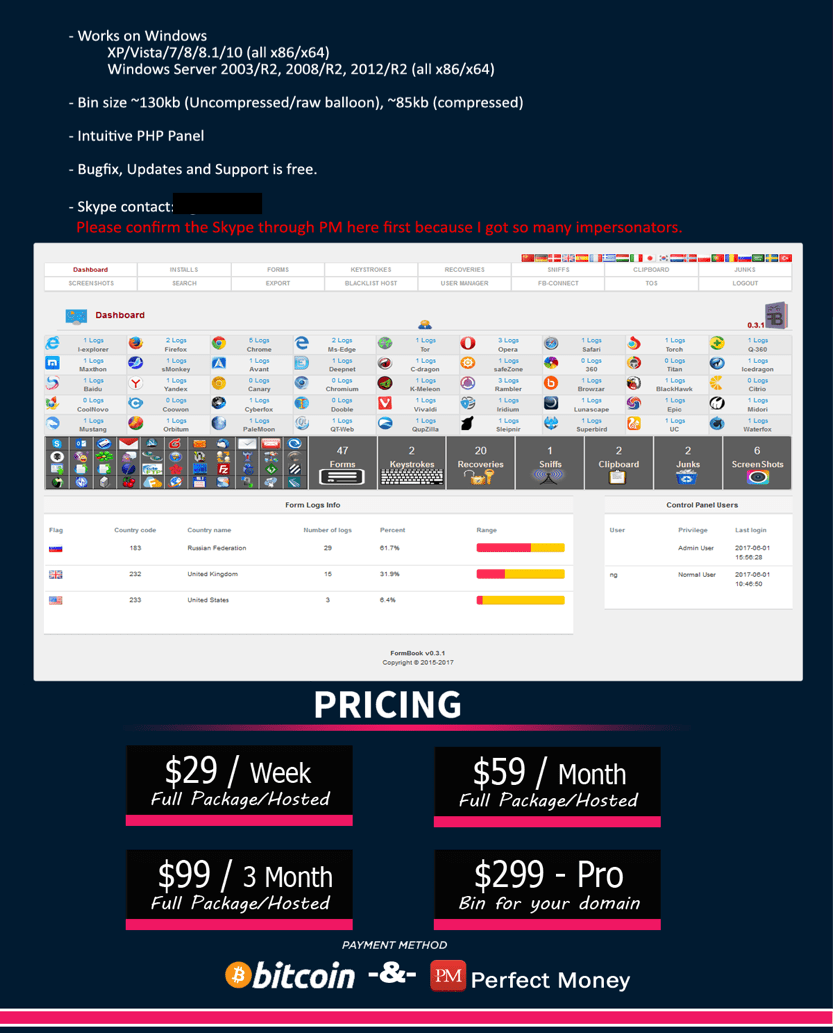
247MalwareTargetted Malware Campaigns to Steal Cookies and Passwords – FormBook
Security researchers from Arbornetworks and FireEye identified a Sophisticated Malware(FormBook malware) campaigns targetting Aerospace, Defense Contractor, and Manufacturing sectors around U.S. and...
-
Articles
FormBook – Cheap Password Stealing Malware Used In Targeted Attacks
It seems sophisticated hackers have changed the way they conduct targeted cyber operations—instead of investing in zero-days and developing their malware; some...
-

 357Data Security
357Data SecurityCloudFlare Boots Off Torrent Site For Using Cryptocurrency Miner
CloudFlare says sites running mining code without notifying users are considered to be malware. In the last couple of weeks, researchers discovered an increasing...
-

 124Malware
124MalwareThis cheap and nasty malware wants to steal your data
FormBook malware advertises an ‘extensive and powerful internet monitoring experience’ for a relatively low-cost – allowing even low level attackers to distribute...
-

 265News
265NewsSmartphones of NATO Soldiers Compromised By Russian Hackers
North Atlantic Treaty Organization, which is universally famous as NATO, has been targeted by none other but the country that is a...
-

 275Malware
275MalwareNew Trending Method of Network Based ATM Malware Attacks
Nowadays ATM Based Cyber Attacks are Evolving with Much More Advance methods and Functions via Sophisticated Malware especially through Network Based ATM...
-

 337Malware
337MalwareMoney-making machine: Monero-mining malware
While the world is holding its breath, wondering where notorious cybercriminal groups like Lazarus or Telebots will strike next with another destructive...
-
 130Cyber Crime
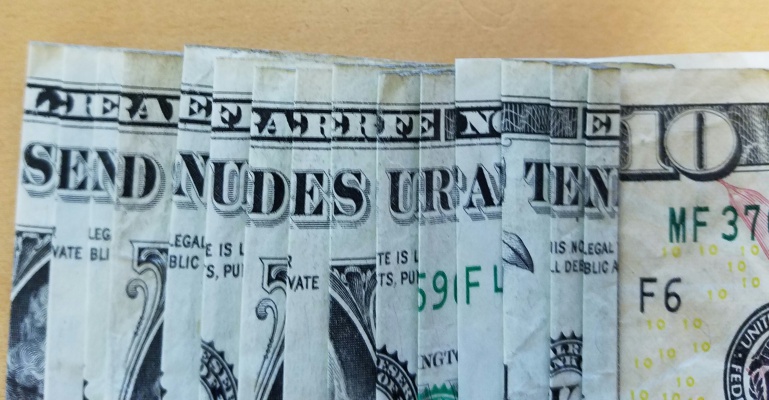
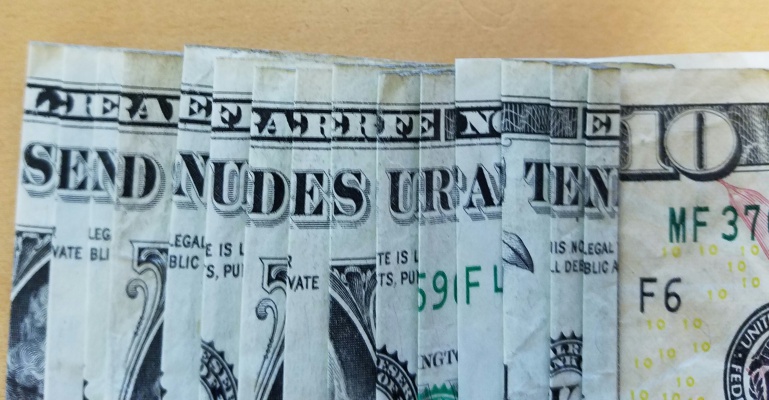
130Cyber CrimeNew ransomware scam asks for nude pics to unlock files
A few months ago, two ransomware scams made news for asking users to play video games in order to get their files...
-
 250Malware
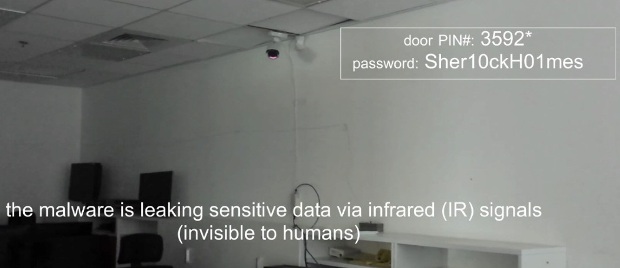
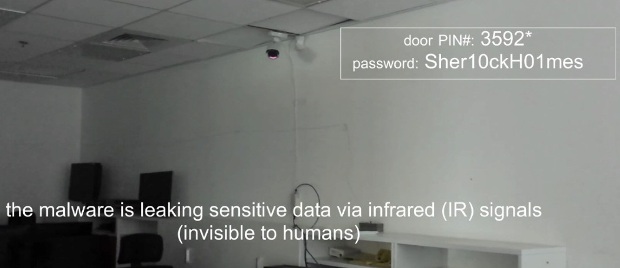
250MalwareMalware Uses Security Cameras With Infrared Capabilities to Steal Data
Proof-of-concept malware created by a team of Israeli researchers uses the infrared capabilities of modern security cameras as a channel for data...
-

 392Data Breach
392Data BreachCCleaner Got Hacked & Used For Distributing Malware that Infected 2 Million Users
A Most Famous Sofware CCleaner Hacked and Distributing Floxif Malware from Download server of Leading Anti-Virus Vendor AVAST and more than 2 million...
-

 174Hacked
174HackedCCleaner Hacked To Spread Malware To 2.27 Million Users — Here’s What To Do
In a blog post published on Monday, Piriform’s VP of Products Paul Yung revealed that the company spotted a security breach in CCleaner 5.33.6162 and...
-

 246Incidents
246IncidentsCCleaner Compromised to Distribute Malware for Almost a Month
Version 5.33 of the CCleaner app offered for download between August 15 and September 12 was modified to include the Floxif malware,...






