All posts tagged "malware"
-

 344Geek
344GeekGhostCtrl Android Malware Records Audio, Video and Spies on Users
Perhaps it is not so surprising to see powerful malware now being created to target Android devices. Researchers at Trend Micro recently...
-
 272Cyber Crime
272Cyber CrimeYou can buy password stealing malware ‘Ovidiy Stealer’ for $7
Researchers at Proofpoint recently discovered a mass-marketed malware called Ovidiy stealer whose main purpose is to steal passwords from victims. It is...
-
 188News
188NewsGandi hosting’ logins breached; 751 domains diverted to malware site
Gandi SAS, a French web hosting company has announced that it suffered a security breach after hackers got hold of the valid login details...
-

 317Geek
317GeekOSX/Dok malware hits Macs; bypasses Apple’ Gatekeeper
IT security researchers at Checkpoint recently discovered that a new malware has started to rise and is targeting Mac devices. The malware...
-

 163Hacked
163HackedHighrise: How This CIA Malware Spies And Steals User Data Using SMS
Short Bytes: The latest WikiLeaks Vault 7 leak deals with an Android malware that doesn’t need the internet to talk to the CIA...
-
 158Malware
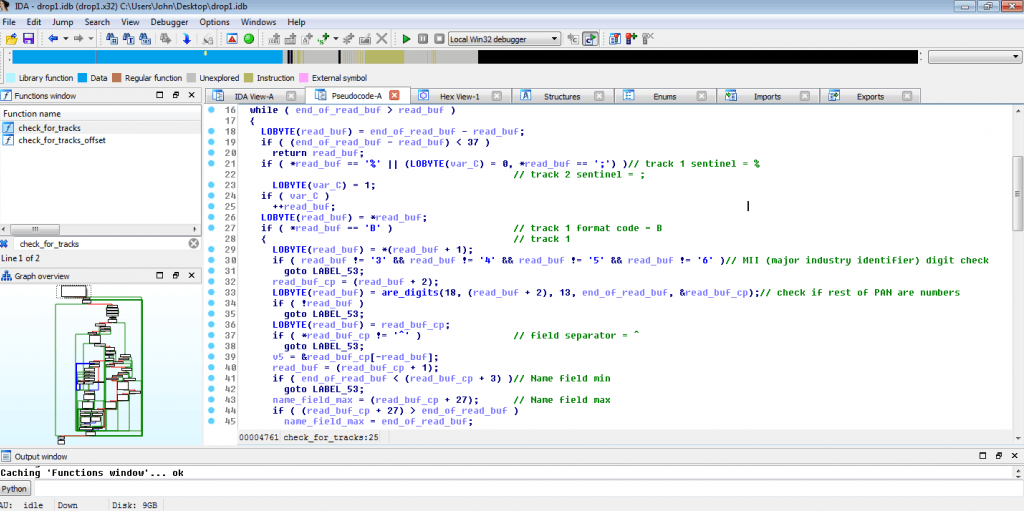
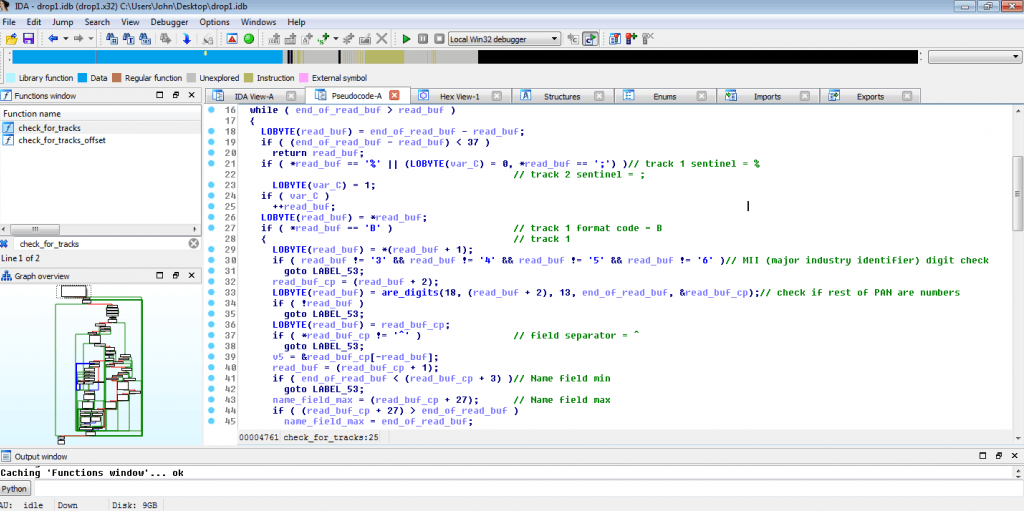
158MalwareNew PoS Malware LockPoS emerges in the threat landscape
A newly discovered Point of Sale (PoS) malware dubbed LockPoS appeared in the wild and it is being delivered through the Flokibot botnet....
-

 350News
350NewsCIA Highrise Android Malware Spies On SMS Messages: WikiLeaks
WikiLeaks is back with yet another batch of Vault 7 related documents detailing the CIA’s (Central Intelligence Agency) hacking tools and programs targeting...
-

 340Trojan / Worms
340Trojan / WormsCross-platform Remote Access Trojan “Adwind” Steal Credentials, Record and Harvest keystrokes the Aerospace Industries Data
Remote Access Trojan(RAT) Called “Adwind”(Adwind/jRAT) Targeting Aerospace Industries to steal credentials, record and harvest keystrokes, take pictures or screenshots, film and retrieve...
-

 190News
190NewsAvanti Markets’ kiosks hacked; credit card, biometric data stolen
The self-service kiosks of Avanti Markets were recently hacked with criminals stealing customer information which included credit card numbers, the first and...
-

 296Hacked
296HackedHow SpyDealer Malware Hacks Your Facebook, WhatsApp, Web Browser, And Other Android Apps
Short Bytes: The security researchers have identified a malware named SpyDealer, which affects Android smartphones running Android versions between 4.4 KitKat and 2.2...
-
 261Phishing
261PhishingBrilliant Phishing Attack Targeting Critical Infrastructure and Manufacturing Industries
Nowadays attackers targeting users more innovatively through Emails and many other ways. This malware attack particularly targeting power sectors including Nuclear power...
-
 156Malware
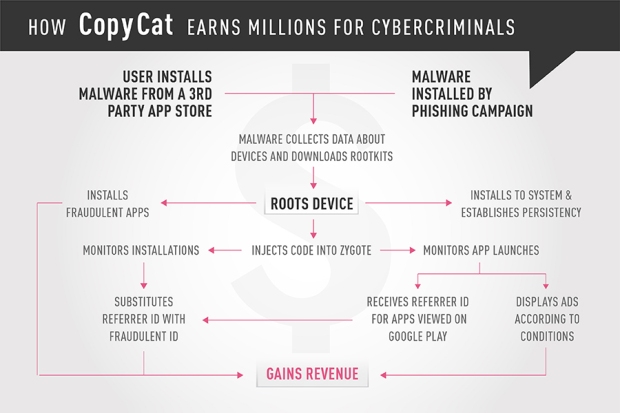
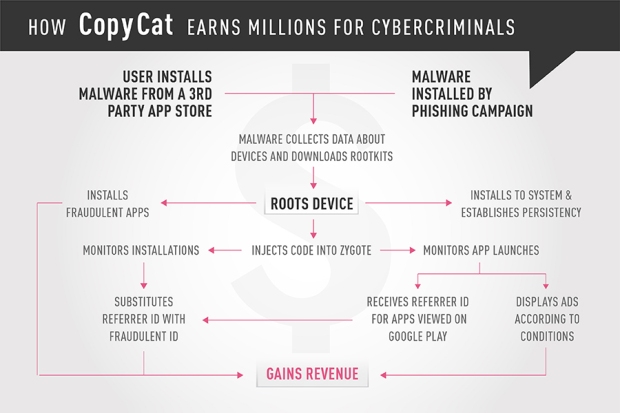
156MalwareHow the CopyCat malware infected Android devices around the world
Check Point researchers identified a mobile malware that infected 14 million Android devices, rooting approximately 8 million of them, and earning the...
-

 120Incidents
120IncidentsCIA Malware Can Steal SSH Credentials, Session Traffic
WikiLeaks dumped today the documentation of two CIA hacking tools codenamed BothanSpy and Gyrfalcon, both designed to steal SSH credentials from Windows...
-

 209Cyber Crime
209Cyber CrimeTwo hackers arrested after a decade of selling malware
Ruslan Bondars and Jurijs Martisevs were identified as the main culprits behind a crime in which they were selling malware over the...
-

 218Hacked
218HackedComputer Servers Of Software Firm Linked To Petya Malware Attack Seized By The Police
Short Bytes: In the wake of recent Petya/NotPetya attack, to prevent the further cyber attacks, Ukraine’s Cyber Police has seized the servers of...
-
 315News
315NewsServers associated with NotPetya attack seized by Ukrainian Police
Last week the computer systems of several companies in Europe were infected with NotPetya malware. At first, the researcher thought it’s just...
-
 287Hacked
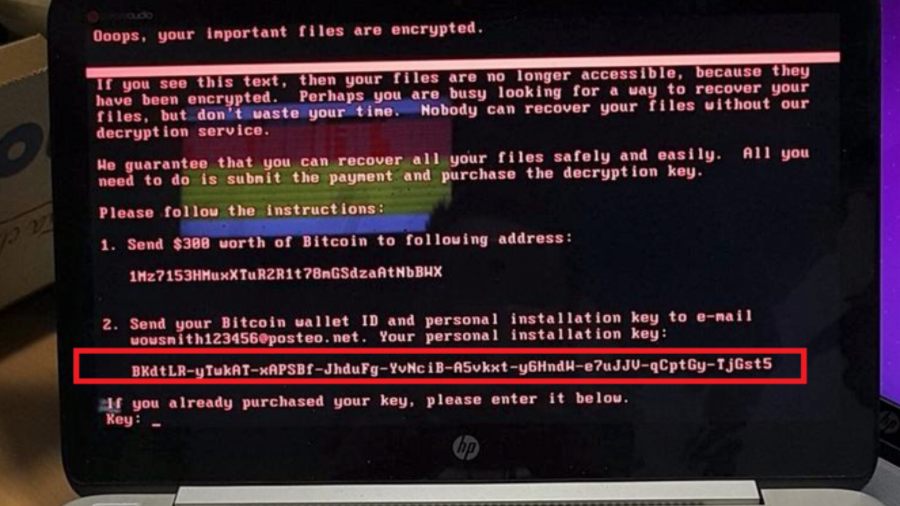
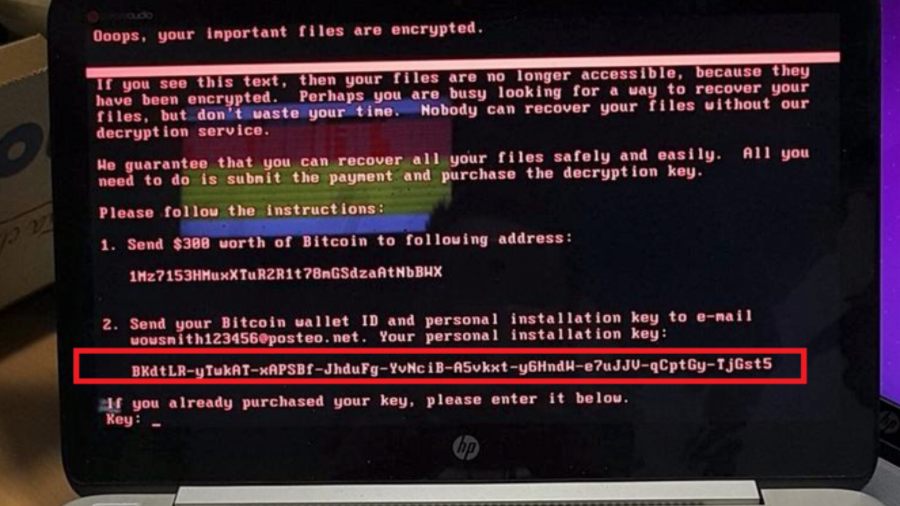
287HackedWhat Happens When Your PC Is Hit With Petya/NotPetya? — Watch Here
Short Bytes: Petya wiper is a dangerous malware that has disguised itself as a ransomware to get the attention of media. After...
-
 333News
333NewsWikileaks Exposes CIA’ Linux Hacking, Geolocation Tracker Malware
As you may know, WikiLeakes has been releasing sensitive documentation associated with CIA’s hacking tools as part of its Vault 7 series....
-
 189Geek
189GeekMicrosoft to use AI in Windows 10 to counter malware attacks
Microsoft’s Windows operating system seems to have been having a really bad year given the major cyber attacks taking place including the...
-
 329Hacked
329HackedPetya Is Not A Ransomware, It’s A “Wiper” — It’s Out To Destroy Your Data Forever
Short Bytes: Petya malware, which is being seen as WannaCry’s obvious successor, isn’t a ransomware. It actually disguises itself as one to...
-

 359Data Security
359Data SecurityPetya not a ransomware but much worse
The breakout of the Petya malware two days ago has caused mayhem once again. It has been the second major global cyber...






