All posts tagged "malware"
-

 327Data Security
327Data SecurityMalware that infects users without needing to click anything
We have all heard or seen malware that is embedded within malicious links. Usually, the user is prompted to click the link...
-
 175Hacked
175HackedSambaCry: This Linux Malware Is Turning Machines Into CryptoCurrency Miners
Short Bytes: A few weeks ago, we got to know about a vulnerability that dealt with all versions of Samba. While a patch...
-

 285Malware
285MalwareDvmap – First Ever Android Rooting Malware with Code Injection Capabilities
Trojan Dvmap distributed through the Google Play Store, uses various exceptionally dangerous methods, including patching system libraries. It installs malicious modules with...
-
 426Cyber Events
426Cyber EventsWannaCry Copycat ‘WannaLocker’ Ransomware Hits Android Devices
The IT security researchers have discovered a malware in China that has mimicked WannaCry ransomware attack to some extent and has been...
-
 316Geek
316GeekA Malware That can Bypass Windows Firewall Using Intel’s Management Tech
A unique and perhaps a very practical way of injecting malware into an entire network has been discovered in which the hacking...
-

 272Geek
272GeekAndroid Malware with Code Injecting Capability Found on Google Play Store
Google Play Store has been found harboring another malware and this one has the ability to disable the security settings on Android...
-
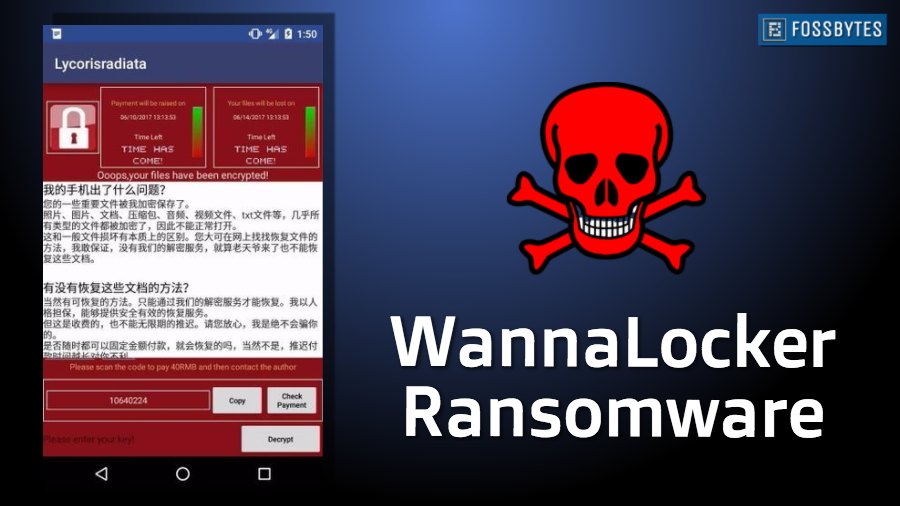
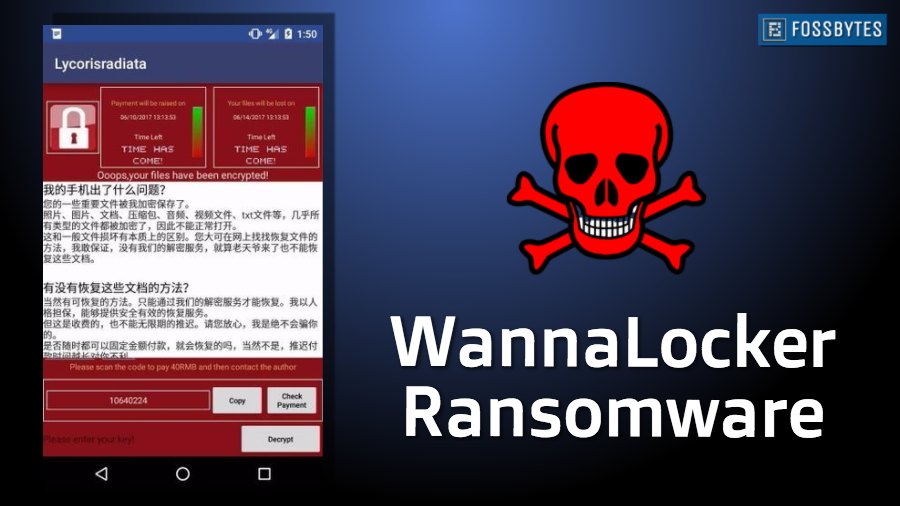 181Hacked
181HackedWannaLocker — A New WannaCry-inspired Ransomware Is Attacking Android Smartphones
Short Bytes: After wrecking havoc on unpatched Windows computers using WannaCry, some new notorious hackers from China are targeting Android smartphones. They’ve...
-

 301Hacked
301Hacked8 Best Anti Ransomware Tools You Must Be Using In 2017
Short Bytes: In the recent past, ransomware has emerged as one of the most challenging cyber security threats. This has demanded the...
-
 111Geek
111GeekHackers are using popular chat apps to control malware operation
Yesterday, a group of IT security researchers had revealed that Russian hackers are controlling malware operation through the official Instagram account of...
-

 211Hacked
211HackedThe Unbelievable Place Where Russian Hackers Hid Their Malware’s Control Center Link
Short Bytes: Researchers have linked a Russian hacker group called Turla to a malicious Firefox extension which contacts its C&C server using the...
-
 356News
356NewsRussian Hackers Control Malware via Britney Spears Instagram Posts
A group of Russian-speaking hackers has been attacking multiple governments for years now. Not only that, but they also experimented with different...
-

 224Hacked
224HackedAfter WannaCry, Fireball Malware Infects 250 Million Computers; India Worst Affected
Short Bytes: Fireball is a new and notorious malware in town which is targeting Windows and macOS devices. Developed by a Chinese...
-

 381How To
381How ToHow to Protect Yourself From Hackers – Useful Tips For Small Business Owners
As a small business owner, you’re bound to take great pride in what you do and use every opportunity you can to...
-

 368Cyber Crime
368Cyber CrimeLeaked NSA Exploit ‘EternalBlue’ Being Used in New Trojan Attacks
A recently leaked NSA exploit that was discovered in the biggest ransomware attack (WannaCry) ever is now powering Trojan malware. The EternalBlue...
-

 280Data Security
280Data SecurityHackers Behind Jaff Ransomware Selling Victims’ Data on Dark Web
The dark web marketplaces and undergrown marketplaces are full of vendors selling databases, weapons, illegal drugs and malicious software. Now security researchers have...
-

 293Geek
293Geek‘Fireball’ Malware Infected 250 Million Mac and Windows Devices
Since the spread of WannaCry ransomware attack the cyber security community is doing whatever it takes to identify new threats against unsuspecting users....
-
 182Malware
182MalwareBeware: Chinese Malware Fireball Infects More than 250 Million Computers around the Globe
Chinese threat operation which has infected more than 250 million PCs around the world. The advanced malware, Fireball, takes control target browsers...
-

 301News
301NewsWikileaks reveals pandemic malware for Windows developed by the CIA
In its latest release as part of the Vault 7 series, WikiLeaks has apparently leaked a document which consists information regarding a...
-
 336Malware
336MalwareNew CIA Cyberweapon Malware “Pandemic” installed in Victims Machine and Replaced Target files where remote users use SMB to Download
One of the CIA Cyberweapon Called “Pandemic” Document Leaked by Vault 7 Projects of WikiLeaks.This Malware tool Specifically interact and run as...
-
 199Malware
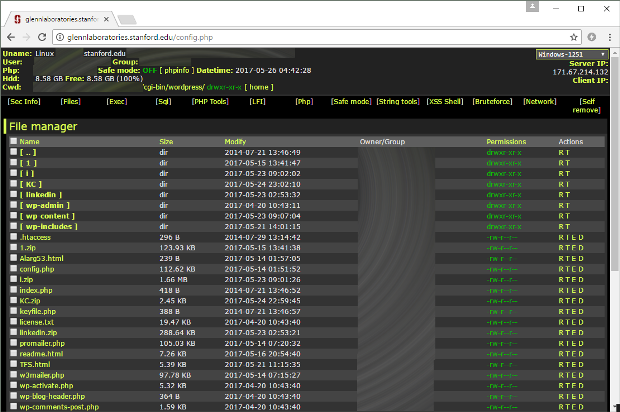
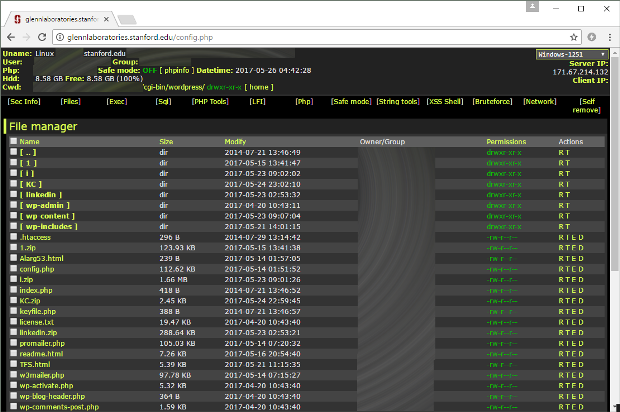
199MalwareStanford University Site Hosted Malware for Months
For almost four months, script kiddies ran amok in one of Stanford’s subdomains, installing web shells, mailers, and other types of web...
-
 233Infosec
233InfosecGoogle using machine learning to block 99.9% of Malware and Phishing Mails
Google published a blog post introducing machine learning to detect phishing Emails, click-time warnings for malicious links, and unintended external reply warnings....






