All posts tagged "malware"
-

 253Geek
253GeekWebroot Antivirus Marked Facebook as Phishing Site and Windows as Malware
You may remember Google’s Safe Browsing Site Status mistakenly marking Google.com as a potentially dangerous domain to visit or the Google Maps mistakenly labeling...
-
 181Malware
181MalwareWebroot antivirus mistakenly flags Windows as malware
Windows’ system files were flagged as malicious, and Facebook was marked as a phishing site. A malware signature update issued by the...
-
 158Malware
158MalwarePoint-of-Sale Malware Steals Driver’s License Information
Malware specialized in infecting Point of Sale (PoS) software has gained the ability to search and steal driver’s license information, according to...
-

 260Geek
260GeekMalicious software bought by a London Police Officer can remotely hack users
One of the officers of UK’s Metropolitan Police Service was caught in possession of a malicious software used for infecting computers and...
-

 153Malware
153MalwareInterpol Identifies 8,800 C&C Servers Used for Malware, Ransomware, Others
Interpol investigators announced today they’d identified over 8,800 servers hosted across eight countries in Southeast Asia used for various cybercrime operations. According...
-
 166Vulnerabilities
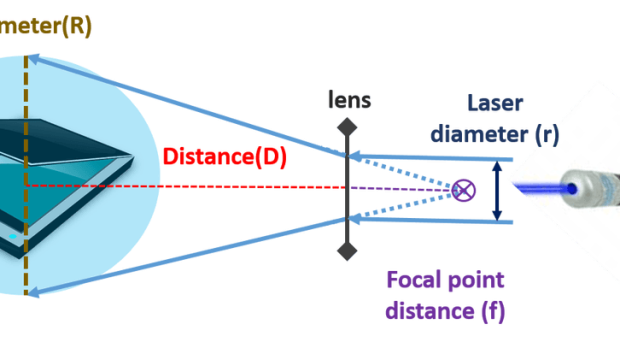
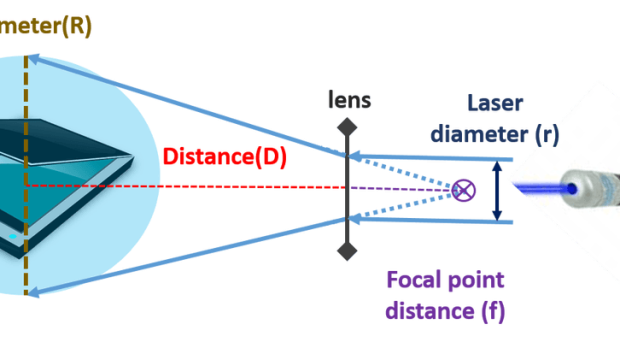
166VulnerabilitiesOps, hackers can exfiltrate data from air-gapped networks through a malware controlled via a scanner
A group of Israeli researchers has devised a new technique to exfiltrate data from a PC in an air-gapped network through malware controlled via scanners....
-

 171Hacked
171HackedIT Engineer Hacked His Own Wall Street Company And Stole Source Code, Arrested By FBI
Short Bytes: FBI has arrested a DevOps Engineer Zhengquan Zhang for stealing proprietary source code and accessing employee accounts at KCG Holdings...
-
 271Hacked
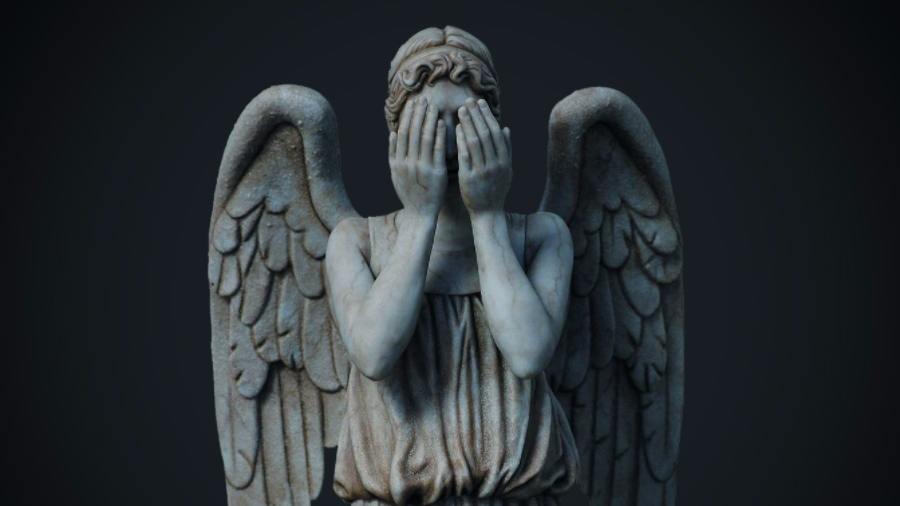
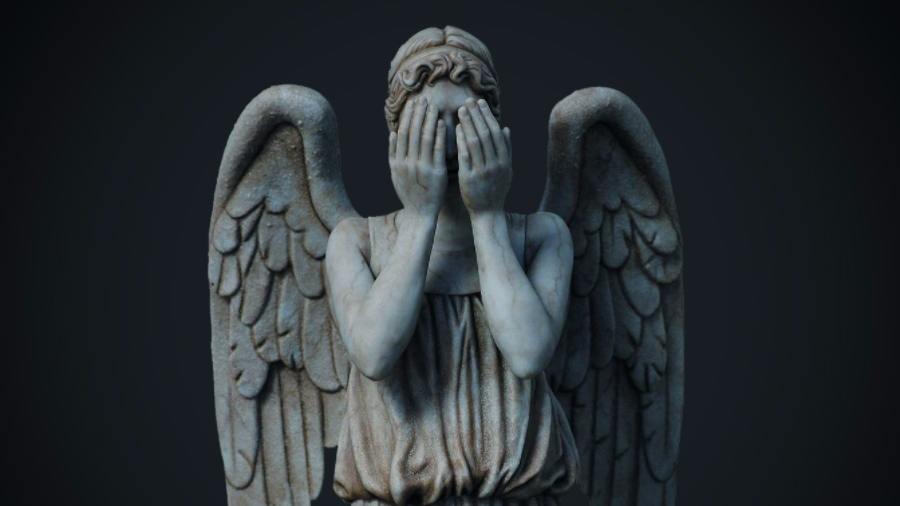
271HackedWikileaks Friday: “Weeping Angel” By CIA, A Hacking Tool For Your Television
Short Bytes: In their latest revelation, Wikileaks has released a user guide describing the working of the Weeping Angel tool designed by...
-
 179Hacked
179HackedGoogle Just Deleted “System Update” Malware Living On Play Store For 3 Years
Short Bytes: A security firm called Zscalar spotted a malicious app living on the Play Store with a false moniker System Update....
-

 227News
227NewsCredit card stealing malware: 1200 InterContinental hotels breached
A few months earlier, it was reported that a number of InterContinental hotels have been targeted by a credit card stealing malware...
-
 107Malware
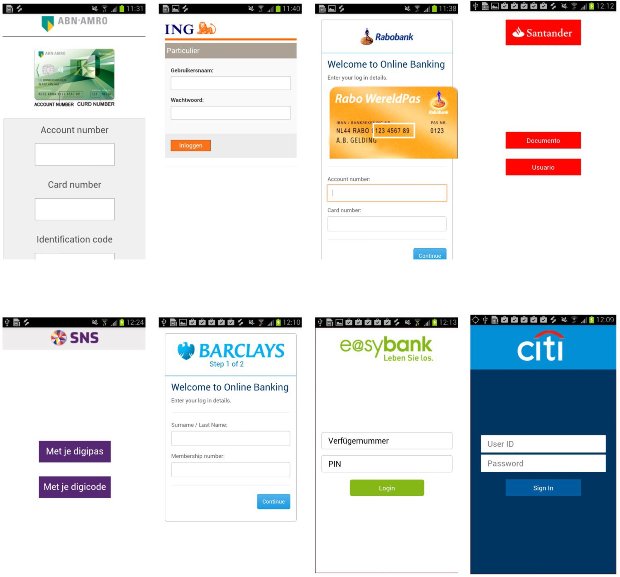
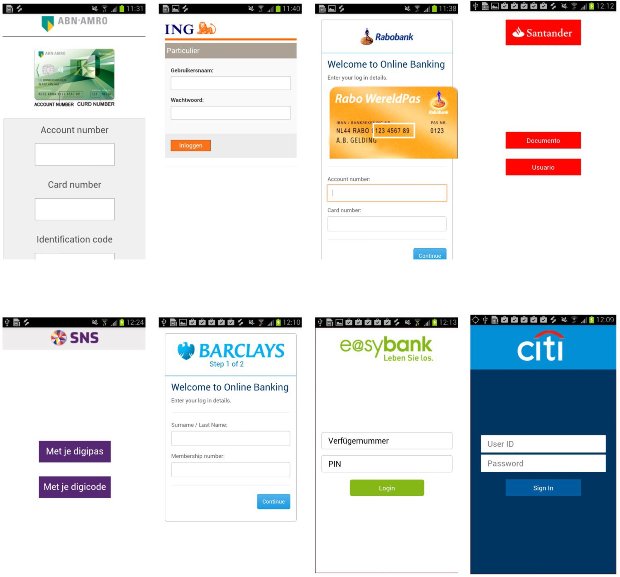
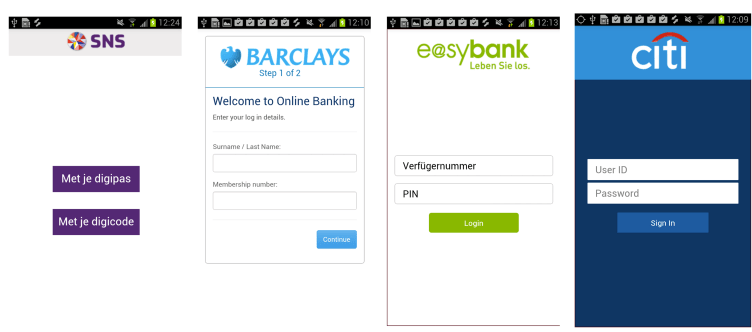
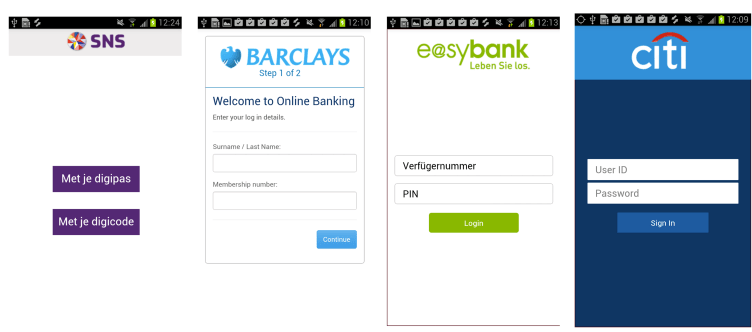
107MalwareMalware Reaches Play Store as Google Wages War Against BankBot Trojan
The BankBot Android banking trojan is giving Google engineers headaches, as this particular piece of malware has a knack for avoiding Google’s...
-

 276Ransomware
276RansomwareGoogle strengthen it’s defence against Ransomware to Attack Android
[jpshare]Ransomware for Android, or any mobile platform, have been generally uncommon.The risk has fundamentally been kept to Windows desktops, where it’s flourished...
-

 312News
312NewsHackers using leaked hacking tools to target Governments
Thanks to ex-NSA spy, Edward Snowden, we all know that Governments use several hacking tools and malware to spy on public and...
-
 305Malware
305MalwareMany New Apps Injected with Banking Malware found in Google Play Store
[jpshare]Security researcher Niels Croese found much new banking malware on Google Play, which has numerous new banking application focuses in its configurations. Taking a look...
-

 334Cyber Crime
334Cyber CrimeFBI Kills Kelihos Botnet after Russian Hacker Arrested in Spain
Earlier this week, Spanish authorities arrested a Russian hacker and “one of the world’s most notorious criminal spammers,” Peter Yuryevich Levashov (Severa)...
-

 217Hacked
217Hacked40 Cyber Attacks Now Link To CIA Hacking Tools Uncovered By Wikileaks
Short Bytes: A team of Symantec researchers has been able to link around 40 cyber attacks, conducted by Longhorn group, to the...
-
 259Data Security
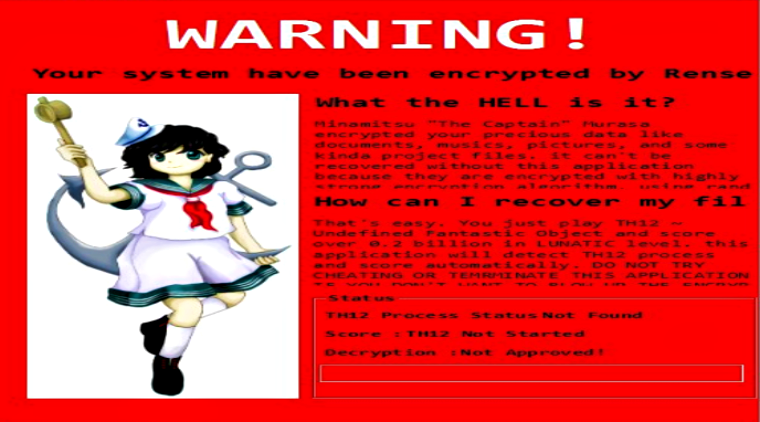
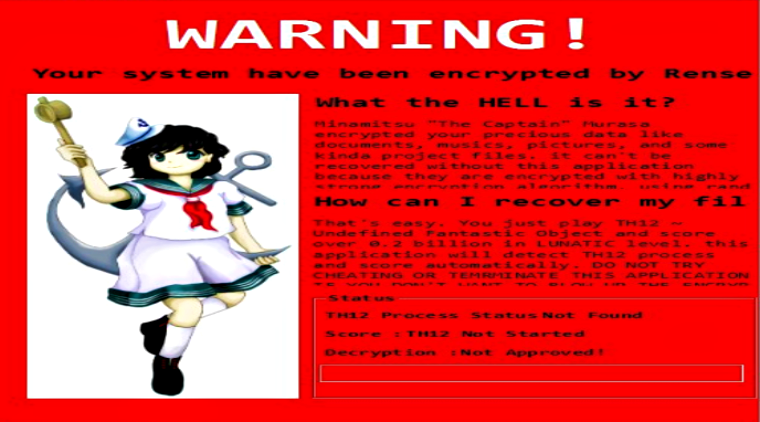
259Data SecurityThis Ransomware tells users to play a popular Japanese game – That’s all
You might have heard countless tales of hackers using malicious ransomware forcing users to pay huge amounts of money but not today....
-

 293Geek
293GeekHackers are Exploiting New Microsoft Office Vulnerability to Drop Malware
Researchers have detected a new zero-day bug which uses a previously unknown flaw in Microsoft Word. The bug allows attackers to send malicious document...
-

 181Hacked
181HackedWikileaks Releases “How To Hack Windows” Secret Guide By CIA
Short Bytes: The latest addition to the Vault 7 leak by CIA is the set of 27 documents of the Grasshopper framework....
-

 322Mobile Security
322Mobile SecurityMobile spyware that steal Twitter credentials uses sandbox to Evade antivirus detections
[jpshare]Security Experts from Avast came through a Malware that uses a sandbox(DroidPlugin) to dynamically load and run an app, without actually installing...
-

 239News
239NewsHackers Leak Passwords to NSA’s “Top Secret Arsenal” against Trump’s Policies
You may remember Shadow Brokers hacking group for selling a trove of hacking tools and exploits stolen from the NSA’s Equation Group...






