All posts tagged "malware"
-

 403Geek
403Geek5 Proven Cyber Security Certifications That Will Skyrocket Your Salary
With rising salaries and a massive global demand for qualified professionals, cybersecurity is an incredibly attractive industry to work in. There are...
-

 309News
309NewsRussian Postal Service Hit by WannaCry Ransomware Attack
WannaCry ransomware attack has left a devastating trail on half of the world and this also includes the Russia’s postal service which was...
-

 248Malware
248MalwareAndroid Users Tricked Into Installing Malware Via “App-For-Money” Scheme
An eight-month-long investigation by Roman Unuchek, a security researcher at Kaspersky Lab, has uncovered one of the most complex malware distribution...
-

 163Data Security
163Data SecurityHackers have found a way to hijack your system through subtitles
Check Point Software Technologies Ltd has revealed that its researchers have found a major attacking method in which hackers use vulnerabilities in...
-

 390Cyber Crime
390Cyber Crime386 WannaCry Ransomware and 26 EternalRocks Samples Discovered
Have you heard the expression “it ain’t over till it’s over”? Well, it matches with the ongoing situation of WannaCry ransomware attacks...
-
 196Hacked
196Hacked386 WannaCry Ransomware Samples Discovered
Short Bytes: According to the latest update, Trustlook has found 386 WannaCry ransomware samples in the wild. The hashes for files have...
-

 108Hacked
108HackedWannabe Russian Bank Malware Attacked Millions Of Android Devices, Stole People’s Money
Short Bytes: A malware named Cron was deployed by a 16-membered hacker group in Russia which infected more than a million Android...
-
 268Hacked
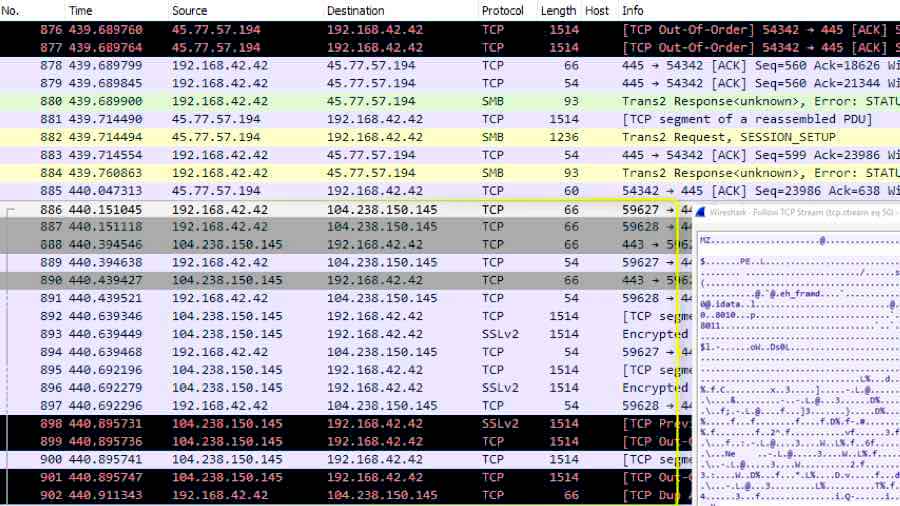
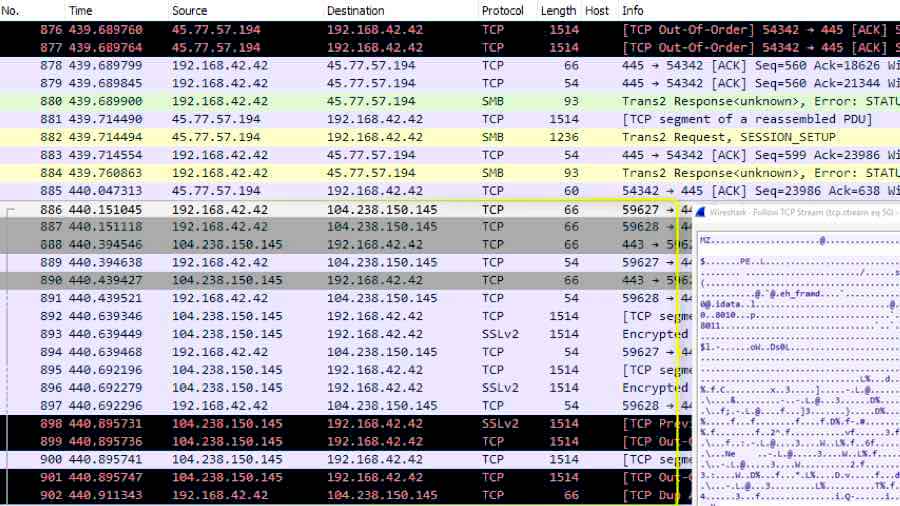
268HackedEternalRocks: New Malware Uses 7 NSA Hacking Tools, WannaCry Used Just 2
Short Bytes: A security researcher’s honeypot has caught a new malware that uses 7 NSA hacking tools to perform the attack. Named...
-

 111News
111NewsHackers trying to bring back WannaCry attacks by DDoSing its KillSwitch
It was over a week ago when the nasty WannaCry ransomware attack started infecting critical cyber infrastructure in more than 150 countries....
-

 368Data Security
368Data SecurityEternalRocks Worm Uses Same SMB Flaw in Windows like WannaCry
The WannaCry incident was just a beginning as now a new and more evolved malware lurks out there in the wild. No, it’s not...
-

 239Hacked
239HackedVault 7: Wikileaks Exposes CIA’s Athena Malware, Hijacks Every Windows Version
On Friday, Wikileaks published a CIA malware project known as Athena. According to the leaked documents, the Athena malware is capable of hijacking all...
-
 511News
511NewsHow To Prevent Growing Issue of Encryption Based Malware (Ransomware)
The threat of ransomware attack is growing and here is how to protect yourself from encryption based malware known as ransomware. The...
-

 334News
334NewsWannaCry responsible for infecting medical devices
It is not surprising to know that Internet-connected Medical devices are vulnerable to cyber attacks. There have been several cases in the...
-
 167Hacked
167HackedAdylkuzz Attack Is Earning More Money Than WannaCry And Making Your PCs Slow
Short Bytes: Proofpoint has uncovered a malware attack that uses the same EternalBlue and DoublePulsar exploits, which were used to spread WannaCry. Called Adylkuzz,...
-
 115Vulnerabilities
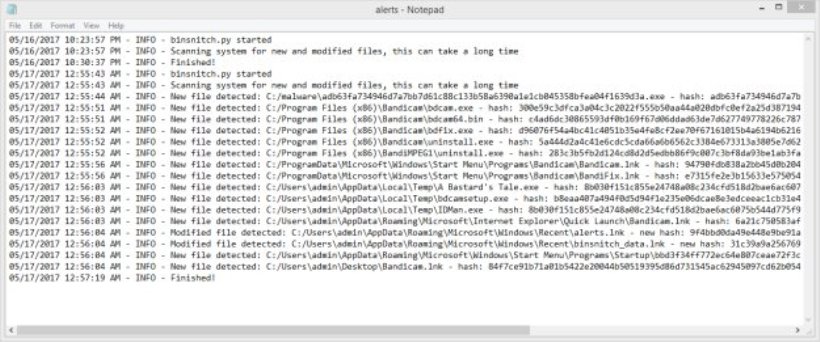
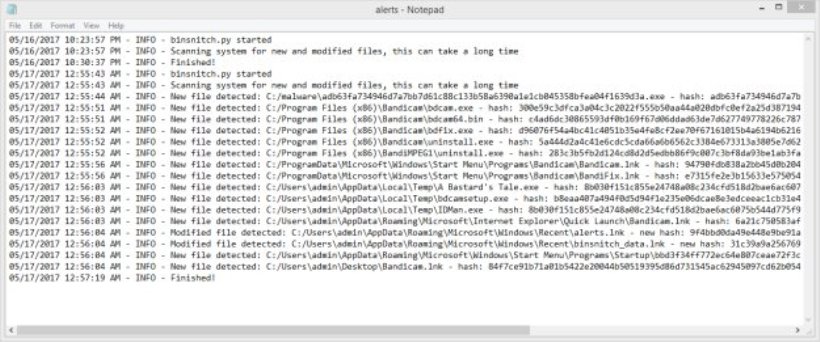
115VulnerabilitiesUsing binsnitch.py to detect files touched by malware
Yesterday, we released binsnitch.py – a tool you can use to detect unwanted changes to the file sytem. The tool and documentation is available...
-

 334Cyber Crime
334Cyber CrimeWannaCry Ransomware Attackers are sending new message to victims
The WannaCry ransomware attack is still infecting unsuspecting users, hospitals, and businesses around the world. While some users on Twitter are claiming...
-
 306Data Security
306Data SecurityCryptoMining malware Adylkuzz using the same vulnerability as WannaCry
It seems that WannaCry had a predecessor that apparently carried out attacks which involved mining the cryptocurrency Monero using the same vulnerability...
-

 195Vulnerabilities
195VulnerabilitiesMalware Uses Fake WordPress API Domain to Steal Sensitive Cookies
Security researchers from Sucuri have found hacked WordPress sites that were altered to secretly siphon off cookies for user and admin accounts...
-
 311News
311NewsWikiLeaks Posts User Manuals for CIA Malware AfterMidnight and Assassin
WikiLeaks recently leaked some files as part of its Vault 7 series, that contained user manuals for two malware called, Assassin and...
-
 401Geek
401GeekMicrosoft Slams NSA over WannaCry Ransomware Attack
Earlier today, Microsoft’s President and Chief Legal Officer, Brad Smith stated that part of the responsibility of the recent WannaCry ransomware attack...
-

 310Cyber Crime
310Cyber CrimeUiwix, yet another ransomware like WannaCry – only more dangerous
In the last few days, the internet has been caught off guard with numerous updates being posted regarding the sprawling effects of...






