All posts tagged "malware"
-

 192Hacked
192HackedShieldFS Stops Ransomware Attacks With 97% Success And Recovers Your Lost Files
Short Bytes: A team of Italian security researchers has created a Windows filesystem add-on named ShieldFS to fight the ransomware attacks. By...
-
 368Malware
368MalwareMachine learning system to create invisible malwares – gym-malware
In the recent DEF CON Meet, technical director of security shop Endgame Hyrum Anderson disclosed a research paper on adapting API frameworks...
-
 345News
345NewsPre-installed Trojan in Cheap Android Devices Steal Data, Intercept Chats
Android devices are one of the most vulnerable mobile OS (operating systems) due to its open source nature. But what would a...
-
 372News
372NewsHealthcare Clinic Suffers Ransomware Attack; 300K Patients Impacted
This without a doubt is the second largest health data breach caused by a ransomware attack. An Oaks, Philadelphia based women’s healthcare...
-

 422News
422NewsHow A Coffee Machine Infected Factory Computers with Ransomware
It’s no surprise that the Internet of Things (IoT) devices are highly vulnerable to cyber attacks but who would know a time...
-
 235Vulnerabilities
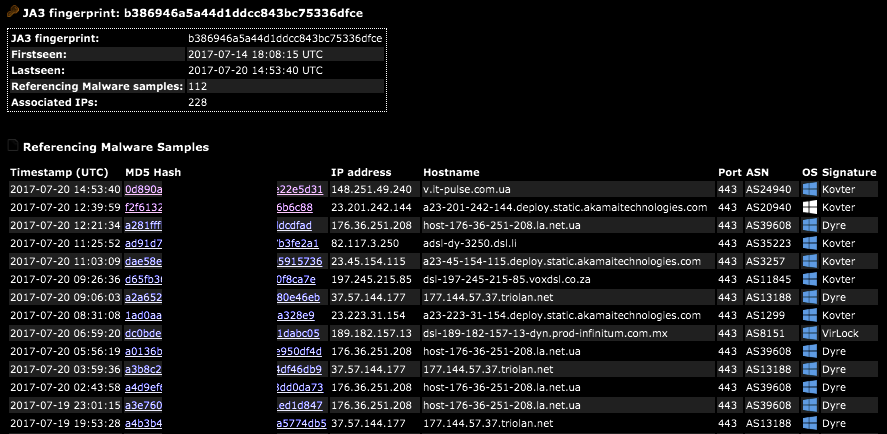
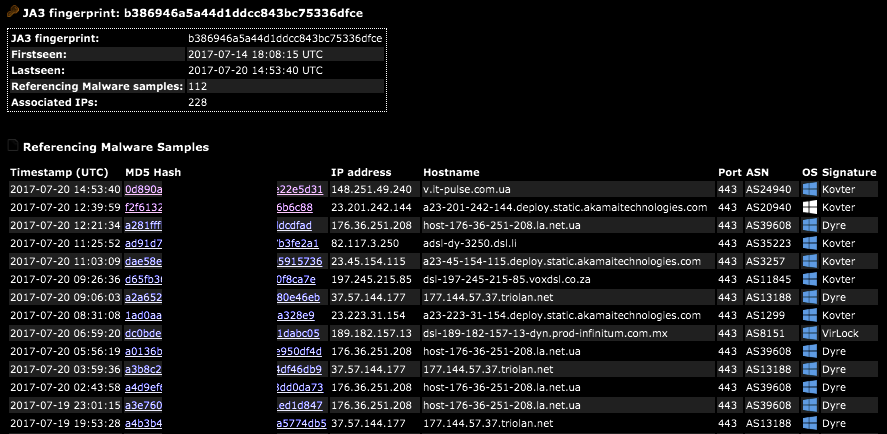
235VulnerabilitiesSSL/TLS Client Fingerprinting for Malware Detection
A JA3 hash represents the fingerprint of an SSL/TLS client application as detected via a network sensor or device, such as Bro...
-

 217Cyber Crime
217Cyber CrimeChina arrests 11 hackers for infecting 250M devices with Fireball malware
Law enforcement authorities in China have arrested eleven hackers suspected of developing Fireball malware which infected 250 million computers worldwide. Among the...
-

 335News
335News6 billion records hacked in 2017 so far; ransomware victims paid $25 million
With every passing day, hackers and cyber criminals are becoming more sophisticated in their attacks. Resultantly, they are getting their hands on...
-

 295Data Security
295Data SecurityCowerSnail Backdoor Targeting Windows Devices
Kaspersky Lab has identified the presence of a backdoor designed primarily for attacking Windows systems. When the backdoor successfully infects the system...
-

 162News
162NewsWatch Security Researcher As She Hacks ATM by Drilling a Hole
ATMs (automated teller machines) have remained a preferred target of hackers around the world. Last year, ATMs in over a dozen locations...
-

 270Hacked
270HackedMystery “FruitFly” Malware Infected Macs For Years, No One Noticed It Until 2017
Short Bytes: Two malware which go by the name FruitFly and FruitFly 2 have been discovered over the course of the last...
-
 73Malware
73Malware“Perverse” malware infecting hundreds of Macs remained undetected for years
Surveillance malware dubbed Firefly was easy to spot but flew under the radar anyway. A mysterious piece of malware that gives attackers...
-

 257Data Security
257Data SecurityVariant of Surveillance Malware Fruitfly Targeting Mac Users
In January this year, a dangerous surveillance malware was found targeting Mac and Linux devices – The malware was discovered by Thomas...
-

 310Geek
310GeekGoogle’ ‘Play Protect’ Ensures Maximum Security For Android Devices
Android is among the widely used mobile operating systems around the world. Understandably it is the top priority for Google to keep...
-
 180Hacked
180Hacked500,000 Windows Users Infected By 15-Year-Old Stantinko Malware
Short Bytes: The security researchers have found a malware that uses stealthy techniques to perform monetization by injecting ads. Called Stantinko, this malware...
-
 259News
259NewsWikiLeaks Release Documents on How CIA Uses 5 Different Malware
WikiLeaks has released a trove of data belong to the American intelligence agency CIA (Central Intelligence Agency) – The latest batch shows...
-

 254Hacked
254HackedPlay Protect: Google’s Android Malware Killing Machine Is Out Now
Google is rolling out their automatic app scanning service called Google Play Protect. What it basically does is it runs in the background...
-
 312News
312NewsRansomware attack on KQED TV, Radio Station wiped out pre-recorded segments
Internet connected devices are the current rage among businesses and corporations alike. However, the various, far-reaching drawbacks associated with connecting every system...
-

 118Hacked
118HackedGhostCtrl Android Malware Steals Your Private Data And Records Audio, Video
Short Bytes: The researchers at the Trend Micro security firm have uncovered a new Android malware that exists in three different versions. Called...
-

 342News
342NewsFedEx: It is still suffering the aftermath of Petya attack
FedEx, a US based globally operating delivery firm, states that customers associated with its subsidiary company TNT Express are continually facing issues....
-
 257Cyber Crime
257Cyber CrimeFake WhatsApp Subscription Email Stealing Banking Data
It is not uncommon for scammers to send phishing emails that trick the users into downloading a malicious link or simply open...






