All posts tagged "cyber security news"
-
 300Malware
300MalwareHackers Distribute Malware Disguised as Pirated Online Textbooks & Essays
Cybercriminals distribute malware disguised as textbooks and essays that downloaded from pirated websites. The costs of materials posted by the university are...
-

 440Malware
440MalwareNew Malware Attack Targeting 60 Million WordPress Websites to add Backdoor & Exploit Plugins Vulnerability
Researchers discovered an ongoing malvertising campaign targeting millions of WordPress websites to infect with backdoor and exploiting the various WordPress plugins vulnerabilities....
-

 431Malware
431MalwareLYCEUM APT Hackers Attack Critical Infrastructures Over a Year using Several Hacking Tools
A new threat group dubbed LYCEUM spotted attacking critical infrastructure organizations including oil, gas and possibly telecommunications using several hacking tools. The...
-
 356Data Breach
356Data BreachImperva Hacked – Email addresses, API keys & SSL certificates of WAF Customers Exposed
Imperva, one of the leading cyber-security firm disclosed a data breach that impacts the customers’ data of Cloud Web Application Firewall (WAF)....
-
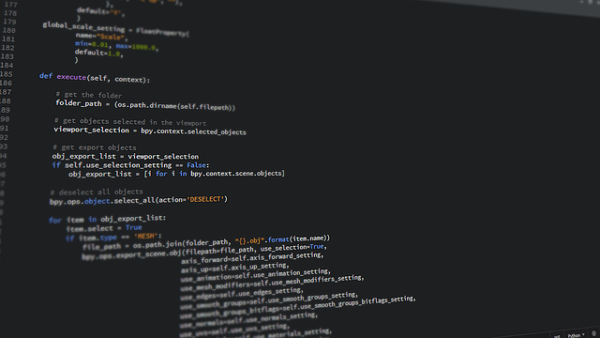
 467Hacking Tools
467Hacking ToolsA Malware Showcase | Understanding Malware With Python
Malware showcase is a Github repository that contains examples of malware usage and behavior, this repo should be used only for educational...
-
 197Malware
197MalwareHackers use Backdoor and Trojan to Attack Financial Departments of Organizations
Hackers use backdoor and remote access trojan that let attackers gain complete remote control over the compromised computer. The campaign particularly targets...
-
 228Malware
228MalwarePaid Insiders Upload a Malware in AT&T Network and Unlocks Over 2 Million AT&T Phones
A recruiter from AT&T charged in a 14-count, U.S to have a paid insiders to planting malware on telecommunications giant AT&T Network...
-

 204Malware
204MalwareHackers use SystemBC Malware to Hide C&C Server Communication by Deploying Proxies on Infected Computer
A new malware dubbed SystemBC delivered by RIG and Fallout exploit kit, sets up a SOCKS5 proxy connection on victims machine to...
-
 400Password
400PasswordCombolists-as-a-Service – Hackers Sell Stolen Passwords on underground Hacking Forums
Threat actors advertising a new Combolists-as-a-Service model to sell credentials on the underground hacking forums that enable account takeovers. Attackers employ several...
-

 287Malware
287MalwareHackers Spreading Android Ransomware via SMS to your Contacts and Encrypt your Device Files
A new family of Android Ransomware dubbed Android/Filecoder.C distributed various online forums and further uses the victim’s contact list to SMS with...
-
 186Data Breach
186Data BreachCapital One Hacked – Over 100 Million Credit Card Application Data Exposed
Capital one hacked, the hack exposed more than 100 million customers data across the US and Canada. The breach was learned by...
-
 522Malware
522MalwareMultistage Attack Delivers BillGates/Setag Backdoor to Turn Elasticsearch Servers into DDoS Botnet
A new multistage attack exploiting Elasticsearch servers using the old unpatched vulnerability to invoke a shell with a crafted query and encoded...
-
 220Ransomware
220RansomwareRansomware Attack on Electric Power Grid in South Africa Encrypt’s the Entire Network
Hackers attack Electric utility City Power on Johannesburg, South Africa using powerful ransomware and take down the entire network, applications, and database....
-
 308Cryptocurrency
308CryptocurrencyCrypto Loans Platform YouHodler Exposes Unencrypted Customer data that Includes Credit cards and Bank Details
Noam Rotem and Ran Locar with their research team found a database leak in YouHodler. YouHodler, A Crypto lending site offered an...
-
 206Malware
206MalwareHackers Attack Financial Institutions & Government Organizations With “Proyecto RAT”
Security researchers observed a new campaign targeting financial institutions and governmental organizations with a customized version of a remote access tool called...
-

 236Data Breach
236Data BreachTelecommunication Company Sprint Customers Account Hacked Through Samsung Website
American telecommunication company Sprint recently learned that hackers breached the customers account through Samsung website. According to the letter shared by the...
-

 280Malware
280MalwareBianLian Android Banking Malware is Back with Screen Recording and SSH Server Capabilities
BianLian malware was first detected in October 2018; the malware aims in stealing OTP authentication codes, check balances, inject push notifications, and...
-
 388Malware
388MalwareUSCYBERCOM Warned that Hackers Exploiting Microsoft Outlook Security Vulnerability to Deliver Malware
USCYBERCOM published an alert that hackers were exploiting the CVE-2017-11774 Microsoft Outlook Security Vulnerability to deliver malware using an HTTPS domain. Microsoft...
-
 371Malware
371MalwareOceanLotus APT Group Uses Undetected Ratsnif Remote Trojan to Leverage Network Attack’s
OceanLotus APT Group also known as APT32, SeaLotus, and CobaltKitty uses undetected Remote Access trojans Ratsnif to leverage network attack capabilities. The...
-
 320Malware
320MalwareRussian Google “Yandex” Hacked with Rare Type of Malware called Regin to Spy on Users Accounts
Russian Internet Giant Yandex hacked by Western intelligence agencies hackers with a rare type of malware called “Regin” to spy on Yandex...
-

 288Malware
288MalwareWaterbug APT Hackers Hijacked Another APT Group Infrastructure to Attack Governments and International Organizations
Waterbug APT Hackers used hijacked infrastructure to attack governments and international organizations through various campaigns using new and publically available malware. The...






