All posts tagged "Cyber Security"
-

 191Articles
191ArticlesNew Malware Takes Commands From Memes Posted On Twitter
Security researchers have discovered yet another example of how cybercriminals disguise their malware activities as regular traffic by using legitimate cloud-based services....
-

 173Articles
173ArticlesTwitter Discloses Suspected State-Sponsored Attack After Minor Data Breach
Twitter has been hit with a minor data breach incident that the social networking site believes linked to a suspected state-sponsored attack....
-

 220News
220NewsBulk Stolen User Information, Sold At A Bargain in the Deep Web
Personal information for sale? A lot of those ‘merchandise’ are available in the Deep web today. The deep web is the part...
-

 156Articles
156ArticlesCritical SQLite Flaw Leaves Millions of Apps Vulnerable to Hackers
Cybersecurity researchers have discovered a critical vulnerability in widely used SQLite database software that exposes billions of deployments to hackers. Dubbed as...
-

 159Articles
159ArticlesNew Shamoon Malware Variant Targets Italian Oil and Gas Company
Shamoon is back… one of the most destructive malware families that caused damage to Saudi Arabia’s largest oil producer in 2012 and...
-

 174Articles
174ArticlesNew Facebook Bug Exposed 6.8 Million Users Photos to Third-Party Apps
Facebook’s latest screw-up — a programming bug in Facebook website accidentally gave 1,500 third-party apps access to the unposted Facebook photos of...
-
 190Articles
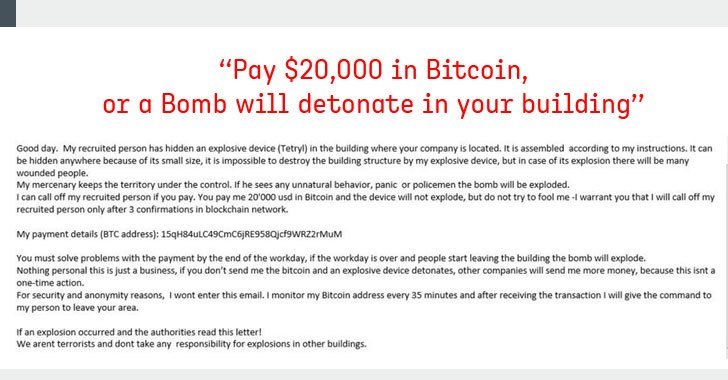
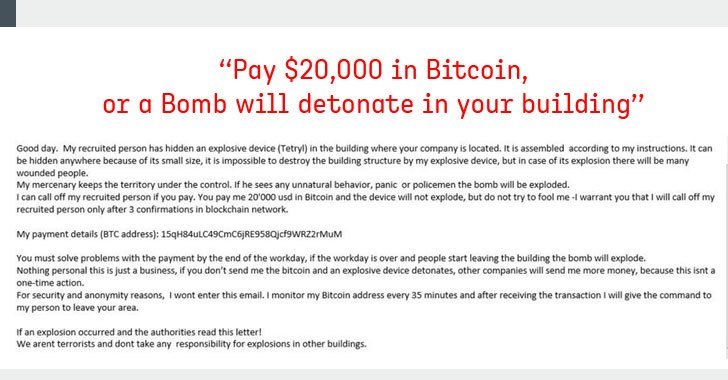
190ArticlesFake Bomb Threat Emails Demanding Bitcoins Sparked Chaos Across US, Canada
“Pay $20,000 worth of bitcoin, or a bomb will detonate in your building” A massive number of businesses, schools, government offices and...
-
 202Articles
202ArticlesAdobe’s Year-End Update Patches 87 Flaws in Acrobat Software
Adobe is closing out this year with its December Patch Tuesday update to address a massive number of security vulnerabilities for just...
-
 276Hacking Tools
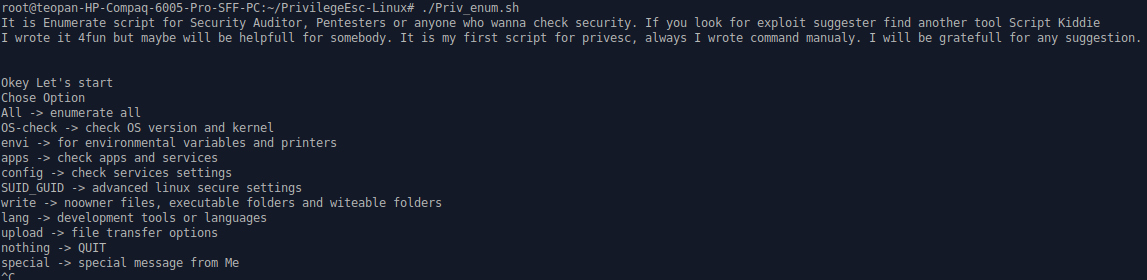
276Hacking ToolsPrivilegeEsc-Linux – Open Source Script for Enumeration on Linux
PrivilegeEsc-Linux is a simple script which checks the security on a Linux machine. It can run many different options, such as for...
-

 177Articles
177ArticlesphpMyAdmin Releases Critical Software Update — Patch Your Sites Now!
Developers of phpMyAdmin, one of the most popular and widely used MySQL database management systems, today released an updated version 4.8.4 of...
-

 160Articles
160ArticlesGoogle+ to Shut Down Early After New API Flaw Hits 52.5 Million Users
Google today revealed that Google+ has suffered another massive data breach, forcing the tech giant to shut down its struggling social network...
-

 238News
238NewsGoogle+ Flaw Hits 52.5M Users, Service to Shut Down Early
A new Google+ bug that has probably hit the accounts of about 52.5 million users has made Google think of shutting down...
-
 262Articles
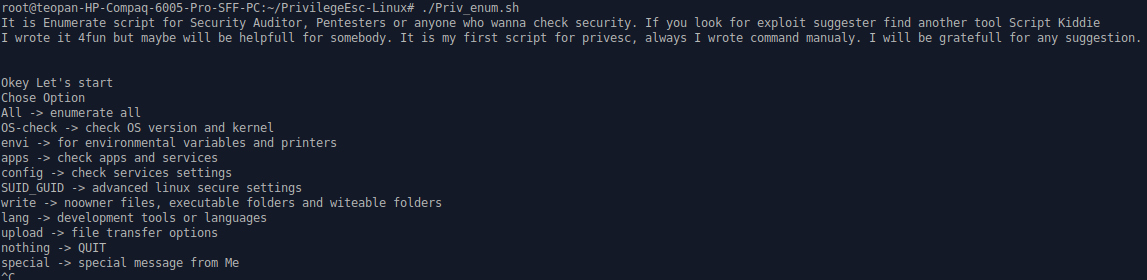
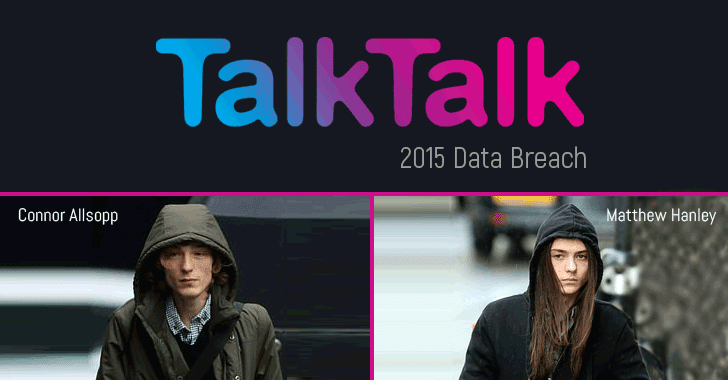
262ArticlesTwo TalkTalk hackers jailed for 2015 data breach that cost it £77 million
Two hackers have been sent to prison for their roles in hacking TalkTalk, one of the biggest UK-based telecommunications company, in 2015...
-

 155Articles
155ArticlesSafeguard Your Data And Privacy Online With This Award-Winning VPN
It seems as though not a day goes by without a new story breaking about a high-level cyber attack on a major...
-
 162Articles
162Articles3 New Code Execution Flaws Discovered in Atlantis Word Processor
This is why you should always think twice before opening innocent looking email attachments, especially word and pdf files. Cybersecurity researchers at...
-
 289Articles
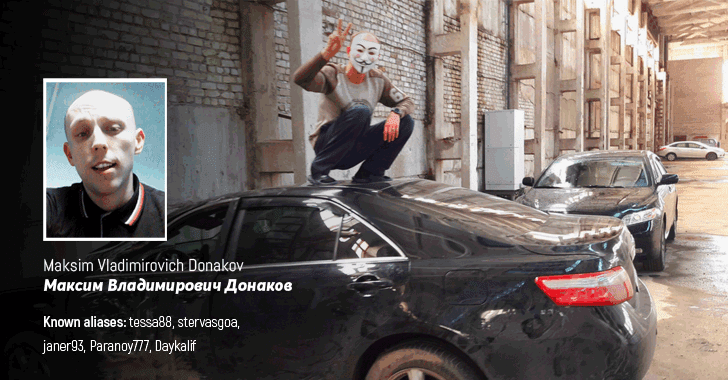
289ArticlesReal Identity of Hacker Who Sold LinkedIn, Dropbox Databases Revealed
The real identity of Tessa88—the notorious hacker tied to several high-profile cyber attacks including the LinkedIn, DropBox and MySpace mega breaches—has been...
-

 303Articles
303ArticlesGet paid up to $40,000 for finding ways to hack Facebook or Instagram accounts
Here we have great news for all bug bounty hunters. Now you can get paid up to $40,000 for finding and responsibly...
-
 331Articles
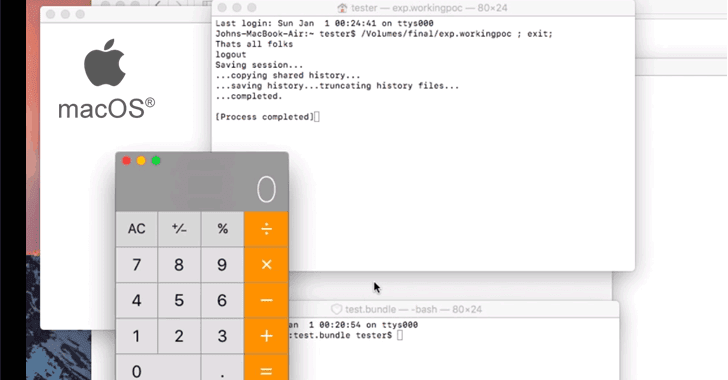
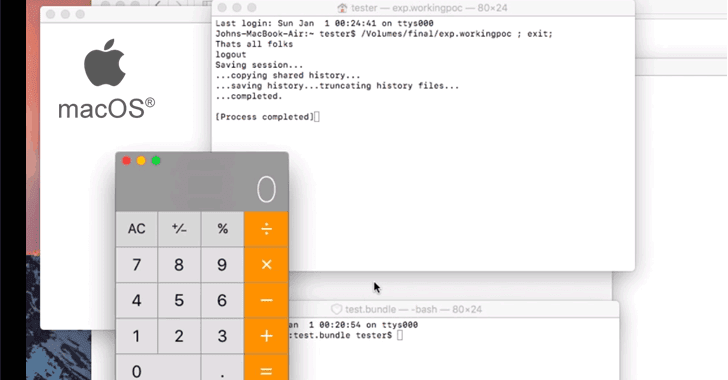
331ArticlesHow Just Opening A Site In Safari Could Have Hacked Your Apple macOS
Earlier this week Dropbox team unveiled details of three critical vulnerabilities in Apple macOS operating system, which altogether could allow a remote...
-

 185Articles
185ArticlesUS Postal Service Left 60 Million Users Data Exposed For Over a Year
The United States Postal Service has patched a critical security vulnerability that exposed the data of more than 60 million customers to...
-

 166Articles
166ArticlesRogue Developer Infects Widely Used NodeJS Module to Steal Bitcoins
A widely used third-party NodeJS module with nearly 2 million downloads a week was compromised after one of its open-source contributor gone...
-

 161Articles
161Articles8 Popular Android Apps Caught Up In Million-Dollar Ad Fraud Scheme
Cheetah Mobile—a prominent Chinese app company, known for its popular utility apps like Clean Master and Battery Doctor—and one of its subsidiary...






