All posts tagged "Cyber Security"
-

 229Hacking Tools
229Hacking ToolsXerosploit – Open Source Toolkit For Man In The Middle Attacks
Xerosploit is a python-based toolkit for creating efficient Man In The Middle attacks which combines the power of bettercap and nmap. The...
-
 228Infosec
228InfosecProtecting Big Data with Hadoop: A Cyber Security Protection Guide
Big Data analytics is emerging from today’s technology as people are demanding better ways to protect their Big data. Keep reading to...
-

 207News
207NewsCanada Imperial Bank of Commerce, Favorite Whipping Boy of Phishers
Phishing attacks anchor itself by its two strong instruments: Pretending to be from a popular brand The clever presentation making its message...
-
 361Geek
361GeekFrom cybercrime to cyber defence: How VPNs went mainstream
Virtual Private Networks, also known as VPNs, have had something of an image change in the last few years. Historically, the term...
-

 284News
284NewsA Defensive Approach in Cybersecurity is the Need of the Hour
Going by the adage “Prevention is better than cure”, it’s high time we adopted the defensive approach in cybersecurity. Ask any sensible...
-

 172Articles
172ArticlesTumblr Patches A Flaw That Could Have Exposed Users’ Account Info
Tumblr today published a report admitting the presence of a security vulnerability in its website that could have allowed hackers to steal...
-

 174Articles
174ArticlesLuminosityLink Hacking Tool Author Gets 30-Months Prison Sentence
A 21-year-old Kentucky man who previously pleaded guilty to developing, marketing, and selling an infamous remote access trojan (RAT) called LuminosityLink has...
-
 141Articles
141ArticlesLibSSH Flaw Allows Hackers to Take Over Servers Without Password
A four-year-old severe vulnerability has been discovered in the Secure Shell (SSH) implementation library known as Libssh that could allow anyone to...
-

 283Articles
283ArticlesGoogle Will Charge Android Phone Makers to Use Its Apps In Europe
Would you prefer purchasing an Android device that doesn’t have any apps or services from Google? No Google Maps, No Gmail, No...
-
 267Articles
267ArticlesNew iPhone Bug Gives Anyone Access to Your Private Photos
A security enthusiast who discovered a passcode bypass vulnerability in Apple’s iOS 12 late last month has now dropped another passcode bypass...
-

 167Articles
167ArticlesChrome, Firefox, Edge and Safari Plans to Disable TLS 1.0 and 1.1 in 2020
All major web browsers, including Google Chrome, Apple Safari, Microsoft Edge, Internet Explorer, and Mozilla Firefox, altogether today announced to soon remove...
-

 313Articles
313ArticlesGoogle to Encrypt Android Cloud Backups With Your Lock Screen Password
In an effort to secure users’ data while maintaining privacy, Google has announced a new security measure for Android Backup Service that...
-
 165Articles
165ArticlesSignal Secure Messaging App Now Encrypts Sender’s Identity As Well
Signal, the popular end-to-end encrypted messaging app, is planning to roll out a new feature that aims to hide the sender’s identity...
-

 171Articles
171ArticlesGoogle Adds Control-Flow Integrity to Beef up Android Kernel Security
Google has added a new security feature to the latest Linux kernels for Android devices to prevent it against code reuse attacks...
-
 181Articles
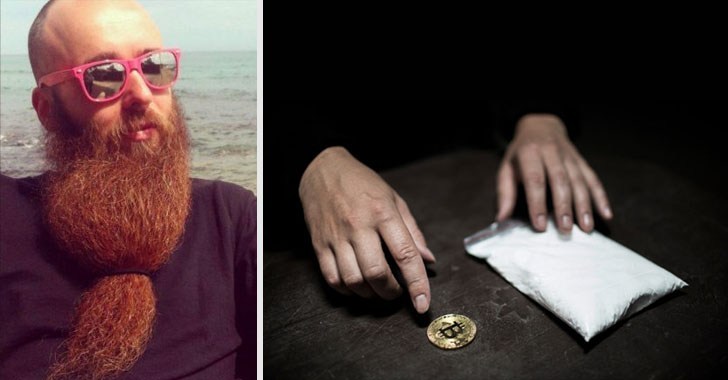
181ArticlesFrench Dark-Web Drug Dealer Sentenced to 20 Years in US Prison
A dark web drugs kingpin who was arrested last year when he arrived in the United States to compete in the World...
-
 182Articles
182ArticlesFacebook Classified the Stolen Data – Check If You’re One of Them
Late last month Facebook announced its worst-ever security breach that allowed an unknown group of hackers to steal secret access tokens for...
-

 142Articles
142ArticlesFortnite for Android Released, But Make Sure You Don’t Download Malware
Yes, it is official. The massively popular battle royale video game from Epic Games, Fortnite: Battle Royale is finally available for Android...
-

 165Articles
165ArticlesCritical Flaws Found in Amazon FreeRTOS IoT Operating System
A security researcher has discovered several critical vulnerabilities in one of the most popular embedded real-time operating systems—called FreeRTOS—and its other variants,...
-
 147Articles
147ArticlesUnpatched MS Word Flaw Could Allow Hackers to Infect Your Computer
Cybersecurity researchers have revealed an unpatched logical flaw in Microsoft Office 2016 and older versions that could allow an attacker to embed...
-
 199Articles
199ArticlesIBM Buys “Red Hat” Open-Source Software Company for $34 Billion
It’s been quite a year for the open source platforms. Earlier this year, Microsoft acquired popular code repository hosting service GitHub for...
-
 211Articles
211ArticlesWindows Built-in Antivirus Gets Secure Sandbox Mode – Turn It ON
Microsoft Windows built-in anti-malware tool, Windows Defender, has become the very first antivirus software to have the ability to run inside a...






