All posts tagged "Cyber Security"
-

 315Articles
315ArticlesUber fined $1.1 million by UK and Dutch regulators over 2016 data breach
British and Dutch data protection regulators Tuesday hit the ride-sharing company Uber with a total fine of $1,170,892 (~ 1.1 million) for...
-

 265Articles
265ArticlesFBI Shuts Down Multimillion Dollar – 3ve – Ad Fraud Operation
Google, the FBI, ad-fraud fighting company WhiteOps and a collection of cyber security companies worked together to shut down one of the...
-
 287Articles
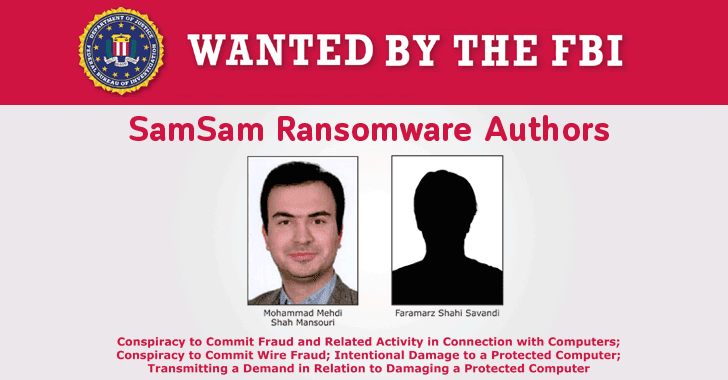
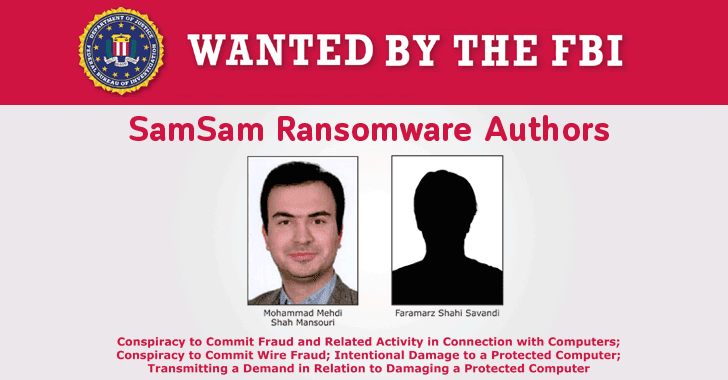
287ArticlesU.S Charges Two Iranian Hackers for SamSam Ransomware Attacks
The Department of Justice announced Wednesday charges against two Iranian nationals for their involvement in creating and deploying the notorious SamSam ransomware....
-

 294Articles
294ArticlesDell Resets All Customers’ Passwords After Potential Security Breach
Multinational computer technology company Dell disclosed Wednesday that its online electronics marketplace experienced a “cybersecurity incident” earlier this month when an unknown...
-
 258Articles
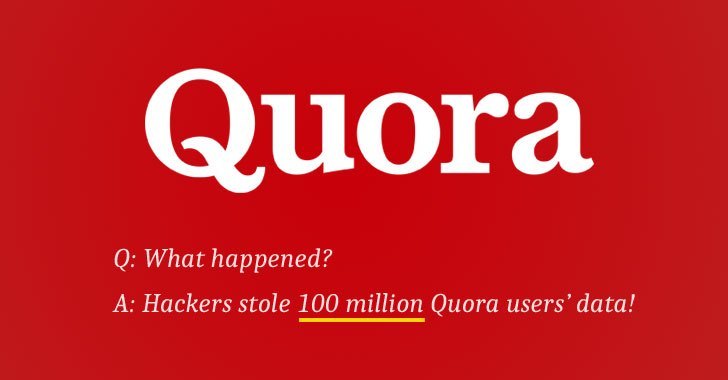
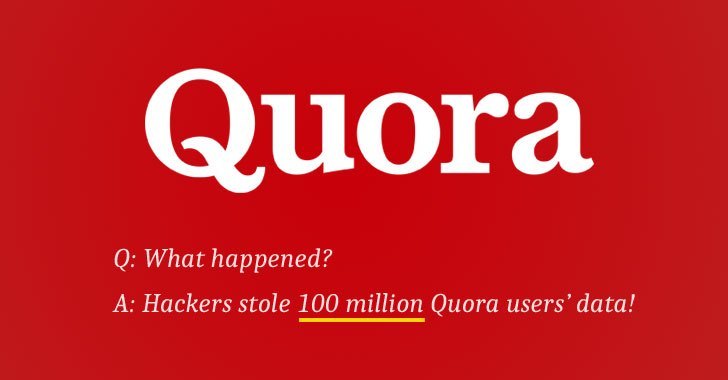
258ArticlesQuora Gets Hacked – 100 Million Users Data Stolen
The World’s most popular question-and-answer website Quora has suffered a massive data breach with unknown hackers gaining unauthorized access to potentially sensitive...
-
 417Articles
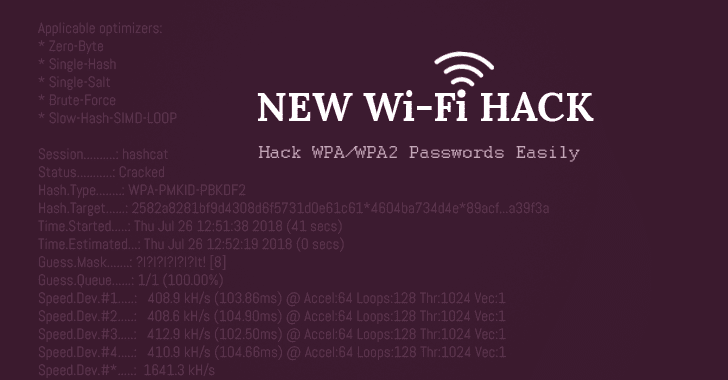
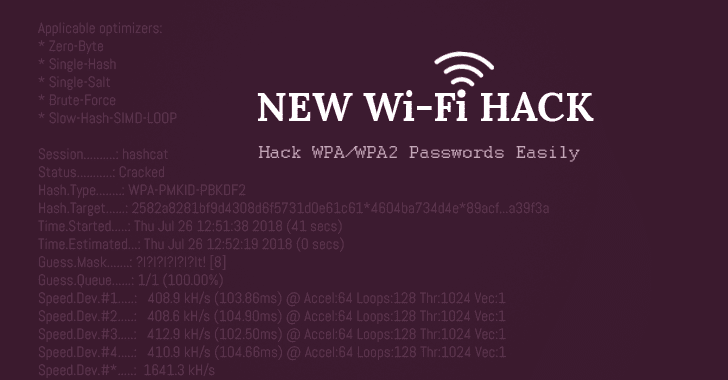
417ArticlesHow to Hack WiFi Password Easily Using New Attack On WPA/WPA2
Looking for how to hack WiFi password OR WiFi hacking software? Well, a security researcher has revealed a new WiFi hacking technique that...
-

 295Articles
295ArticlesMicrosoft building Chrome-based browser to replace Edge on Windows 10
It is no secret how miserably Microsoft’s 3-year-old Edge web browser has failed to compete against Google Chrome despite substantial investment and...
-
 179Articles
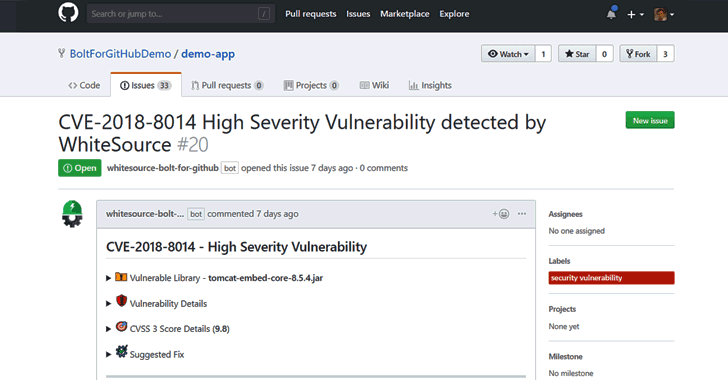
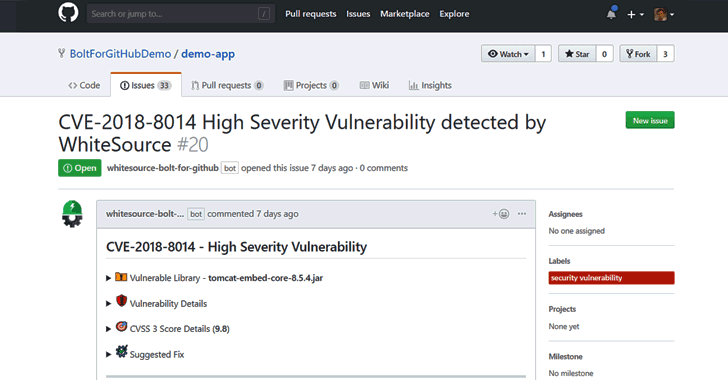
179ArticlesFree Open Source Vulnerability Management App for Developers
Developers around the world depend on open source components to build their software products. According to industry estimates, open source components account...
-
 314Articles
314ArticlesNew Adobe Flash Zero-Day Exploit Found Hidden Inside MS Office Docs
Cybersecurity researchers have discovered a new zero-day vulnerability in Adobe Flash Player that hackers are actively exploiting in the wild as part...
-
 133Articles
133ArticlesWarning! Unprivileged Linux Users With UID > INT_MAX Can Execute Any Command
Hold tight, this may blow your mind… A low-privileged user account on most Linux operating systems with UID value anything greater than...
-

 136Articles
136ArticlesNew Ransomware Spreading Rapidly in China Infected Over 100,000 PCs
A new piece of ransomware is spreading rapidly across China that has already infected more than 100,000 computers in the last four...
-
 231Articles
231ArticlesAI-Powered Online Automated Malware Analysis Platform
Looking for an automated malware analysis software? Something like a 1-click solution that doesn’t require any installation or configuration…a platform that...
-
 284Hacking Tools
284Hacking ToolsmassExploitConsole – An Open Source Tool For Exploiting Known Vulnerabilities
MassExploitConsole is a python based easy-to-use cli tool for executing exploits. It has a collection of exploits to execute, built-in scanner for...
-
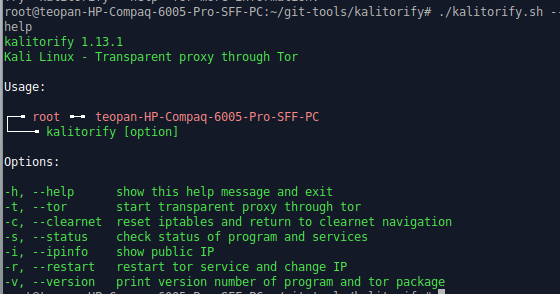
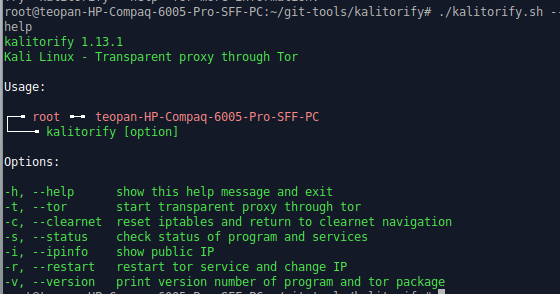 219Hacking Tools
219Hacking ToolsKalitorify – Open Source Tool to Run Kali Linux Traffic Through Tor
Kalitorify is a shell based script for Kali Linux. It uses iptables and TOR to create a transparent proxy. In simple terms,...
-

 305News
305NewsLondon Blue Cybergang List 50,000 execs for Phishing Attacks
As reported by SC Magazine, a U.K./Nigerian cybergang has accumulated a list of more than 50,000 corporate executives to be targeted in...
-
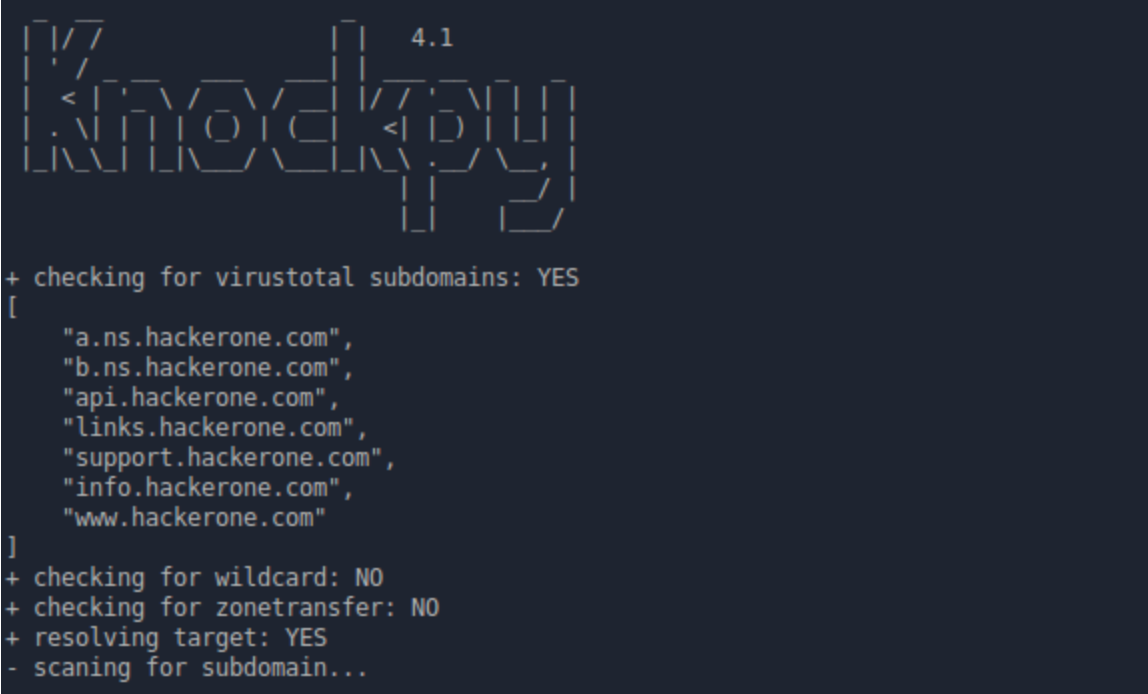
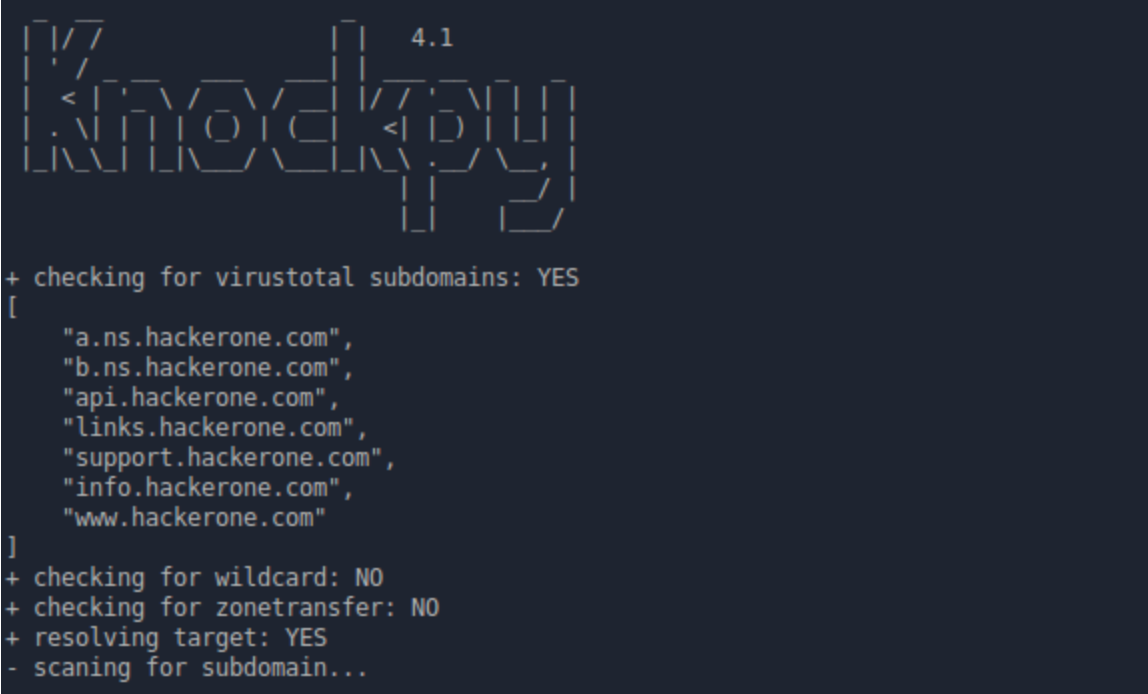 320Hacking Tools
320Hacking ToolsKnock – Open Source Subdomain Scanner Tool
Knock is a python based tool for enumerating subdomains on a targeted domain. You can use a custom wordlist and also you...
-

 152News
152NewsStealing Data from Infected Computer’s Blinking LED
This may sound strange, and to an extent startling as well. A hacker could steal data from your system (which would already...
-
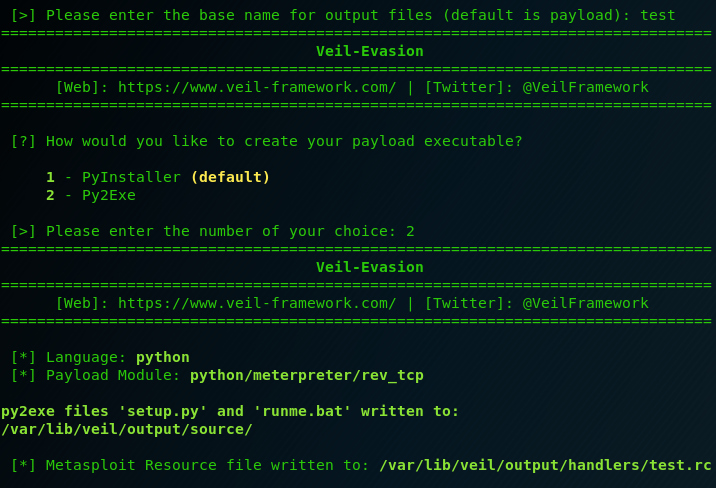
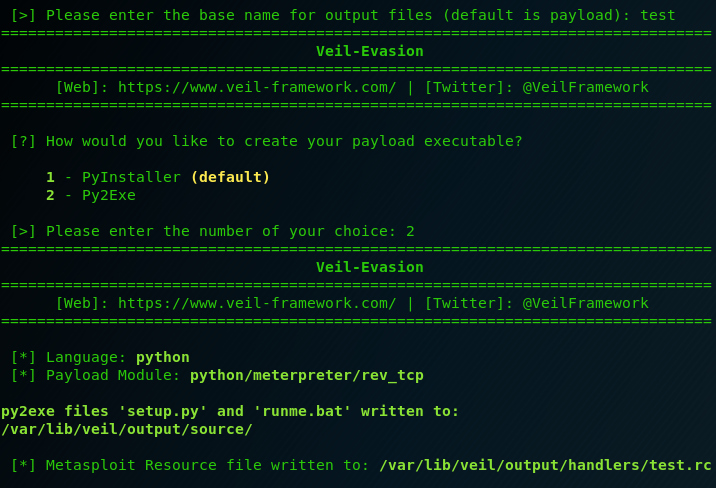 235Hacking Tools
235Hacking ToolsVeil-Framework – Open Source Tool to Bypass Common Anti-Virus Solutions
Based on python, the Veil-Framework is one of the most popular tools for Anti-Virus evasion. You can generate many different Metasploit payloads...
-

 349News
349NewsAustralia’s Shortage of Cybersecurity Professionals, Highlighted by the Government
The Cybersecurity-related profession is a very dynamic, too dynamic in fact that many in the industry are not formally educated to become...
-
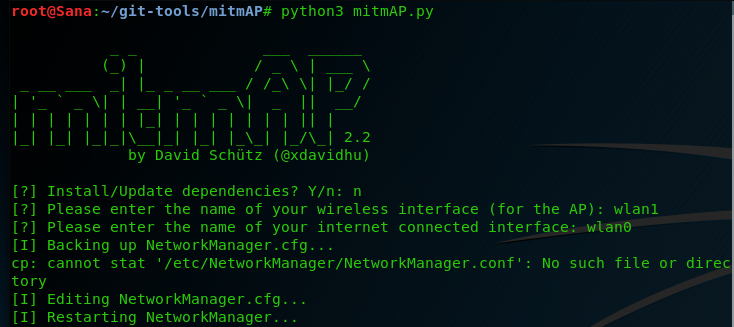
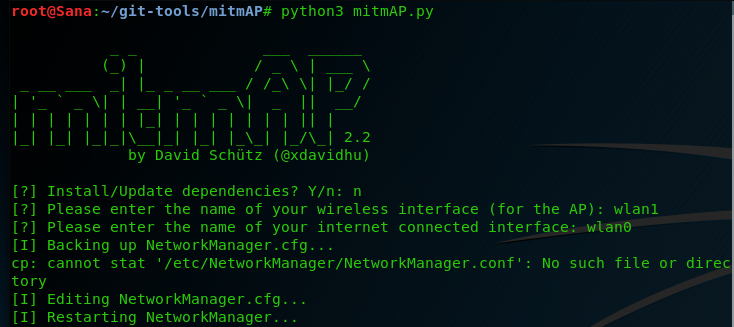 201Hacking Tools
201Hacking ToolsmitmAP – An Open Source Tool to Create a Fake Access Point and Sniff Data
The Evil Access Point (AP) attack has been around for a long time. There are several ways to create this attack and...
-

 292Cyber Crime
292Cyber CrimeSingapore, One of the Top Countries With Least the Cybersecurity Risk
Singapore is above average when it comes to the risks of being targeted by cyber attacks, that is the disclosure published in...






