All posts tagged "ethical hacking"
-

 2.7KHack Tools
2.7KHack ToolsLinuxCheck – Linux Information Collection Script
A small linux information collection script is mainly used for emergency response. It can be used under Debian or Centos.Features CPU TOP10,...
-
 2.1KHack Tools
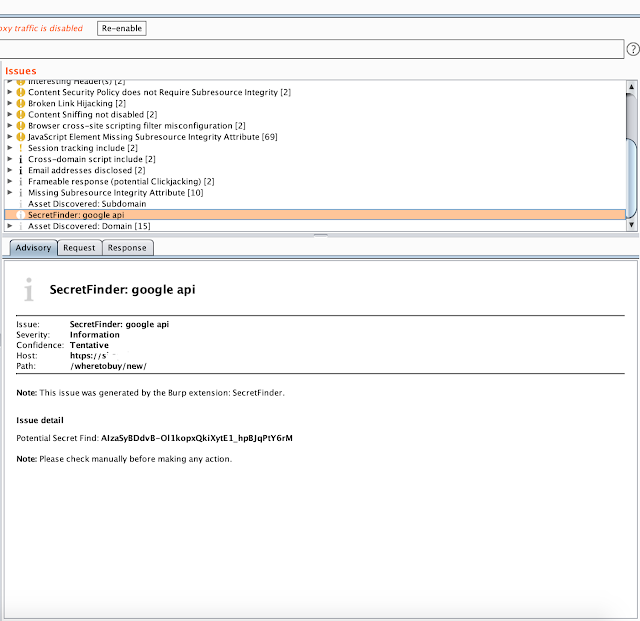
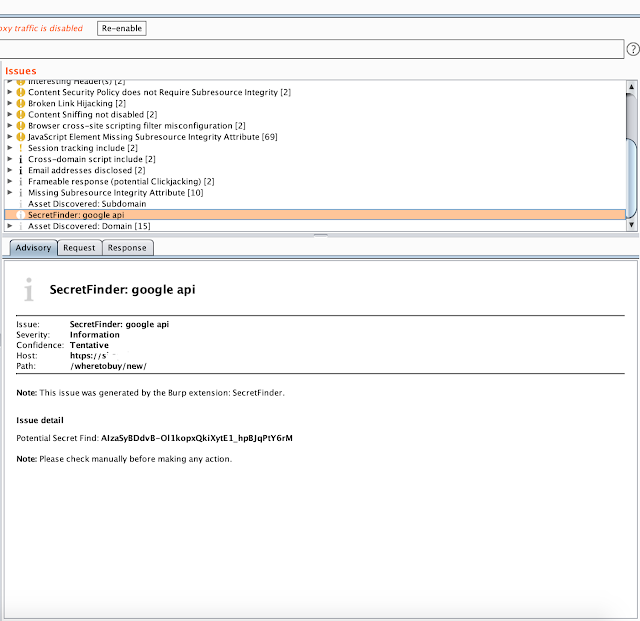
2.1KHack ToolsBurp Suite Secret Finder – Burp Suite Extension To Discover Apikeys/Tokens From HTTP Response
Burp Suite extension to discover a apikey/tokens from HTTP response. Install download SecretFinder wget https://raw.githubusercontent.com/m4ll0k/BurpSuite-Secret_Finder/master/SecretFinder.pyorgit clone https://github.com/m4ll0k/BurpSuite-Secret_Finder.git now open Burp > Extender...
-

 2.7KHack Tools
2.7KHack ToolsaSYNcrone – A SYN Flood DDoS Tool
aSYNcrone is a SYN Flood DDoS Attack Tool!Usage: git clone https://github.com/fatih4842/aSYNcrone.gitcd aSYNcronegcc aSYNcrone.c -o aSYNcrone./aSYNcrone <source IP> <source port> <destination IP> <destination...
-
 914Hack Tools
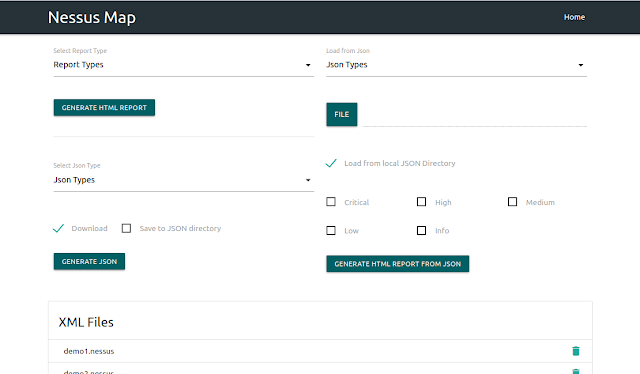
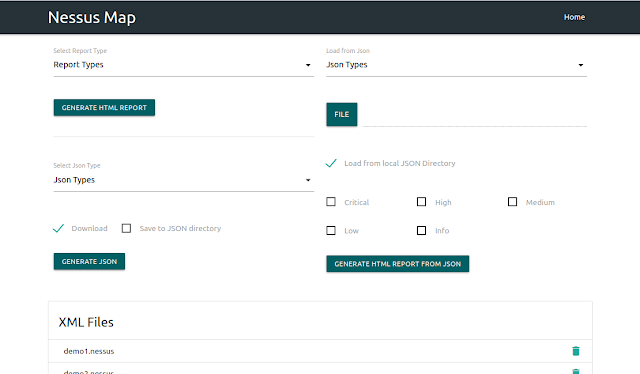
914Hack ToolsNessus Map – Parse .Nessus File(S) And Shows Output In Interactive UI
Nessus XML Praser Requirements Python3 Django Tested on Ubuntu 18.04 What it does Vulnerability based parsing Service based parsing Host bases parsing...
-
 2.1KHacking Tools
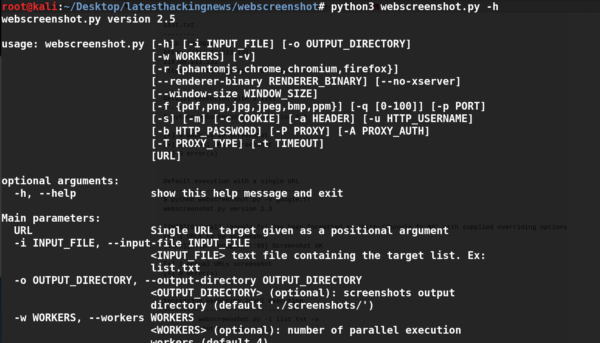
2.1KHacking Toolswebscreenshot.py | A Simple script that aids in testing large websites
Web Screenshot – webscreenshot.py is a great tool which comes in handy when a penetration tester needs to quickly identify potential vulnerabilities...
-

 3.8KHack Tools
3.8KHack ToolsSooty – The SOC Analysts All-In-One CLI Tool To Automate And Speed Up Workflow
Sooty is a tool developed with the task of aiding SOC analysts with automating part of their workflow. One of the goals...
-

 1.5KHack Tools
1.5KHack ToolsCAPE – Malware Configuration And Payload Extraction
CAPE is a malware sandbox. It is derived from Cuckoo and is designed to automate the process of malware analysis with the...
-

 2.2KHack Tools
2.2KHack ToolsANDRAX v4 DragonFly – Penetration Testing on Android
ANDRAX is a Penetration Testing platform developed specifically for Android smartphones, ANDRAX has the ability to run natively on Android so it behaves like a common...
-

 2.9KHack Tools
2.9KHack ToolsGoblin – An Impish, Cross-Platform Binary Parsing Crate, Written In Rust
Documentationhttps://docs.rs/goblin/changelog UsageGoblin requires rustc 1.31.1.Add to your Cargo.toml [dependencies]goblin = "0.1" Features awesome crate name zero-copy, cross-platform, endian-aware, ELF64/32 implementation – wow!...
-

 2.3KHack Tools
2.3KHack ToolsCCAT – Cloud Container Attack Tool For Testing Security Of Container Environments
Cloud Container Attack Tool (CCAT) is a tool for testing security of container environments. Quick reference Where to get help: the Pacu/CloudGoat/CCAT...
-
 1.3KHack Tools
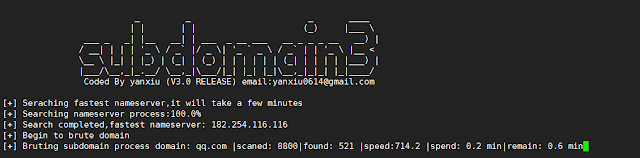
1.3KHack ToolsSubdomain3 – A New Generation Of Tool For Discovering Subdomains
Subdomain3 is a new generation of tool , It helps penetration testers to discover more information in a shorter time than other...
-

 4.1KHack Tools
4.1KHack ToolsMordor – Re-play Adversarial Techniques
The Mordor project provides pre-recorded security events generated by simulated adversarial techniques in the form of JavaScript Object Notation (JSON) files for...
-
 5.4KHack Tools
5.4KHack ToolsAttack Monitor – Endpoint Detection And Malware Analysis Software
Attack Monitor is Python application written to enhance security monitoring capabilites of Windows 7/2008 (and all later versions) workstations/servers and to automate...
-

 4.3KHack Tools
4.3KHack ToolsBaseQuery – A Way To Organize Public Combo-Lists And Leaks In A Way That You Can Easily Search Through Everything
Your private data is being traded and sold all over the internet as we speak. Tons of leaks come out on a...
-

 3.6KHack Tools
3.6KHack ToolsNetstat2Neo4J – Create Cypher Create Statements For Neo4J Out Of Netstat Files From Multiple Machines
Graphs help to spot anomalies and patterns in large datasets.This script takes netstat information from multiple hosts and formats them in a...
-
 3.2KHack Tools
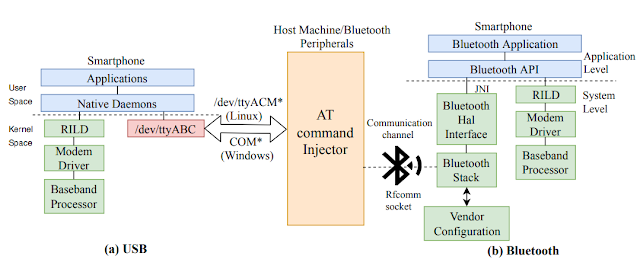
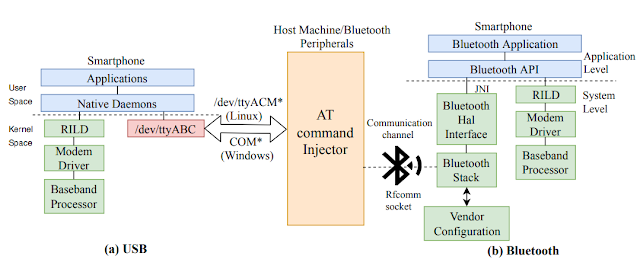
3.2KHack ToolsATFuzzer – Dynamic Analysis Of AT Interface For Android Smartphones
“Opening Pandora’s Box through ATFuzzer: Dynamic Analysis of AT Interface for Android Smartphones” is accepted to the 35th Annual Computer Security Applications...
-
 497Hack Tools
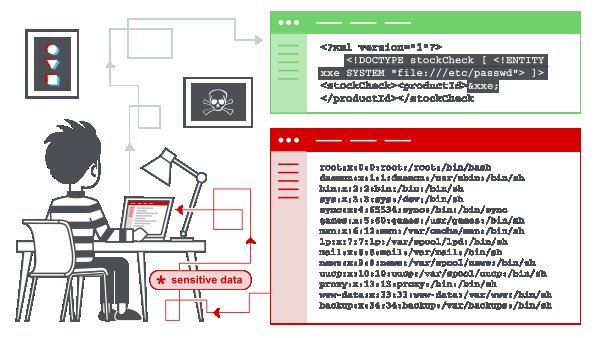
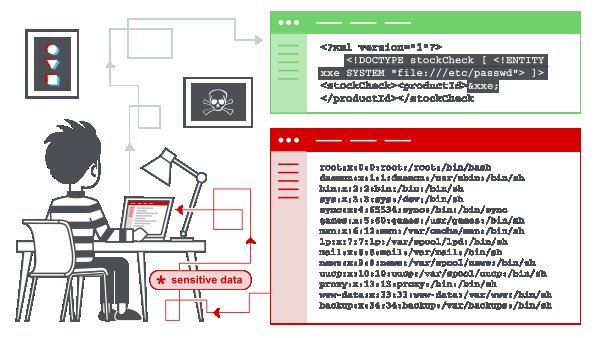
497Hack ToolsXML External Entity (XXE) Injection Payload List
In this section, we’ll explain what XML external entity injection is, describe some common examples, explain how to find and exploit various...
-
 1.1KHack Tools
1.1KHack ToolsKali Linux 2019.4 Release – Penetration Testing and Ethical Hacking Linux Distribution
We are incredibly excited to announce our fourth and final release of 2019, Kali Linux 2019.4. 2019.4 includes some exciting new updates:...
-
 2.3KHack Tools
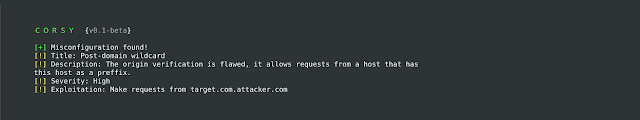
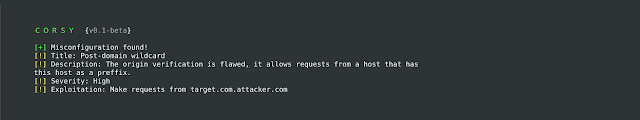
2.3KHack ToolsCorsy – CORS Misconfiguration Scanner
Corsy is a lightweight program that scans for all known misconfigurations in CORS implementations. UsageUsing Corsy is pretty simplepython corsy.py -u https://example.comA...
-
 4.6KHack Tools
4.6KHack ToolsFlan – A Pretty Sweet Vulnerability Scanner By CloudFlare
Flan Scan is a lightweight network vulnerability scanner. With Flan Scan you can easily find open ports on your network, identify services...
-
 1.2KHack Tools
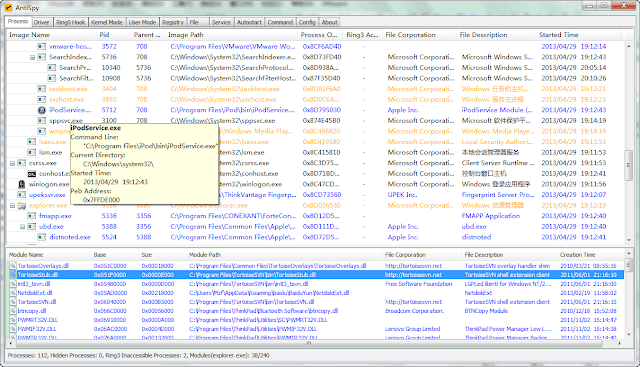
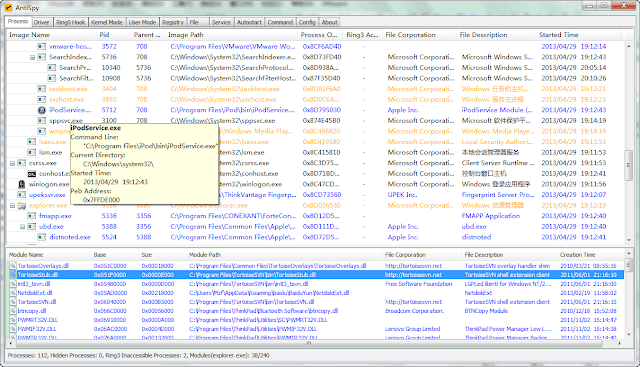
1.2KHack ToolsAntispy – A Free But Powerful Anti Virus And Rootkits Toolkit
AntiSpy is a free but powerful anti virus and rootkits toolkit.It offers you the ability with the highest privileges that can detect,analyze...






