All posts tagged "ethical hacking"
-

 195Incidents
195IncidentsGovernment Agency exposes millions of records of victims of natural disasters
By an oversight, the U.S. Federal Emergency Management Agency (FEMA) shared with a third party 2.3 million of records of natural disaster...
-

 252Incidents
252IncidentsIT employee was fired and deletes all his former employer’s AWS cloud servers
The authors of the book ‘Learn ethical hacking‘ narrate an unlikely story. A company fired one of its IT employees after only...
-

 377Malware
377MalwareAsus laptops users: Don’t update your software as new update has a backdoor
According to the authors of the book ‘Learn ethical hacking’, a group of hackers has infected hundreds of thousands of Asus computers...
-

 311Vulnerabilities
311VulnerabilitiesRemote execution vulnerability in Cisco IP Phone 7800 Series and 8800 Series
A vulnerability in the web based management interface of the Session Initiation Protocol (SIP) Software on the Cisco IP Phone 7800 Series...
-

 310Data Security
310Data SecurityChange your Facebook password and use multi-factor authentication; experts recommend
Change your Facebook password and get use to the multi-factor authentication; these are the main tips that the specialists from the best...
-

 176Incidents
176IncidentsPolice organization suffers ransomware infection
According to specialists in ethical hacking training in India and the International Institute of Cyber Security, the Police Federation of England and...
-

 273Malware
273MalwarePiewDiePie Ransomware: Encrypted files until YouTuber reaches 100 million subscribers
Subscribers to the PewDiePie YouTube channel have decided to take drastic steps to make the famous content creator consolidate as the user...
-

 253Incidents
253IncidentsTornado alert systems in Texas were hacked
On March 12th, around 2:00 A.M., the sound of emergency alerts awakened the inhabitants of two locations in Texas, U.S., all due...
-
 171Vulnerabilities
171VulnerabilitiesCritical key exchange vulnerability in PuTTY
PuTTY, the SSH client has been updated with various security patches, while its main maintainers recently admitted that a critical vulnerability was...
-

 278Cyber Events
278Cyber Events19-year-old ethical hacker is a millionaire now; thanks to his skills
Argentina’s Santiago Lopez is now a millionaire due to his prowess on identifying flaws in online services as well as software. The...
-

 292Hacking Tools
292Hacking ToolsKali Linux 2019.1 Released
Kali Linux 2019.1 is now available for download, updating many of its features, as well as introducing a few more. These include...
-

 207Incidents
207IncidentsCoinbase grants $30k USD to the hacker who discovered a critical vulnerability
Technical details about the vulnerability are still unknown Coinbase, the popular cryptocurrency exchange, has just awarded a $ 30k USD bounty to...
-
 315Tutorials
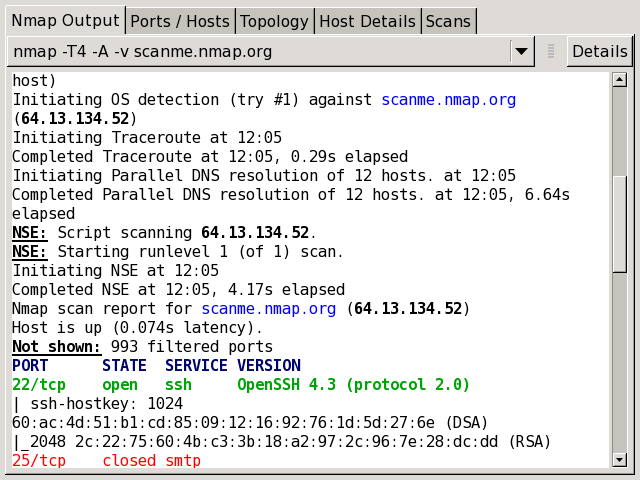
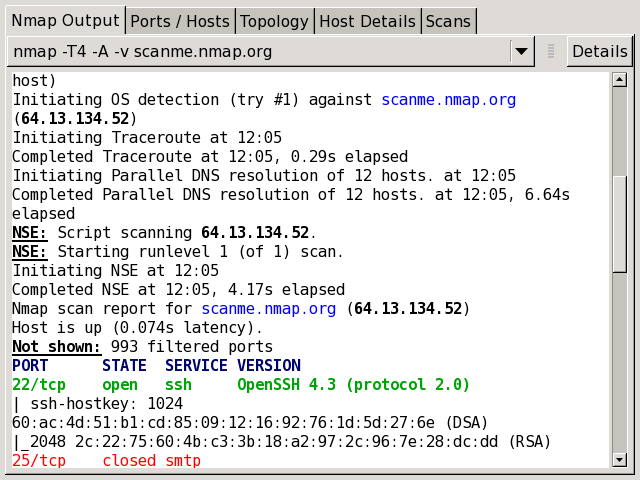
315TutorialsFind vulnerability of any target to hack
Scanning is the initial phase of pentesting. Security researchers/ pentesters are very well aware of this phase. This is the phase where...
-

 306Incidents
306IncidentsEthical hacker faces prison time for exposing vulnerabilities in a telecom company
The company considers that the defendant exceeded the limits of the ethical hacking labor The Hungarian authorities are investigating an ethical hacker...
-
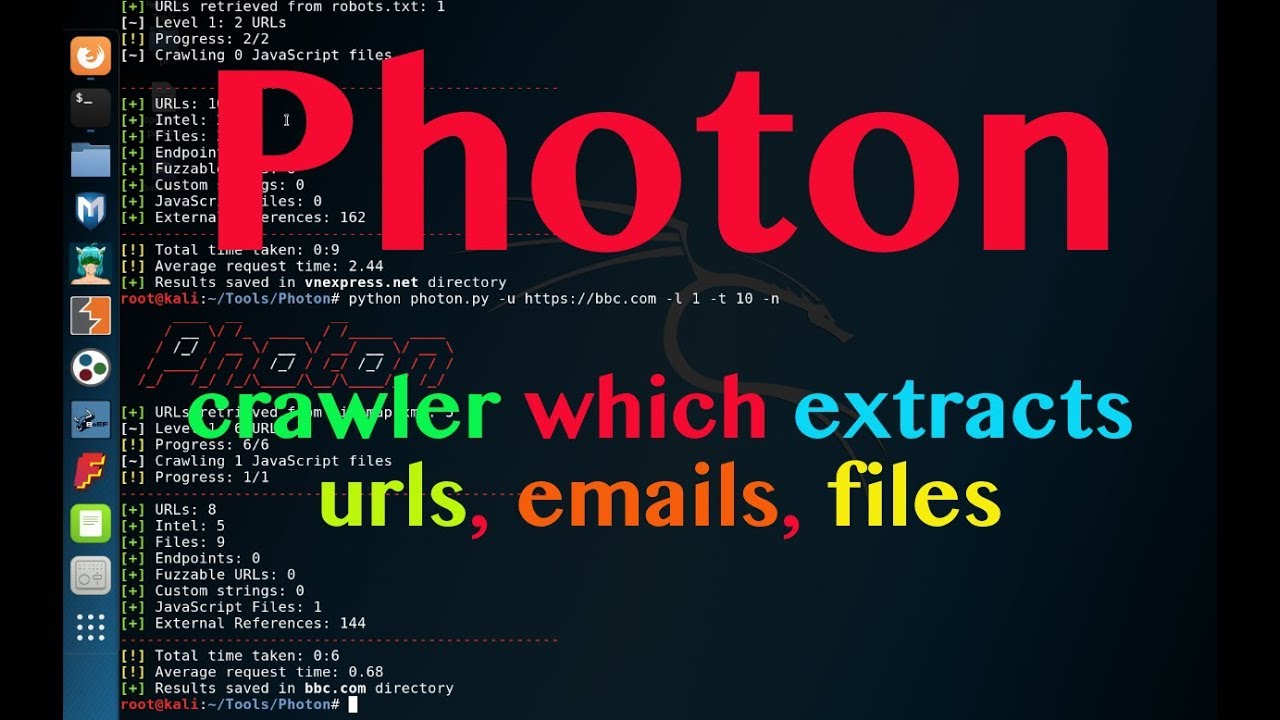
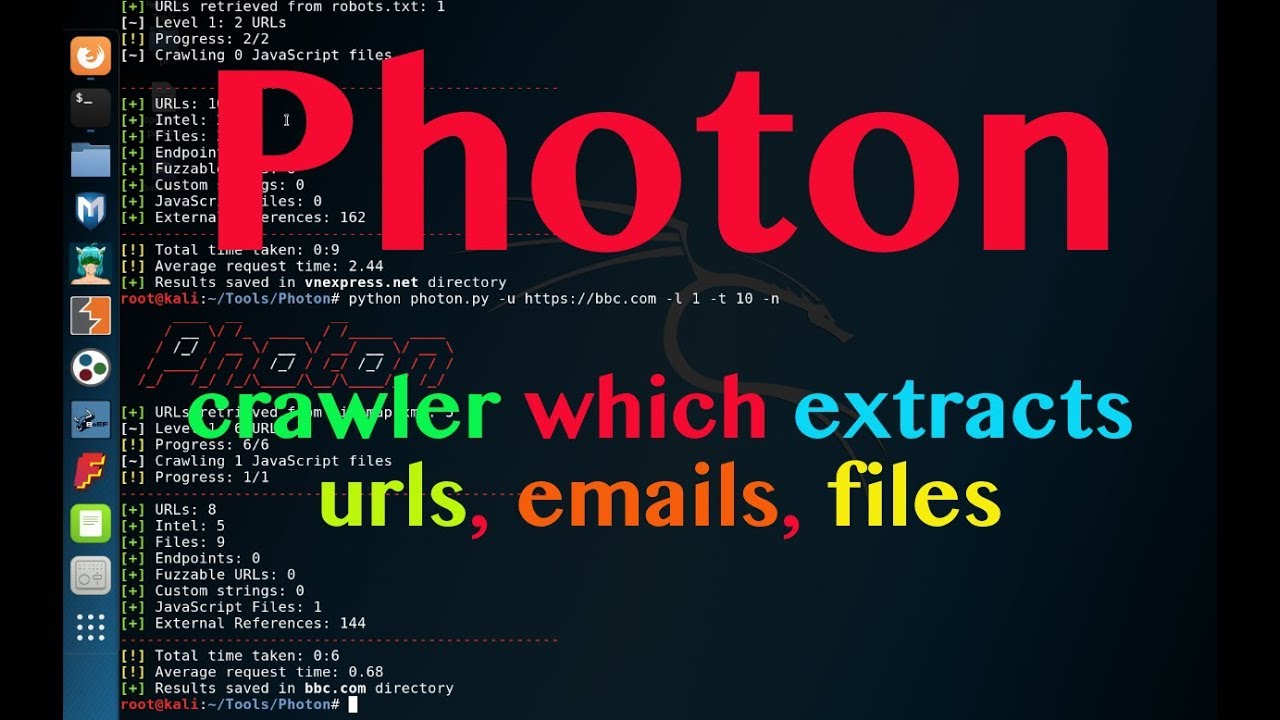 320Tutorials
320TutorialsHack secret keys, emails, subdomains, DNS of any company website
There are many tools which are used in gathering information. These tools gather information but are not able to gather some secret...
-

 337Tutorials
337TutorialsFake any website in seconds Facebook, Snapchat, Instagram :-
Social engineering has always been on top list in hacking world. The most simple and efficient way to steal login credentials of...
-

 271Data Security
271Data SecurityFacebook will pay you $40k USD for reporting bug
The social network would pay up to $40k USD for reporting errors that allow a single account takeover In the middle...
-
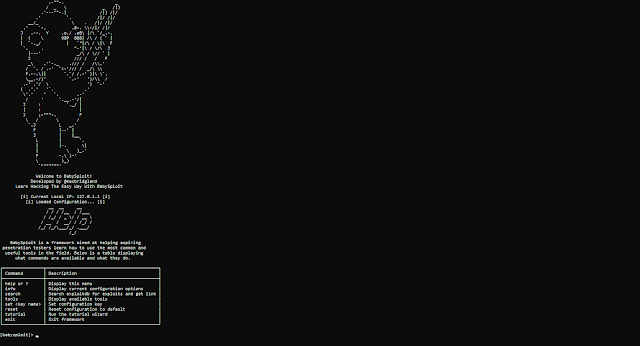
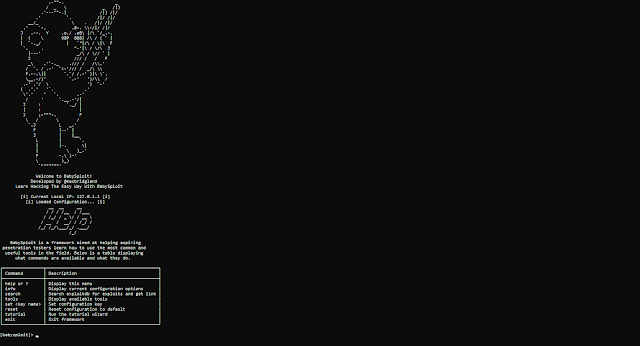 224Exploitation Tools
224Exploitation ToolsBabySploit – BabySploit Beginner Pentesting Framework
Tested on Kali Linux. Should work with all Debian based distros (and other ones if you have the right packages installed) BabySploit...
-

 287Incidents
287IncidentsPwn2Own Tokyo 2018 ethical hacking event
Sponsors paid over $100k USD for iPhone X exploits The ethical hacking event Pwn2Own 2018, conducted in Tokyo, organized by Zero Day...
-

 343Exploitation Tools
343Exploitation ToolsANDRAX – The First And Unique Penetration Testing Platform For Android Smartphones
ANDRAX The first and unique Penetration Testing platform for Android smartphones What is ANDRAX ANDRAX is a penetration testing platform developed specifically...
-

 258News
258NewsThe Best Ethical Hacking Courses for Programmers
Being on the internet is part of our day to day lives today. With the internet becoming so integral a part of...






