All posts tagged "hackers"
-

 374Cyber Events
374Cyber EventsUK companies have ‘misplaced confidence’ on cyber security
A majority of British businesses are convinced that they won’t fall victim to a damaging cyber attack, despite that fact that high-profile...
-

 310Cyber Crime
310Cyber CrimeScammers Targeting PayPal Users with “Suspicious Activity” Phishing Scam
PayPal has been one of the most attractive platforms for the hackers and spammers. During a recent year, PayPal users have been...
-

 167Hacked
167HackedFBI Advises Ransomware Victims To Pay The Ransom for Retrieving Data
Short Bytes: FBI has advised ransomware victims to pay the ransom and retrieve their data as there is not much the top...
-

 252News
252NewsUndisputed Hacker Group Fin5 Stole 150000 Credit Cards From Casinos
Two security firms (FireEye and Mandiant), have found a group of hackers (Fin5) who specialize in credit card stealing and have till date stolen...
-

 207Geek
207GeekMugShot Program Provides You Picture of Culprit Trying to Hack You
If you feel continually threatened by hackers then this program will help in tracking the culprit and definitely offer you some relief. You...
-
 111Data Security
111Data SecurityRussian-speaking hackers breach 97 websites, many of them dating ones
ussian-speaking hackers have breached 97 websites, mostly dating-related, and stolen login credentials, putting hundreds of thousands of users at risk. Many of...
-

 275Data Security
275Data SecurityHackers Can Replace Apps on Your Android Device with New Vulnerability
The Zero-day vulnerability presented by IBM’s researchers Or Peles and Roee Hay will affect all Android devices. The two researchers from IBM’s...
-
 289Hacked
289HackedRussian Hackers Attack Pentagon Computers, Used New and Unseen Methods
Short Bytes: In a recent cyberattack at Pentagon, Russian hackers are being suspected as the key players. This attack was launched around July...
-

 323Data Security
323Data SecurityElectronic Skateboards Are Easy To Hack
As we are approaching the much-awaited hacking conferences DefCon and Black Hat, security researchers and engineers are revealing their studies and exploits...
-

 191News
191NewsOne Million Android Users Infected With Facebook Hacking Malware Apps
Ever wondered about the number of users an Android-based malware app can infect after getting approved and published on the Google Play...
-

 286Hacked
286HackedCongrats Hacking Team: After Governments, Now Terrorists Have Your Tools
This Sunday, in a massive data breach at the Hacking Team, about 400GB of internal documents, spyware source codes, and tools were...
-

 298Cyber Events
298Cyber EventsAnonymous is Relatively Much Bigger Than You Anticipated
The global Anonymous network is relatively much bigger than your actual anticipation, a recent visual analysis by a University of Copenhagen graduate...
-

 286Hacked
286HackedHacking Team Becomes “Hacked Team”, Firm Sold Spying Tech to Governments
Hacking Team, a controversial company from Italy which specializes in selling powerful surveillance equipment to governments and their enforcement agencies, has been...
-

 296Data Security
296Data SecurityHackers Develop Android Malware Every 17 Seconds
By the first quarter of 2015, hacker/cyber-attackers have optimized their efforts to design Android Malware to such an extent that every seventeen...
-

 128Geek
128GeekHackerville: Inside the World’s Most Dangerous Town
Have you ever heard of a small town named Râmnicu Vâlcea from Romania? I’m pretty sure that your answer is no. This...
-

 112News
112NewsUber Petition Website Hacked- Hacker Uploaded Ad of Rival Firm Lyft
Due to a security flaw, researcher Austin Epperson took control of a page of Uber’s website and displayed the ad of its arch-rival...
-

 283Data Security
283Data SecurityHacker Targets Pedophiles with TOX Ransomware
Tox is yet another example of cyber justice that has been meted out by cyber criminals. In this case, Tox sends a...
-

 208News
208NewsPro-Palestinian Group Hacks Piatt County’s Sheriff Office Website
Summary: In a successful cyber attack the online pro-Palestinian hackivist AnonGhost hacked the official website of Piatt County, Illinois along with the...
-
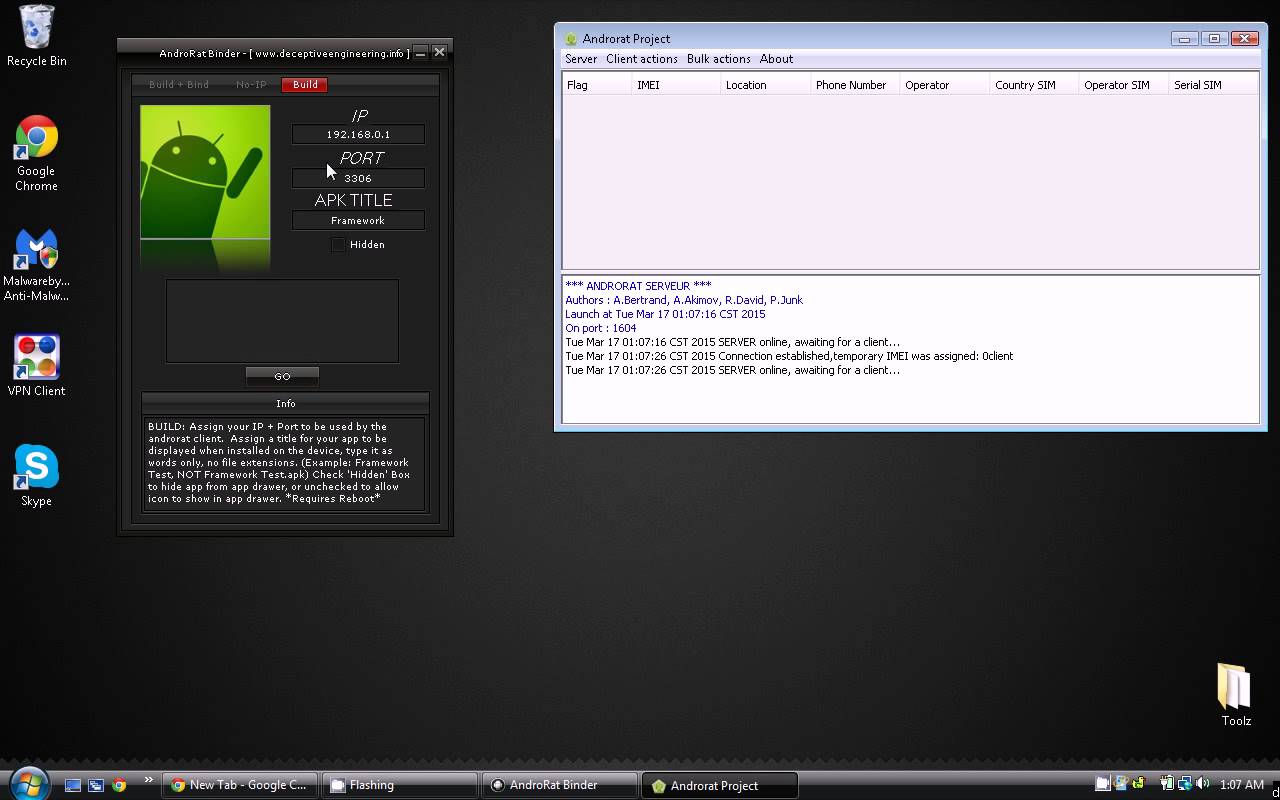
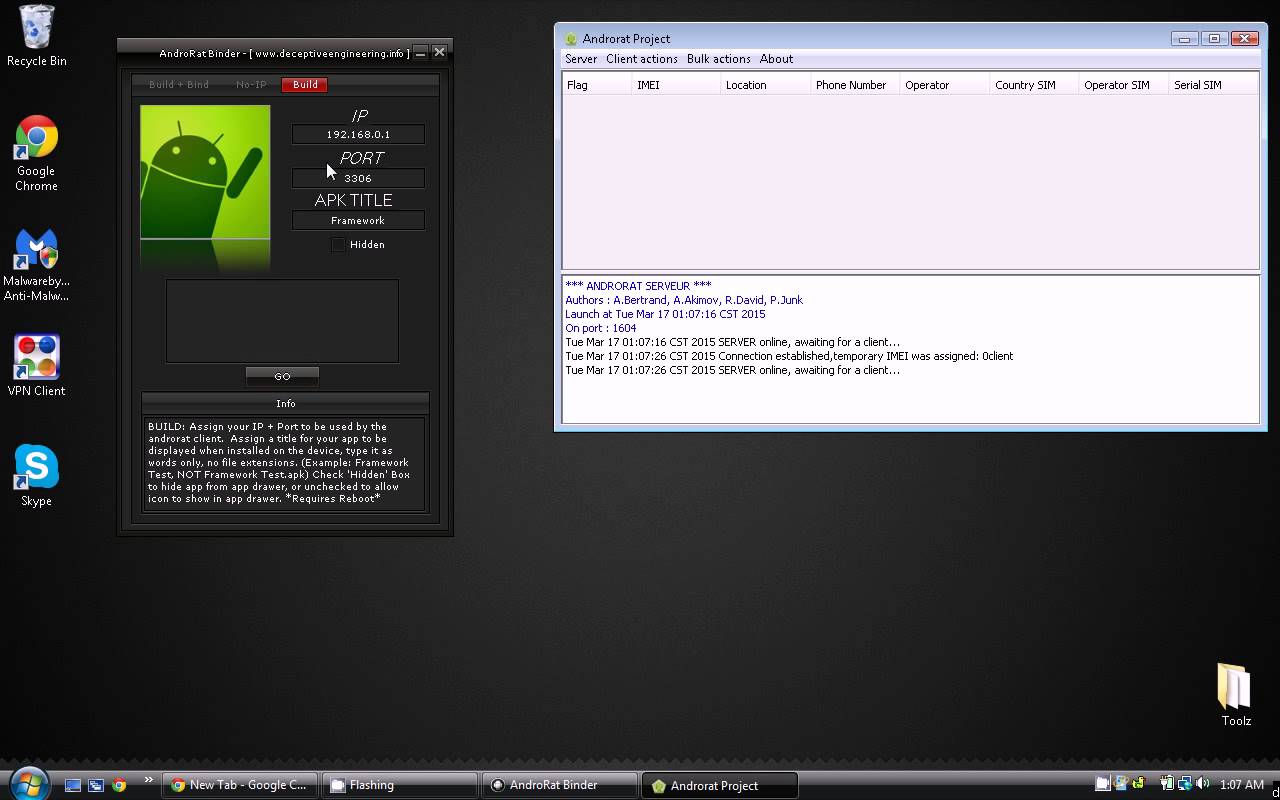 294How To
294How ToHow To Hack Android Phones With Androrat
In this tutorial we are going to show you how to hack Android phones with Androrat. In our tutorials we only EVER hack...
-

 198Data Security
198Data SecurityAre hackers experiencing karma in the Underground Economy?
The underground economy is a large group of websites that make it possible for hackers and fraudsters to trade illegal services and stolen...
-
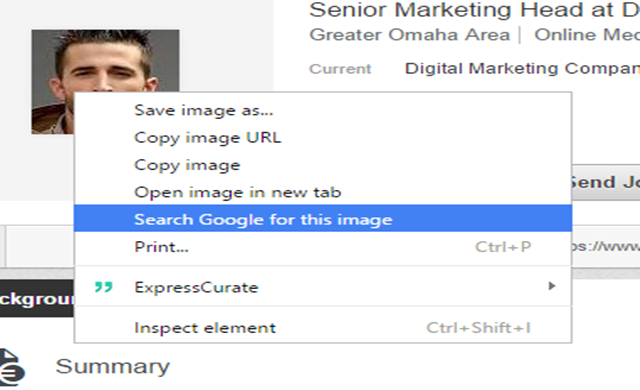
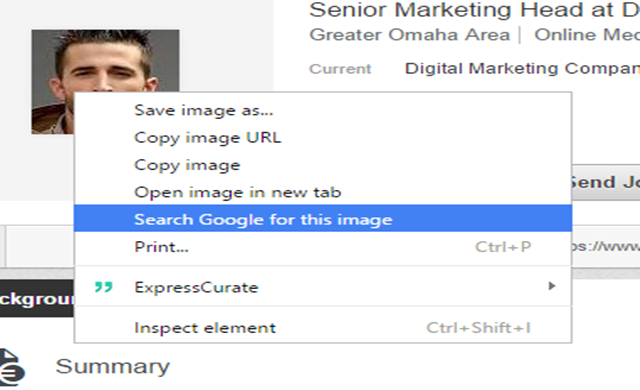 269Geek
269GeekIdentifying Fake Social Media Profiles Possible with Google Image Search
Creating fake social media accounts has been the favorite trick of hackers and scammers for interacting with potential victims. However, thanks to...






