All posts tagged "hacking news"
-
 689Vulnerabilities
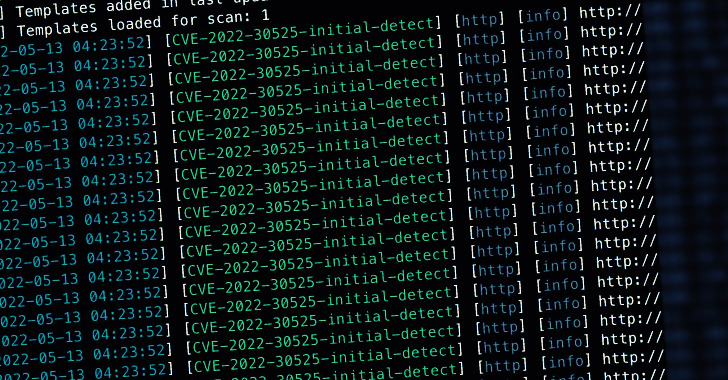
689VulnerabilitiesWatch Out! Hackers Begin Exploiting Recent Zyxel Firewalls RCE Vulnerability
Image source: z3r00t The U.S. Cybersecurity and Infrastructure Security Agency on Monday added two security flaws, including the recently disclosed remote code...
-
 1.5KMalware
1.5KMalwareResearchers Warn of “Eternity Project” Malware Service Being Sold via Telegram
An unidentified threat actor has been linked to an actively in-development malware toolkit called the “Eternity Project” that lets professional and amateur...
-

 1.5KVulnerabilities
1.5KVulnerabilitiesGoogle Created ‘Open Source Maintenance Crew’ to Help Secure Critical Projects
Google on Thursday announced the creation of a new “Open Source Maintenance Crew” to focus on bolstering the security of critical open...
-

 2.8KMalware
2.8KMalwareIranian Hackers Leveraging BitLocker and DiskCryptor in Ransomware Attacks
A ransomware group with an Iranian operational connection has been linked to a string of file-encrypting malware attacks targeting organizations in Israel,...
-
 3.7KMalware
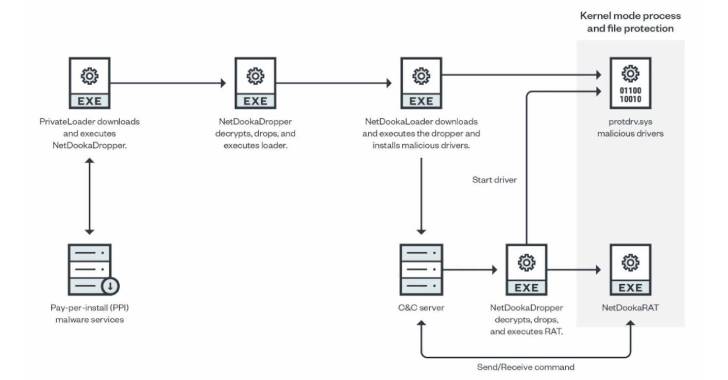
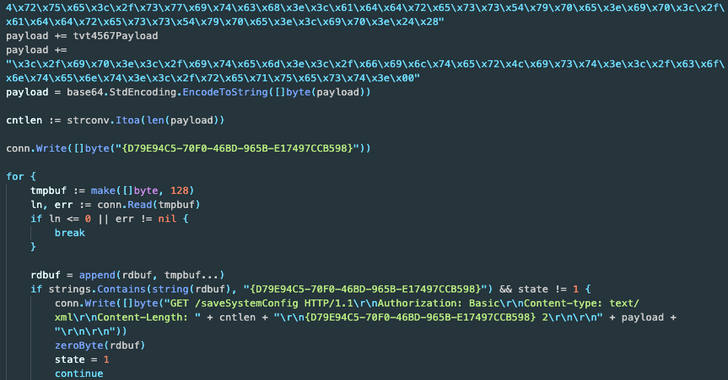
3.7KMalwareHackers Using PrivateLoader PPI Service to Distribute New NetDooka Malware
A pay-per-install (PPI) malware service known as PrivateLoader has been spotted distributing a “fairly sophisticated” framework called NetDooka, granting attackers complete control...
-

 1.3KMalware
1.3KMalwareUkraine War Themed Files Become the Lure of Choice for a Wide Range of Hackers
A growing number of threat actors are using the ongoing Russo-Ukrainian war as a lure in various phishing and malware campaigns, even...
-

 1.6KMalware
1.6KMalwareExperts Analyze Conti and Hive Ransomware Gangs’ Chats With Their Victims
An analysis of four months of chat logs spanning more than 40 conversations between the operators of Conti and Hive ransomware and...
-

 2.2KCyber Attack
2.2KCyber AttackRussian Hackers Targeting Diplomatic Entities in Europe, Americas, and Asia
A Russian state-sponsored threat actor has been observed targeting diplomatic and government entities as part of a series of phishing campaigns commencing...
-

 2.3KData Breach
2.3KData BreachIndian Govt Orders Organizations to Report Security Breaches Within 6 Hours to CERT-In
India’s computer and emergency response team, CERT-In, on Thursday published new guidelines that require service providers, intermediaries, data centers, and government entities...
-

 3.8KMalware
3.8KMalwareExperts Detail 3 Hacking Teams Working Under the Umbrella of TA410 Group
A cyberespionage threat actor known for targeting a variety of critical infrastructure sectors in Africa, the Middle East, and the U.S. has...
-

 2.9KMalware
2.9KMalwareNPM Bug Allowed Attackers to Distribute Malware as Legitimate Packages
A “logical flaw” has been disclosed in NPM, the default package manager for the Node.js JavaScript runtime environment, that enables malicious actors...
-

 3.1KVulnerabilities
3.1KVulnerabilitiesMicrosoft Discovers New Privilege Escalation Flaws in Linux Operating System
Microsoft on Tuesday disclosed a set of two privilege escalation vulnerabilities in the Linux operating system that could potentially allow threat actors...
-

 2.3KCyber Attack
2.3KCyber AttackGold Ulrick Hackers Still in Action Despite Massive Conti Ransomware Leak
The infamous ransomware group known as Conti has continued its onslaught against entities despite suffering a massive data leak of its own...
-

 3.2KMalware
3.2KMalwareNorth Korean Hackers Target Journalists with GOLDBACKDOOR Malware
A state-backed threat actor with ties to the Democratic People’s Republic of Korea (DRPK) has been attributed to a spear-phishing campaign targeting...
-
 405Malware
405MalwareNew BotenaGo Malware Variant Targeting Lilin Security Camera DVR Devices
A new variant of an IoT botnet called BotenaGo has emerged in the wild, specifically singling out Lilin security camera DVR devices...
-

 3.8KData Breach
3.8KData BreachT-Mobile Admits Lapsus$ Hackers Gained Access to its Internal Tools and Source Code
Telecom company T-Mobile on Friday confirmed that it was the victim of a security breach in March after the LAPSUS$ mercenary gang...
-
 4.7KMalware
4.7KMalwareWatch Out! Cryptocurrency Miners Targeting Dockers, AWS and Alibaba Cloud
LemonDuck, a cross-platform cryptocurrency mining botnet, is targeting Docker to mine cryptocurrency on Linux systems as part of an active malware campaign....
-

 3.3KMalware
3.3KMalwareHackers Sneak ‘More_Eggs’ Malware Into Resumes Sent to Corporate Hiring Managers
A new set of phishing attacks delivering the more_eggs malware has been observed striking corporate hiring managers with bogus resumes as an...
-
 3.9KCyber Attack
3.9KCyber AttackNew Incident Report Reveals How Hive Ransomware Targets Organizations
A recent Hive ransomware attack carried out by an affiliate involved the exploitation of “ProxyShell” vulnerabilities in the Microsoft Exchange Server that...
-

 1.3KData Breach
1.3KData BreachOkta Says Security Breach by Lapsus$ Hackers Impacted Only Two of Its Customers
Identity and access management provider Okta on Tuesday said it concluded its probe into the breach of a third-party vendor in late...
-
 4.7KVulnerabilities
4.7KVulnerabilitiesHackers Exploiting Recently Reported Windows Print Spooler Vulnerability in the Wild
A security flaw in the Windows Print Spooler component that was patched by Microsoft in February is being actively exploited in the...






