All posts tagged "hacking news"
-

 4.2KMalware
4.2KMalwareApple’s New “Lockdown Mode” Protects iPhone, iPad, and Mac Against Spyware
Apple on Wednesday announced it plans to introduce an enhanced security setting called Lockdown Mode in iOS 16, iPadOS 16, and macOS...
-
 1.4KMalware
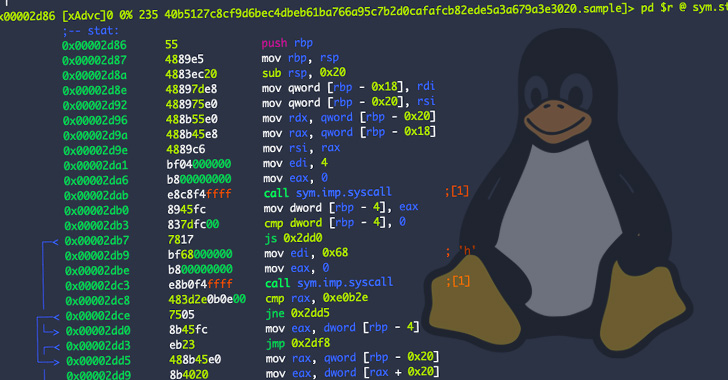
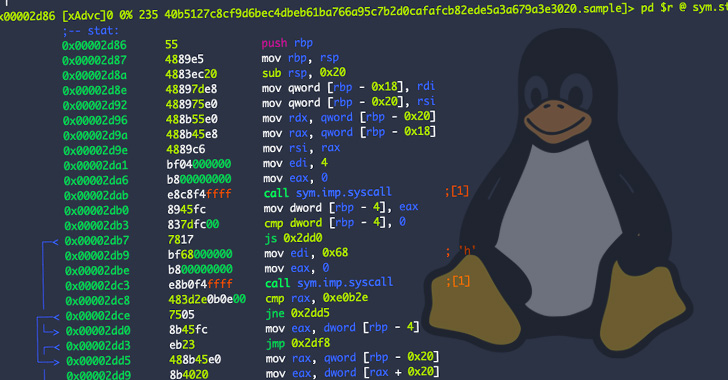
1.4KMalwareResearchers Warn of New OrBit Linux Malware That Hijacks Execution Flow
Cybersecurity researchers have taken the wraps off a new and entirely undetected Linux threat dubbed OrBit, signally a growing trend of malware...
-

 3.3KMalware
3.3KMalwareHackers Abusing BRc4 Red Team Penetration Tool in Attacks to Evade Detection
Malicious actors have been observed abusing legitimate adversary simulation software in their attacks in an attempt to stay under the radar and...
-
 4.8KMalware
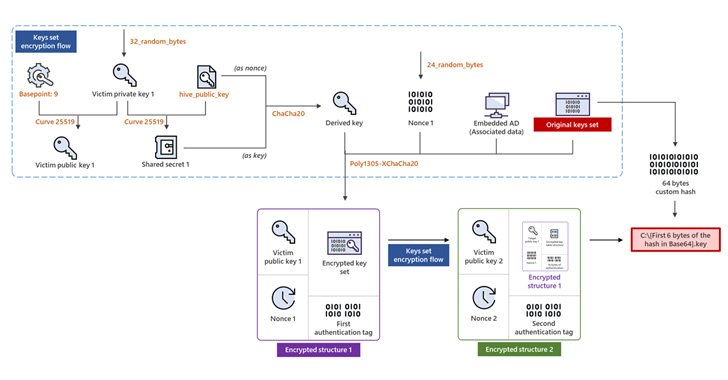
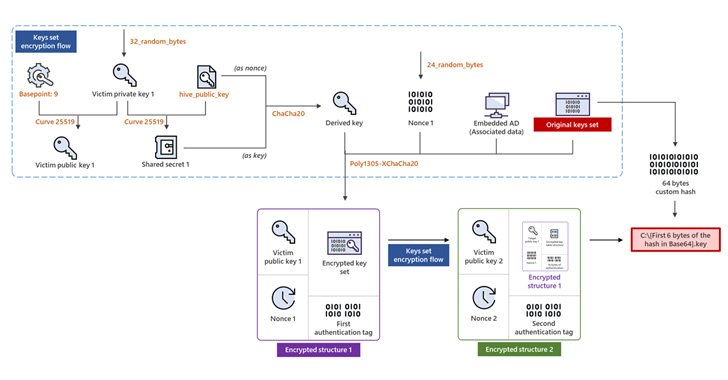
4.8KMalwareHive Ransomware Upgrades to Rust for More Sophisticated Encryption Method
The operators of the Hive ransomware-as-a-service (RaaS) scheme have overhauled their file-encrypting software to fully migrate to Rust and adopt a more...
-

 1.0KMalware
1.0KMalwareAs New Clues Emerges, Experts Wonder: Is REvil Back?
Change is a part of life, and nothing stays the same for too long, even with hacking groups, which are at their...
-

 5.2KMalware
5.2KMalwareNew ‘SessionManager’ Backdoor Targeting Microsoft IIS Servers in the Wild
A newly discovered malware has been put to use in the wild at least since March 2021 to backdoor Microsoft Exchange servers...
-

 5.1KVulnerabilities
5.1KVulnerabilitiesAmazon Quietly Patches ‘High Severity’ Vulnerability in Android Photos App
Amazon, in December 2021, patched a high severity vulnerability affecting its Photos app for Android that could have been exploited to steal...
-
 3.5KMalware
3.5KMalwareEx-Canadian Government Employee Pleads Guilty Over NetWalker Ransomware Attacks
A former Canadian government employee this week agreed to plead guilty in the U.S. to charges related to his involvement with the...
-
 1.9KVulnerabilities
1.9KVulnerabilitiesCISA Warns of Active Exploitation of ‘PwnKit’ Linux Vulnerability in the Wild
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) this week moved to add a Linux vulnerability dubbed PwnKit to its Known Exploited...
-

 746Cyber Attack
746Cyber AttackAPT Hackers Targeting Industrial Control Systems with ShadowPad Backdoor
Entities located in Afghanistan, Malaysia, and Pakistan are in the crosshairs of an attack campaign that targets unpatched Microsoft Exchange Servers as...
-

 1.4KData Breach
1.4KData BreachOverview of Top Mobile Security Threats in 2022
Your smartphone is your daily companion. The chances are that most of our activities rely on them, from ordering food to booking...
-
 1.9KVulnerabilities
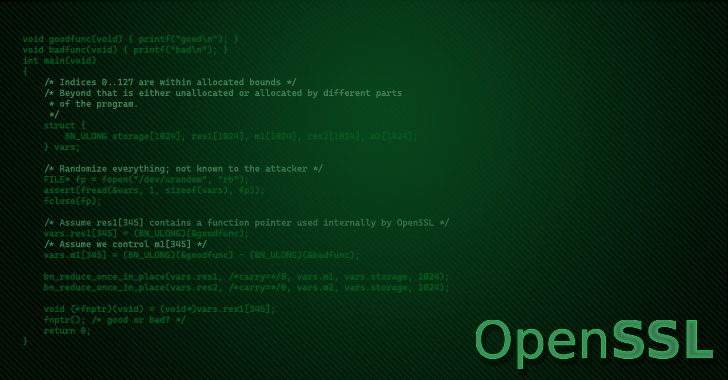
1.9KVulnerabilitiesOpenSSL to Release Security Patch for Remote Memory Corruption Vulnerability
The latest version of the OpenSSL library has been discovered as susceptible to a remote memory-corruption vulnerability on select systems. The issue...
-

 4.2KMalware
4.2KMalwareNew Android Banking Trojan ‘Revive’ Targeting Users of Spanish Financial Services
A previously unknown Android banking trojan has been discovered in the wild, targeting users of the Spanish financial services company BBVA. Said...
-

 1.6KMalware
1.6KMalwareCybersecurity Experts Warn of Emerging Threat of “Black Basta” Ransomware
The Black Basta ransomware-as-a-service (RaaS) syndicate has amassed nearly 50 victims in the U.S., Canada, the U.K., Australia, and New Zealand within...
-

 4.5KMalware
4.5KMalwareResearchers Warn of ‘Matanbuchus’ Malware Campaign Dropping Cobalt Strike Beacons
A malware-as-a-service (Maas) dubbed Matanbuchus has been observed spreading through phishing campaigns, ultimately dropping the Cobalt Strike post-exploitation framework on compromised machines....
-

 5.0KMalware
5.0KMalwareGoogle Says ISPs Helped Attackers Infect Targeted Smartphones with Hermit Spyware
A week after it emerged that a sophisticated mobile spyware dubbed Hermit was used by the government of Kazakhstan within its borders,...
-

 1.7KMalware
1.7KMalwareState-Backed Hackers Using Ransomware as a Decoy for Cyber Espionage Attacks
A China-based advanced persistent threat (APT) group is possibly deploying short-lived ransomware families as a decoy to cover up the true operational...
-

 4.6KMalware
4.6KMalwareChinese Hackers Distributing SMS Bomber Tool with Malware Hidden Inside
A threat cluster with ties to a hacking group called Tropic Trooper has been spotted using a previously undocumented malware coded in...
-
 4.9KCyber Attack
4.9KCyber AttackCritical PHP Vulnerability Exposes QNAP NAS Devices to Remote Attacks
QNAP, Taiwanese maker of network-attached storage (NAS) devices, on Wednesday said it’s in the process of fixing a critical three-year-old PHP vulnerability...
-

 3.3KMalware
3.3KMalwareEuropol Busts Phishing Gang Responsible for Millions in Losses
Europol on Tuesday announced the dismantling of an organized crime group that dabbled in phishing, fraud, scams, and money laundering activities. The...
-

 3.3KMalware
3.3KMalwareRIG Exploit Kit Now Infects Victims’ PCs With Dridex Instead of Raccoon Stealer
The operators behind the Rig Exploit Kit have swapped the Raccoon Stealer malware for the Dridex financial trojan as part of an...






