All posts tagged "hacking news"
-

 2.4KCyber Attack
2.4KCyber AttackThe Business of Hackers-for-Hire Threat Actors
Today’s web has made hackers’ tasks remarkably easy. For the most part, hackers don’t even have to hide in the dark recesses...
-

 2.9KCyber Attack
2.9KCyber AttackHackers Behind Twilio Breach Also Targeted Cloudflare Employees
Web infrastructure company Cloudflare on Tuesday disclosed at least 76 employees and their family members received text messages on their personal and...
-
 4.4KMalware
4.4KMalwareNew IoT RapperBot Malware Targeting Linux Servers via SSH Brute-Forcing Attack
A new IoT botnet malware dubbed RapperBot has been observed rapidly evolving its capabilities since it was first discovered in mid-June 2022....
-

 472Vulnerabilities
472VulnerabilitiesHackers Exploit Twitter Vulnerability to Exposes 5.4 Million Accounts
Twitter on Friday revealed that a now-patched zero-day bug was used to link phone numbers and emails to user accounts on the...
-

 3.6KMalware
3.6KMalwareIranian Hackers Likely Behind Disruptive Cyberattacks Against Albanian Government
A threat actor working to further Iranian goals is said to have been behind a set of damaging cyberattacks against Albanian government...
-
 3.9KCyber Attack
3.9KCyber AttackEmergency Alert System Flaws Could Let Attackers Transmit Fake Messages
The U.S. Department of Homeland Security (DHS) has warned of critical security vulnerabilities in Emergency Alert System (EAS) encoder/decoder devices. If left...
-
 3.8KMalware
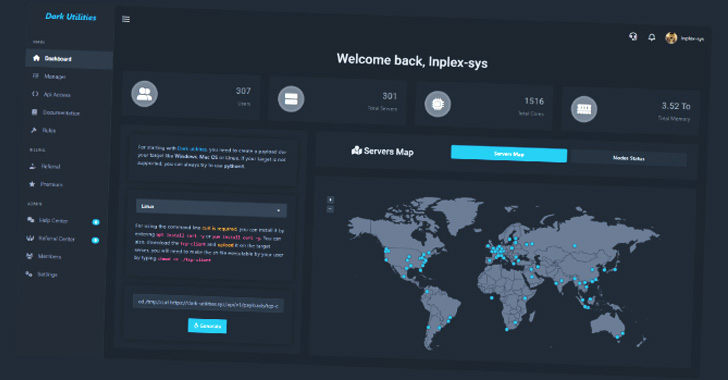
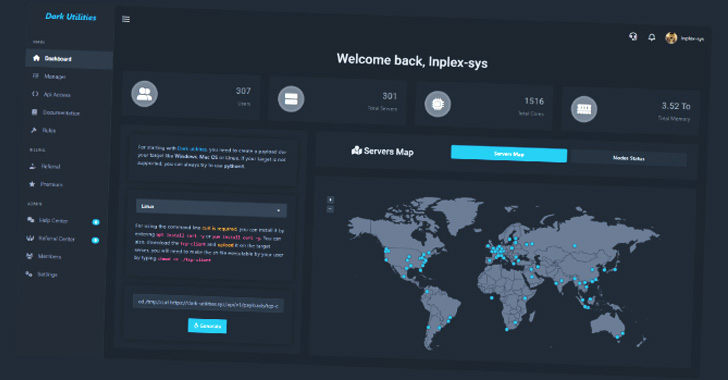
3.8KMalwareA Growing Number of Malware Attacks Leveraging Dark Utilities ‘C2-as-a-Service’
A nascent service called Dark Utilities has already attracted 3,000 users for its ability to provide command-and-control (C2) services with the goal...
-

 4.0KMalware
4.0KMalwareCritical RCE Bug Could Let Hackers Remotely Take Over DrayTek Vigor Routers
As many as 29 different router models from DrayTek have been identified as affected by a new critical, unauthenticated remote code execution...
-

 4.5KMalware
4.5KMalwareNew Woody RAT Malware Being Used to Target Russian Organizations
An unknown threat actor has been targeting Russian entities with a newly discovered remote access trojan called Woody RAT for at least...
-

 957Vulnerabilities
957VulnerabilitiesHackers Exploited Atlassian Confluence Bug to Deploy Ljl Backdoor for Espionage
A threat actor is said to have “highly likely” exploited a security flaw in an outdated Atlassian Confluence server to deploy a...
-

 4.5KMalware
4.5KMalwareVirusTotal Reveals Most Impersonated Software in Malware Attacks
Threat actors are increasingly mimicking legitimate applications like Skype, Adobe Reader, and VLC Player as a means to abuse trust relationships and...
-
 4.3KMalware
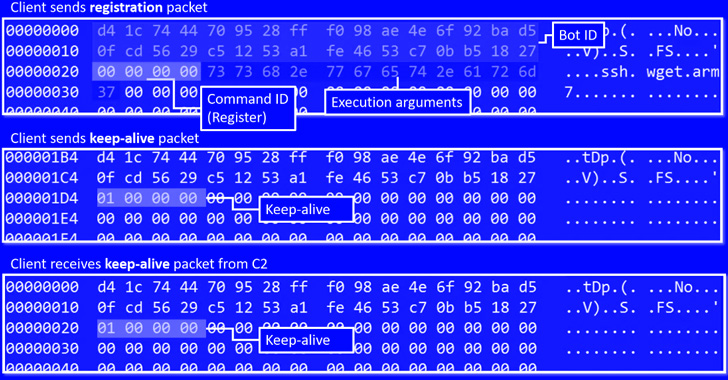
4.3KMalwareChinese Hackers Using New Manjusaka Hacking Framework Similar to Cobalt Strike
Researchers have disclosed a new offensive framework referred to as Manjusaka that they call is a “Chinese sibling of Sliver and Cobalt...
-

 3.5KMalware
3.5KMalwareWhat is ransomware and how can you defend your business from it?
Ransomware is a kind of malware used by cybercriminals to stop users from accessing their systems or files; the cybercriminals then threaten...
-
 5.0KMalware
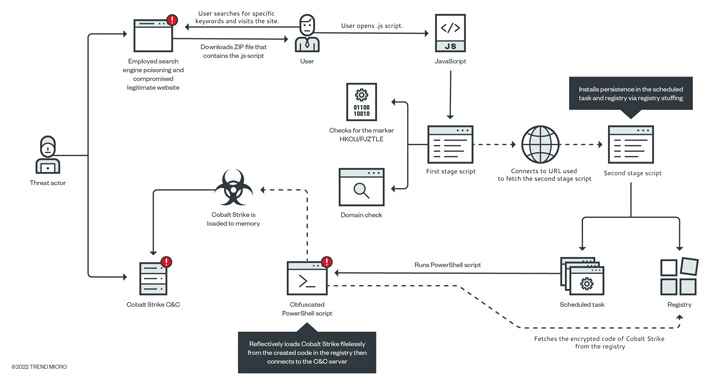
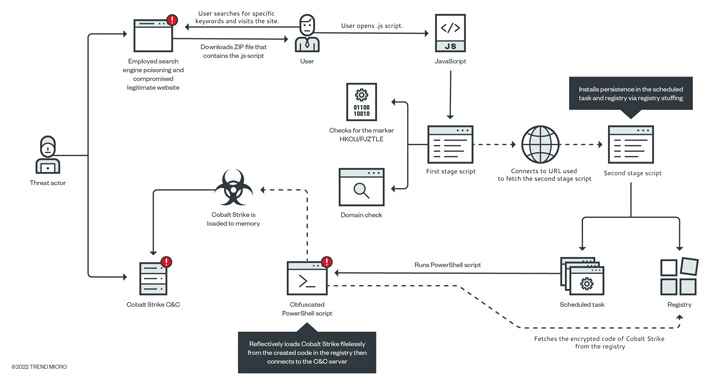
5.0KMalwareGootkit Loader Resurfaces with Updated Tactic to Compromise Targeted Computers
The operators of the Gootkit access-as-a-service (AaaS) malware have resurfaced with updated techniques to compromise unsuspecting victims. “In the past, Gootkit used...
-

 4.7KMalware
4.7KMalwareMicrosoft Links Raspberry Robin USB Worm to Russian Evil Corp Hackers
Microsoft on Friday disclosed a potential connection between the Raspberry Robin USB-based worm and an infamous Russian cybercrime group tracked as Evil...
-
 2.3KMalware
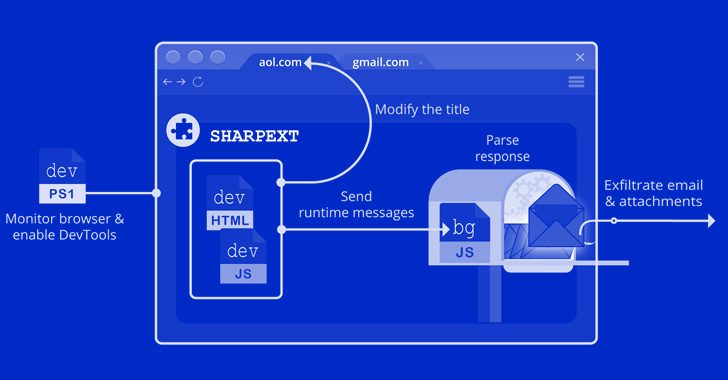
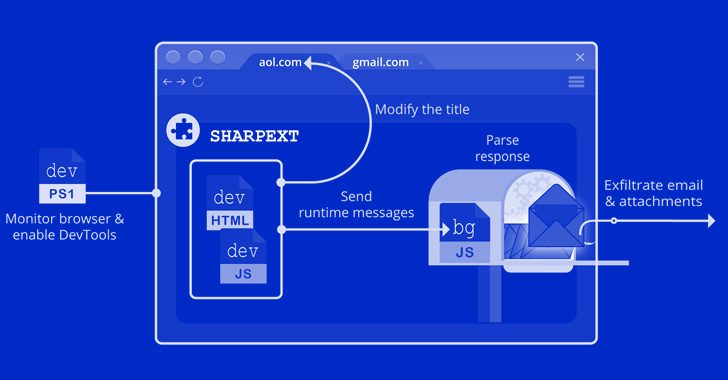
2.3KMalwareNorth Korean Hackers Using Malicious Browser Extension to Spy on Email Accounts
A threat actor operating with interests aligned with North Korea has been deploying a malicious extension on Chromium-based web browsers that’s capable...
-
 985Cyber Attack
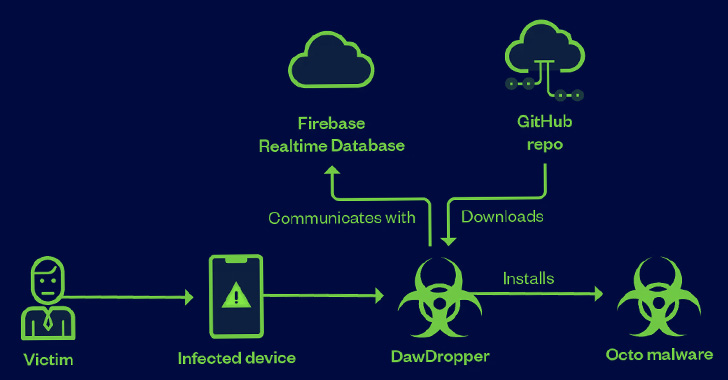
985Cyber AttackOver a Dozen Android Apps on Google Play Store Caught Dropping Banking Malware
A malicious campaign leveraged seemingly innocuous Android dropper apps on the Google Play Store to compromise users’ devices with banking malware. These...
-

 716Malware
716MalwareSpanish Police Arrest 2 Nuclear Power Workers for Cyberattacking the Radiation Alert System
Spanish law enforcement officials have announced the arrest of two individuals in connection with a cyberattack on the country’s radioactivity alert network...
-

 3.3KMalware
3.3KMalwareMicrosoft Uncovers Austrian Company Exploiting Windows and Adobe Zero-Day Exploits
A cyber mercenary that “ostensibly sells general security and information analysis services to commercial customers” used several Windows and Adobe zero-day exploits...
-

 2.4KMalware
2.4KMalwareThese 28+ Android Apps with 10 Million Downloads from the Play Store Contain Malware
As many as 30 malicious Android apps with cumulative downloads of nearly 10 million have been found on the Google Play Store...
-
 3.8KMalware
3.8KMalwareExperts Find Similarities Between New LockBit 3.0 and BlackMatter Ransomware
Cybersecurity researchers have reiterated similarities between the latest iteration of the LockBit ransomware and BlackMatter, a rebranded variant of the DarkSide ransomware...






