All posts tagged "hacking news"
-

 691Malware
691MalwareThe Ultimate Security Blind Spot You Don’t Know You Have
How much time do developers spend actually writing code? According to recent studies, developers spend more time maintaining, testing and securing existing...
-

 946Cyber Attack
946Cyber AttackInfra Used in Cisco Hack Also Targeted Workforce Management Solution
The attack infrastructure used to target Cisco in the May 2022 incident was also employed against an attempted compromise of an unnamed...
-

 4.5KVulnerabilities
4.5KVulnerabilitiesApple Releases iOS Update for Older iPhones to Fix Actively Exploited Vulnerability
Apple on Wednesday backported security updates to older iPhones, iPads, and iPod touch devices to address a critical security flaw that has...
-

 843Malware
843MalwareChinese Hackers Used ScanBox Framework in Recent Cyber Espionage Attacks
A months-long cyber espionage campaign undertaken by a Chinese nation-state group targeted several entities with reconnaissance malware so as to glean information...
-
 750Malware
750MalwareNew Golang-based ‘Agenda Ransomware’ Can Be Customized For Each Victim
A new ransomware strain written in Golang dubbed “Agenda” has been spotted in the wild, targeting healthcare and education entities in Indonesia,...
-

 1.0KMalware
1.0KMalwareCybercrime Groups Increasingly Adopting Sliver Command-and-Control Framework
Nation-state threat actors are increasingly adopting and integrating the Sliver command-and-control (C2) framework in their intrusion campaigns as a replacement for Cobalt...
-
 5.0KCyber Attack
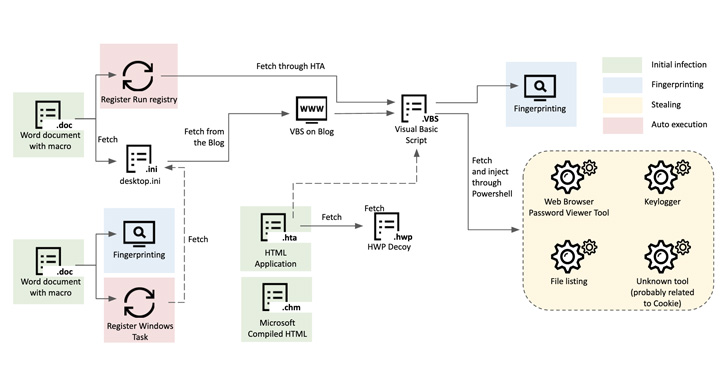
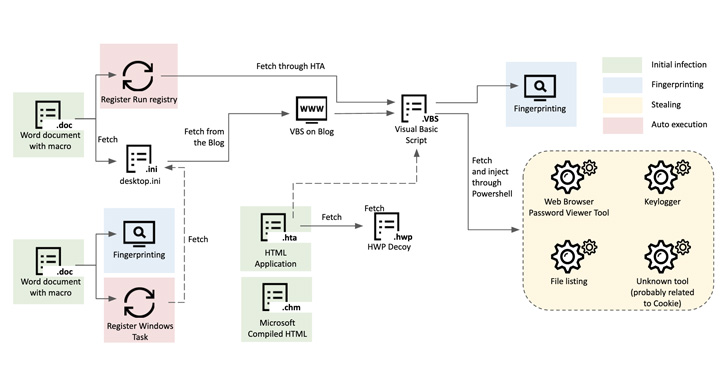
5.0KCyber AttackResearchers Uncover Kimusky Infra Targeting South Korean Politicians and Diplomats
The North Korean nation-state group Kimusky has been linked to a new set of malicious activities directed against political and diplomatic entities...
-

 2.8KMalware
2.8KMalwareCrypto Miners Using Tox P2P Messenger as Command and Control Server
Threat actors have begun to use the Tox peer-to-peer instant messaging service as a command-and-control method, marking a shift from its earlier...
-

 3.0KCyber Attack
3.0KCyber AttackThe Rise of Data Exfiltration and Why It Is a Greater Risk Than Ransomware
Ransomware is the de facto threat organizations have faced over the past few years. Threat actors were making easy money by exploiting...
-

 3.2KVulnerabilities
3.2KVulnerabilities“As Nasty as Dirty Pipe” — 8 Year Old Linux Kernel Vulnerability Uncovered
Details of an eight-year-old security vulnerability in the Linux kernel have emerged that the researchers say is “as nasty as Dirty Pipe.”...
-
 944Malware
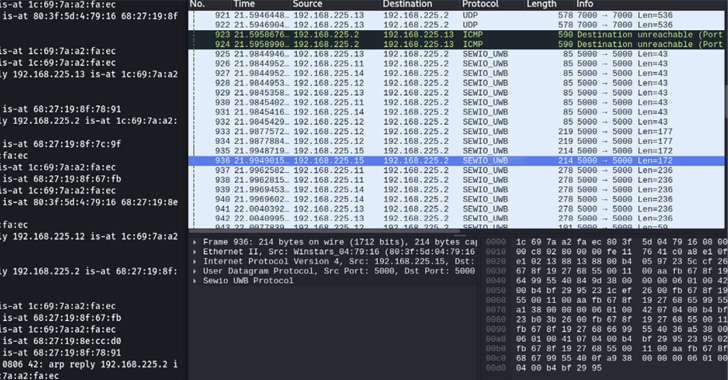
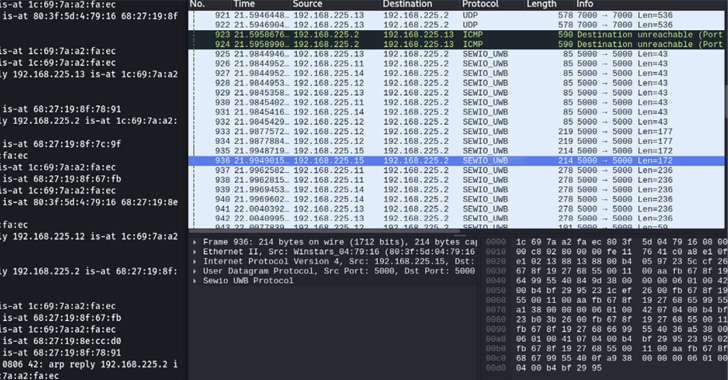
944MalwareRTLS Systems Found Vulnerable to MiTM Attacks and Location Tampering
Researchers have disclosed multiple vulnerabilities impacting Ultra-wideband (UWB) Real-time Locating Systems (RTLS), enabling threat actors to launch adversary-in-the-middle (AitM) attacks and tamper...
-
 4.2KMalware
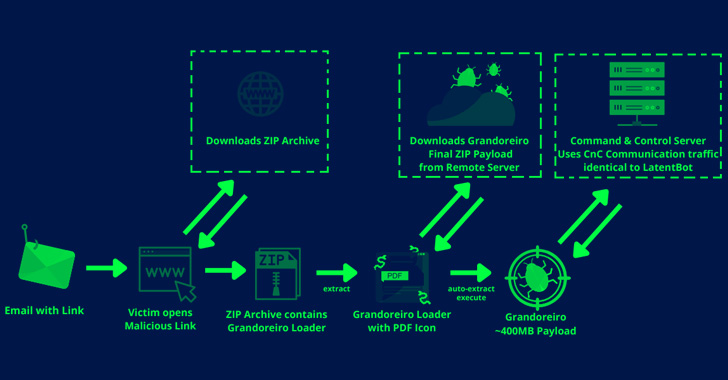
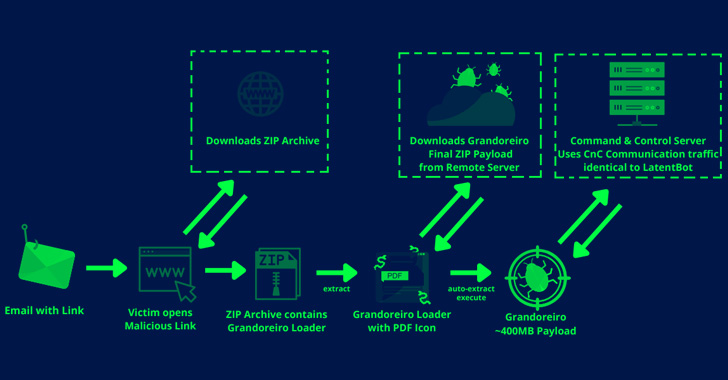
4.2KMalwareNew Grandoreiro Banking Malware Campaign Targeting Spanish Manufacturers
Organizations in the Spanish-speaking nations of Mexico and Spain are in the crosshairs of a new campaign designed to deliver the Grandoreiro...
-

 3.8KMalware
3.8KMalwareDoNot Team Hackers Updated its Malware Toolkit with Improved Capabilities
The Donot Team threat actor has updated its Jaca Windows malware toolkit with improved capabilities, including a revamped stealer module designed to...
-

 2.5KMalware
2.5KMalwareCybercrime Group TA558 Targeting Hospitality, Hotel, and Travel Organizations
A financially motivated cybercrime group has been linked to an ongoing wave of attacks aimed at hospitality, hotel, and travel organizations in...
-

 2.1KMalware
2.1KMalwareCybercriminals Developing BugDrop Malware to Bypass Android Security Features
In a sign that malicious actors continue to find ways to work around Google Play Store security protections, researchers have spotted a...
-

 4.8KMalware
4.8KMalwareMalicious Browser Extensions Targeted Over a Million Users So Far This Year
More than 1.31 million users attempted to install malicious or unwanted web browser extensions at least once, new findings from cybersecurity firm...
-
 776Malware
776MalwareSOVA Android Banking Trojan Returns With New Capabilities and Targets
The SOVA Android banking trojan is continuing to be actively developed with upgraded capabilities to target no less than 200 mobile applications,...
-

 4.7KData Breach
4.7KData BreachTornado Cash Developer Arrested After U.S. Sanctions the Cryptocurrency Mixer
Dutch authorities on Friday announced the arrest of a software developer in Amsterdam who is alleged to be working for Tornado Cash,...
-

 4.8KMalware
4.8KMalwareChinese Hackers Backdoored MiMi Chat App to Target Windows, Linux, macOS Users
A pair of reports from cybersecurity firms SEKOIA and Trend Micro sheds light on a new campaign undertaken by a Chinese threat...
-

 4.4KVulnerabilities
4.4KVulnerabilitiesResearchers Warn of Ongoing Mass Exploitation of Zimbra RCE Vulnerability
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added two flaws to its Known Exploited Vulnerabilities Catalog, citing evidence of...
-
 645Malware
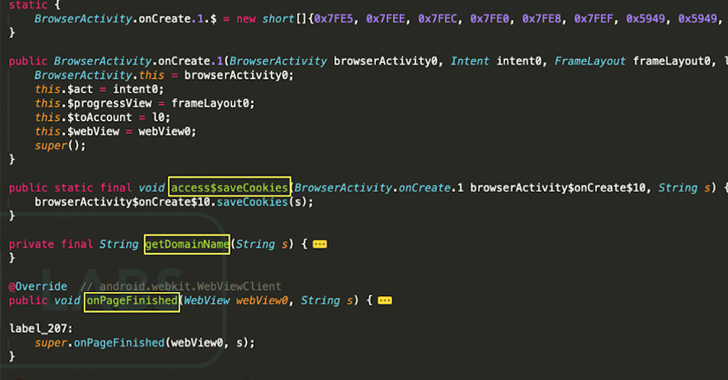
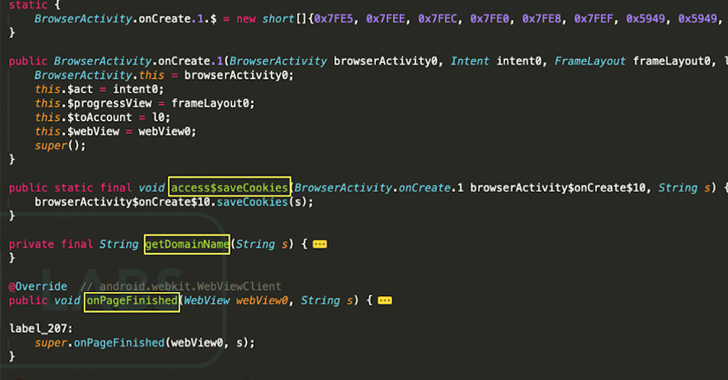
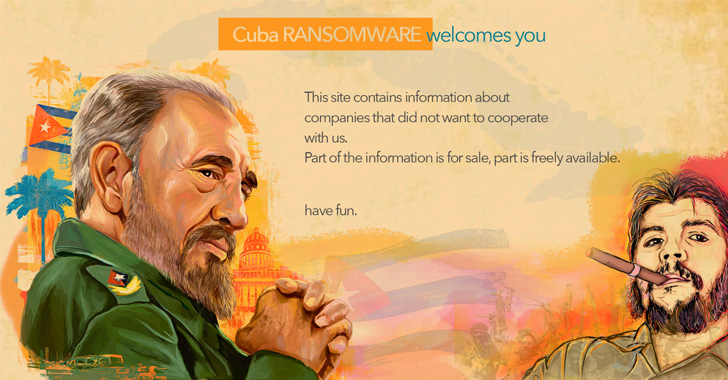
645MalwareHackers Behind Cuba Ransomware Attacks Using New RAT Malware
Threat actors associated with the Cuba ransomware have been linked to previously undocumented tactics, techniques and procedures (TTPs), including a new remote...






