All posts tagged "hacking news"
-
 1.0KMalware
1.0KMalwareTraffic Exchange Networks Distributing Malware Disguised as Cracked Software
An ongoing campaign has been found to leverage a network of websites acting as a “dropper as a service” to deliver a...
-
 4.1KCyber Attack
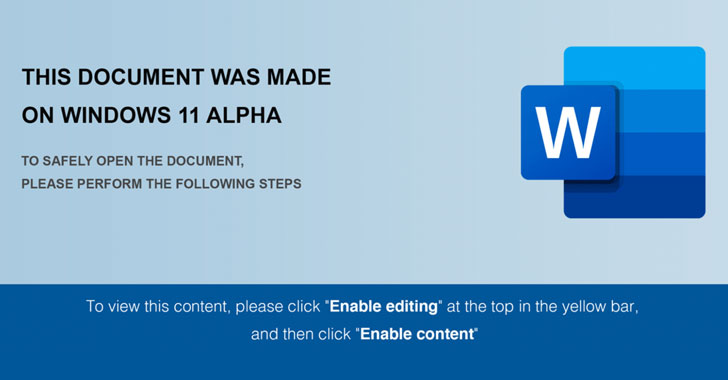
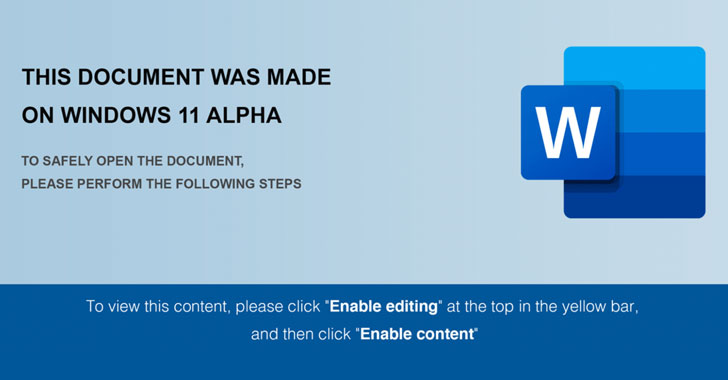
4.1KCyber AttackFIN7 Hackers Using Windows 11 Themed Documents to Drop Javascript Backdoor
A recent wave of spear-phishing campaigns leveraged weaponized Windows 11 Alpha-themed Word documents with Visual Basic macros to drop malicious payloads, including...
-
 4.8KMalware
4.8KMalwareChinese Authorities Arrest Hackers Behind Mozi IoT Botnet Attacks
The operators of the Mozi IoT botnet have been taken into custody by Chinese law enforcement authorities, nearly two years after the...
-
 1.3KCyber Attack
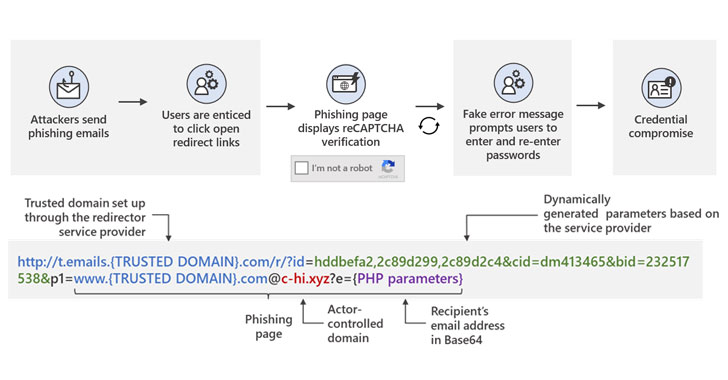
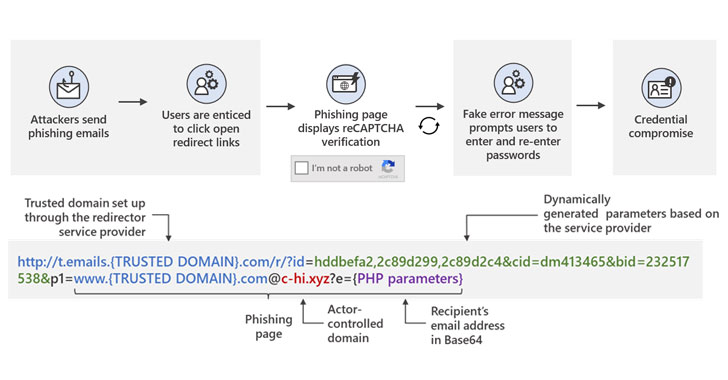
1.3KCyber AttackMicrosoft Warns of Widespread Phishing Attacks Using Open Redirects
Microsoft is warning of a widespread credential phishing campaign that leverages open redirector links in email communications as a vector to trick...
-
 801Malware
801MalwareResearchers Uncover FIN8’s New Backdoor Targeting Financial Institutions
A financially motivated threat actor notorious for setting its sights on retail, hospitality, and entertainment industries has been observed deploying a completely...
-

 3.6KData Breach
3.6KData BreachResearchers Detail Modus Operandi of ShinyHunters Cyber Crime Group
ShinyHunters, a notorious cybercriminal underground group that’s been on a data breach spree since last year, has been observed searching companies’ GitHub...
-

 4.5KCyber Attack
4.5KCyber AttackShadowPad Malware is Becoming a Favorite Choice of Chinese Espionage Groups
ShadowPad, an infamous Windows backdoor that allows attackers to download further malicious modules or steal data, has been put to use by...
-

 1.7KMalware
1.7KMalwareResearchers Find New Evidence Linking Diavol Ransomware to TrickBot Gang
Cybersecurity researchers have disclosed details about an early development version of a nascent ransomware strain called Diavol that has been linked to...
-

 3.5KVulnerabilities
3.5KVulnerabilitiesUnpatched Remote Hacking Flaw Disclosed in Fortinet’s FortiWeb WAF
Details have emerged about a new unpatched security vulnerability in Fortinet’s web application firewall (WAF) appliances that could be abused by a...
-
 4.6KMalware
4.6KMalwareNew AdLoad Variant Bypasses Apple’s Security Defenses to Target macOS Systems
A new wave of attacks involving a notorious macOS adware family has evolved to leverage around 150 unique samples in the wild...
-
 3.8KCyber Attack
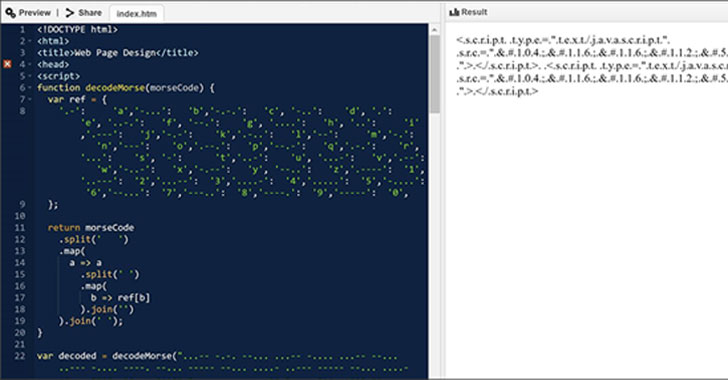
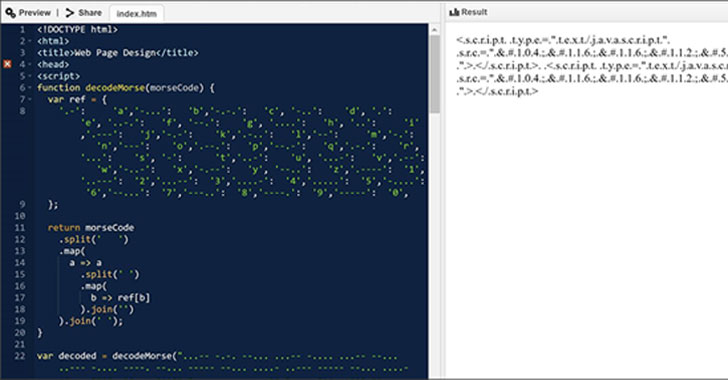
3.8KCyber AttackHackers Spotted Using Morse Code in Phishing Attacks to Evade Detection
Microsoft has disclosed details of an evasive year-long social engineering campaign wherein the operators kept changing their obfuscation and encryption mechanisms every...
-
 3.5KCyber Attack
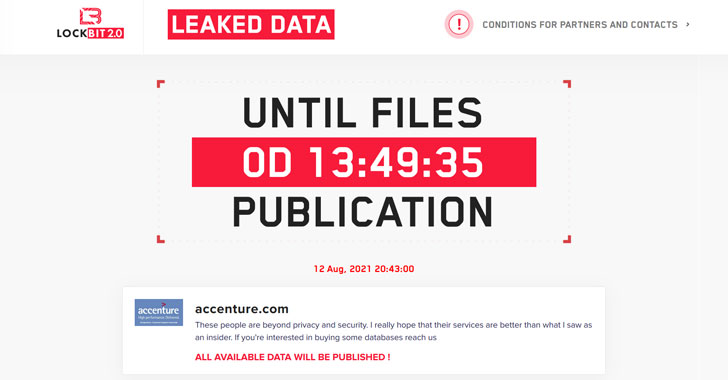
3.5KCyber AttackIT Giant Accenture Hit by LockBit Ransomware; Hackers Threaten to Leak Data
Global IT consultancy giant Accenture has become the latest company to be hit by the LockBit ransomware gang, according to a post...
-

 5.3KCyber Attack
5.3KCyber AttackHackers Steal Over $600 Million Worth of Cryptocurrencies from Poly Network
Hackers have siphoned $611 million worth of cryptocurrencies from a blockchain-based financial network in what’s believed to be one of the largest...
-

 4.0KMalware
4.0KMalwarePulse Secure VPNs Get New Urgent Update for Poorly Patched Critical Flaw
Pulse Secure has shipped a fix for a critical post-authentication remote code execution (RCE) vulnerability in its Connect Secure virtual private network...
-

 1.9KMalware
1.9KMalwareNew Amazon Kindle Bug Could’ve Let Attackers Hijack Your eBook Reader
Amazon earlier this April addressed a critical vulnerability in its Kindle e-book reader platform that could have been potentially exploited to take...
-

 3.6KMalware
3.6KMalwareChinese Hackers Target Major Southeast Asian Telecom Companies
Three distinct clusters of malicious activities operating on behalf of Chinese state interests have staged a series of attacks to target networks...
-

 1.4KMalware
1.4KMalwareSolarmarker InfoStealer Malware Once Again Making its Way Into the Wild
Healthcare and education sectors are the frequent targets of a new surge in credential harvesting activity from what’s a “highly modular” .NET-based...
-

 2.3KMalware
2.3KMalwareExperts Uncover Several C&C Servers Linked to WellMess Malware
Cybersecurity researchers on Friday unmasked new command-and-control (C2) infrastructure belonging to the Russian threat actor tracked as APT29, aka Cozy Bear, that...
-

 1.5KMalware
1.5KMalwareSeveral Malicious Typosquatted Python Libraries Found On PyPI Repository
As many as eight Python packages that were downloaded more than 30,000 times have been removed from the PyPI portal for containing...
-

 989Cyber Attack
989Cyber AttackA New Wiper Malware Was Behind Recent Cyberattack On Iranian Train System
A cyber attack that derailed websites of Iran’s transport ministry and its national railway system earlier this month, causing widespread disruptions in...
-

 5.4KMalware
5.4KMalwarePhony Call Centers Tricking Users Into Installing Ransomware and Data-Stealers
An ongoing malicious campaign that employs phony call centers has been found to trick victims into downloading malware capable of data exfiltration...






