All posts tagged "hacking news"
-
 4.9KMalware
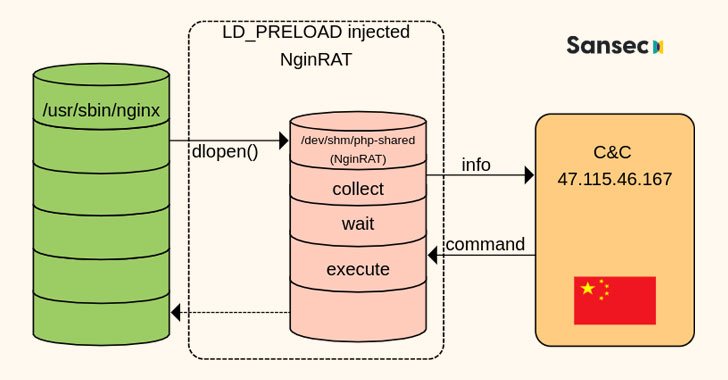
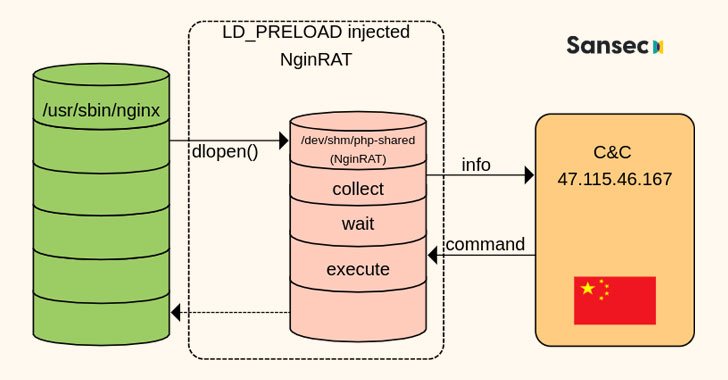
4.9KMalwareNew Payment Data Stealing Malware Hides in Nginx Process on Linux Servers
E-commerce platforms in the U.S., Germany, and France have come under attack from a new form of malware that targets Nginx servers...
-

 3.6KVulnerabilities
3.6KVulnerabilitiesCISA Warns of Actively Exploited Critical Zoho ManageEngine ServiceDesk Vulnerability
The U.S. Federal Bureau of Investigation (FBI) and the Cybersecurity and Infrastructure Security Agency (CISA) are warning of active exploitation of a...
-

 3.2KMalware
3.2KMalwareResearches Detail 17 Malicious Frameworks Used to Attack Air-Gapped Networks
Four different malicious frameworks designed to attack air-gapped networks were detected in the first half of 2020 alone, bringing the total number...
-

 2.3KData Breach
2.3KData BreachPanasonic Suffers Data Breach After Hackers Hack Into Its Network
Japanese consumer electronics giant Panasonic has disclosed a security breach wherein an unauthorized third-party broke into its network and potentially accessed data...
-
 577Cyber Attack
577Cyber AttackWIRTE Hacker Group Targets Government, Law, Financial Entities in Middle East
Government, diplomatic entities, military organizations, law firms, and financial institutions primarily located in the Middle East have been targeted as part of...
-

 832Malware
832MalwareNew Chinotto Spyware Targets North Korean Defectors, Human Rights Activists
North Korean defectors, journalists who cover North Korea-related news, and entities in South Korea are being zeroed in on by a nation-state-sponsored...
-

 766Malware
766MalwareHackers Using Compromised Google Cloud Accounts to Mine Cryptocurrency
Threat actors are exploiting improperly-secured Google Cloud Platform (GCP) instances to download cryptocurrency mining software to the compromised systems as well as...
-
 3.1KMalware
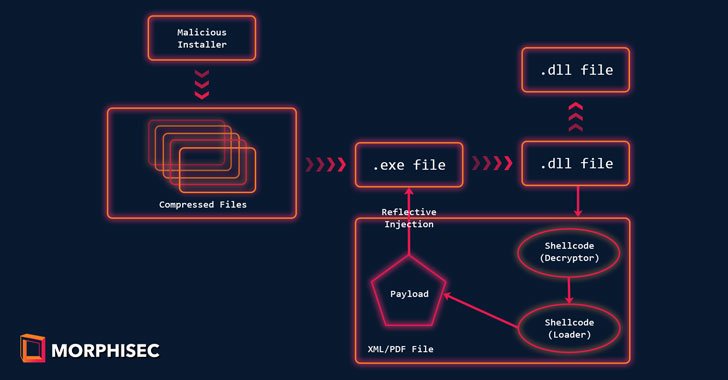
3.1KMalwareCrypto Hackers Using Babadeda Crypter to Make Their Malware Undetectable
A new malware campaign has been discovered targeting cryptocurrency, non-fungible token (NFT), and DeFi aficionados through Discord channels to deploy a crypter...
-

 1.2KMalware
1.2KMalwareCronRAT: A New Linux Malware That’s Scheduled to Run on February 31st
Researchers have unearthed a new remote access trojan (RAT) for Linux that employs a never-before-seen stealth technique that involves masking its malicious...
-
 4.1KMalware
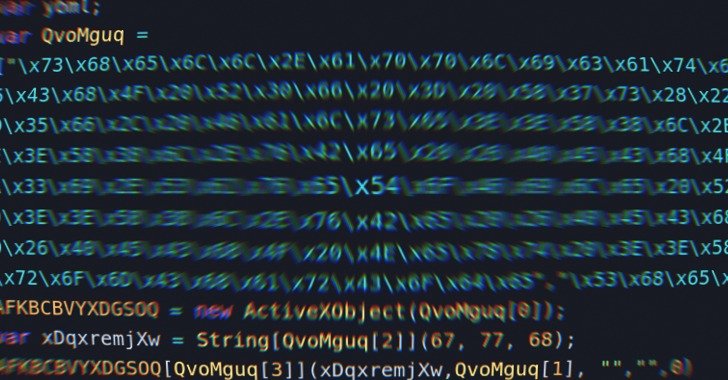
4.1KMalwareThis New Stealthy JavaScript Loader Infecting Computers with Malware
Threat actors have been found using a previously undocumented JavaScript malware strain that functions as a loader to distribute an array of...
-

 2.5KMalware
2.5KMalwareNew Golang-based Linux Malware Targeting eCommerce Websites
Weaknesses in e-commerce portals are being exploited to deploy a Linux backdoor as well as a credit card skimmer that’s capable of...
-
 3.1KMalware
3.1KMalwareRedCurl Corporate Espionage Hackers Return With Updated Hacking Tools
A corporate cyber-espionage hacker group has resurfaced after a seven-month hiatus with new intrusions targeting four companies this year, including one of...
-

 438Malware
438Malware11 Malicious PyPI Python Libraries Caught Stealing Discord Tokens and Installing Shells
Cybersecurity researchers have uncovered as many as 11 malicious Python packages that have been cumulatively downloaded more than 41,000 times from the...
-

 3.5KData Breach
3.5KData BreachA Simple 5-Step Framework to Minimize the Risk of a Data Breach
Today’s businesses run on data. They collect it from customers at every interaction, and they use it to improve efficiency, increase their...
-
 4.7KMalware
4.7KMalwareExperts Expose Secrets of Conti Ransomware Group That Made 25 Million from Victims
The clearnet and dark web payment portals operated by the Conti ransomware group have gone down in what appears to be an...
-
 2.1KMalware
2.1KMalwareNotorious Emotet Botnet Makes a Comeback with the Help of TrickBot Malware
The notorious Emotet malware is staging a comeback of sorts nearly 10 months after a coordinated law enforcement operation dismantled its command-and-control...
-
 4.1KMalware
4.1KMalwareNew ‘Moses Staff’ Hacker Group Targets Israeli Companies With Destructive Attacks
A new politically-motivated hacker group named “Moses Staff” has been linked to a wave of targeted attacks targeting Israeli organizations since September...
-
 2.5KMalware
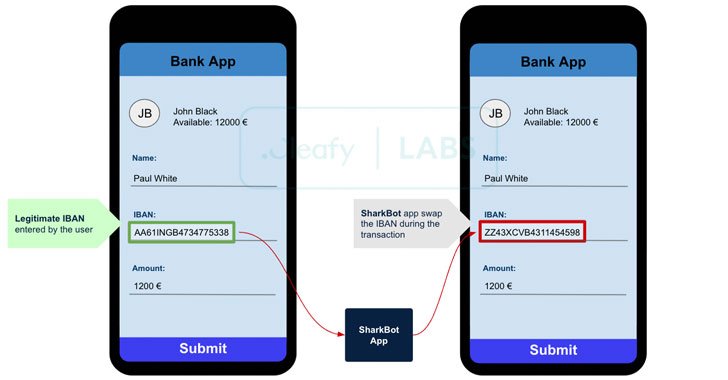
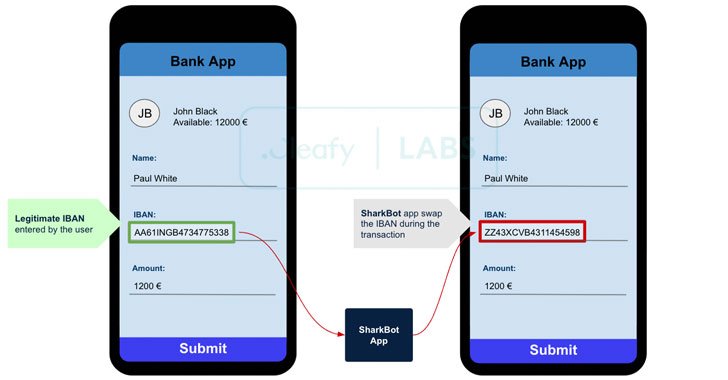
2.5KMalwareSharkBot — A New Android Trojan Stealing Banking and Cryptocurrency Accounts
Cybersecurity researchers on Monday took the wraps off a new Android trojan that takes advantage of accessibility features on mobile devices to...
-
 1.8KCyber Attack
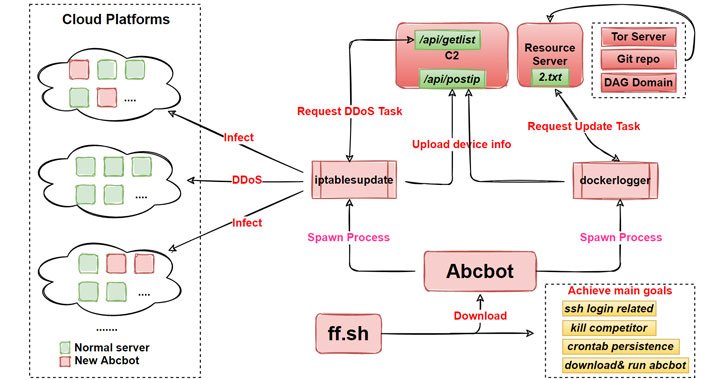
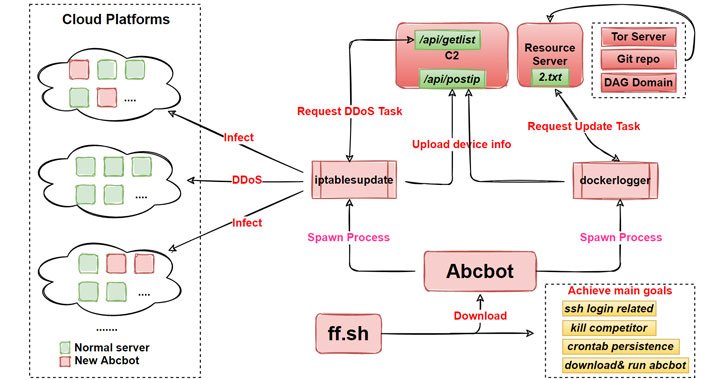
1.8KCyber AttackAbcbot — A New Evolving Wormable Botnet Malware Targeting Linux
Researchers from Qihoo 360’s Netlab security team have released details of a new evolving botnet called “Abcbot” that has been observed in...
-
 1.7KMalware
1.7KMalwareHackers Exploit macOS Zero-Day to Hack Hong Kong Users with new Implant
Google researchers on Thursday disclosed that it found a watering hole attack in late August exploiting a now-patched zero-day in macOS operating...
-
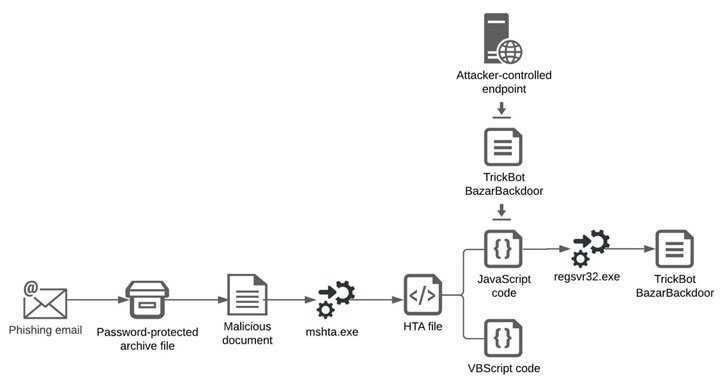
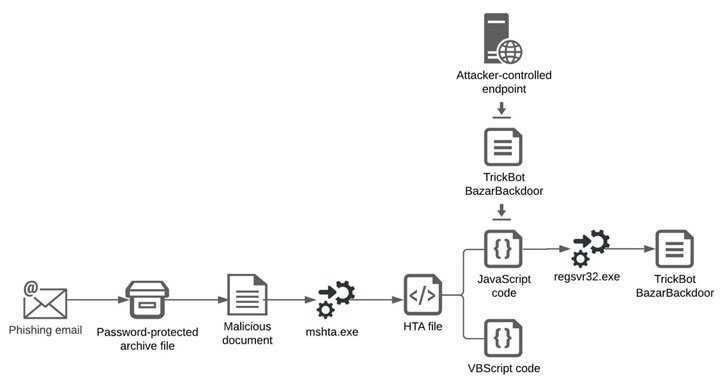 3.7KMalware
3.7KMalwareTrickBot Operators Partner with Shathak Attackers for Conti Ransomware
The operators of TrickBot trojan are collaborating with the Shathak threat group to distribute their wares, ultimately leading to the deployment of...






