All posts tagged "hacking news"
-

 1.8KMalware
1.8KMalwareEmotet Now Using Unconventional IP Address Formats to Evade Detection
Social engineering campaigns involving the deployment of the Emotet malware botnet have been observed using “unconventional” IP address formats for the first...
-

 4.6KMalware
4.6KMalwareGoogle Details Two Zero-Day Bugs Reported in Zoom Clients and MMR Servers
An exploration of zero-click attack surface for the popular video conferencing solution Zoom has yielded two previously undisclosed security vulnerabilities that could...
-
 3.1KCyber Attack
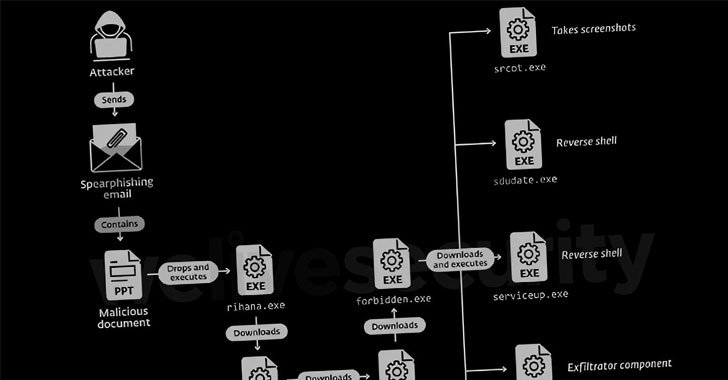
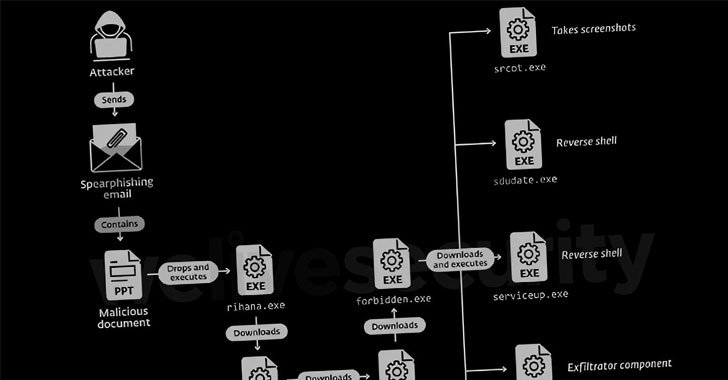
3.1KCyber AttackDoNot Hacking Team Targeting Government and Military Entities in South Asia
A threat actor with potential links to an Indian cybersecurity company has been nothing if remarkably persistent in its attacks against military...
-
 3.2KCyber Attack
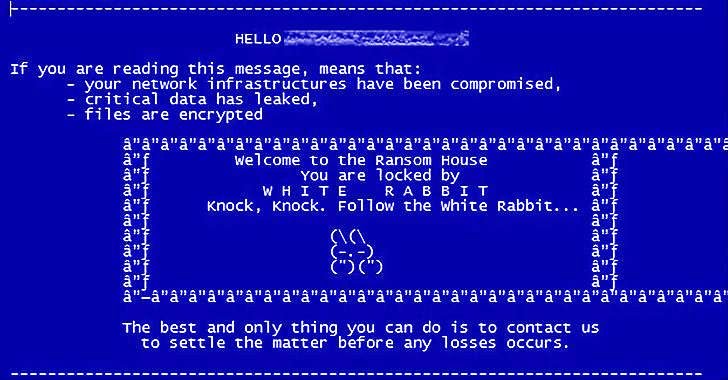
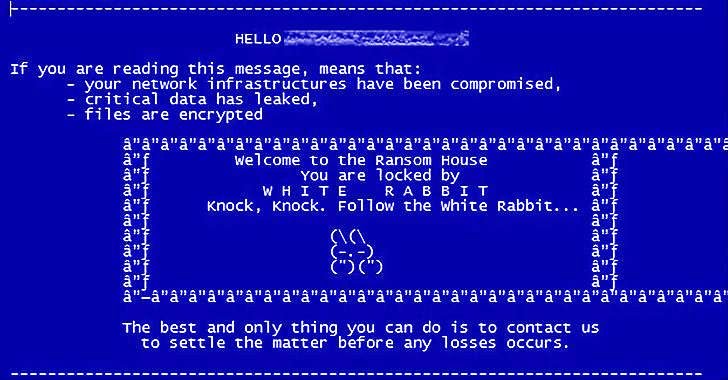
3.2KCyber AttackFIN8 Hackers Spotted Using New ‘White Rabbit’ Ransomware in Recent Attacks
The financially motivated FIN8 actor, in all likelihood, has resurfaced with a never-before-seen ransomware strain called “White Rabbit” that was recently deployed...
-
 596Malware
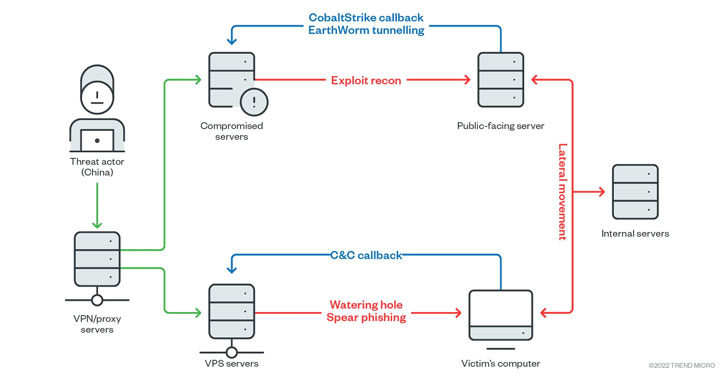
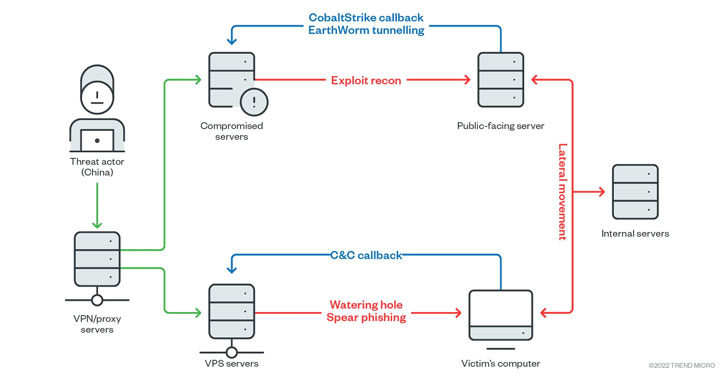
596MalwareEarth Lusca Hackers Aimed at High-Value Targets in Government and Private Sectors
An elusive threat actor called Earth Lusca has been observed striking organizations across the world as part of what appears to be...
-
 2.4KMalware
2.4KMalwareA New Destructive Malware Targeting Ukrainian Government and Business Entities
Cybersecurity teams from Microsoft on Saturday disclosed they identified evidence of a new destructive malware operation targeting government, non-profit, and information technology...
-
 1.4KCyber Attack
1.4KCyber AttackUS Cyber Command Links ‘MuddyWater’ Hacking Group to Iranian Intelligence
The U.S. Cyber Command (USCYBERCOM) on Wednesday officially confirmed MuddyWater’s ties to the Iranian intelligence apparatus, while simultaneously detailing the various tools...
-

 3.2KVulnerabilities
3.2KVulnerabilitiesApple Releases iPhone and iPad Updates to Patch HomeKit DoS Vulnerability
Apple on Wednesday rolled out software updates for iOS and iPadOS to remediate a persistent denial-of-service (DoS) issue affecting the HomeKit smart...
-
 2.8KMalware
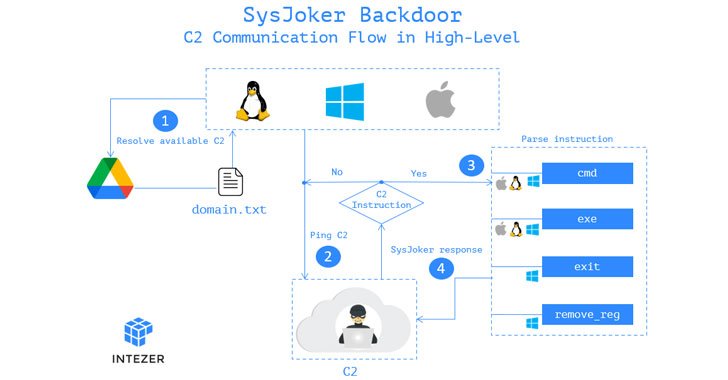
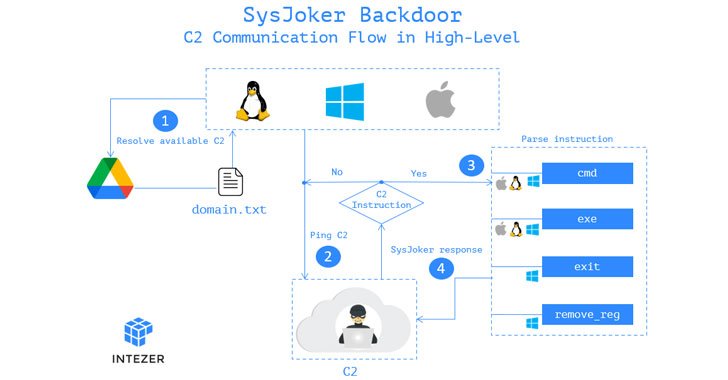
2.8KMalwareNew SysJoker Espionage Malware Targeting Windows, macOS, and Linux Users
A new cross-platform backdoor called “SysJoker” has been observed targeting machines running Windows, Linux, and macOS operating systems as part of an...
-
 1.2KCyber Attack
1.2KCyber AttackFBI, NSA and CISA Warns of Russian Hackers Targeting Critical Infrastructure
Amid renewed tensions between the U.S. and Russia over Ukraine and Kazakhstan, American cybersecurity and intelligence agencies on Tuesday released a joint...
-

 4.9KMalware
4.9KMalwareNorth Korean Hackers Start New Year with Attacks on Russian Foreign Ministry
A North Korean cyberespionage group named Konni has been linked to a series of targeted attacks aimed at the Russian Federation’s Ministry...
-

 5.2KMalware
5.2KMalwareNew Trick Could Let Malware Fake iPhone Shutdown to Spy on Users Secretly
Researchers have disclosed a novel technique by which malware on iOS can achieve persistence on an infected device by faking its shutdown...
-
 3.5KMalware
3.5KMalwareNew Zloader Banking Malware Campaign Exploiting Microsoft Signature Verification
An ongoing ZLoader malware campaign has been uncovered exploiting remote monitoring tools and a nine-year-old flaw concerning Microsoft’s digital signature verification to...
-

 912Malware
912MalwareNew iLOBleed Rootkit Targeting HP Enterprise Servers with Data Wiping Attacks
A previously unknown rootkit has been found setting its sights on Hewlett-Packard Enterprise’s Integrated Lights-Out (iLO) server management technology to carry out...
-

 4.2KCyber Attack
4.2KCyber AttackChinese APT Hackers Used Log4Shell Exploit to Target Academic Institution
A never-before-seen China-based targeted intrusion adversary dubbed Aquatic Panda has been observed leveraging critical flaws in the Apache Log4j logging library as...
-

 765Vulnerabilities
765VulnerabilitiesNew Apache Log4j Update Released to Patch Newly Discovered Vulnerability
The Apache Software Foundation (ASF) on Tuesday rolled out fresh patches to contain an arbitrary code execution flaw in Log4j that could...
-

 2.0KMalware
2.0KMalware‘Spider-Man: No Way Home’ Pirated Downloads Contain Crypto-Mining Malware
Peter Parker might not be a mastermind cryptocurrency criminal, but the name Spiderman is quickly becoming more associated with the mining landscape....
-
 1.3KMalware
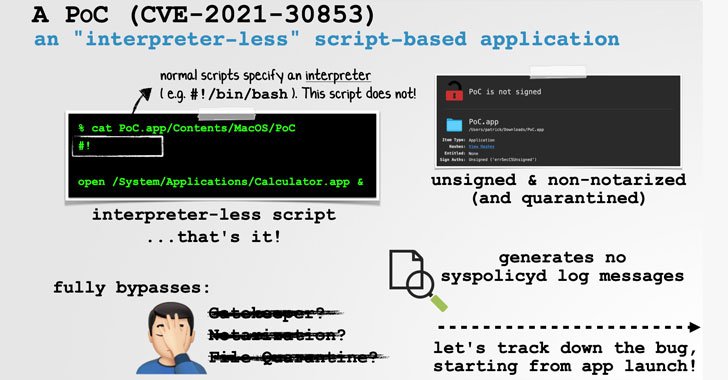
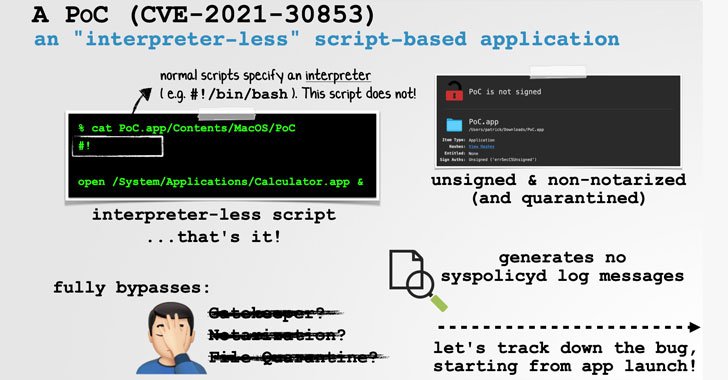
1.3KMalwareExpert Details macOS Bug That Could Let Malware Bypass Gatekeeper Security
Apple recently fixed a security vulnerability in the macOS operating system that could be potentially exploited by a threat actor to “trivially...
-

 2.3KMalware
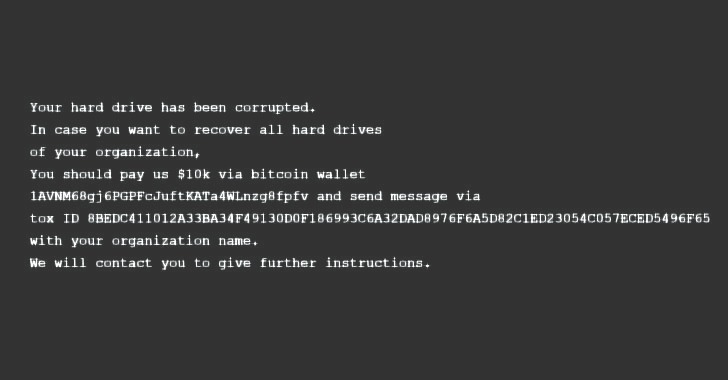
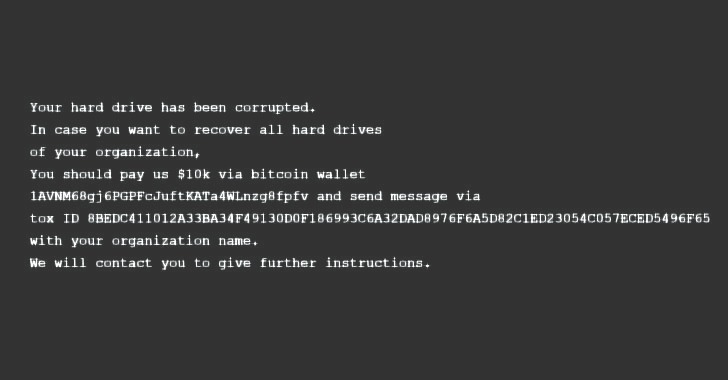
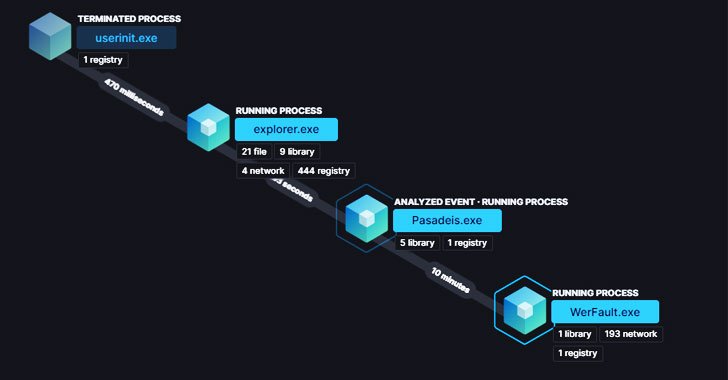
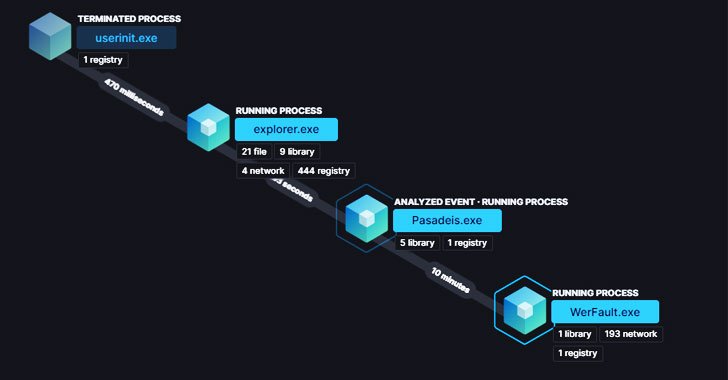
2.3KMalwareNew Ransomware Variants Flourish Amid Law Enforcement Actions
Ransomware groups continue to evolve their tactics and techniques to deploy file-encrypting malware on compromised systems, notwithstanding law enforcement’s disruptive actions against...
-
 1.5KCyber Attack
1.5KCyber AttackNew BLISTER Malware Using Code Signing Certificates to Evade Detection
Cybersecurity researchers have disclosed details of an evasive malware campaign that makes use of valid code signing certificates to sneak past security...
-
 2.5KVulnerabilities
2.5KVulnerabilitiesChina suspends deal with Alibaba for not sharing Log4j 0-day first with the government
China’s internet regulator, the Ministry of Industry and Information Technology (MIIT), has temporarily suspended a partnership with Alibaba Cloud, the cloud computing...






