All posts tagged "kali"
-

 1.5KExploitation Tools
1.5KExploitation ToolsMaskPhish – Give A Mask To Phishing URL
MaskPhish is a simple script to hide phishing URL under a normal looking URL(google.com or facebook.com). Legal Disclaimer: Usage of MaskPhish...
-

 728News
728NewsKali Linux 2019.4 Hacking OS Comes With An Undercover Mode
The Debian-based Linux distribution Kali Linux is getting its final update for this year. Kali Linux 2019.4 is available for download for...
-
 390Geek
390GeekKali Linux 2019.3 Released For Ethical Hacking Enthusiasts
Earlier this year in May, the folks at Offensive Security shipped Kali Linux 2019.2 — the second Kali release of 2019. The...
-
 397News
397NewsKali Linux 2019.2 Released With NetHunter 2019.2 And New Kernel
Offensive Security, the makers of Kali Linux, have shipped their second release in 2019. The new Kali Linux 2019.2 distribution is now...
-

 292Hacking Tools
292Hacking ToolsKali Linux 2019.1 Released
Kali Linux 2019.1 is now available for download, updating many of its features, as well as introducing a few more. These include...
-

 302Pentest Linux Distributions
302Pentest Linux DistributionsKali Linux 2018.4 Release – Penetration Testing and Ethical Hacking Linux Distribution
Welcome to our fourth and final release of 2018, Kali Linux 2018.4, which is available for immediate download. This release brings kernel...
-
 270Information Gathering
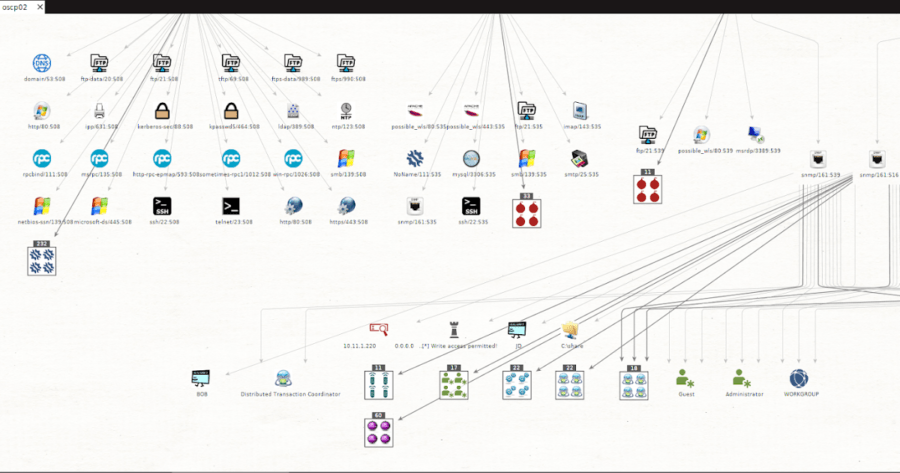
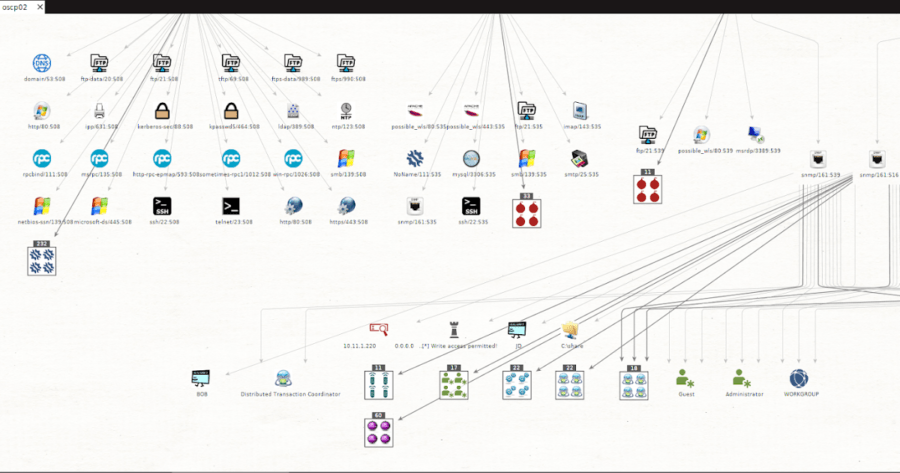
270Information GatheringMsploitego – Pentesting Suite For Maltego Based On Data In A Metasploit Database
msploitego leverages the data gathered in a Metasploit database by enumerating and creating specific entities for services. Services like samba, smtp, snmp,...
-

 237Wireless Attacks
237Wireless AttacksAirba.sh – A POSIX-compliant, Fully Automated WPA PSK Handshake Capture Script Aimed At Penetration Testing
Airbash is a POSIX-compliant, fully automated WPA PSK handshake capture script aimed at penetration testing. It is compatible with Bash and Android...
-
 335Geek
335GeekKali Linux 2018.2 Ethical Hacking Distro Is Here: Download ISO And Torrent Files
Earlier this year in February, Offensive Security pushed the first release snapshot of Kali Linux for the year 2018. The Kali developers...
-
 217Data Security
217Data SecurityHow to do offensive Penetration Testing with Kali?
We will start with the preparation. We will need some basic skills. Even more important than being able to do research, time...
-

 426Geek
426GeekKali Linux For Windows 10 Arrives In Microsoft Store
Installing and running Linux on Windows 10, also called Linux Subsystem on Windows (WSL), is old news. You can already install distros...
-

 240Pentest Linux Distributions
240Pentest Linux DistributionsKali Linux 2018.1 Release – The Best Penetration Testing Distribution
Kali Linux 2018.1 the first release of 2018, this fine release contains all updated packages and bug fixes since our 2017.3 release...
-
 237Exploitation Tools
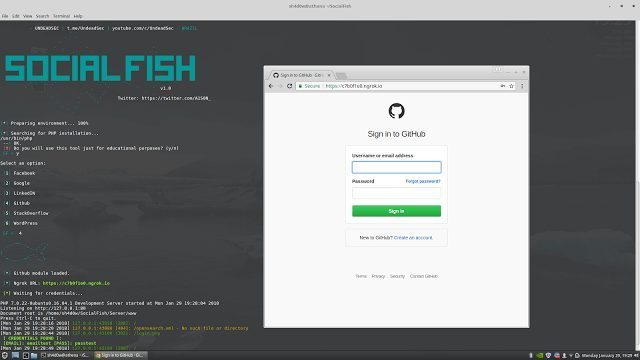
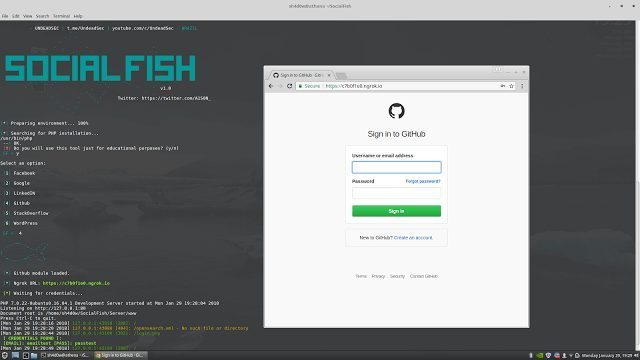
237Exploitation ToolsSocialFish – Ultimate phishing tool with Ngrok integrated
Ultimate phishing tool with Ngrok integrated. PREREQUISITES Python 2.7 Wget from Python PHP TESTED ONKali Linux – ROLLING EDITION CLONE git clone...
-
 238Exploitation Tools
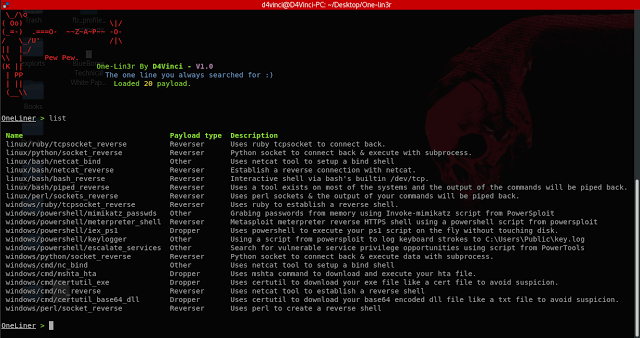
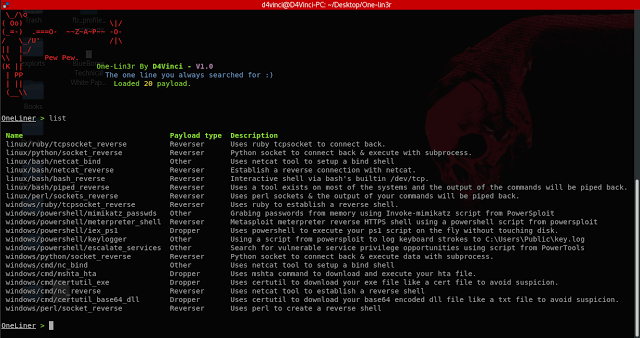
238Exploitation ToolsOne-Lin3r – Gives you One-Liners that Aids in Penetration Testing Operations
One-Lin3r is simple and light-weight framework inspired by the web-delivery module in Metasploit. It consists of various one-liners that aids in penetration...
-
 364Geek
364GeekKali Linux 2017.3 Brings New Hacking Tools — Download ISO And Torrent Files Here
Kali Linux, the leading ethical hacking operating system, is distributed and developed by Offensive Security. In 2016, the developers decided to make...
-
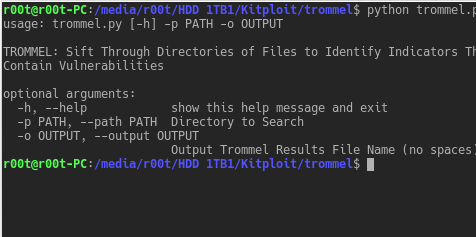
 218Vulnerability Analysis
218Vulnerability AnalysisTROMMEL – Sift Through Directories of Files to Identify Indicators That May Contain Vulnerabilities
TROMMEL sifts through directories of files to identify indicators that may contain vulnerabilities. TROMMEL identifies the following indicators related to: Secure Shell...
-
How To
How to Scan for SMB vulnerabilities using Nmap
Hi there my fellow hackers, we are back with another tutorial. Today we will see how we can use a Nmap script...
-

 281Hacked
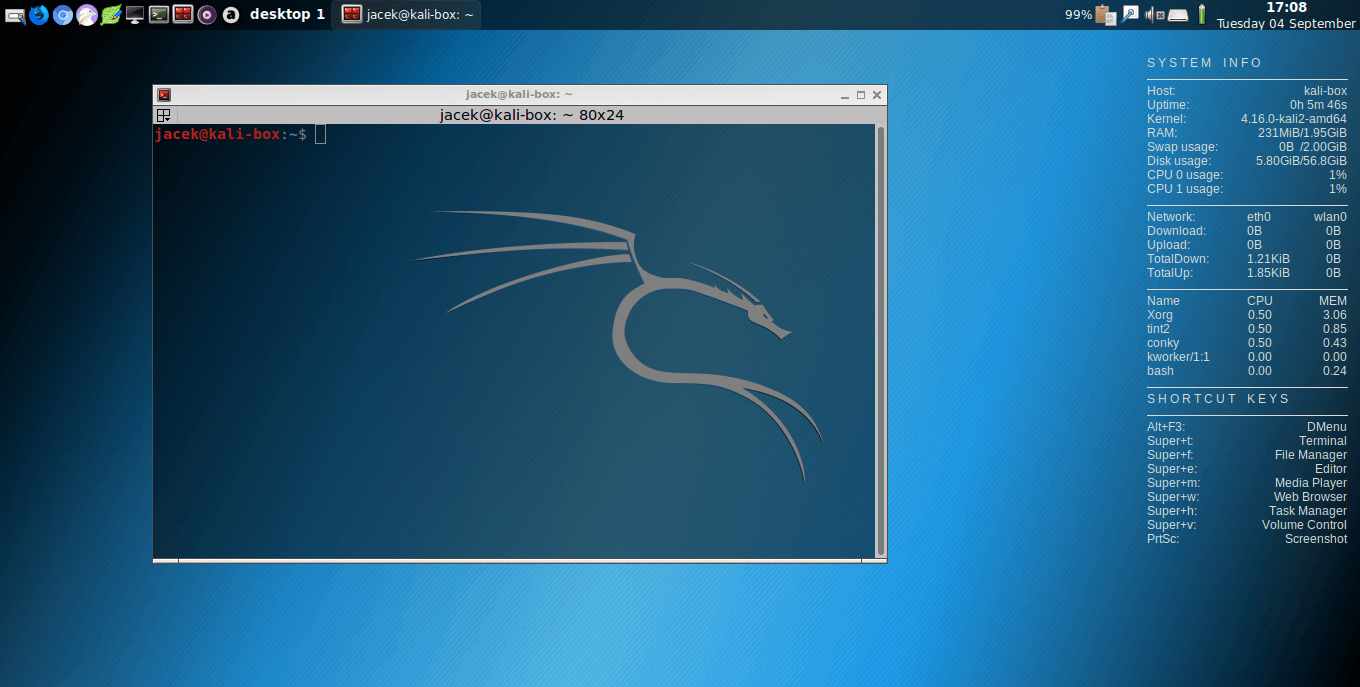
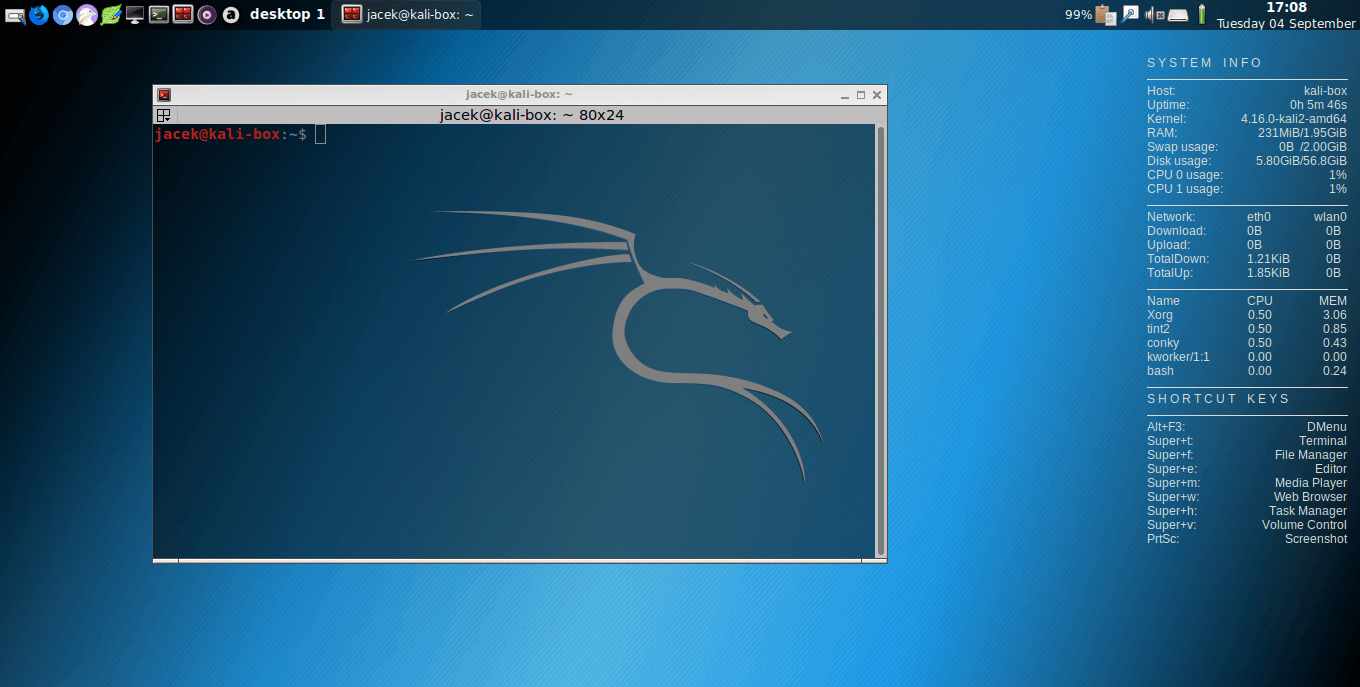
281HackedKali Linux Rolling Release — Best Features That Make It The Best OS For Ethical Hackers
Image | Kali.org Short Bytes: Kali Linux, a hacker’s favorite operating system, is now available with first Rolling release. This release ensures...
-

 222Data Security
222Data SecurityHack Like a Pro: Using Sparta for Reconnaissance
As all of you know, reconnaissance is critical to being successful in a pentest or hack. Recon is where we gather all...
-

 313Vulnerabilities
313VulnerabilitiesHow to Build a Portable Hacking Station with a Raspberry Pi and Kali Linux
Cracking Wi-Fi passwords, spoofing accounts, and testing networks for exploits is all fun enough, but if you want to take the...
-
 254Hacking Tutorials
254Hacking TutorialsReset Windows Password with Kali
Sometimes we forget our password, or even we want to reset the password of the windows OS of our friends, officemate or...






