All posts tagged "malware"
-

 294Geek
294GeekHackers are Exploiting New Microsoft Office Vulnerability to Drop Malware
Researchers have detected a new zero-day bug which uses a previously unknown flaw in Microsoft Word. The bug allows attackers to send malicious document...
-

 184Hacked
184HackedWikileaks Releases “How To Hack Windows” Secret Guide By CIA
Short Bytes: The latest addition to the Vault 7 leak by CIA is the set of 27 documents of the Grasshopper framework....
-

 325Mobile Security
325Mobile SecurityMobile spyware that steal Twitter credentials uses sandbox to Evade antivirus detections
[jpshare]Security Experts from Avast came through a Malware that uses a sandbox(DroidPlugin) to dynamically load and run an app, without actually installing...
-

 245News
245NewsHackers Leak Passwords to NSA’s “Top Secret Arsenal” against Trump’s Policies
You may remember Shadow Brokers hacking group for selling a trove of hacking tools and exploits stolen from the NSA’s Equation Group...
-
 184Malware
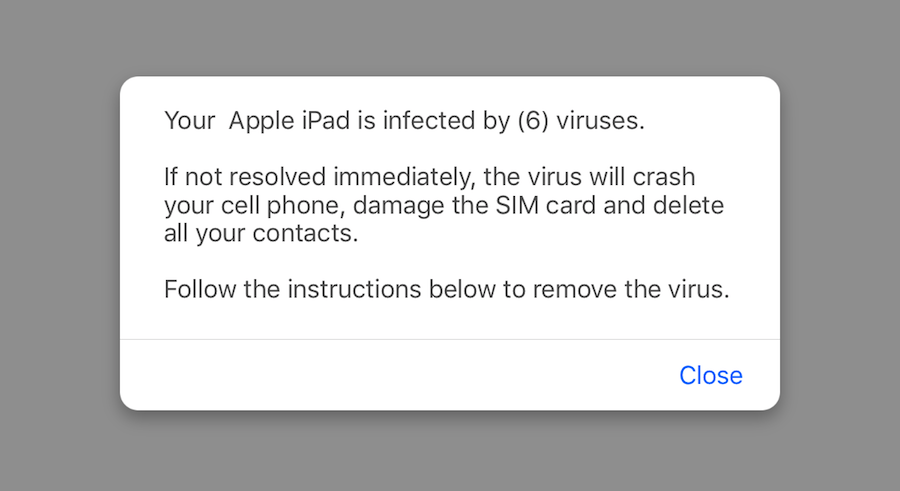
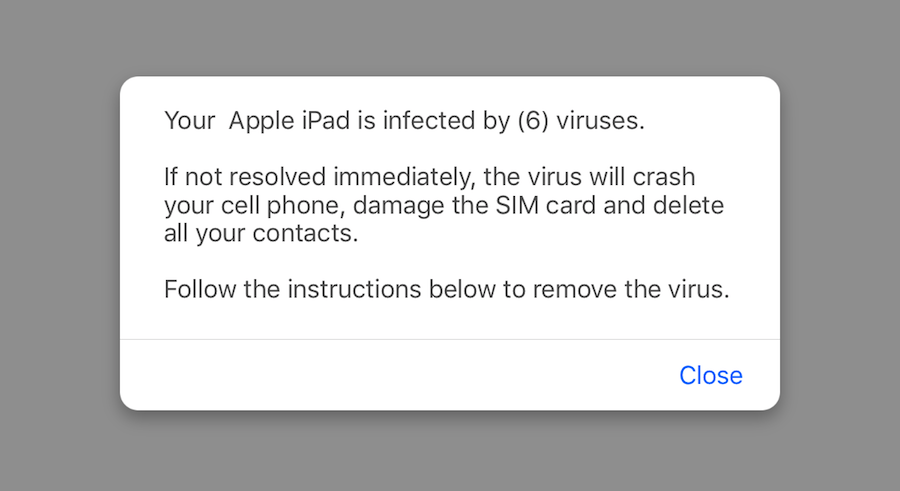
184MalwareMalvertising on iOS pushes eyebrow-raising VPN app
There is a preconceived idea that malvertising mostly affects the Windows platform. Certainly, when it comes to malicious adverts, Internet Explorer is...
-
 348Cyber Events
348Cyber EventsFake News Site Targeting Android, Windows Users with Malware Scam
A group of hackers is performing highly sophisticated cyber-attacks against high-profile organizations of Middle East – Cyber security firms Palo Alto Networks...
-

 159Malware
159MalwareNew Malware Intentionally Bricks IoT Devices
A new malware strain called BrickerBot is bricking Internet of Things (IoT) devices around the world by corrupting their storage capability and...
-
 283Data Security
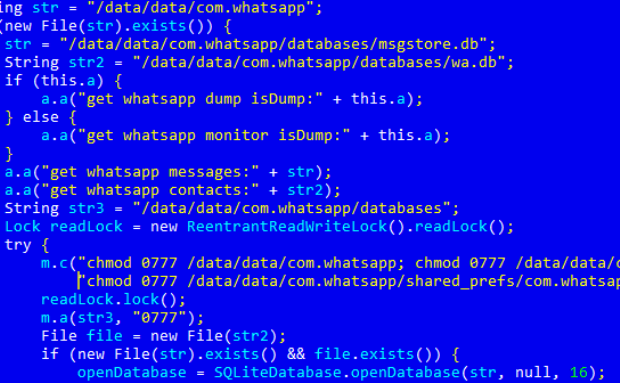
283Data SecurityMeet Pegasus, the Worst Android RAT Malware Created for Targeted Attack
The malware can snoop on people’s conversations, act as keylogger, take screenshots, control camera and microphone. A new Android RAT malware was...
-

 255Data Security
255Data SecuritySkype Users Hit By Fake Flash Player Download Malware Scam
A few days ago Skype users noticed that the instant messaging service served a malicious malware masquerading as fake Flash player update. Several users...
-

 166Hacked
166Hacked“Disappearing Malware” Allowed Hackers Steal $800,000 Cash From Russian ATMs
Short Bytes: A team of researchers at Kaspersky Labs have recently cracked the mystery of a fileless malware that was used to...
-
 179Hacked
179HackedWikileaks’ Most “Technically Damaging” Leak Reveals CIA Source Code That’s Hides Identity Traces From Malware
Short Bytes: Continuing their CIA leak further, Wikileaks has released a part of CIA Core Library called Marble Framework. It is used...
-

 331Geek
331GeekNew Android ransomware proves why antivirus software are a joke
A new ransomware app has been spotted in the wild, which could easily bypass your mobile anti-virus allowing the app to lock...
-
 286Data Security
286Data SecurityData-Stealing Malware ‘Dimnie’ Targeting Developers on Github
A new series of malware attacks has occurred, and this time, the targets are the owners of Github repositories. Developers who own...
-

 155Data Security
155Data SecurityFlatbed Scanners Used as Relay Point for Controlling Malware in Air-Gapped Systems
Scientists from two Israeli universities have come up with a way to use flatbed scanners as relay points when sending commands to...
-
 140Malware
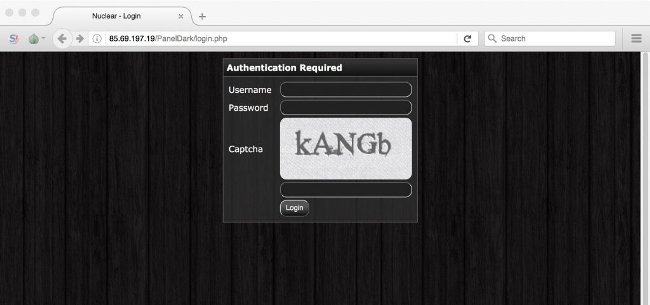
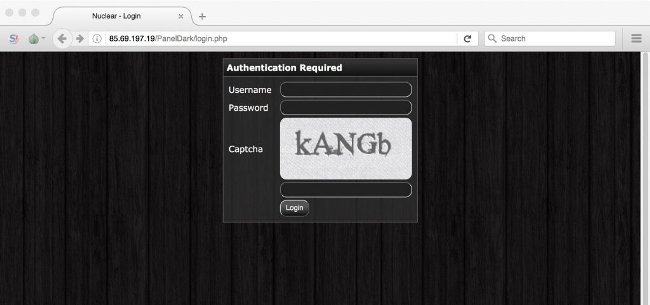
140MalwareHumbled Malware Author Leaks His Own Source Code to Regain Community’s Trust
The author of the Nuclear Bot banking trojan has leaked the source code of his own malware in a desperate attempt to...
-

 284Data Security
284Data SecurityHere’s What a Samsung Galaxy S7 Hacked with Ransomware Looks Like
A couple of months ago we reported about an Android-based LG Smart TV had its screen bricked after a critical ransomware infection....
-

 322Cyber Crime
322Cyber CrimeOnline stores under attack; a new fraudster bot spotted in the wild
Hackers have designed a new bot named Giftghostbot which is being used to defraud thousands of gift card owners. As per reports, these...
-
 156Malware
156MalwareMalvertising Campaign on Adult Sites Spreads Ramnit Trojan
Security researchers from Malwarebytes have discovered a new malvertising campaign targeting visitors of several adult websites, spreading the Ramnit trojan and focusing...
-

 97Malware
97MalwareMost Industrial Control Systems Get Infected with Malware by Accident
The vast majority of malware incidents that take place at industrial facilities around the world are just accidental infections, albeit a very...
-

 144Malware
144MalwareChinese Crooks Use Fake Cellular Telephony Towers to Spread Android Malware
Malware authors in China are using fake base transceiver stations (BTSs), which is equipment usually installed on cellular telephone towers, to send...
-
 182Data Security
182Data SecurityNew Attack Uses Microsoft’s Application Verifier to Hijack Antivirus Software
A new technique named DoubleAgent, discovered by security researchers from Cybellum, allows an attacker to hijack security products and make them take...






