All posts tagged "malware"
-
 203Malware
203MalwareChinese PUPs distributing Backdoored Drivers which affect Windows operating system
PUP(potentially unwanted program) packages that install’s along with Chinese software’s consist of backdoors targeting English speakers. The backdoor was uncovered by Malware...
-

 312Vulnerabilities
312VulnerabilitiesAttackers Leverage Excel, PowerShell and DNS in Latest Non-Malware Attack
Increasingly, cyberattackers have been leveraging “non-malware” attack methods to target vulnerable organizations. Recently, the Carbon Black Threat Research Team was alerted about...
-

 268Hacked
268HackedVirtual and Augmented Reality: Transforming The Way We Look At The Internet and Data Security
Short Bytes: Virtual and Augmented Reality have redefined every aspect of our modern world ranging from gaming, music, and pop culture, to business,...
-

 131Malware
131MalwareRansomware operators are hiding malware deeper in installer packages
We are seeing a wave of new NSIS installers used in ransomware campaigns. These new installers pack significant updates, indicating a collective...
-

 278Malware
278MalwareMajikPOS Dual malware targeting businesses across North America and Canada
A new group of POS malware family made its presence targeting business systems around North America and Canada.The objective of PoS malware...
-

 244Geek
244GeekBeware; 36 Android Devices Shipped with Preinstalled Malware
Android devices have remained the center of attraction for malicious cyber criminals since forever. Not only do they churn out fake, infected...
-

 256Malware
256MalwareHancitor Makes First Appearance in Top Five Most wanted malware – February 2017
Hancitor has grown into the main five of the ‘most wanted’ malware families worldwide for the first time, reported by Checkpoint Threat Intelligence...
-

 124Geek
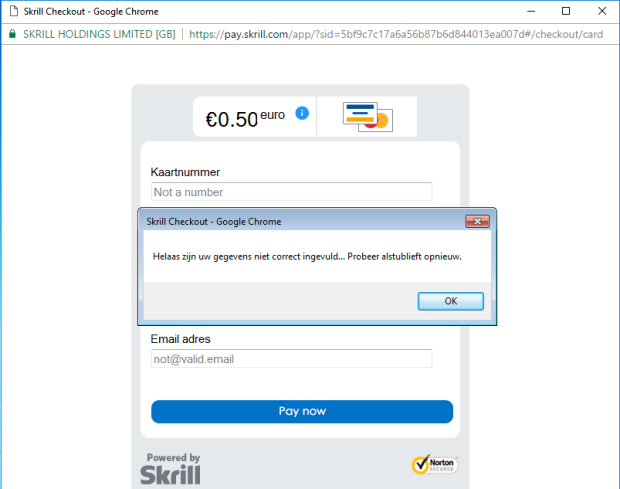
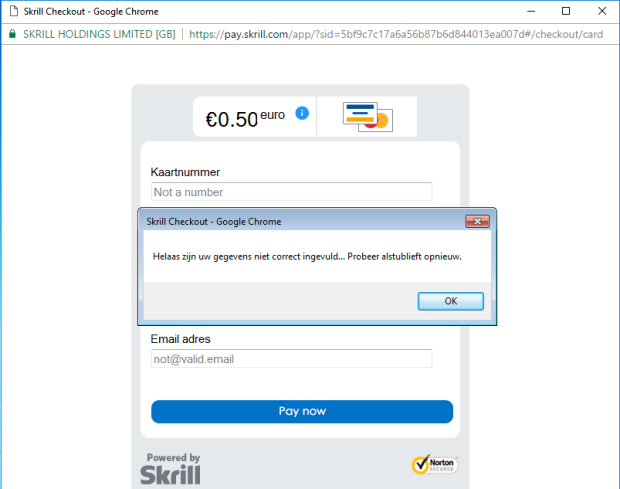
124GeekLatest Google Chrome Scam Aims At Stealing Credit Card Data
Google’s Chrome browser has remained the apple of every hacker’s eyes for more than one reasons, the most important being that it...
-
 166Vulnerabilities
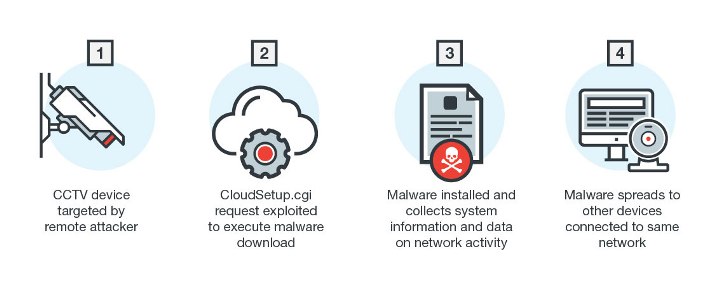
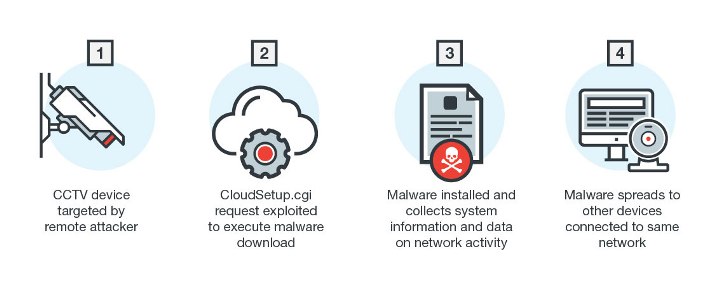
166VulnerabilitiesNew Linux Malware Exploits CGI Vulnerability
Linux has long been the preferred operating system for enterprise platforms and Internet of Things (IoT) manufacturers. Linux-based devices are continually being...
-
 330News
330NewsNotepad++ Issues Fix After CIA Attack Revealed in Vault7 Documents
On 7th Match 2017, the whistle-blowing organization Wikileaks published a series of new documents code-named “Vault 7” allegedly belonging to the U.S. Central Intelligence Agency...
-

 107Malware
107MalwareMalware found preinstalled on 38 Android phones used by 2 companies
Malicious apps were surreptitiously added somewhere along the supply chain. A commercial malware scanner used by businesses has recently detected an outbreak...
-
 162Vulnerabilities
162VulnerabilitiesCredit Card Stealer Disguises as Google Chrome Browser
A new malicious application tries to disguise itself as the Google Chrome browser to fool victims into entering their payment card details....
-

 217Malware
217MalwareMobile security: The reality of malware … augmented
Originally, it was expected that mobile devices would evolve to become handheld computers with capabilities similar to any desktop. It is clear...
-
 113Malware
113MalwareMobile Menace Monday: Facebook Lite infected with Spy FakePlay
A version of the popular mobile app Facebook has been found to be infected with what we detect as Android/Trojan.Spy.FakePlay. Facebook Lite...
-

 516Hacked
516HackedEverything You Need To Know About WikiLeaks’ Release –Windows, iPhone, Linux, Android, Mac, WhatsApp and Telegram Messages, TVs, Routers, And Modern Cars Are Hackable By CIA
Short Bytes: WikiLeaks has released the complete catalog of CIA’s hacking tools and malware. This revelation by WikiLeaks, named Year Zero, is...
-

 271Malware
271MalwareThis hard drive will self destruct. Data-wiping malware targets Europe
Meaner strain of Shamoon makes comeback, joined by new, never-before disk wiper. Shamoon—the mysterious disk wiper that popped up out nowhere in...
-

 105Geek
105GeekMicrosoft Bug Bounty Program: Report Vulnerabilities, Get up to $30,000
For the last couple of year, Google has been releasing details about unpatched vulnerabilities discovered by its researchers in Microsoft’s products. Now,...
-

 311News
311NewsSouth Korean Retail Giant Lotte’s Website Hacked After US Military Deal
Lotte Group is a multinational corporation having footprints across Asia, Europe and North America. It has headquarters in Seoul, South Korea. Apart...
-

 223Data Security
223Data SecurityHackers Using Unmonitored System Tools, Protocols for Malicious Goals
The IT security researchers at Cisco’s security intelligence and research group Talos have discovered a malware that can fully hide its origins. The sample that...
-
 90Incidents
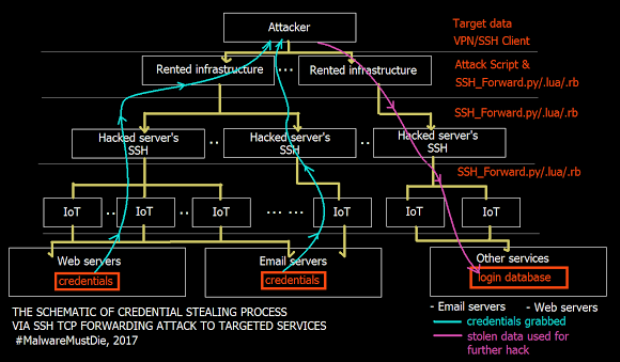
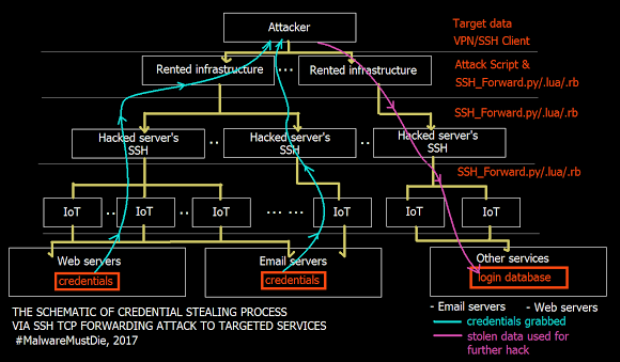
90IncidentsExclusive: A criminal group using SSH TCP direct forward attack is also targeting Italian infrastructure
Exclusive: MalwareMustDie for Security Affairs released the list of the sites under attack. A criminal gang is using SSH TCP direct forward...
-
 148Malware
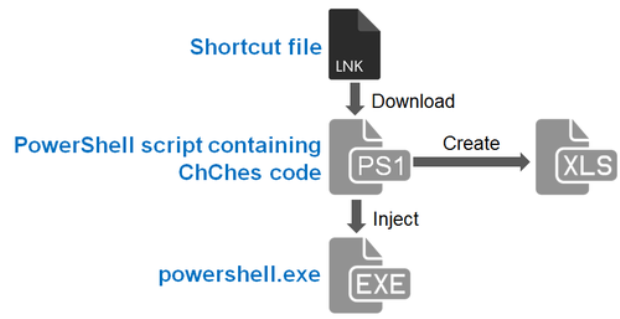
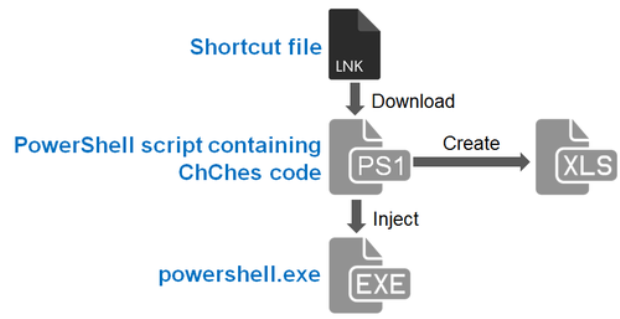
148MalwareMalware Leveraging PowerSploit
Hi again, this is Shusei Tomonaga from the Analysis Center. In this article, I’d like to share some of our findings about...






