All posts tagged "Powershell"
-
 245Data Security
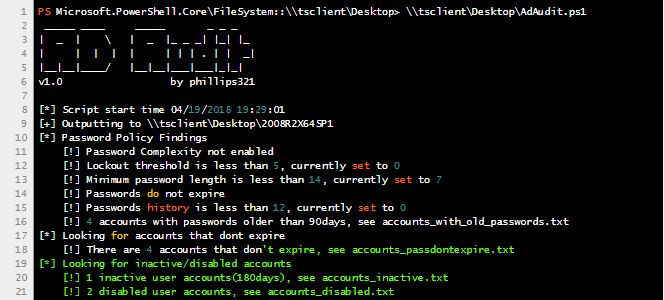
245Data SecurityPowerShell, How to Automate an Active Directory Audit
A group of information security professionals that does active directory audits recently noticed that they are repeating themselves over and over again. So, the...
-
 229Incidents
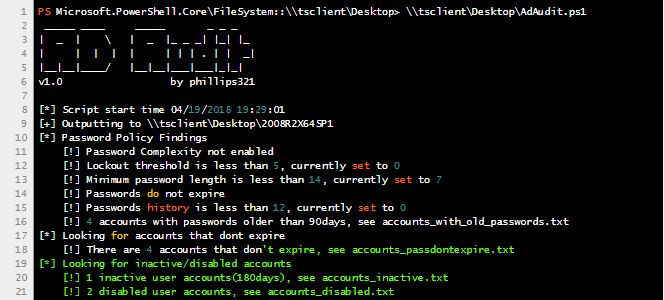
229IncidentsInvoke-DOSfuscation v1.0
Invoke-DOSfuscation is a PowerShell v2.0+ compatible cmd.exe command obfuscation framework. (White paper: https://www.fireeye.com/blog/threat-research/2018/03/dosfuscation-exploring-obfuscation-and-detection-techniques.html) Over the past several years we witnessed a myriad of...
-

 275System Administration
275System AdministrationGrouper – Find Vulnerable Settings in AD Group Policy
Grouper is a slightly wobbly PowerShell module designed for pentesters and redteamers (although probably also useful for sysadmins) which sifts through the...
-
 244Vulnerability Analysis
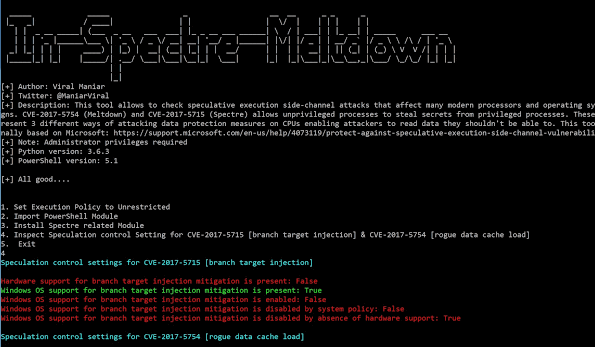
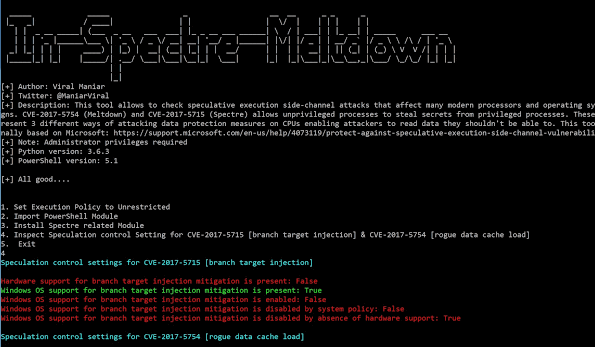
244Vulnerability AnalysisIn-Spectre-Meltdown – Tool to identify Meltdown & Spectre Vulnerabilities in processors
This tool allows to check speculative execution side-channel attacks that affect many modern processors and operating systems designs. CVE-2017-5754 (Meltdown) and CVE-2017-5715...
-

 245System Administration
245System AdministrationPowerUpSQL – A PowerShell Toolkit for Attacking SQL Server
The PowerUpSQL module includes functions that support SQL Server discovery, auditing for common weak configurations, and privilege escalation on scale. It is...
-
 276Exploitation Tools
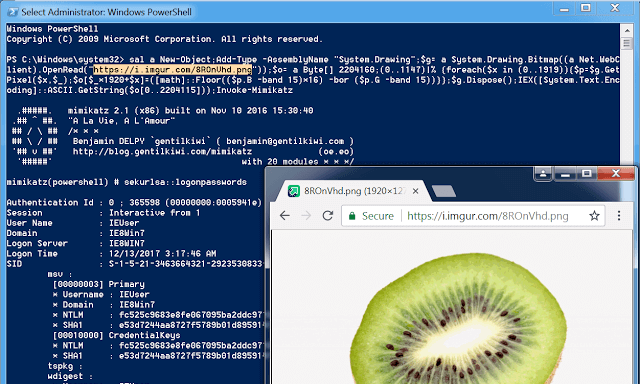
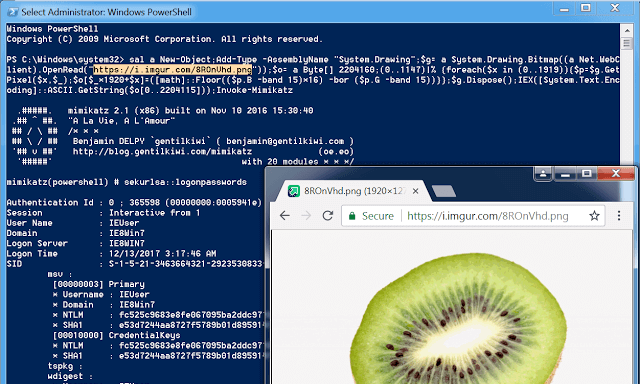
276Exploitation ToolsInvoke-PSImage – Embeds a PowerShell script in the pixels of a PNG file and generates a oneliner to execute
Invoke-PSImage takes a PowerShell script and embeds the bytes of the script into the pixels of a PNG image. It generates a...
-

 263Exploitation Tools
263Exploitation ToolsMacro Creator – MS-Word Payload Delivery
Invoke-MacroCreator is a powershell Cmdlet that allows for the creation of an MS-Word document embedding a VBA macro with various payload delivery...
-
 247Incidents
247IncidentsGo to HELL, PowersHELL : Powerdown the PowerShell Attacks
Powerdown the PowerShell Attacks : Harnessing the power of logs to monitor the PowerShell activities Lately, I have been working on analyzing...
-

 252Malware
252MalwareLocky Ransomware Used Necurs Malware Again back To Form and Take a Screenshot of Your Screen
A Dangerous Necurs malware evolving again and spreading via new email campaign by Necurs bots or hacked web servers and mainly taking...
-

 243Vulnerability Analysis
243Vulnerability AnalysisACLight – PowerShell Script for Advanced Discovery of Privileged Accounts (includes Shadow Admins)
ACLight is a tool for discovering privileged accounts through advanced ACLs (Access Lists) analysis. It includes the discovery of Shadow Admins in...
-

 201Vulnerabilities
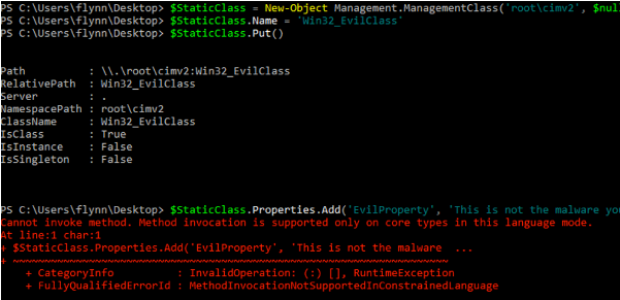
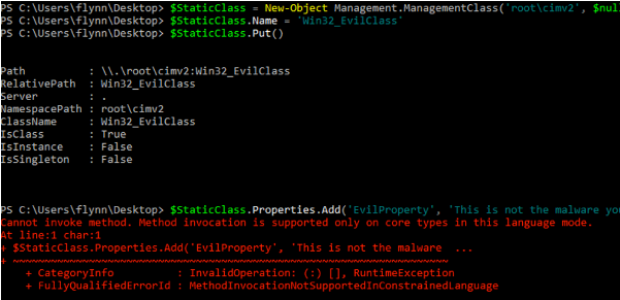
201VulnerabilitiesPowerShell Injection with Diskless Payload Persistence and Bypass Techniques
PowerShell continues to be the tool of choice for defenders, IT administrators, and hackers. The extensibility, support, and ability to have a...
-
 91Malware
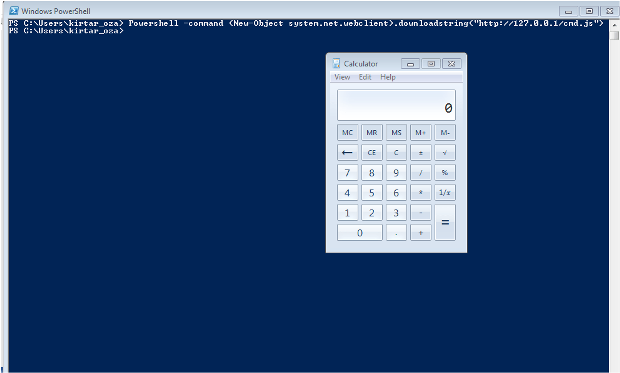
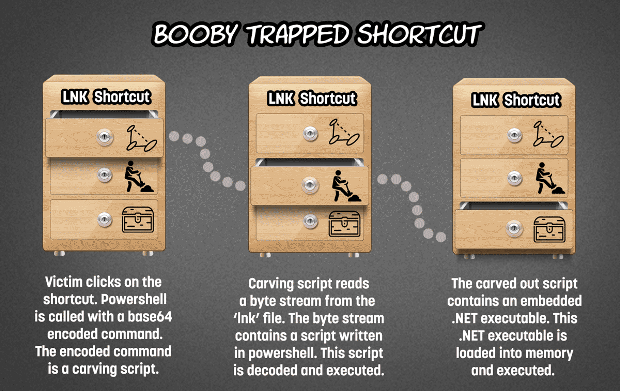
91MalwareBooby trap a shortcut with a backdoor
Embedding a shortcut (.lnk file) which points to powershell (accompanied by an encoded command) in a word document or zip file is...
-
 280Vulnerabilities
280VulnerabilitiesWMImplant – A WMI Based Agentless Post-Exploitation RAT Developed in PowerShell
Just over one year ago (November 2015), I released WMIOps, a PowerShell script that enables a user to carry out different actions...
-

 312Vulnerabilities
312VulnerabilitiesAttackers Leverage Excel, PowerShell and DNS in Latest Non-Malware Attack
Increasingly, cyberattackers have been leveraging “non-malware” attack methods to target vulnerable organizations. Recently, the Carbon Black Threat Research Team was alerted about...
-

 223Vulnerabilities
223VulnerabilitiesA rash of invisible, fileless malware is infecting banks around the globe
Once the province of nation-sponsored hackers, in-memory malware goes mainstream. Two years ago, researchers at Moscow-based Kaspersky Lab discovered their corporate network...
-
 130How To
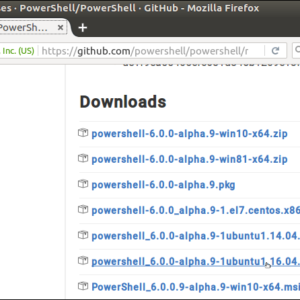
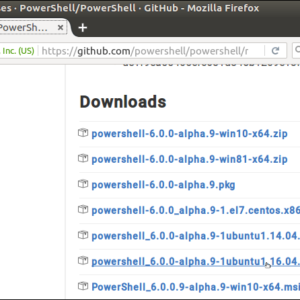
130How ToHow to Install Powershell on A Linux Computer
We know that PowerShell is open source. It is now available for both Linux and Mac. You can download the official packages from...
-

 278How To
278How ToHow To Install Microsoft PowerShell On Linux And OS X
Short Bytes: Microsoft has open sourced the code of its command line shell and scripting language PowerShell, bringing this automation framework to Linux and...
-

 167Malware
167MalwareBrazilian banking Trojans meet PowerShell
Crooks are always creating new ways to improve the malware they use to target bank accounts, and now Brazilian bad guys have...
-
 295Geek
295GeekMicrosoft PowerShell Is Open Source, Now Available On Linux And OS X
Short Bytes: Microsoft has made the official announcement that it’s open sourcing PowerShell. As a result, the company has released the required...
-
 232Hacked
232HackedMicrosoft PowerShell — Hackers’ New Favorite Tool For Coding Malware
Short Bytes: You might not know but PowerShell, the ubiquitous force running behind the Windows environment, is slowly becoming a secure way...
-

 122Data Security
122Data SecurityMalware Created with Microsoft PowerShell Is on the Rise
PowerShell scripts seen in around 38% of malware incidents. Microsoft’s PowerShell task automation framework is becoming one of the most popular tools for...






